The Lazparking virus belongs to the ransomware type infection. This ransomware encrypts all user’s data on the PC (photos, documents, excel tables, music, videos, etc), adds its specific extension to every file, and creates the !!LAZPARKING-MESSAGE.txt files in every folder which contains encrypted files.
What is “Lazparking”?
☝️ Lazparking can be correctly identify as a ransomware infection.
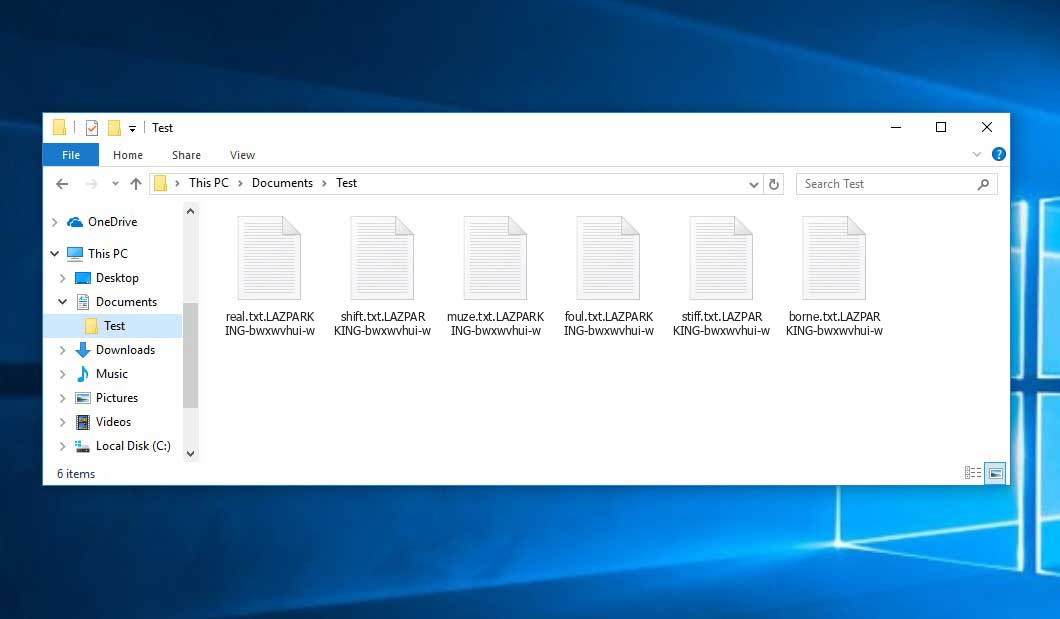
After the encryption process files will be renamed according to the pattern LAZPARKING, which is laid in ransomware. Your photo, named an example “me.jpg” will be altered to “me.jpg.LAZPARKING-bwxwvhui-w” after the encryption.
!!LAZPARKING-MESSAGE.txt file, which can be found in every folder that contains the encrypted files, is a ransom money note. Inside of it, you can find information about ways of contacting Lazparking ransomware developers, and some other info. Inside of the ransom note, there is usually an instruction saying about purchasing the decryption tool. This decryption tool is created by ransomware developers, and can be obtained through the email, contacting [email protected] and [email protected].
Here is a summary for the Lazparking:
| Extension | .LAZPARKING |
| Ransomware note | !!LAZPARKING-MESSAGE.txt |
| Contact | [email protected] and [email protected] |
| Detection | Bulz.239039, Virus:Win32/Neshta.B, MSIL/Bladabindi.BA |
| Symptoms | Your files (photos, videos, documents) have a .LAZPARKING extension and you can’t open it. |
| Fix Tool | See If Your System Has Been Affected by Lazparking virus |
The !!LAZPARKING-MESSAGE.txt file by the Lazparking ransomware states the following frustrating information:
Hello! Your network is penetrated. Forced shutdown of devices can lead to the loss of all data. Do not forcibly disconnect storage volumes from hosts, interrupt process and restart. Damaged information cannot be recovered. All data is properly protected against unauthorized access by steady encryption technology. We have downloaded essential data of company: HR files. Personal data of employees. Like background checks,ssn,account#,signatures. Files of ~4000 employees from folder Departmental Shares\\CTOPS\\Admin\\Employee Document Folder (Scan) Payroll files like tax reports with personal info. SQL database dumps. For example, 400k records of customers with name,address,email,credit card data from LAZPARIS server. Marketing data, for example email lists for MailChimp. Financial, corp accounting data. ... In case if you refuse to cooperate with us, all essential data will be published at forums. Full details and proofs will be provided in case of contacting us by following emails. [email protected] [email protected] It\'s just a business. We can help you to quickly recover all your files. We will explain what kind of vulnerability was used to hack your network. If you will not cooperate with us, you will never know how your network was compromised. We guarantee this will happen again. We can decrypt 2 small files (up to 1MB) for free. Send files by email. Register new email account at secure mail service like mailfence, protonmail to be sure that outgoing email not blocked by spam filter. Don\'t use gmail!. WARNING! Don\'t report to police. They will suspend financial activity of company and negotiation process.
