The Cdpo virus, also known as a ransomware infection, is part of the STOP/DJVU family. This malware is notorious for malignant file encryption operations. Once the Cdpo virus infects a system, it scans the system for files such as documents, videos, photos, and more. It alters the file structure and appends the “.cdpo” extension to each file, making them inaccessible and unusable without the decryption key.
Cdpo Virus Overview
Cdpo
🤔 Cdpo virus can be classified as ransomware that originates from the DJVU/STOP family. Its main target is to cipher files that are important to you. Then, this ransomware asks for a ransom payment – ($490 – $980) in Bitcoin.
The Cdpo virus is a type of malware that encrypts your files and makes you pay for their recovery. This malware encrypts different file types. Encrypted files are identifiable by a distinct “.cdpo” extension. As a result, the affected files become inaccessible and unusable.
Subsequently, the ransomware asks for a ransom payment in Bitcoin from the victims, which ranges from $490 to $980, depending on the time passed after the attack. In all cases, a text file with ransom payment guidances is named as “_readme.txt“.
Cdpo Ransomware operates by Salsa20 encryption algorithms to cipher the targeted files. Since the Cdpo virus uses such a robust ciphering method, it becomes really difficult, if even possible, to pick the decryption key without cooperating with the attackers.
Once Cdpo malware finishes the encryption, it shows a ransom note to the user, asking for a ransom payment in exchange for the decryption key. The ransom note contains instructions on how to pay off the bill and also often contains threats of data loss or increased ransom amounts if the ransom is not paid within a specified timeframe.
