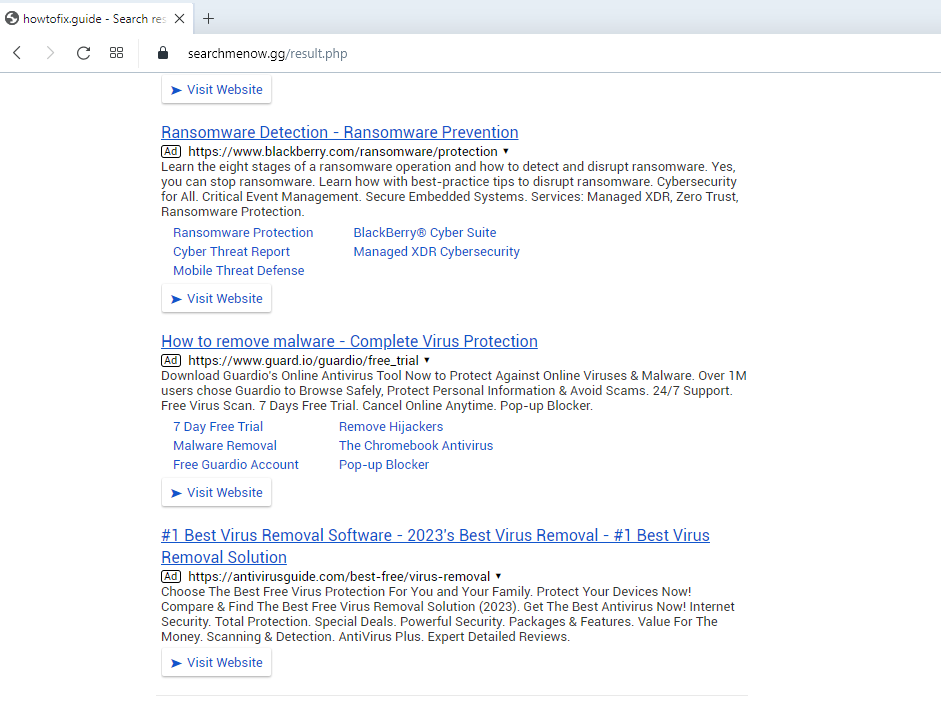
We identified SearchMeNow.gg as a dubious search engine during our testing. Our team came across searchmenow.gg after deliberately installing a browser hijacker on a web browser. It is crucial to note that Chrome browsers can incorporate the “Managed by your organization” feature as part of applications designed to promote searchmenow.gg.
Overview of searchmenow.gg
Searchmenow.gg should not be trusted for several reasons when it comes to the search results it presents. Firstly, searchmenow.gg falls into the category of shady search engines, raising doubts about its reliability and credibility. This raises concerns about the accuracy and relevance of the search results it delivers.
In addition, searchmenow.gg is linked to browser hijackers like the “Apps” browser hijacker, which are notorious for altering browser settings without the user’s consent. These unauthorized modifications can manipulate search results, potentially promoting suspicious or deceptive websites. This compromises the integrity and trustworthiness of the search engine’s outcomes.
Taking into account these factors, it is advisable to exercise caution and avoid relying on search results from searchmenow.gg, as they may not provide accurate, unbiased, or trustworthy information. It is worth noting that users are redirected to searchmenow.gg through searchesmia.com.
Upon installation of the Searchmenow.gg browser hijacker, users may experience the following common symptoms:
- Search queries in the browser are redirected through Searchmenow.gg.
- An unwanted browser extension or program is installed on the computer.
Searchmenow.gg actively deceives users and takes control of their web browsers while manipulating their search queries. It masquerades as a legitimate search engine, luring users into installing harmful browser extensions or browser hijackers.
Once users install these extensions or hijackers, their browser settings get modified, specifically redirecting all search queries through Searchmenow.gg. Consequently, when users enter a search term in their browser’s search bar, the queries no longer go directly to the intended search engine but instead get routed through Searchmenow.gg.
The primary objective of this malicious activity is to generate traffic and ad revenue for Searchmenow.gg. By intercepting and redirecting users’ search queries, Searchmenow.gg can display targeted advertisements and sponsored search results, thus generating revenue upon user interaction.