The image below gives a clear vision of how the files with “.LAZPARKING” extension look like:
How did I get Lazparking ransomware on my computer?
That was a huge number of different ways of ransomware injection.
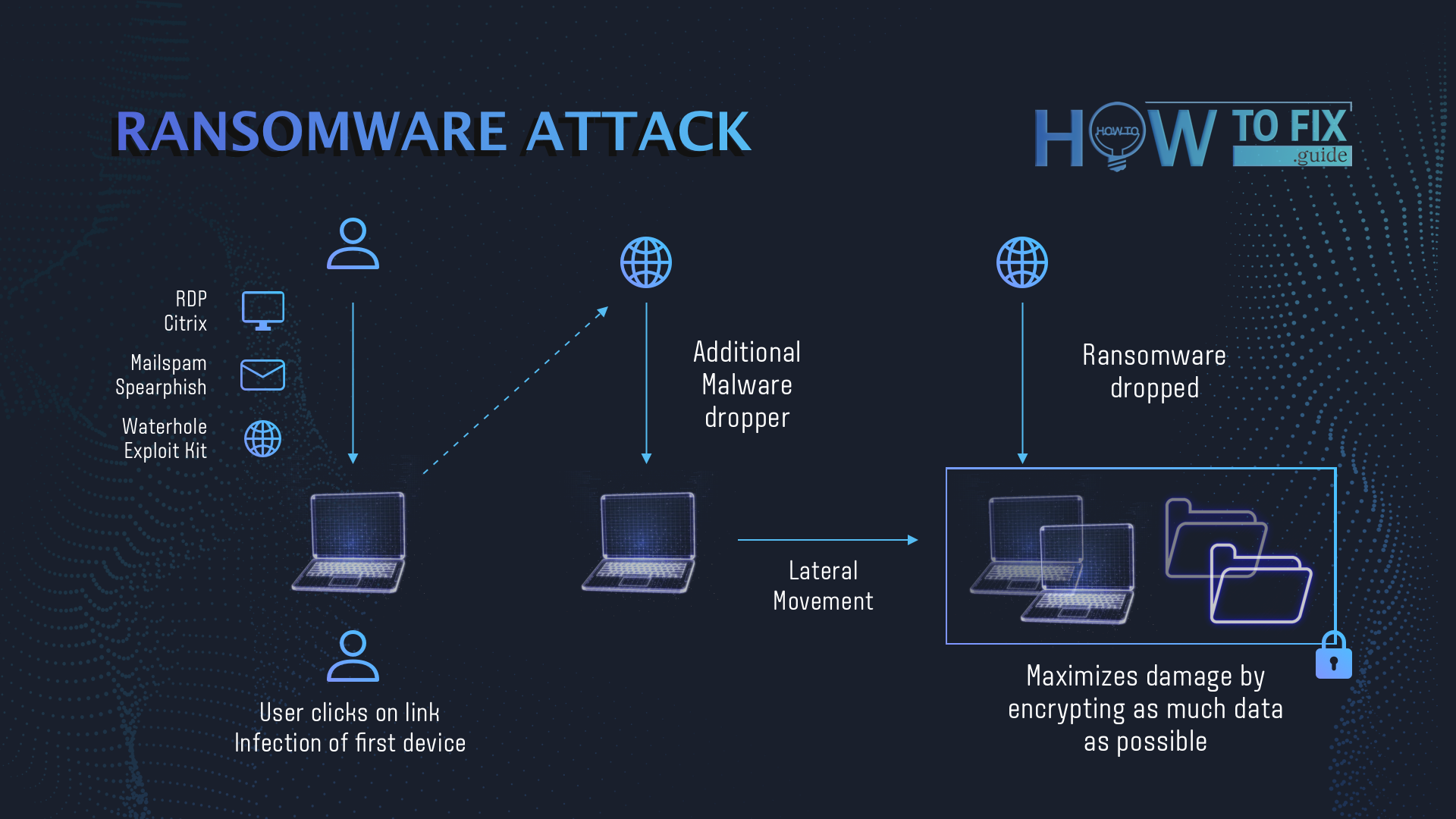
Ransomware injection scheme
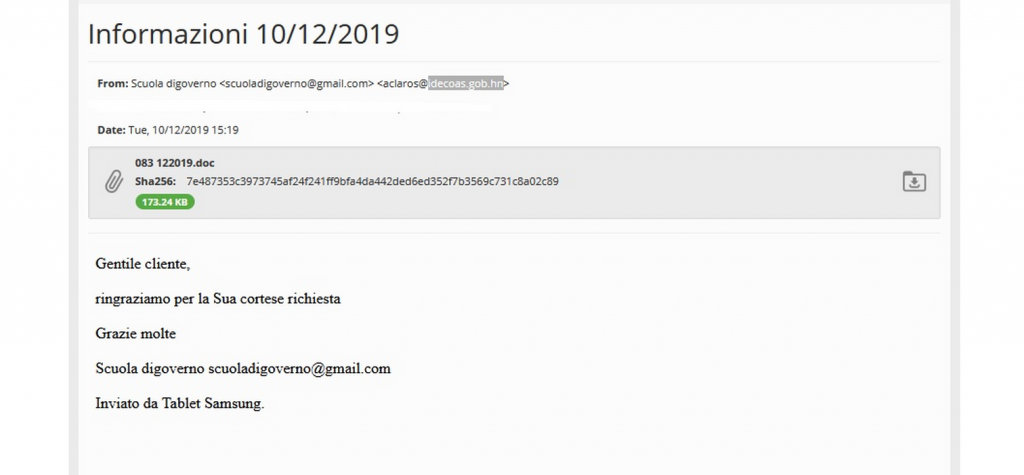
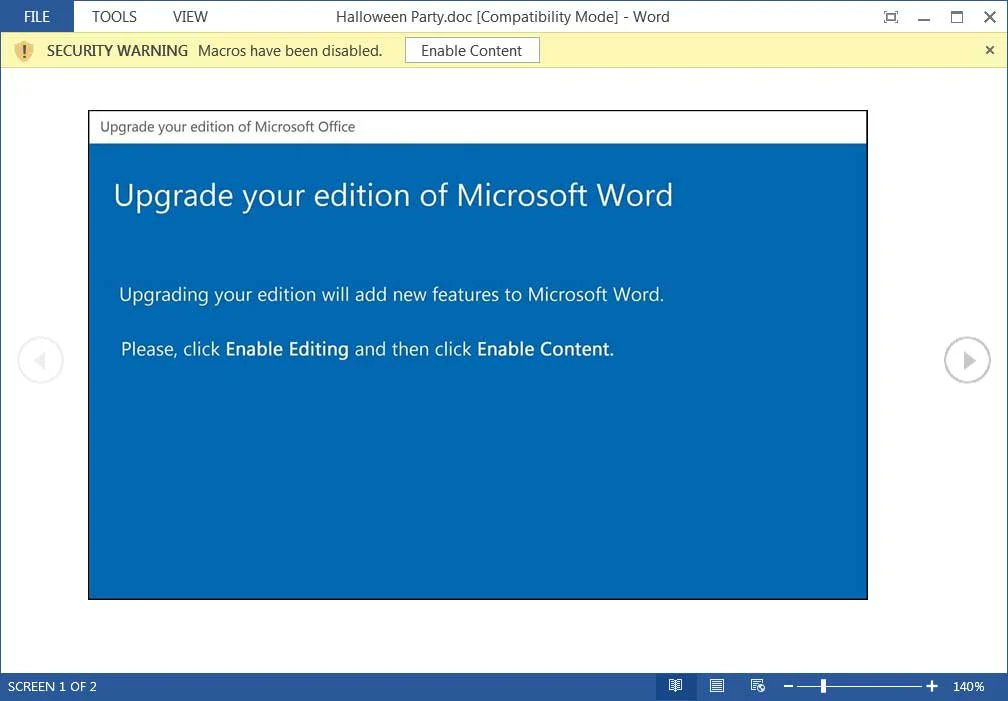
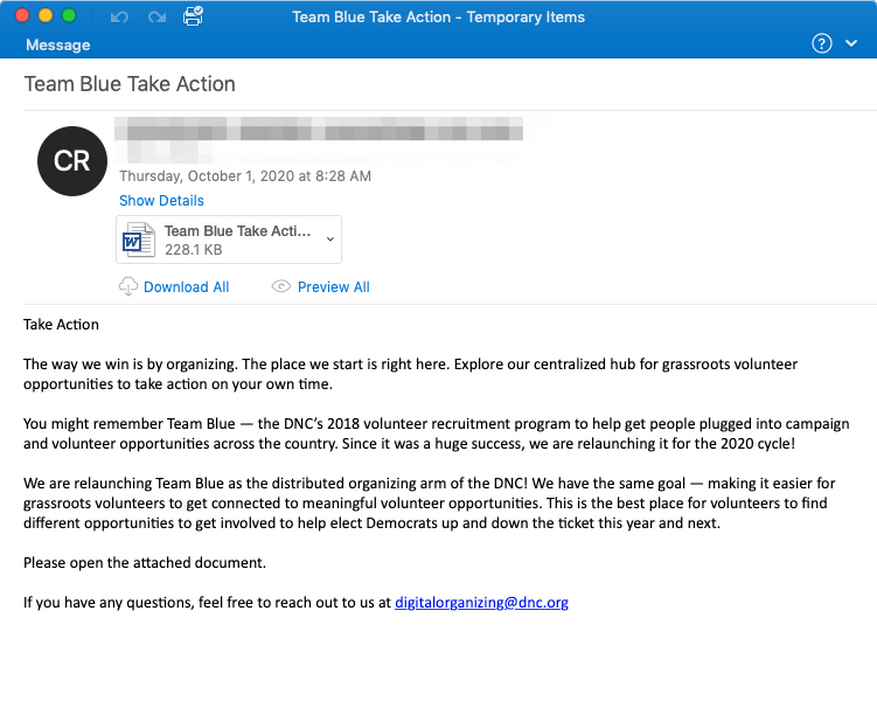
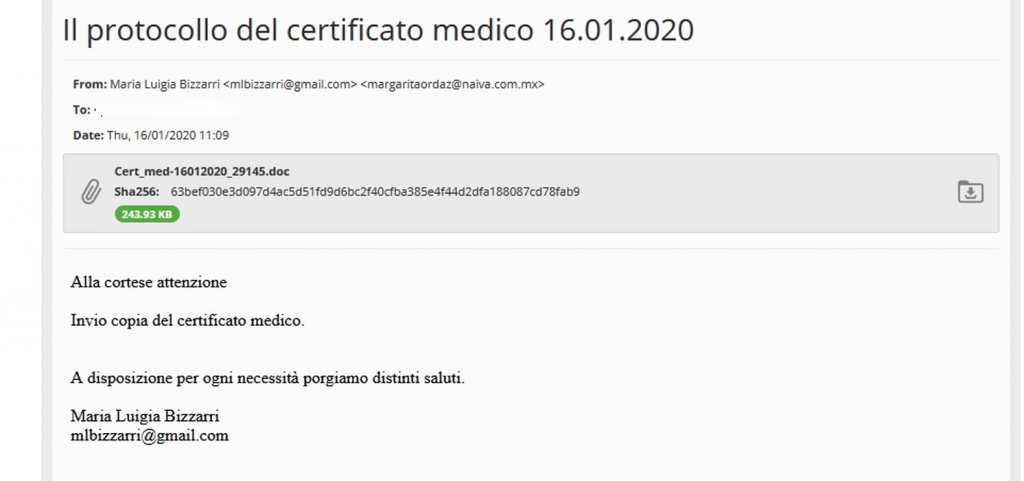
As it was talked about, ransomware distributors are not very innovative in dispersing ways. The biggest share of . virus infiltrations is against email spamming. Victim gets an e-mail which looks similar to a notification from the parcel post service, bill from the automobile lending company, et cetera. Nevertheless, the sender’s address does not look acquainted: normally, it is a bundle of randomly-picked numbers and letters, like “[email protected]”. Companies generally utilize addresses that are representing their own brands, so the use of such an unusual e-mail address should raise suspicion. However, as the practical scenarios reveal, users generally do not look at the email sender’s address, clicking the web links or opening the attached data without any uncertainties. Lazparking ransomware is concealed in this attachment, or in the file which will be downloaded after following the web link.