I have created an all-encompassing list of potential solutions, tips, and practices to disable the Cdpo virus and recover your files. In some cases, you can recover the files, but sometimes, it may be impossible.
📌 Important Reminder!
It is essential to say that paying the ransom is not a guarantee of the successful files recovery. The cybercriminals who stand behind the Cdpo virus are known for their untrustworthiness. There were the cases where people have paid the ransom, only to be denied by the cyber criminals with the decryption key provision.
Cdpo uses a unique key for every victim, with one exception:
The Cdpo virus bears resemblance to other DJVU ransomware variants like Cdxx, Cdtt, Cdwe and Cdaz. This virus encrypts a wide range of common file types and appends its distinct “.cdpo” extension to all files. For instance, a file named “1.jpg” would be altered to “1.jpg.cdpo” and “2.png” to “2.png.cdpo“.
After successful encryption, malware spawns a special text file named “_readme.txt” and places it in every folder containing the encrypted files. It as well adds the readme file to the desktop, so the victim will not miss the attack even without opening folders.
The image below provides a visual representation of files with the “cdpo” extension:
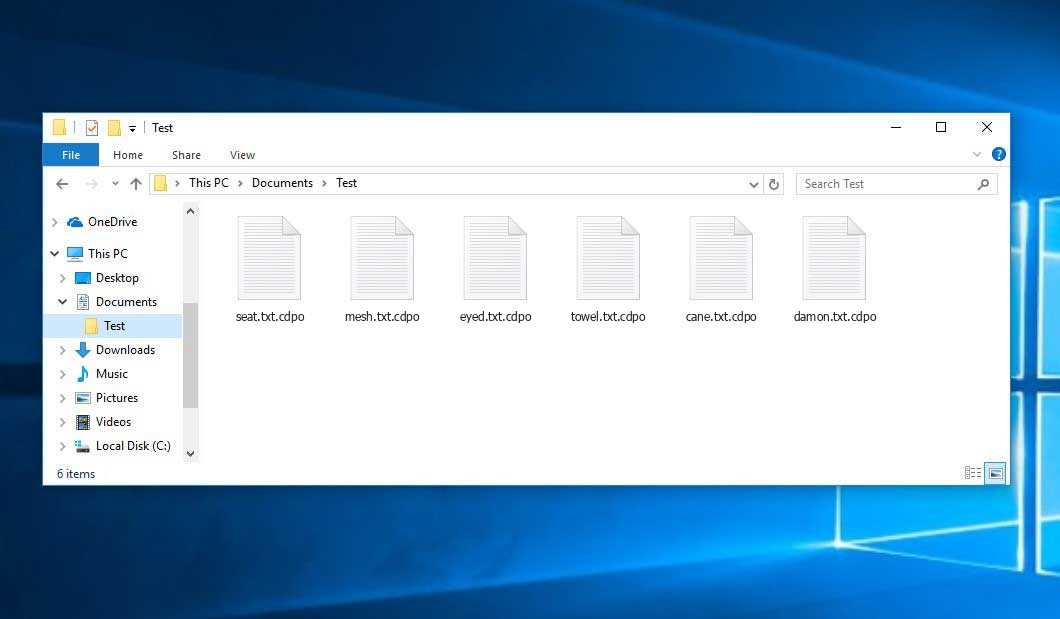
Encrypted Files by STOP/DJVU Ransomware
| Name | Cdpo Virus |
| Ransomware family1 | DJVU/STOP2 ransomware |
| Extension | .cdpo |
| Ransomware note | _readme.txt |
| Ransom | From $490 to $980 (in Bitcoins) |
| Contact | [email protected], [email protected] |
| Detection | Trojan:MSIL/Lokibot.ABXX!MTB, Trojan:Win32/Smokeloader.AMBI!MTB, Win32/GenCBL.CTW |
| Symptoms |
|
| Fix Tool |
To remove possible malware infections, scan your PC:
6-day free trial available. |
This message asking payment is for restore files via decryption key:
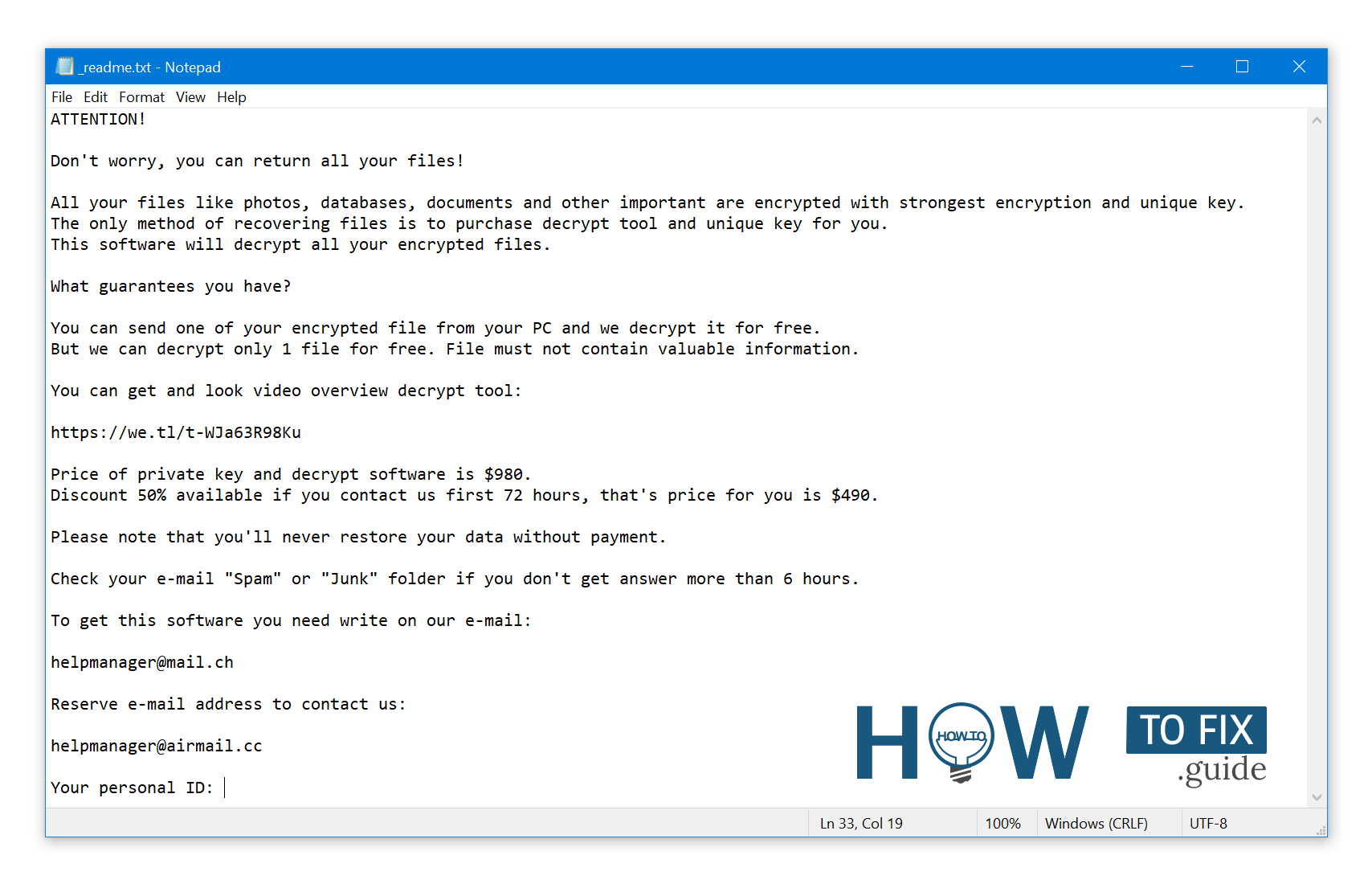