Moreover, Searchmenow.gg may collect and store users’ search data, browsing habits, and other personal information. This information can then be utilized for targeted advertising, sold to third parties, or even exploited for nefarious purposes.
It is crucial to note that Searchmenow.gg often appears on users’ computers without their consent and is considered a form of browser hijacking. Users are strongly advised to remove any suspicious browser extensions, reset their browser settings, and use reputable anti-malware software to ensure the complete eradication of Searchmenow.gg and any associated threats.
What are Searchmenow.gg redirect?
Searchmenow.gg Redirect Virus
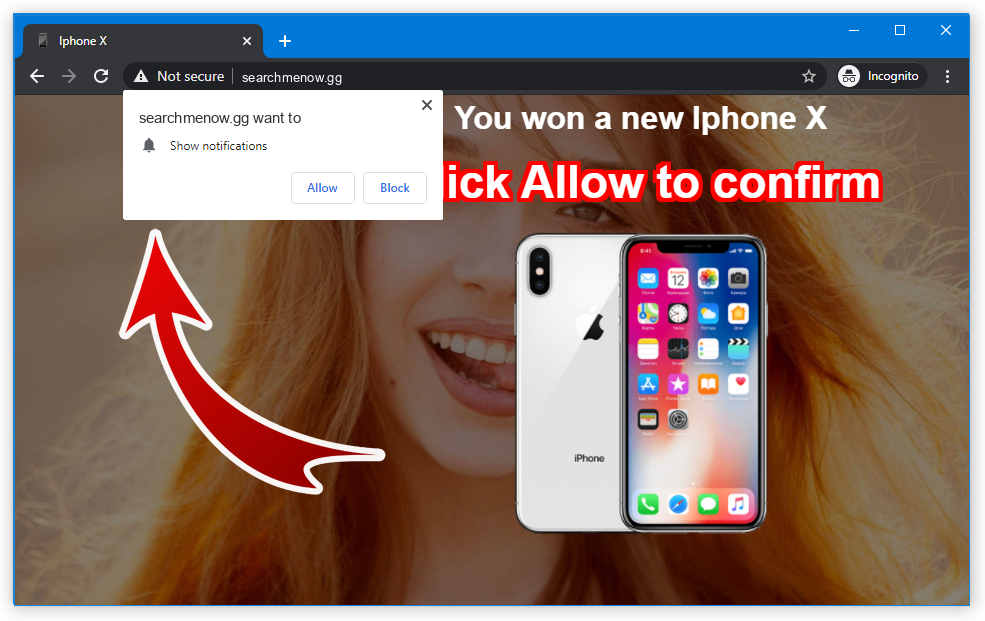
As the pop-up definition goes, these are short and small advertisements that attract your attention to a product they promote. But the difference between regular pop-up advertisements and Searchmenow.gg notifications is the malicious origins of the latter. Common pop-ups are offered for you to enable with a legitimate purpose – notify you about the latest articles, goods for sale and so on. It is an effective approach to help your website to retain visitors and help the interested visitors to have the best price.
Searchmenow.gg Search Hijacker:
| Name | Searchmenow.gg |
| Hosting | AS13335 Cloudflare, Inc. United States, San Francisco |
| IP Address | 172.67.189.157 |
| Malware type | Adware |
| Effect | Unwanted pop-up advertisements |
| Hazard level | Medium |
| Malware source | Apps from third-party websites, ads on dubious websites |
| Similar behavior | Juble, Haffnetwork, Darkmodeforbrowser |
| Removal method |
To remove possible virus infections, try to scan your PC
|
How does this work?
The majority of browsers support turning on push notifications from websites. Sites, on the other hand, can send notifications with the content they want. It may be a promotion of the product or a page published on this website, as well as a promotion of their partner page. As a result, you can see the pop-up from site X, but clicking it will redirect you to site Y – because a referral link to that website was added.
