Sodinokibi is most likely being dispersed by attackers associated with those that dispersed the well known GandCrab ransomware family1, which is supposed to be retired soon according to the underground discussion forum where GandCrab initially appeared.
In this tutorial I will try to help you remove Sodinokibi ransomware.
What is “Sodinokibi”?
Sodinokibi can be correctly identify as a ransomware infection.
Sodinokibi ransomware exploits an Oracle WebLogic vulnerability (CVE-2019-2725)2 to gain access to the target’s machine. Once it’s in, the malware attempts to implement itself with elevated user legal rights in order to access all files as well as resources on the system with no constraint.
Sodinokibi attempts to stay clear of contaminating computer systems from Romania, Russia, Ukraine, Belarus, Estonia, Latvia, Lithuania, Armenia, Georgia, Iran, Syria, Azerbaijan, Kazakhstan, Kyrgyzstan, Tajikistan, Turkmenistan, Uzbekistan most of them are formerly part of the USSR. This ransomware pressure utilizes AES and also Salsa20 algorithm3 to encrypt individual’s data, AES is utilized to encrypt session secrets and also data that is sent to the control server, individual data are encrypted using Salsa20 security.
Sodinokibi uses an Elliptic-curve Diffie-Hellman crucial exchange algorithm to create and also proliferate encryption keys.
Once it infiltrates a device, it erases every one of the documents in the back-up folder.
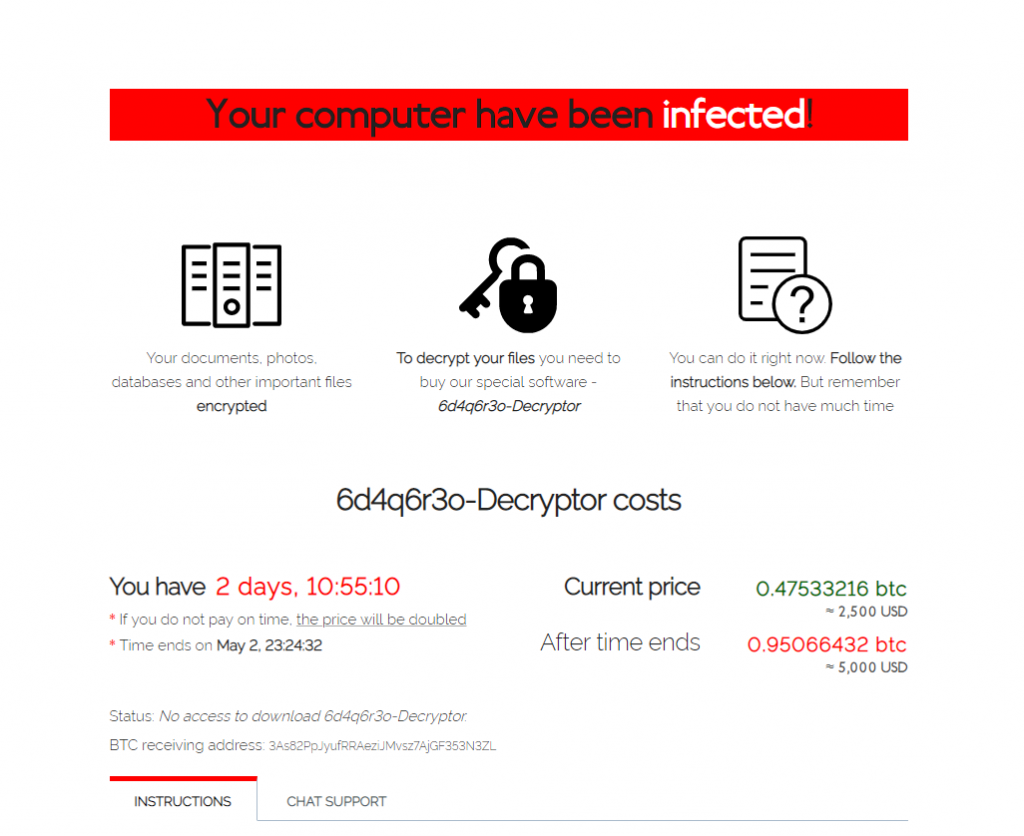
Presently, the ransomware needs 0.32806964 BTC (≈ $2500) to reclaim accessibility to the encrypted documents. They declare that this quantity must be paid within four days or the ransom demand will be increased.