_readme.txt (STOP/DJVU Ransomware) – The terrifying alert insisting users to pay off the ransom to unlock the encoded data contains these annoying cautions.
Cdpo ransomware arrives as a set of actions that are meant to perform certain tasks on a victim’s computer. One of the first processes being launched is winupdate.exe, a deceptive process that shows a fake Windows update notification during the attack. Such a trick helps to convince the victim that a sudden system slowdown is caused by a Windows update.
Simultaneously, the ransomware runs another process (which name commonly consists of 4 random characters) which commences scanning the disk for target files and ciphering them. Next, the ransomware deletes Volume Shadow Copies from the disk through the following CMD command:
vssadmin.exe Delete Shadows /All /Quiet
Once removed, it becomes impossible to retrieve the previous computer state using System Restore Points. The issue is, ransomware operators are getting rid of any built-in Windows approaches that could help the victim to restore files for free. In addition, the crooks modify the Windows HOSTS file by appending a list of domains to it and linking them to the localhost IP. As a result, the victim will encounter a DNS_PROBE_FINISHED_NXDOMAIN error when trying to access one of the blocked websites.
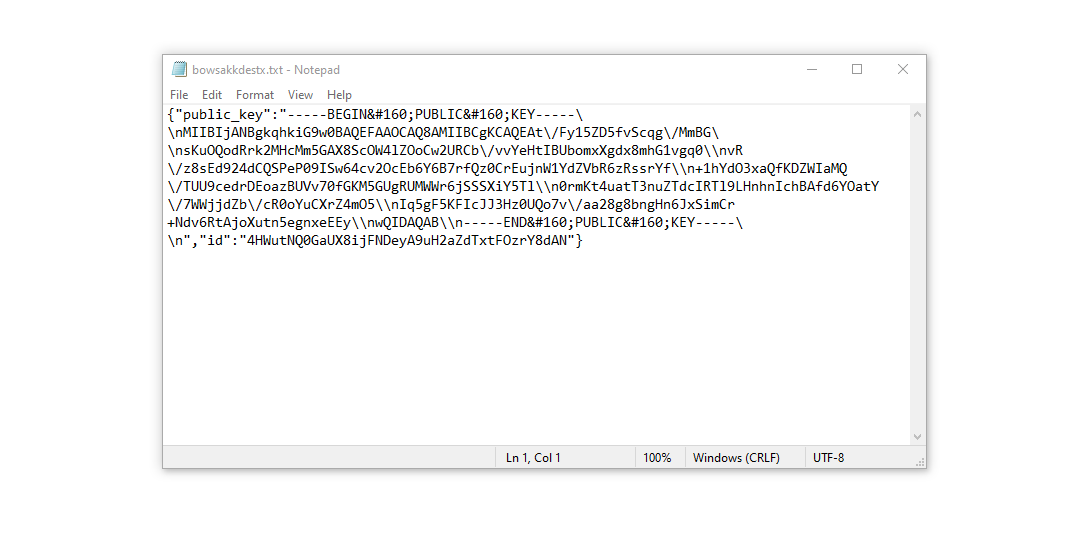
We noticed that ransomware attempts to block websites that promote various how-to guides for computer users. It is clear that by hindering specific domains, the perpetrators are seeking to stop the victim from accessing relevant and helpful ransomware-attack-related information online. Malware also saves two .txt files on the victim’s computer that provide details related to the attack – the victim’s public encryption key and personal ID. These two files are named bowsakkdestx.txt and PersonalID.txt.