Crooks bear on this ability in their attempt to gain money using illegal advertising. They trick users into allowing the pop-ups, and after that just spread hundreds of banners of anyone they contract with. As you can suppose, no normal organisations will contract with fraudsters. All the Searchmenow.gg push ads you can see lead to other untrustworthy sites. In some cases, the same user may get into a trap of several pop-up spamming web pages, and its browser will turn into a complete mess.
The banners these crooks show are paid under the pay-per-view model. It commonly provides a miserable pay for one viewer, but when you can send ads to a huge number of victims and make it hundreds of times every day – that is a much more significant sum. Despite the majority of such banners giving no result at all, it may still give all the participants a lot of money.
Are Searchmenow.gg pop-up notifications dangerous?
Yes, they are. Initially, they may look safe – just a blinking window that appears from time to time. However, the things this window promotes differ sharply from what you used to see in pop-up ads. Searchmenow.gg website is ruled by fraudsters, who intendedly spread tons of malicious ads in pop-ups. They also don’t follow any manners of advertising and can make sporadic push notifications into a hurricane of banners. For weak systems, that may be enough to cause performance issues. But that is not all troubles these push notifications carry.
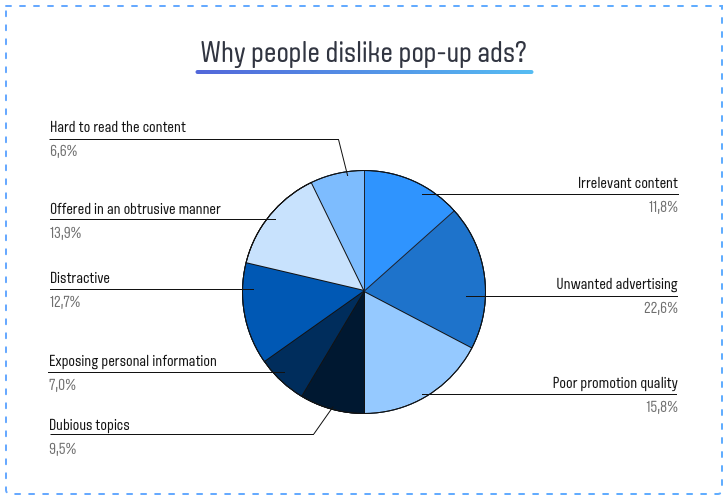
As with any other thing that touches illegal advertising, Searchmenow.gg pop-up advertisements don’t have legit deals to offer. Even though crooks make the banners looking similar to ones from Amazon, Walmart or Ebay, the web page these banners will throw you to are completely different. And these pages may offer you to turn on other pop-ups, install a “useful” program, or pay for a thing at a big discount and never receive it. Let’s leave aside the cases when pop-ups promote phishing pages or straightforward malware. There’s no way these pages will bring you any good, thus interacting with them is a very bad idea. For the same reason, Searchmenow.gg push notifications are not recommended to click on either, and the best solution is to disable them as soon as possible.
How to remove Searchmenow.gg pop-ups?
Initially, you should reset your browser settings. It is possible to do in both manual and automatic manner. The former, obviously, takes more time to complete and can be somewhat complicated if you have never done that. Automated supposes the use of anti-malware programs that can reset all browser settings at once.