Here is a summary for the Sodinokibi :
| Ransomware family | REvil ransomware |
| Extension | random |
| Ransomware note | readme.txt |
| Ransom | From $2500 to $5000 (in Bitcoins) |
| Detection4 | Ransom.Phobos, Ransomware.Sodinokibi, Trojan.Multi |
| Symptoms | Most of your files (photos, videos, documents) have a random extension and you can’t open it |
| Fix Tool | See If Your System Has Been Affected by Sodinokibi ransomware |
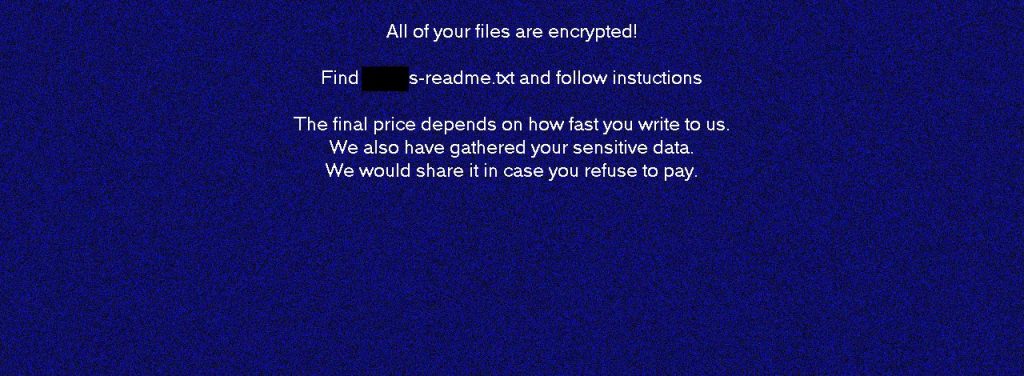
REvil/Sodinokibi version 2.2 add a new text in wallpaper:
All of your files are encrypted! Find readme.txt and follow instructions* The final price depends on how fast you write to us. We also have gathered your sensitive data. We would share it in case you refuse to pay.
This text asking payment is for get files back via decryption key:
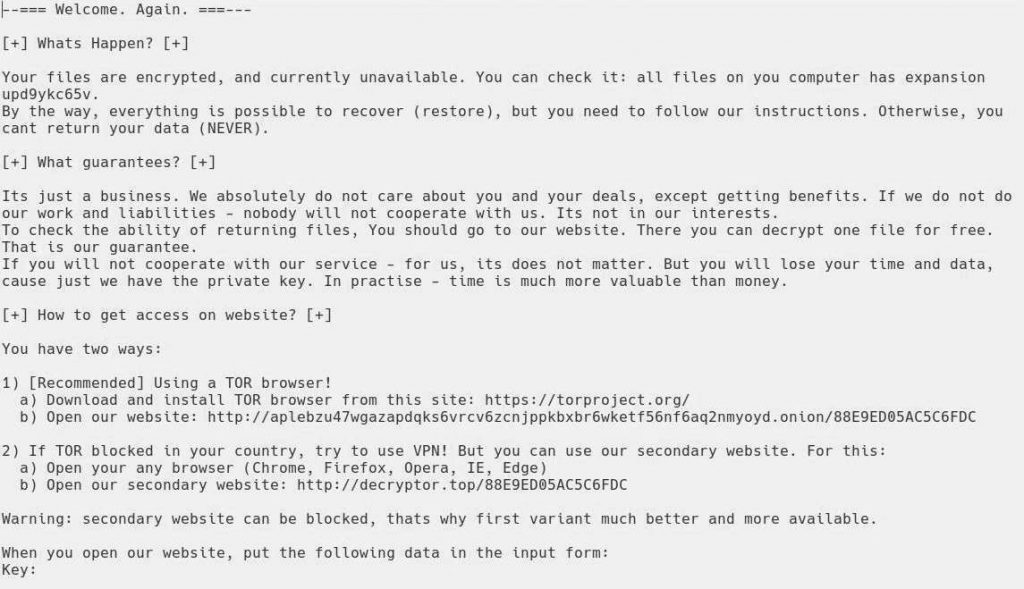
The scary alert demanding from users to pay the ransom to decrypt the encoded data contains these frustrating warnings
The cryptography algorithm used by Sodinokibi is AES-256. So, if your documents got encrypted with a specific decryption key, which is totally and there are no other copies. The sad reality is that it is impossible to recover the information without the unique key available.