After all these alterations, the malware doesn’t cease. Variants of STOP/DJVU have a tendency to deploy Vidar password-stealing Trojan on compromised systems. This threat possesses an huge list of capabilities, including:
- Infiltrating the victim’s computer with malware and executing it to gain unauthorized access.
- Obtaining unauthorized access to login credentials of Steam, Telegram, and Skype.
- Manipulating and viewing files on the victim’s computer without their knowledge.
- Stealing cryptocurrency wallets from the victim’s system.
- Granting the hackers remote control over the victim’s computer for various malicious activities.
- Extracting sensitive information such as browser cookies, saved passwords, and browsing history.
The encryption algorithm used by DJVU/STOP virus is AES-256. So, once your data is encrypted with an online decryption key, the possibility to get your files back are quite low. Thing is, online key is unique for each victim, and brute forcing it will take too much time.
Retrieving the online decryption key in another way is also merely impossible. It is stored on a remote server owned by the hackers who promote the Cdpo malware. For receiving decryption key the payment should be $980. To get the payment details, the victims should contact the fraudsters by email ([email protected]).
The message by the ransomware states the following information:
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-WJa63R98Ku Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: [email protected] Reserve e-mail address to contact us: [email protected] Your personal ID: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
How To Remove STOP/Djvu Ransomware?
Video Guide
How To Decrypt .cdpo Files?
How to restore big files?
Try removing .cdpo extension on a few big files and opening them. This malware has issues with large files encryption. Either the virus accessed and did not lock the file, or it bugged and did not add the filemarker. If you have files that are very large (2GB+), the latter is most likely. Please, let me know in comments if that will work for you.
The newest extensions released around the end of August 2019 after the criminals made changes. This includes Cdtt, Cdwe, Cdaz etc.
As a consequence of the modifications made by the criminals, STOPDecrypter is no longer assisted. It has been replaced with the Emsisoft Decryptor for STOP Djvu Ransomware developed by Emsisoft.
You can download free decryption tool here: Decryptor for STOP Djvu.
-
Select folders for decryption.
Based on the default configurations, the decryptor will by default choose the reachable directories in order to unlock the currently accessible drives (the connected ones), including the network drives. You can choose other locations with the “Add” button.
Decryptors usually offer several options depending on the specific malware family. The existing possible options are shown in the Options tab and can be turned on or disabled there. You may discover a comprehensive list of the currently active Options below.
-
Click on the “Decrypt” button.
As soon as you add all the desired locations for decryption into the list, click on the “Decrypt” button in order to initiate the decryption procedure.
Note that the main screen may turn you to a status view, letting you know of the active process and the decryption statistics of your data:
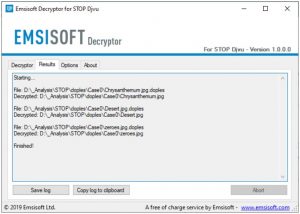
The decryptor will notify you as soon as the decryption procedure is completed. If you need the report for your personal papers, you can save it by choosing the “Save log” button. Note that it is also possible to copy it directly to your clipboard and to paste it into emails or messages here if you need to do so.
