Last fall, information security experts drew attention to the STOP ransomware (Djvu), to which then were released decoders. However, now IS experts report about appearance of malicious Zorab decryptor, which does not help ransomware victims, but re-encrypts files.
The STOP ransomware (Djvu), according to ID Ransomware, created by renowned information security expert Michael Gillespie, turned out to be one of the most active threats of the past year, along with Ryuk, GandCrab and Sodinkibi.Back then, it was reported that Ransomware ID received approximately 2,500 messages about ransomware attacks per day, but about 60-70% of them are messages about STOP ransomware attacks, which leaves other ransomware far behind.
While ransomware operations such as Maze, REvil, Netwalker, and DoppelPaymer get wide media attention due to their high worth victims, another ransomware called STOP Djvu is infecting more people then all of them combined on a daily basis. The lack of attention is explained by the fact that this ransomware mostly affects home users infected through adware bundles pretending to be software cracks”, — writes Bleeping Computer magazine.
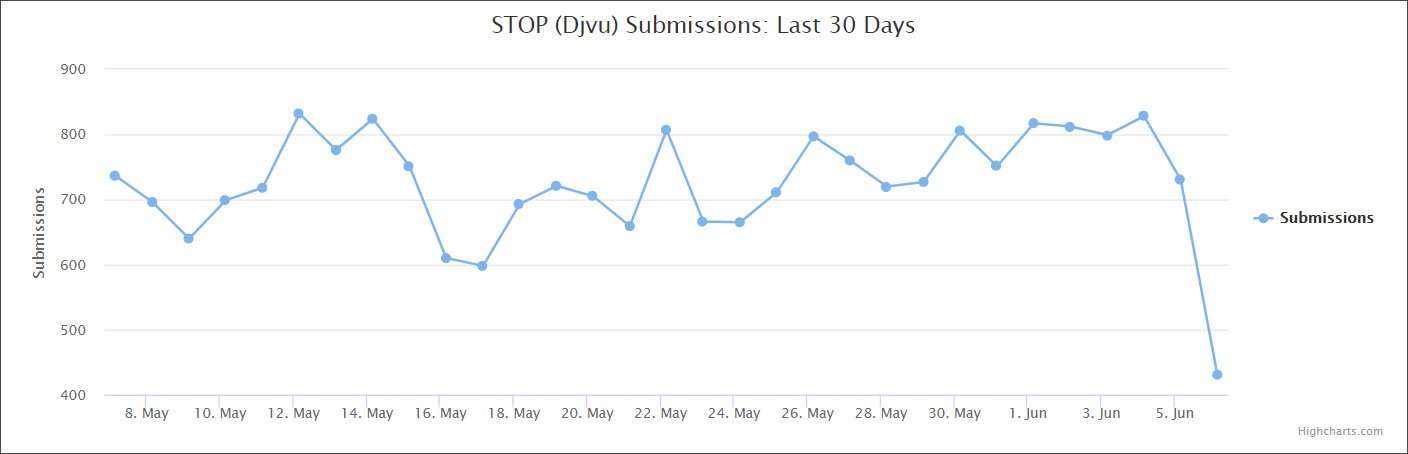
Currently, Ransomware ID still receives about 600 STOP infection messages per day.
Last year, Emsisoft and Michael Gillespie released a free utility to decrypt data affected by STOP ransomware attacks. The tool developed by Emsisoft worked against 148 out of 160 variations of the encryptor, so it could help approximately 70% of the victims.
Now, Bleeping Computer and MalwareHunterTeam are warning that unknown attackers have created a ransomware that masquerades as the very free utility from Emsisoft. Malware named is Zorab: a fake utility re-encrypts all the data of a victim who has already suffered from a STOP attack.
When a user enters its data into a fake decryptor and clicks “Start Scan”, the program extracts another executable file crab.exe and saves it in the% Temp% folder. This file is the basis of Zorab, which immediately begins to encrypt files on the computer again, adding the .ZRB extension to them.
As a result, only a ransom note is left unencrypted on the injured machine, containing instructions on how to contact the malware operators to receive instructions for payment.
The ransomware will also create ransom notes named ‘–DECRYPT–ZORAB.txt.ZRB’ in each folder that a file is encrypted. This note contains instructions on how to contact the ransomware operators for payment instructions”, — write Bleeping Computer journalists.
Researchers strongly discourage Zorab victims from paying attackers and write that they are already analyzing a new malware.
Please read our recommendations on how to decrypt Stop (Djvu) ransomware infected files and not fall for another trick of cybercriminals.


Leave a Comment