In case if Sodinokibi worked in online mode, it is impossible for you to gain access to the AES-256 key. It is stored on a remote server owned by the criminals who promote the Sodinokibi virus.
Do not pay for Sodinokibi!
Please, try to use the available backups, or Decrypter tool
_readme.txt file also indicates that the computer owners must get in touch with the Sodinokibi representatives during 72 hours starting from the moment of files where encrypted. On the condition of getting in touch within 72 hours users will be granted a 50% rebate, thus the ransom amount will be minimized down to $490). However, stay away from paying the ransom!
I definitely advise that you do not contact these frauds and do not pay. The one of the most real working solution to recover the lost data – just using the available backups, or use Decrypter tool.
The peculiarity of all such viruses apply a similar set of actions for generating the unique decryption key to recover the ciphered data.
Thus, unless the ransomware is still under the stage of development or possesses with some hard-to-track flaws, manually recovering the ciphered data is a thing you can’t really perform. The only solution to prevent the loss of your valuable data is to regularly make backups of your crucial files.
Note that even if you do maintain such backups regularly, they ought to be put into a specific location without loitering, not being connected to your main workstation.
For instance, the backup may be kept on the USB flash drive or some alternative external hard drive storage. Optionally, you may refer to the help of online (cloud) information storage.
Needless to mention, when you maintain your backup data on your common device, it may be similarly ciphered as well as other data.
For this reason, locating the backup on your main PC is surely not a good idea.
How I was infected?
Sodinokibi has a various methods to built into your system. But it doesn’t really matter what concrete way was used in your case.
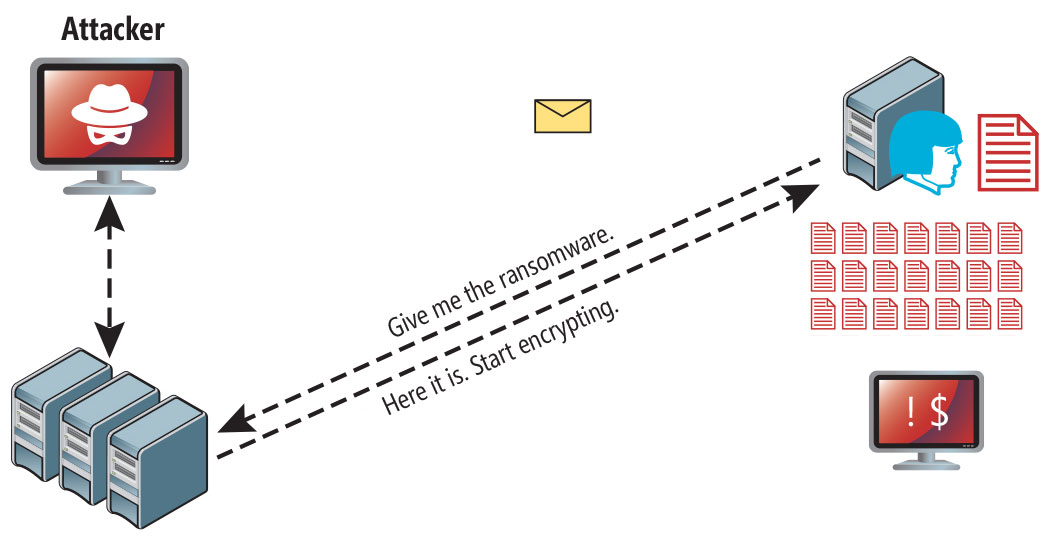
Sodinokibi ransomware attack following a successful phishing attempt.