The Emsisoft Decryptor might display different messages after a failed attempt to restore your files:
✓ Error: Unable to decrypt file with ID: [your ID]
Emsisoft failed to find a correspondnig decryption key in their database.
✓ No key for New Variant online ID: [your ID]
Notice: this ID appears to be an online ID, decryption is impossible
Malware used an online key to cipher your files. Your key is unique and is kept on the command server, controlled by criminals. File recovery without paying the ransom is impossible. 🙁
✓ Result: No key for new variant offline ID: [example ID]
This ID appears be an offline ID. Decryption may be possible in the future.
Malware used an offline key, though the file recovery operation failed (the offline decryption key isn’t available yet). Nonetheless, this message is a good news for you, since it is possible to restore your files in the future. 🙂
It can take a few weeks or months until the decryption key gets found and uploaded to the decryptor. Please follow updates regarding the decryptable DJVU versions here.
✓ Remote name could not be resolved
This stands for a DNS issues. Our first recommendation is to reset your HOSTS file back to default.
How to Restore .cdpo Files?
In some case ransomware is not doom for your files…
The Cdpo ransomware encryption mechanism is next: it encrypts every file byte-by-byte, then saves a duplicate, removing (not overriding!) the original file. Thus, the data of the file placement on the disk drive is lost, but the original file is not deleted from the disk. The cell, or the sector where this file was stored, can still contain this file, but it is not present in the file system and can be overwritten by data that has been loaded to this drive after the removal. Hence, it is possible to restore your files using special software.
Anyway, after realizing it was an online algorithm, it is impossible to retrieve my encrypted files. I also had my backup drive plugged in at the time of the virus, and this was also infected, or so I thought. Every folder within my backup drive had been infected and was encrypted. However, despite losing some important files, I retrieved almost 80% of my 2TB storage.
When I started going through the folders, I noticed the readme.txt ransom note in every folder. I opened some of the folders and found that all files that were not in a subfolder within that folder had been encrypted. However, I found a flaw and glimmer of hope when I went into the subfolders in other folders and found that these files had not been encrypted. Every folder within my c and d drives, including subfolders, had been encrypted, but this was not the case with the backup drive. Having subfolders created within a folder has saved 80% of my data.
As I said, I believe this to be only a small loophole on a backup drive. I’ve since found a further 10 % of my data on another hard drive on a different pc. So my advice is if you use a backup drive, create subfolders. I was lucky, I guess. But I was also unlucky that the virus hit as I was transferring some files from my backup.
Hopefully, this can help some other people in my situation.
Jamie NewlandRecovering your files with PhotoRec
PhotoRec is an open-source program, which is initially created for file retrieval from damaged disks, or for data recovery in case if they are unintentionally deleted. However, with time flow, this program received the ability to recover the files of 400 different file types. Hence, it can be used for data recovery after the Cdpo attack.