Reset your browsers manually
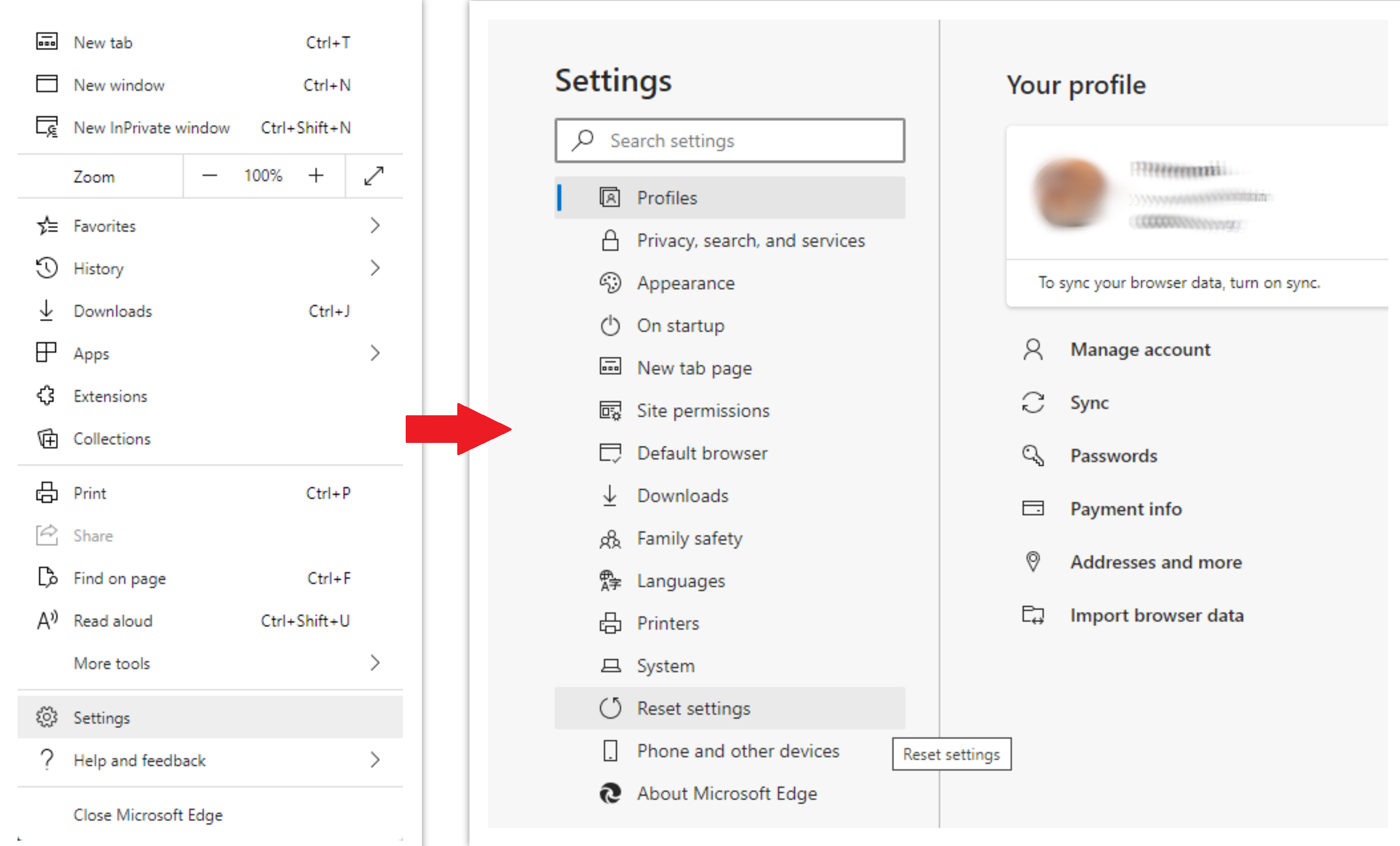
To reset Edge, do the following steps:
- Open “Settings and more” tab in upper right corner, then find here “Settings” button. In the appeared menu, choose “Reset settings” option:
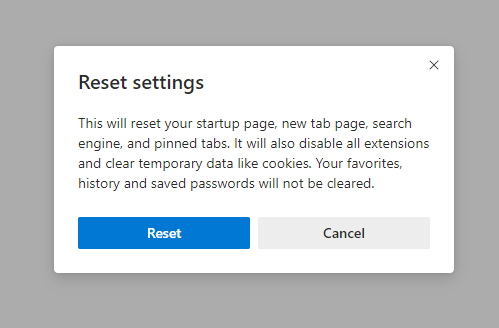