- hidden installation along with other apps, especially the utilities that work as freeware or shareware;
- dubious link in spam emails leading to the Sodinokibi installer
- online free hosting resources;
- using illegal peer-to-peer (P2P) resources for downloading pirated software.
There were cases when the Sodinokibi virus was disguised as some legitimate tool, for example, in the messages demanding to initiate some unwanted software or browser updates. This is typically the way how some online frauds aim to force you into installing the Sodinokibi ransomware manually, by actually making you directly participate in this process.
Surely, the bogus update alert will not indicate that you are going to actually inject the Sodinokibi ransomware. This installation will be concealed under some alert mentioning that allegedly you should update Adobe Flash Player or some other dubious program whatsoever.
Of course, the cracked apps represent the damage too. Using P2P is both illegal and may result in the injection of serious malware, including the Sodinokibi ransomware.
To sum up, what can you do to avoid the injection of the Sodinokibi ransomware into your device? Even though there is no 100% guarantee to prevent your PC from getting damaged, there are certain tips I want to give you to prevent the Sodinokibi penetration. You must be cautious while installing free software today.
Make sure you always read what the installers offer in addition to the main free program. Stay away from opening dubious email attachments. Do not open files from the unknown addressees. Of course, your current security program must be always updated.
The malware does not speak openly about itself. It will not be mentioned in the list of your available programs. However, it will be masked under some malicious process running regularly in the background, starting from the moment when you launch your computer.
The message by the Sodinokibi ransomware states the following frustrating information:
Sodinokibi Ransomware Note
The image below gives a clear vision of how the files with Sodinokibi infection
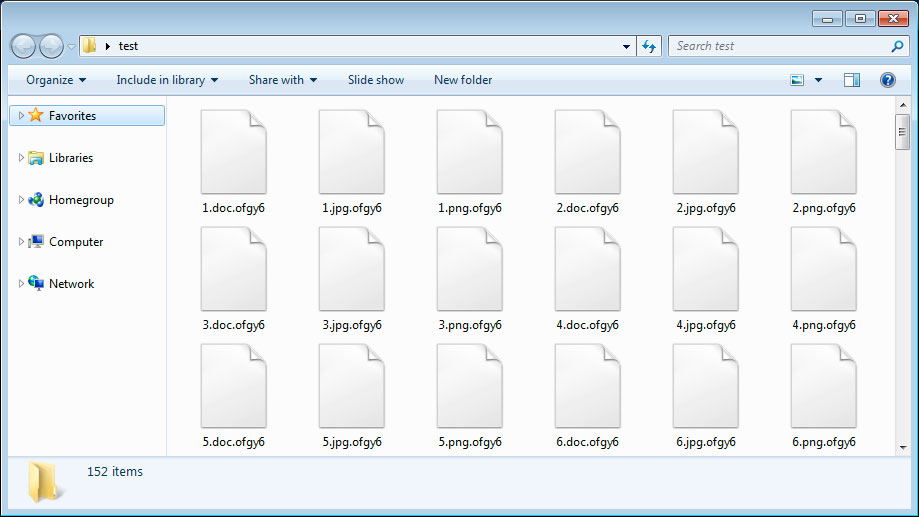
Sodinokibi files
How to remove Sodinokibi virus?
In addition to encode a victim’s files, the Sodinokibi infection has also started to install the Azorult Spyware on system to steal account credentials, cryptocurrency wallets, desktop files, and more.
Reasons why I would recommend GridinSoft5
Download Removal Tool.
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

How to decrypt Sodinokibi ransomware?
There is no free decrypter available for this ransomware and the only choice is to use the decryption service provided by the attackers, which can be accessed by following the instructions in the ransom note.
References
- Ransomware GandCrab: https://krebsonsecurity.com/2019/07/whos-behind-the-gandcrab-ransomware/
- Vulnerability CVE-2019-2725: https://www.oracle.com/security-alerts/alert-cve-2019-2725.html
- About Salsa20: https://en.wikipedia.org/wiki/Salsa20
- Encyclopedia of threats.


Leave a Comment