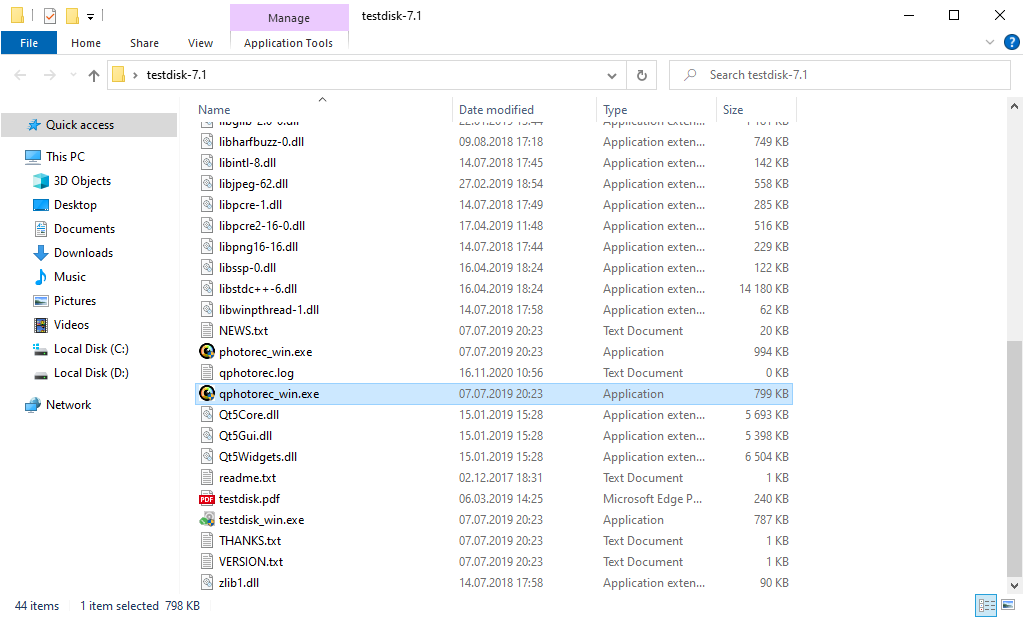
First, you need to download this app. It is 100% free, but the developer notifies that there is no warranty that your files will be recovered. PhotoRec is spread together with other utility of the same developer – TestDisk. The program archive will have TestDisk name, but don’t worry. PhotoRec files are right inside.
To open PhotoRec, find and open “qphotorec_win.exe” file. No installation is needed – the program has all the files it need inside of the archive, hence, you can mount it on your USB drive, and try to help your friends/parents/anyone who has been attacked by Cdpo ransomware.
Upon the start, you will witness the screen showing you the entire list of your drives. However, this details are probably futile, because the required menu is placed a bit higher. Click this menu, then choose the disk which was attacked by ransomware.
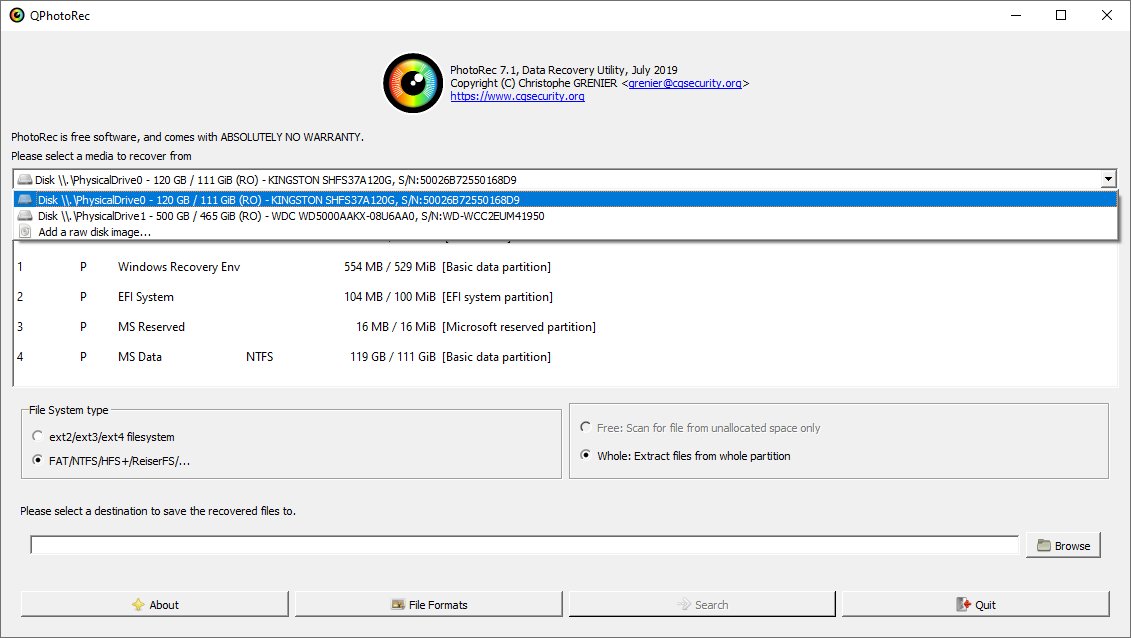