The second (by success) strategy of ransomware distribution is trojan viruses. In the last several years, trojans turned into all-in-one viruses: one malware may be composed of spyware, backdoor, keylogger and downloader; the last one is utilized to recover the viruses, if they are erased by the user, as well as to download new and new malware. Ransomware may be included to primary trojan packaging, and also downloaded later by malware downloader. It is quite tough to predict, when the ransomware will show itself.
There is also the third way of ransomware injection, however, it becomes less and less popular day-to-day. I am talking about peering networks, such as torrents or eMule. No one can control which files are packed in the seeding, so you can discover a huge pack of different malware after downloading. If circumstances force you to download something from peering networks – scan every downloaded folder or archive with antivirus software.
How to remove Lazparking virus?
In addition to encode a victim’s files, the Lazparking infection has also started to install the Azorult Spyware on computer to steal account credentials, cryptocurrency wallets, desktop files, and more.
To ensure the user that ransomware distributors really have the decryption tool, they may offer to decrypt several encrypted files. And they are the single owners of this decryption program: Lazparking ransomware is a completely new type, so there is no legit program from anti-malware vendors, which can decrypt your files. But such a situation is in momentum: decryption tools are updating every month.
However, paying the ransom is a bad decision, too. There is no guarantee that Lazparking ransomware developers will send you the decryption tool and a proper decryption key. And there are a lot of cases when ransomware distributors deceived their victims, sending the wrong key or even nothing. In the majority of cases, there is a way to recover your files for free. Search for available backups, and restore your system using it. Of course, there is a chance that the backup you found is too old, and does not contain a lot of files you need. But, at least you will be sure that there is no malware in your system. However, to ensure that there are no malicious programs in your system after the backup, you need to scan your PC with anti-malware software.
Lazparking ransomware is not unique. There are more ransomware of this type: Doppelpaymer, Doppelpaymer, Esexz. These examples of ransomware act in a similar way: encrypting your files, adding a specific extension, and leaving a great number of ransom money notes in every folder. But there are two things which make difference between these ransomware – cryptography algorithm, which is used for file encryption, and ransom amount. In some cases, victims are able to decrypt their files without any payments, just using free solutions produced by several anti-malware vendors, or even with the decryption tool which is offered by ransomware creators. The last scenario is possible when ransomware distributors have typed your decryption key inside of a ransom money note. However, as you can already guess, such luck is a very rare thing. Ransomware is created for money gaining, not for jokes or scaring.
Reasons why I would recommend GridinSoft1
Download Removal Tool.
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

Frequently Asked Questions
How сan I avoid ransomware attack?
Lazparking ransomware doesn’t have a superpower.
You can easily protect yourself from its injection in several easy steps :
- Ignore all emails from unknown mailboxes with a strange unknown address, or with content that has likely no connection to something you are waiting for (can you win in a lottery without taking part in it?). If the email subject is likely something you are waiting for, check carefully all elements of the suspicious letter. A fake email will surely contain a mistake.
- Do not use cracked or untrusted programs. Trojans are often distributed as a part of cracked software, possibly under the guise of “patch” which prevents the license check. But untrusted programs are very hard to distinguish from trustworthy software, because trojans may also have the functionality you need. You can try to find information about this program on the anti-malware forums, but the best solution is not to use such programs.


Leave a Comment