The “I have e-mailed you from your account” scam spreads via deceptive emails claiming to originate from recipients’ accounts. This phishing campaign falsely asserts access to users’ devices, citing malware from adult-themed sites.
Perpetrators threaten to release non-existent compromising videos unless a $250 Bitcoin ransom is paid within 48 hours. Users are warned against sharing the scam, reinforcing the need for caution in the face of these fraudulent emails.
What Is “I have e-mailed you from your account” Email Scam?
The “I have e-mailed you from your account” Email Scam denotes a sextortion spam campaign characterized by a large-scale operation involving disseminating numerous deceptive emails. In this fraudulent scheme, recipients receive emails falsely asserting the existence of a compromising video featuring the recipient, threatening its public release unless ransom demands are met. It is crucial to underscore that all information presented in these emails is baseless. There are no actual recordings, and neither the recipients’ devices nor their privacy have been compromised.
“I have e-mailed you from your account” Email Scam
| Name | “I have e-mailed you from your account” Email Scam |
| Threat Type | Phishing, Scam, Social Engineering |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Similar Behavitor | “Some Bad News That You Are About To Hear” Email Scam, “Password Was Compromised Through A Legitimate Website” Email Scam |
| Fix Tool | See If Your System Has Been Affected by Your Account Was Hacked Virus |
How Does “I have e-mailed you from your account” Scam Work?
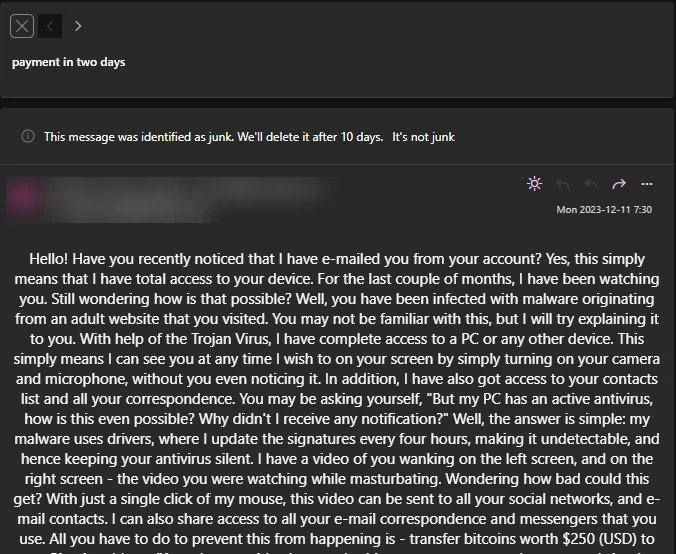
The scam emails titled “I have e-mailed you from your account” (often appearing as “payment in two days”) purport to have been sent from the recipient’s email accounts, creating a false impression that the sender has gained access to the users’ devices. These deceptive emails allege that the recipients’ systems were infected with malware traced back to an adult-themed website visited by the targets. The scammers assert that leveraging the non-existent malware infection, they have recorded a video using the cameras on the devices. The purported recording supposedly took place during the recipients’ visits to adult websites, capturing the user on one side and the content they were viewing on the other.
Furthermore, the scam emails claim that the scammers have acquired the recipients’ email and social media contact lists. To coerce compliance, the scammers threaten to distribute the fabricated video to these contacts unless the recipients transfer 250 USD of Bitcoin cryptocurrency to a specified cryptowallet address. The ransom payment is mandated within a 48-hour, commencing from the moment the recipient opens the “I have e-mailed you from your account” message. Recipients are explicitly cautioned that any attempt to share these emails will result in disseminating the recording to the extracted contacts. As emphasized earlier, all the assertions made in these emails are entirely false. Consequently, trusting these claims exposes users to financial losses and potential recurrence of scam attempts.
Is It Dangerous?
The email in question is only an immediate threat if the recipient falls prey to the demands made within. However, the primary risk associated with this communication is financial loss. Additionally, there is a potential for similar scams to be targeted at the individual, given the success of the initial attempt by scammers.
As previously stated, we advise recipients to ignore the email. Furthermore, labeling it as spam and blocking the sender is a protective measure that can shield the recipient and enhance anti-spam filters. Proactively taking this step may act as a deterrent, discouraging scammers from persistently targeting the individual.
How to Remove Malware from Your PC?
Although the claims of scammers are false in most cases, to be safe, we recommend scanning your device to ensure there is no malware. The best way to do it is by using anti-malware software. I recommend GridinSoft Anti-Malware as a fast, lightweight, and effective security solution that can easily repel threats, including Bladabindi!ml. You can try it out during a 6-day free trial.
You can remove the threat manually, but we do not recommend doing so. As malware tries to gain persistence, it creates numerous instances of itself, making it nearly impossible to trace all the parts. As a result, manual removals may take time for low to no efficiency. I compiled the best removal practices for malware in the guide below.
Remove malware with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common viruses as shown from our tests with the software, and we assure you that it can remove malware as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “malware” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing malware and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
Frequently Asked Questions (FAQ)
There is a probability that a bit of the promises made by the “I have e-mailed you from your account” are real. However, I heavily recommend you do not follow any of the actions on the banner. Instead, check all the aforementioned issues by yourself – and then make a decision.
There is a high chance that pop-up scams like “I have e-mailed you from your account” will happen due to malware activity. In particular, things like adware and browser hijackers aim specifically for such activities. Along with pop-up scams, it can shift you to phishing pages and malicious websites.
This scam banner is only a scary picture. That being said, following the “instructions” from the banner is what really creates malware injection risk. Usually, crooks who pose as tech support managers spread unwanted programs or even outright malware through such a scheme.
If you did what the pop-up asked, remain calm and revert all the changes that the “support” have made. Next, execute the scan with GridinSoft Anti-Malware to ensure that all malicious or unwanted items removed. Also, reinstall the remote access utility you have installed to prevent any unauthorized connections.
"I have e-mailed you from your account"
Name: I have e-mailed you from your account Email Scam
Description: The "I have e-mailed you from your account" scam spreads via deceptive emails claiming to originate from recipients' accounts. This phishing campaign falsely asserts access to users' devices, citing malware from adult-themed sites. Perpetrators threaten to release non-existent compromising videos unless a $250 Bitcoin ransom is paid within 48 hours. Users are warned against sharing the scam, reinforcing the need for caution in the face of these fraudulent emails.
Operating System: Windows
Application Category: Malware

