Yts.mx is one of the many torrent websites. These websites are unsafe for downloading software, files, or other content as they are frequently exploited by cybercriminals to distribute harmful programs. Moreover, downloading copyrighted content through torrent web pages is illegal.
Research indicates that this particular website utilizes deceptive advertising networks, which redirect visitors to questionable and potentially malicious pages.
In most cases, websites employing deceptive advertising networks lead to untrustworthy pages that promote potentially unwanted applications (PUAs) or even malicious software. These PUAs include browser hijackers, adware, and dangerous malware such as ransomware and Trojan-type software.
Ransomware encrypts victims’ files, denying them access, and demands payment for decryption tools that can only be obtained from the cybercriminals responsible. Trojans are malicious programs that often infect computers with other harmful software, causing a chain of infections.

Torrent yts.mx site
What is yts.mx?
| Site | Yts.mx |
| Hosting | United States, San Francisco |
| Infection Type | Adware, Push notifications, Unwanted Ads, Pop-up Ads |
| IP Address | 104.26.0.60 |
| Symptoms | Experiencing advertisements that are unrelated to the websites you are visiting. Intrusive pop-up ads disrupting your browsing experience. Noticeably slower internet browsing speed. |
| Fix Tool |
To remove possible virus infections, try to scan your PC
|
It’s important to note that yts.mx may also open various scam websites, such as Mr Beast Giveaways or Your computer is disabled which aim to deceive visitors into providing personal information, installing unwanted software, or making payments for dubious programs.
During the research, it was observed that yts.mx redirected users to the download page of ExpressVPN software and a suspicious address, velocecdn.com.
To protect yourself from unwanted downloads/installations of PUAs and malicious programs, avoid falling victim to rogue web pages, and prevent other potential issues, it is strongly advised not to visit yts.mx or any other torrent websites that employ deceptive advertising networks. Additionally, torrents are frequently used to propagate malicious programs.
Other examples of torrent websites include 1337x.to, rarbg, and limetorrent. These websites commonly display dubious advertisements and open untrusted sites that advertise PUAs, deceive visitors into installing harmful software, or request sensitive information.