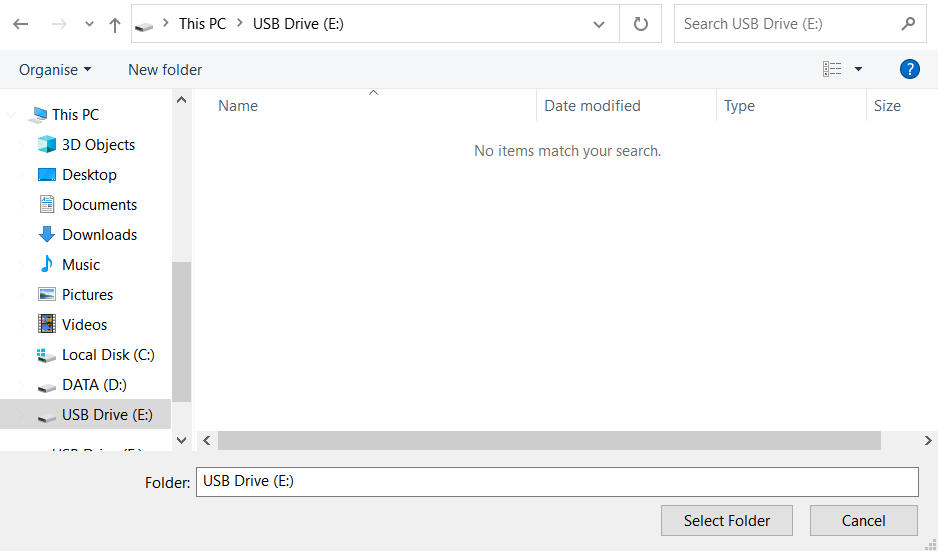
After picking the disk, you need to choose the destination folder for the restored files. This menu is located at the lower part of the PhotoRec window. The best selection is to export them on USB drive or any other type of removable disk.
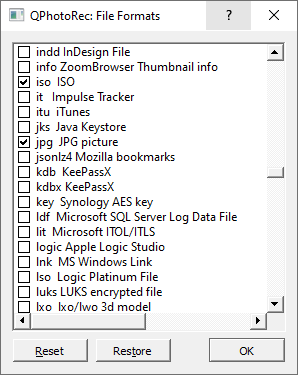
Then, you need to designate the file formats. This feature is located at the bottom, too. As it was mentioned, PhotoRec can regain the files of about 400 different formats.
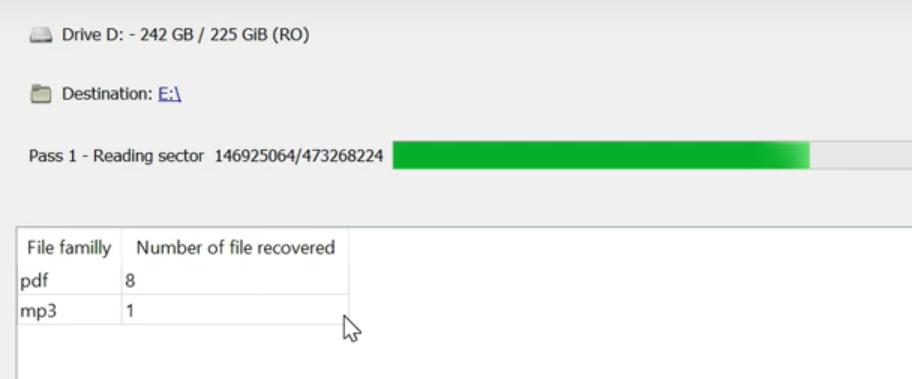
Finally, you can begin files recovery by pressing the “Search” button. You will view the screen where the results of the scan and recovery are shown.
Cdpo files recovery Video Guide.
Frequently Asked Questions
I need your help to share this article.
It is your turn to help other people. I have written this guide to help people like you. You can use buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan Smith

Leave a Comment