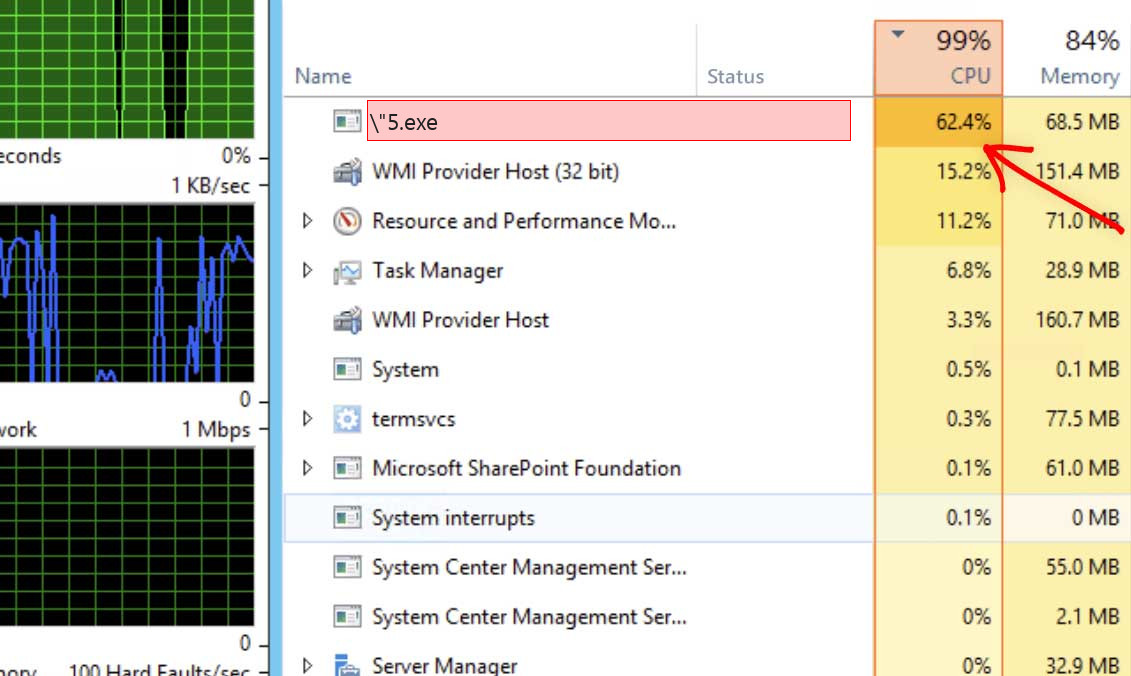
\”5.exe process belongs to a malicious application that can properly be recognized as a coin miner trojan virus. That malware form uses your PC components to mine cryptocurrencies, generally – Monero or DarkCoin1. It makes your system pretty much unusable due to high CPU utilization.
What is \”5.exe process?
\”5.exe is a malicious process created by coin miner virus
Besides CPU usage, some of the coin miners additionally make use of GPU power for their operations. In that instance, you will likely struggle even to see the mouse arrow moving – GPU is often utilized on 100%. It is not as essential as CPU for system work, so \”5.exe coin miner viruses do not waste time on trifles and utilize it all. It often can lead to sad effects.
Shortly about cryptocurrency mining
List of the typical coin miner symptoms
How dangerous is the \”5.exe miner?
Coin miners does not deal damage to your files. However, they make a lot of unpleasant things with the whole system
Initially, \”5.exe malware makes your PC overloaded. It is unable to run your applications anymore, as all CPU power is used by a malware. That malware does not care for your wants, all it focuses on is making money on you. Even if you are patient, and you waited until browser is open, you will likely struggle with extremely slow performance. Pages will open up for years, any type of logins will likely take about a minute – just a nightmare for a person who does a job online.