Therefore, it is crucial never to trust these websites. If your browser automatically opens suspicious pages, it is likely that a PUA has already been installed on your browser and/or operating system.
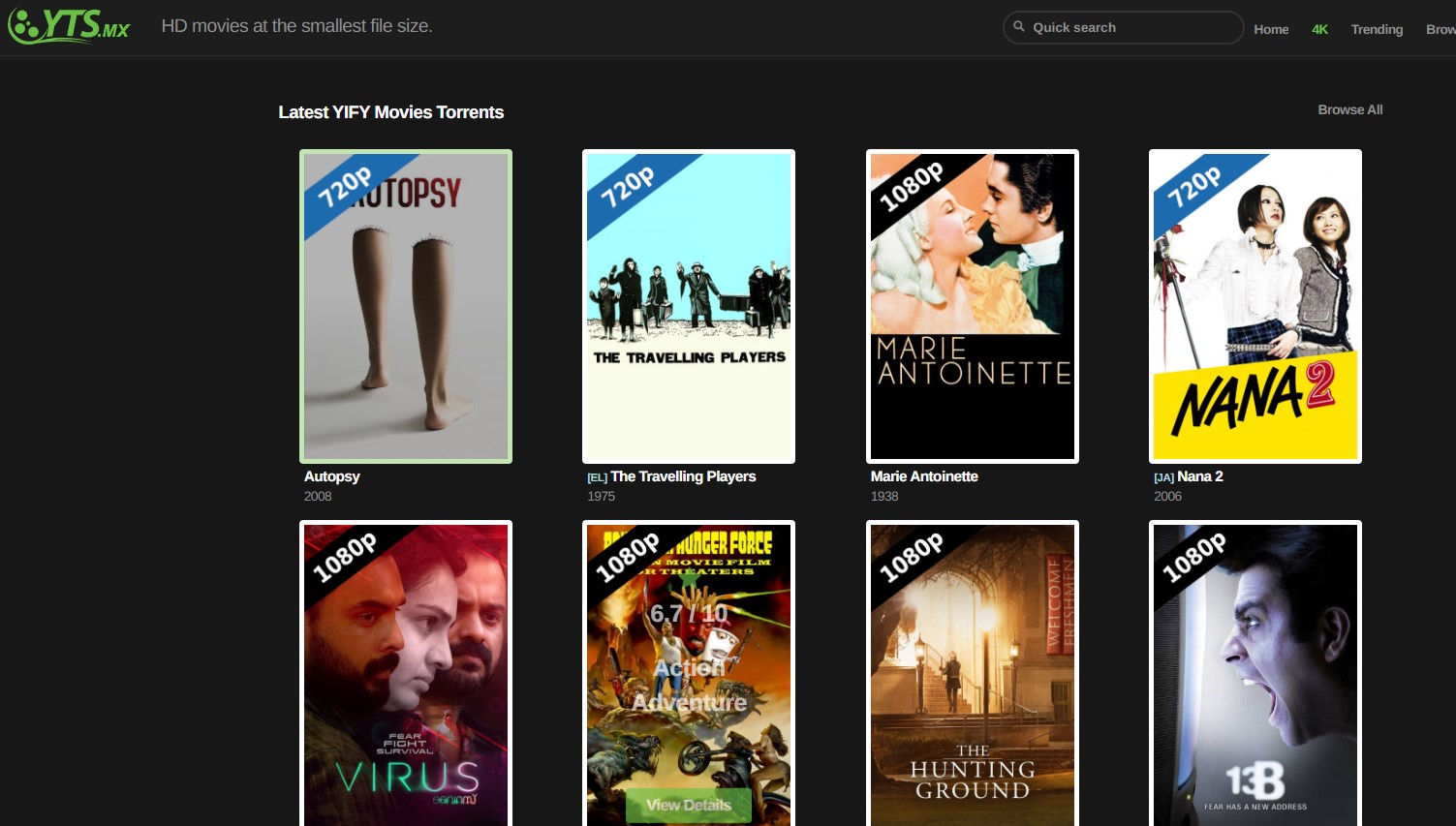
yts.mx torrents
How was adware installed on my computer?
Adware is commonly distributed through a method called “bundling,” where it is included as an “additional offer” in the setup of other programs. These offers to download and/or install potentially unwanted apps are usually presented in options or settings such as “Advanced” or “Custom”.
Users have the option to decline these offers before completing the download/installation process. However, many users overlook or neglect to check these settings, inadvertently allowing PUAs to infiltrate their systems. In some cases, unwanted downloads/installations can occur when users click on ads that execute certain scripts.
How to prevent the installation of potentially unwanted applications
It is crucial to avoid using Peer-to-Peer networks (eMule, torrent clients), unofficial or dubious websites, third-party downloaders, installers, and other unreliable channels for downloading or installing software. These platforms are frequently exploited for the distribution of PUAs and even malicious programs.
Always download software and files from official websites or through direct links. Before completing the download and installation process, carefully review all settings such as “Advanced,” “Manual,” or “Custom” and decline any offers to download or install unwanted software.
Avoid clicking on intrusive ads that appear on dubious pages, as they can lead to untrusted websites or trigger scripts that initiate the download and installation of unwanted applications. Remove all unwanted, suspicious, and unfamiliar apps, including extensions, add-ons, and plug-ins, from your browser.
How to remove the Yts.mx pop-ups with related malware?

Frequently Asked Questions
The less time is gone after the Yts.mx pop-up spam and/or malware infiltration, the less the chances of potential infiltration of far more critical destructive tool. Virus distributors are ready for whatever to receive their profit, and the more time is gone – the extra confident they are. And also, no matter which the anti-malware program you are utilizing, you need to remember about so-called “internet hygiene”. Do not download and install records from untrusted webpages, stop making use of cracked applications, stop seeing websites that have lots of dubious promotions. Every one of these easy, as well as understandable principles can help you to forget about malware attacks and Yts.mx pop-ups in your browser.


Leave a Comment