- After picking the Reset Settings option, you will see the following menu, stating about the settings which will be reverted to original:
For Mozilla Firefox, do the next actions:
- Open Menu tab (three strips in upper right corner) and click the “Help” button. In the appeared menu choose “troubleshooting information”:
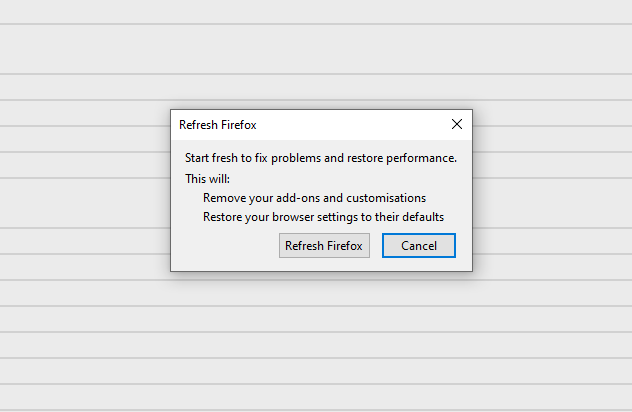
- In the next screen, find the “Refresh Firefox” option:
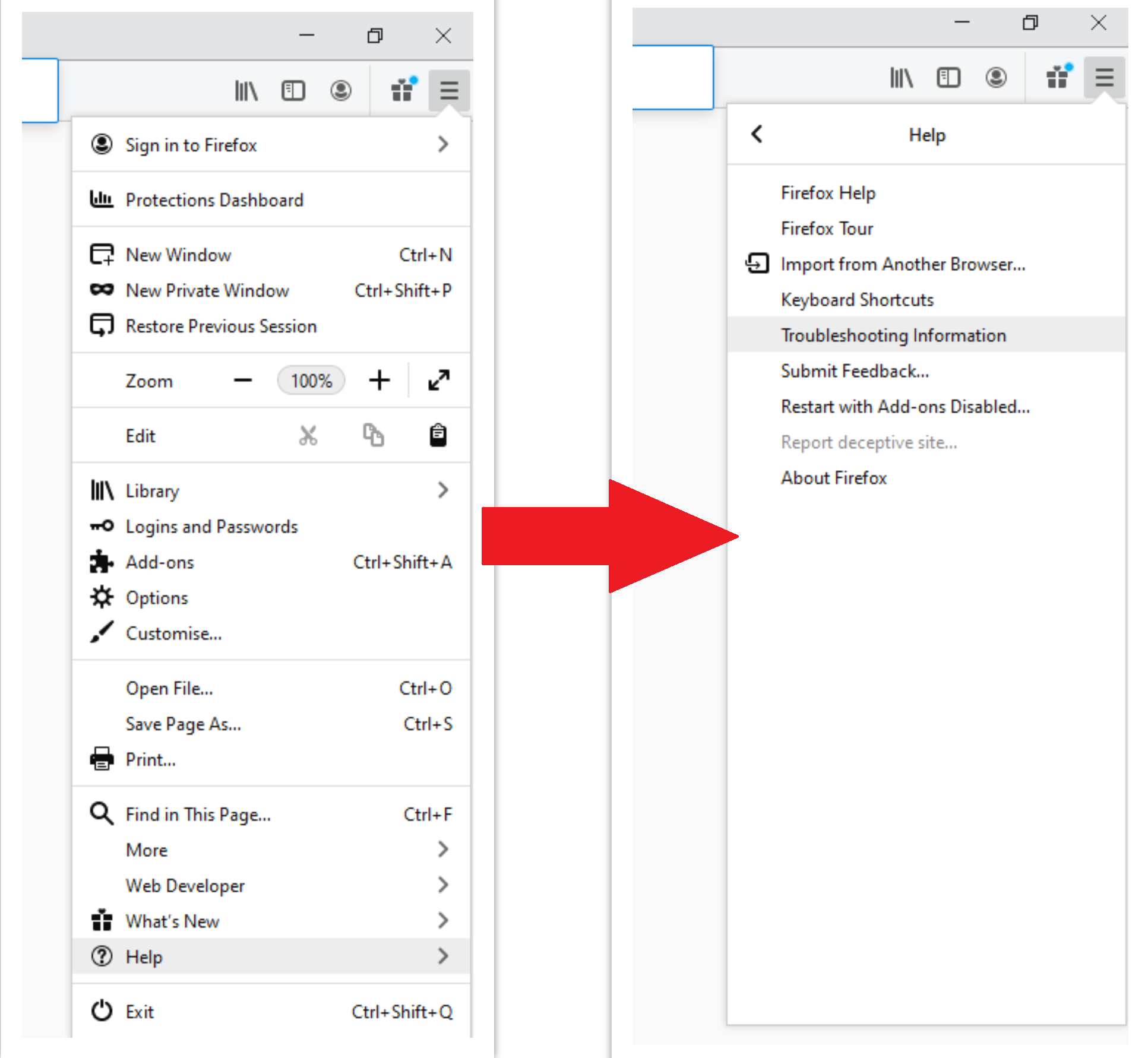
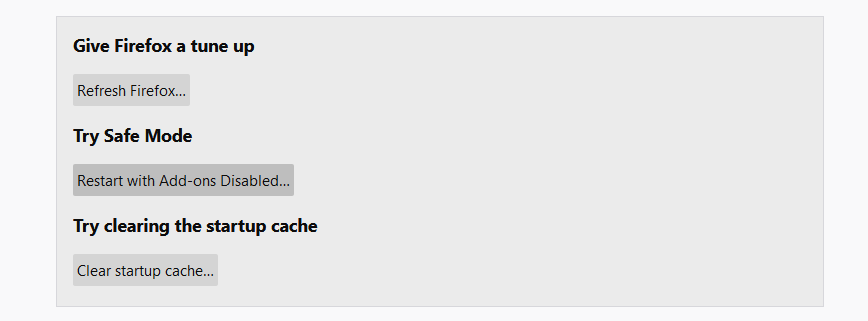
After choosing this option, you will see the next message:
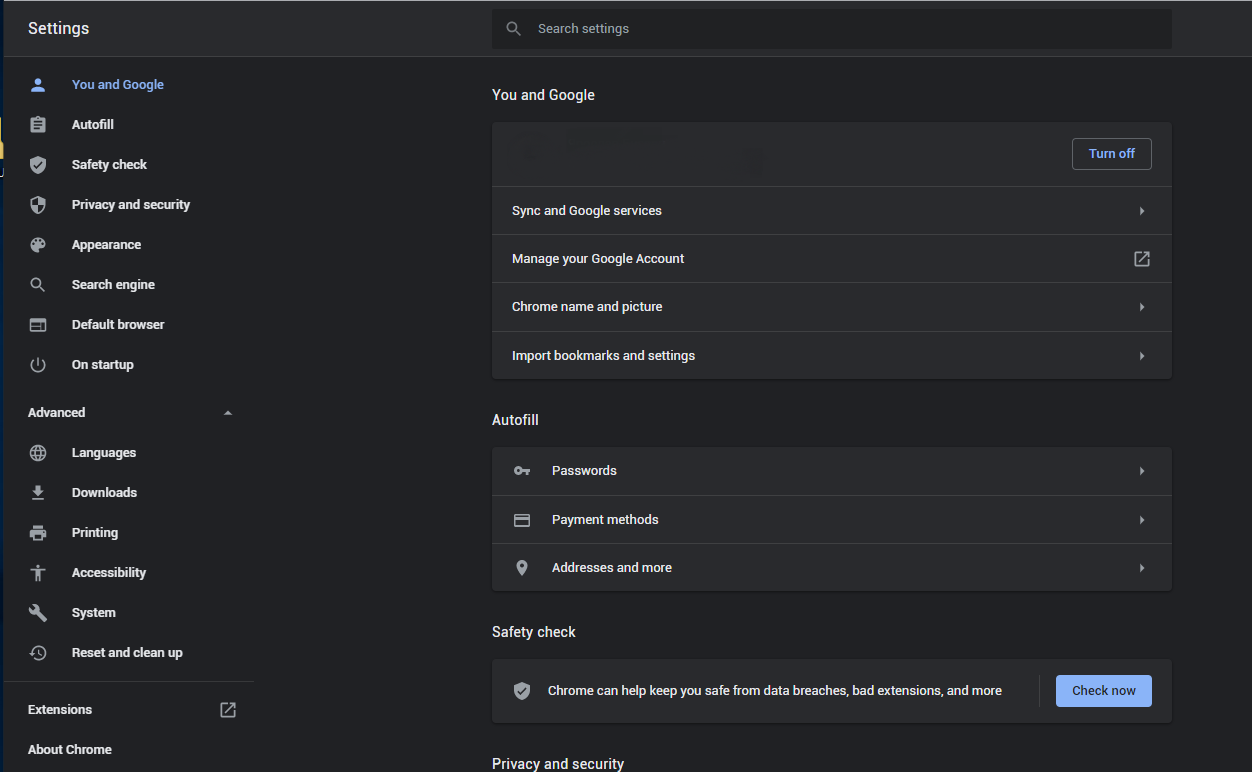
If you use Google Chrome
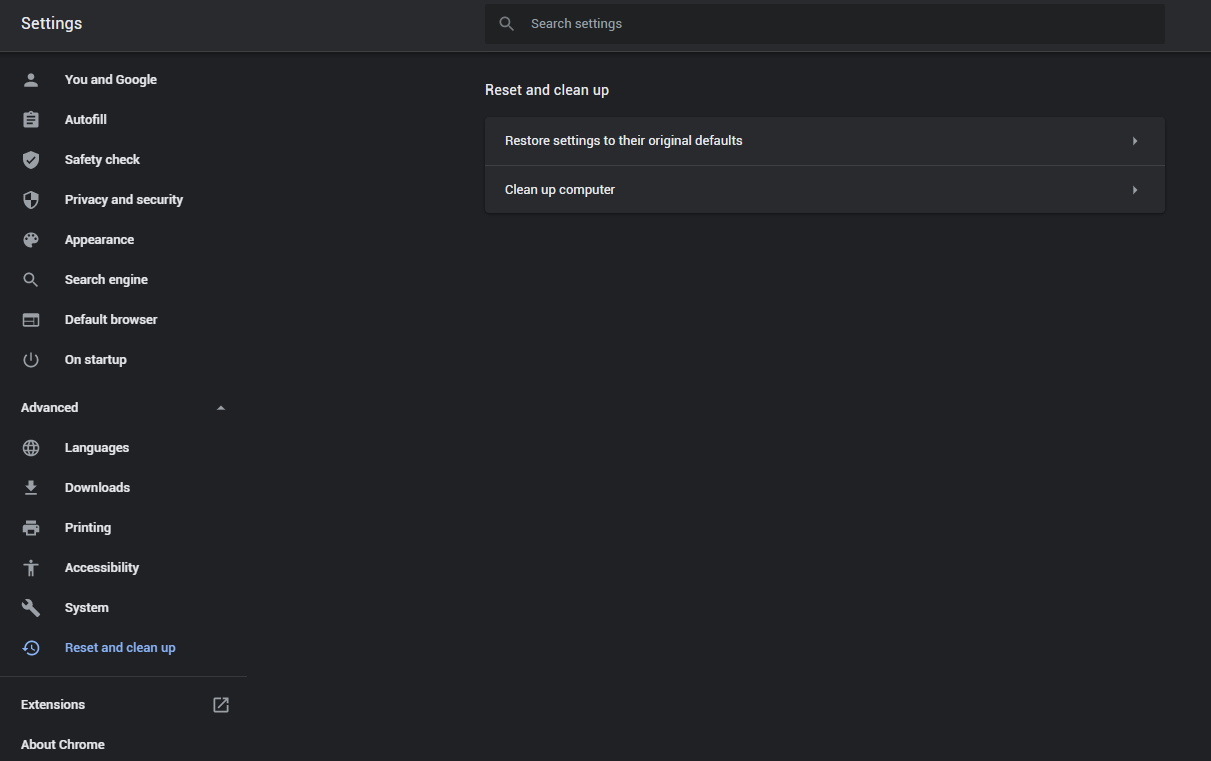