\”5.exe Technical Summary.
| File Name | \”5.exe |
| Type | Trojan Coin Miner |
| Detection Name | Trojan:Win32/CoinMiner |
| Distribution Method | Software bundling, Intrusive advertisement, redirects to shady sites etc. |
| Similar behavior | Soska.exe, Conhost_rs.exe, Starter.exe |
| Removal | Download and install GridinSoft Anti-Malware for automatic \”5.exe removal. |
“Visible” harm is not a solitary negative activity coin miners do to your system. \”5.exe coin miner likewise deals damage to your operating system. To perform all malevolent operations correctly, it ruins the security mechanisms of your system. You will likely see your Microsoft Defender disabled – malware stops it to prevent detection. If you open the HOSTS file, you will likely see a load of new notes – they are brought in by this coin miner to connect your computer to a malicious mining network. All these changes shall be thrown back to the original in the process of system recovery.
Hardware effects of coin miner activity
Besides making your computer slow, performing at peak power for long times may trigger damage to your device and increase power bills. Hardware components are created to easily get along with high load, but they are good with it only in case when they are in a good shape.
Tiny and covered CPU cooling system is quite hard to damage. Meanwhile, GPUs have big and easy-to-access fans, which can be easily broke if touched while working, for example, by the user much earlier before the malware injection. Malfunctioning cooling system, together with the very high load caused by \”5.exe virus can easily lead to GPU failure3. Video cards are also tend to have very fast wearing when utilized for cryptocurrency mining. It is surely a bad situation when the performance of your graphic card decreases on 20-30% just after several weeks of being exploited in such a way.
How did I get \”5.exe coin miner virus?
Coin miners are spread through different ways, but their main sources are malicious banners and programs from dubious sources
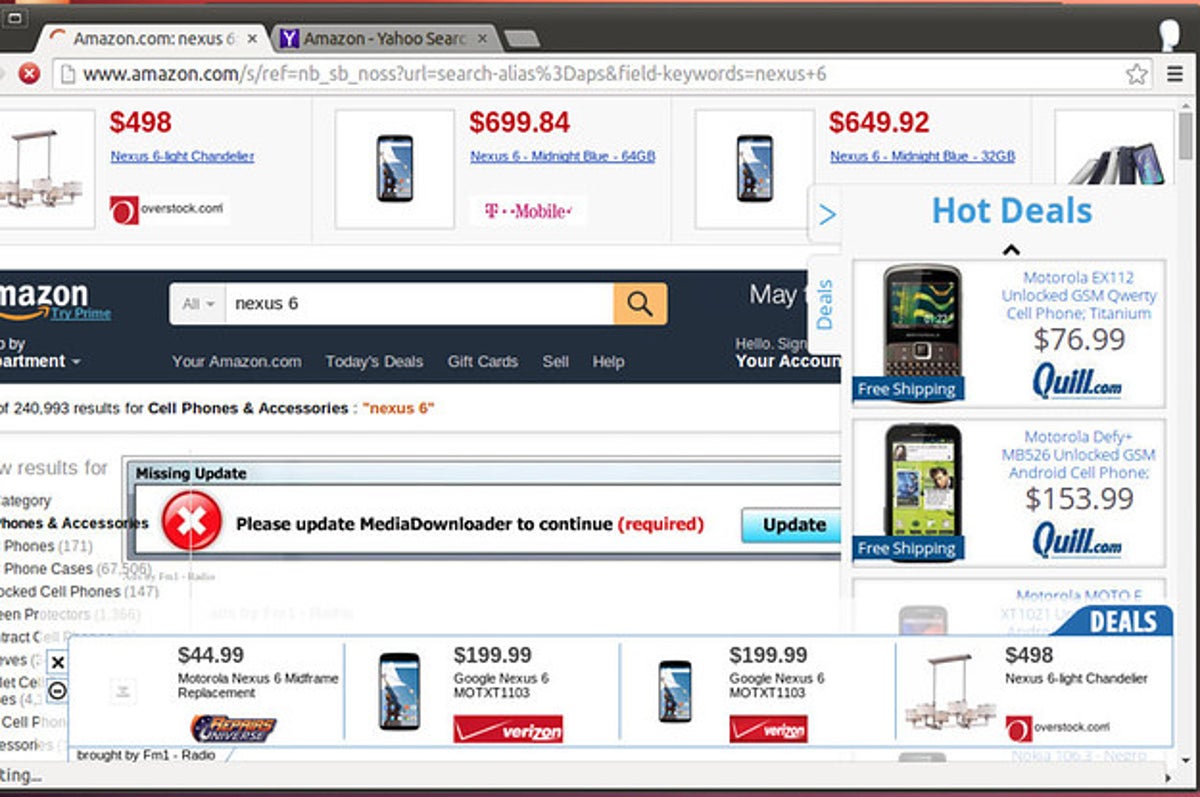
The example of malicious banners you can see in the Internet
One more way you could get this thing on your PC is by downloading it from the suspicious site as a part of a program. People that spread hacked variants of favored programs (which do not need the license key) have small chances to get paid. For this reason, there is a very big temptation to add malware to the final package of the hacked app and acquire a coin for each