XWorm is a dangerous remote access Trojan (RAT) that grants cybercriminals unauthorized access and control over victims’ computers. Capable of stealing sensitive data, running ransomware, and keylogging, it spreads through deceptive emails posing as business matters, containing attachments that lead to harmful downloads when opened.
What is XWorm virus?
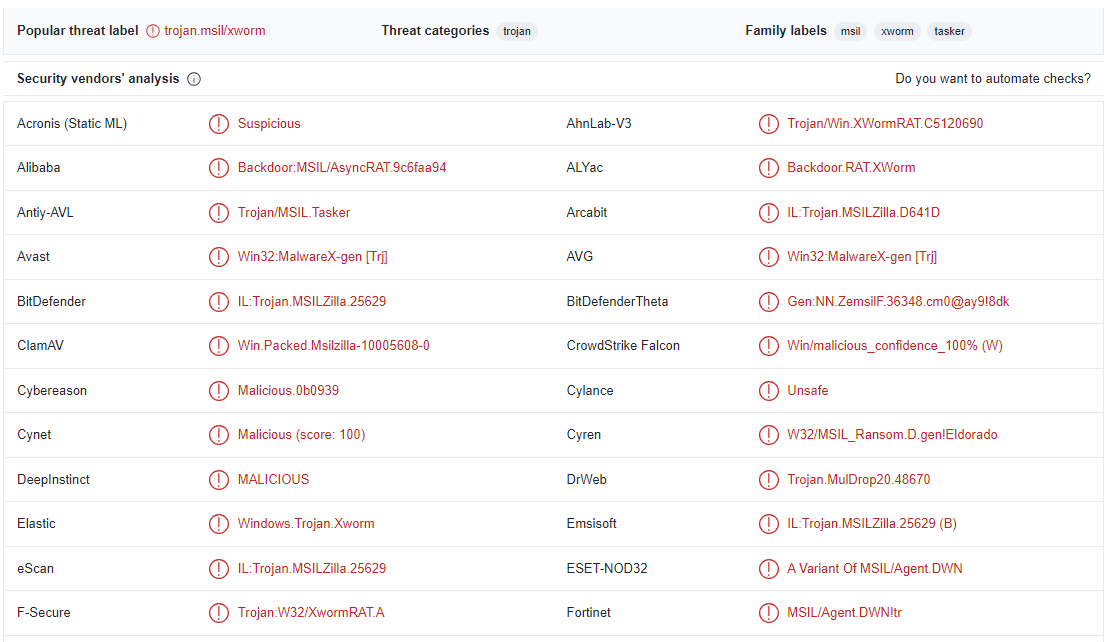
XWorm is a remote administration/access Trojan (RAT), that turned up recently. This malware allows cybercriminals to gain unauthorized access and full control over unsuspecting victims’ computers. It is a highly sought-after tool, being sold by its developers on the black market for a just $400.
Remote access trojans is a class of malware that aims at establishing a remote connection to the infected system. They are often confused with backdoor, and for a reason – their functionality is nearly identical. However, backdoors rarely offer direct connection to the infected system, granting the ability to execute remote commands instead. RATs, on the other hand, act more like a remote access utility, such as TeamViewer, so its master can literally roam across the system on par with its owner. To top this up, remote access trojans also include stealer and spyware capabilities – as built-in functionality or attachable modules.
| Name | XWorm |
| Detection | XWorm |
| Similar behavior | Adware, Behavior, Trojan |
| Damage | Exploits your hardware to mine cryptocurrencies without your permission. |
XWorm Functionality Analysis
The capabilities of XWorm are alarmingly wide. One of its primary functions is to pilfer crucial system information from the victim’s computer. This data provides attackers with valuable insights into the target’s setup, enabling them to launch more sophisticated and tailored attacks. Beyond this, XWorm boasts an array of malicious actions it can execute on the compromised system. It can manipulate files, access the victim’s webcam and microphone, open URLs, execute shell commands, and even manage files at will. This complete control over the victim’s system grants the attackers unfettered access to their personal and sensitive data.
The list of XWorm’s capabilities doesn’t end there. It can also edit or manage vital components like User Account Control (UAC), Registry Editor, Task Manager, Firewall, and system updates. It can go as far as invoking the dreaded Blue Screen of Death (BSoD), rendering the victim’s system inoperable. Moreover, XWorm is designed to target specific web browsers like Chromium and Firefox, allowing it to plunder passwords, cookies, credit card details, bookmarks, downloads, keywords, history, and autofill data. This information provides a goldmine for cybercriminals, enabling them to engage in identity theft and other malicious activities.
XWorm can also extract Telegram session data, Discord tokens, WiFi passwords, Metamask and FileZilla data, and even log keystrokes to capture sensitive information. Another important functionality of this malware is keylogging. It involves capturing and recording every keyboard input made by users on an infected system. This process enables the malware to gather credentials and stuff, circumventing modern security features like traffic encryption. Unbeknownst to the victim, this sensitive information is stealthily transmitted to the attacker’s command and control server.
The ability to hijack and spoof clipboard contents is an icing on the cake. This stealthy tactic involves the malware meticulously monitoring and intercepting data copied to the victim’s clipboard. Its primary focus is on cryptocurrency wallet addresses. When a victim copies a Bitcoin, Ethereum, or any other cryptocurrency wallet address, XWorm instantly detects the action and performs a swap. Thus, instead of the intended crypto wallet the victim pastes – and sends money to – the wallet of cybercriminals.
Real-world usage
In the wild, the XWorm RAT is mostly used as a persistence establishing tool in cyberattacks on corporations. After the initial reconnaissance of the environment, hackers introduce ransomware and stealers. You may probably know the rest – the company have its data leaked, files encrypted, and a huge ransom for reverting all this mess demanded.


Leave a Comment