Law enforcement officials from France, Japan and New Zealand warn that Emotet activity surged in the last week, with sharply rising number of attacks targeting their countries.
The fact is that the number of spam emails originating from the Emotet infrastructure and targeting companies and government agencies in these three countries has indeed significantly increased.Emotet activity described in the alerts refers to email spam campaigns that originated from Emotet infrastructure and targeted companies and government agencies in the three countries. Victim organizations who received the emails, opened, and then ran the attached documents were at risk of getting infected with one of today’s most dangerous malware”, — write ZDNet journalists.
Joseph Rosen, one of the enthusiasts of the Cryptolaemus group, which includes more than 20 cybersecurity specialists from around the world, united in 2018 for a common goal – to combat Emotet malware, confirmed to ZDNet that attacks on the aforementioned countries have indeed increased.
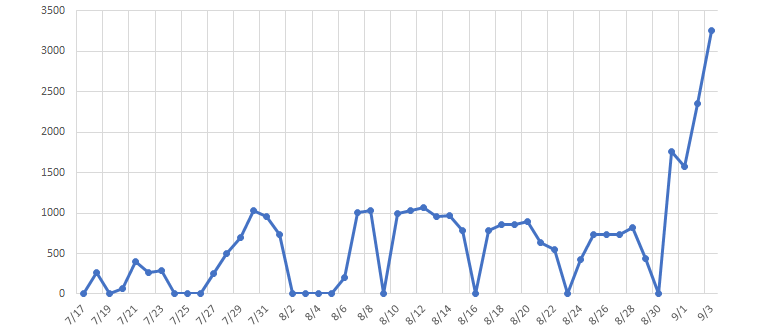
Rosen said that Emotet operators have begun to actively attack New Zealand and most of the malicious emails come from E3 (one of three mini-botnets included in the Emotet infrastructure). At the same time, all three botnets (E1, E2 and E3) also attacked Japan. These waves of spam have tripled the number of Emotet detections in the country, according to a local CERT.
While the number of attacks targeting France was significantly lower, there Emotet managed to infect computers of the Parisian judicial system, get on the headlines and caused a stir that resulted in a warning issued by the authorities.
The French Interior Ministry reacted by blocking all Office documents (.doc) from being delivered via email, and France’s cyber-security agency ANSSI followed through with an official cyber-security alert on Monday, urging government agencies to pay attention to the emails they’re opening”, — reports ZDNet.
According to government reports, attacks in all three countries followed the same scenario. Emotet operators infected one victim and then stole their old email threads. The hackers resumed these old conversations by adding malicious attachments (usually .doc files and password-protected ZIP archives) and attacking other users, who usually opened the files out of curiosity.
Security experts believe that at some point Emotet will switch targeting on attacking users from other countries, since, according to cybersecurity company Proofpoint, the botnet can send spam in several languages.


Leave a Comment