setup. Before criticizing these people for hacking and malware spreading, ask yourself – is it alright to avoid paying for the program in this manner? It is more affordable to pay $20-$30 one time than to pay a much bigger sum for antivirus program as well as new parts for your PC.
How to remove the \”5.exe miner from my PC?
The best way to get rid of this coin miner virus is to use anti-malware software
Booting the PC into Safe Mode with Networking
Press the Start button, then choose Power, and click on Reboot while holding the Shift key on the keyboard.
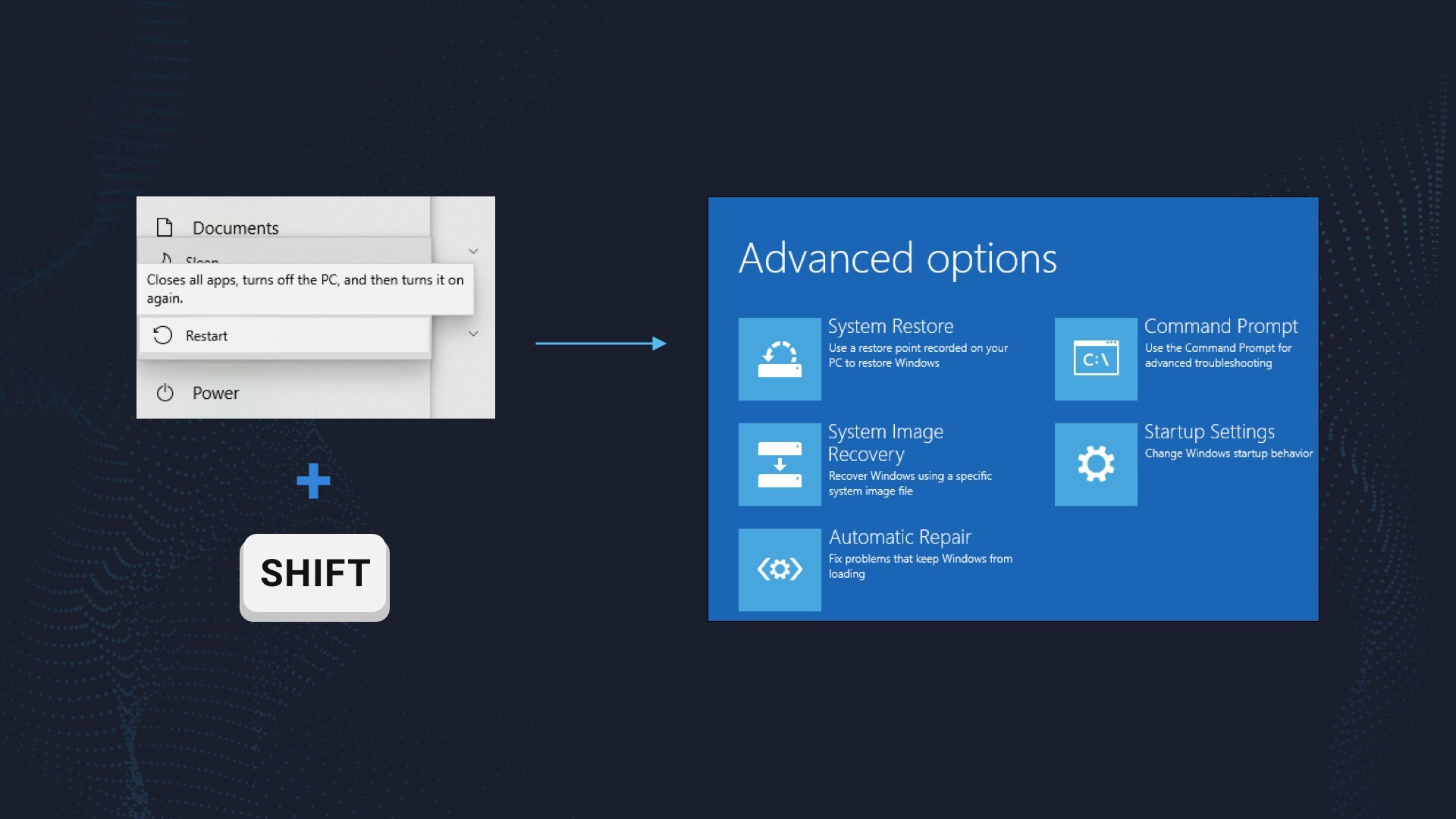
Windows will reboot into recovery mode. In that mode, choose Troubleshoot→ Startup Settings→ Safe Mode with Networking. Press the corresponding button on your keyboard to choose that option.
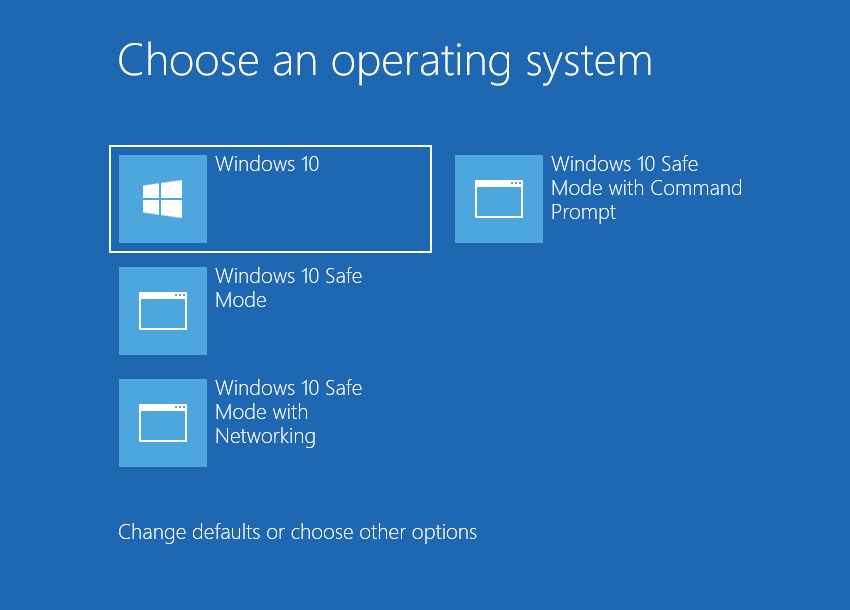
When your computer is in Safe Mode, all third-party software, just like the majority of non-crucial system components, are not started with the system start. That allows you to clean the PC without dealing with high processor usage of the coin miner.
References
- Read about why Monero and DarkCoin are so popular amongst cybercriminals.
- About unwanted effects for GPUs in the process of cryptomining.


Leave a Comment