- Open Settings tab, find the “Advanced” button. In the extended tab choose the “Reset and clean up” button:
- In the appeared list, click on the “Restore settings to their original defaults”:
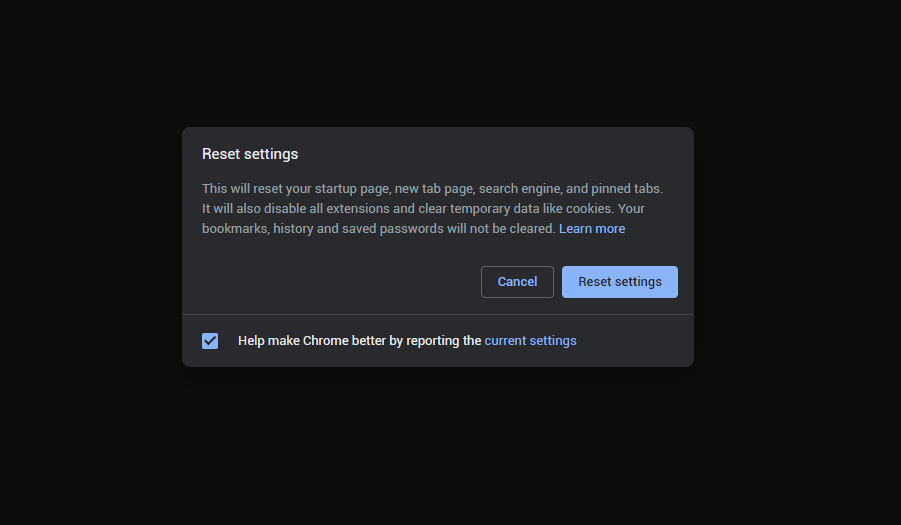
- Finally, you will see the window, where you can see all the settings which will be reset to default:
Opera can be reset in the next way
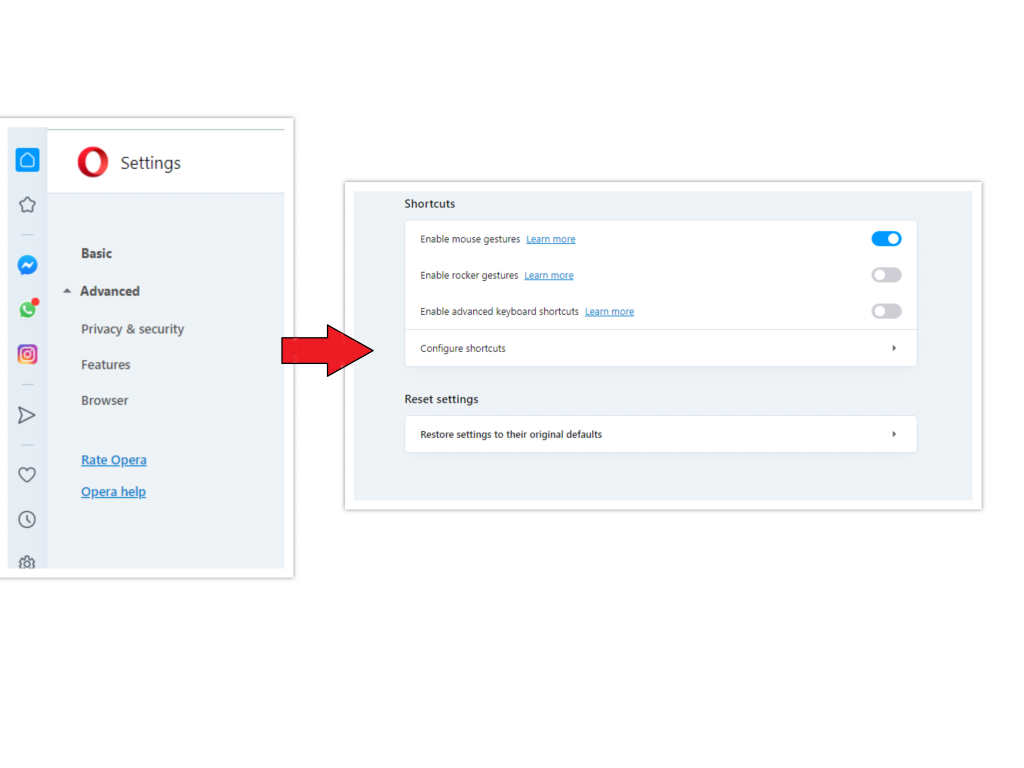
- Open Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click “Advanced” option, and choose “Browser” button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there “Restore settings to their original defaults” option:
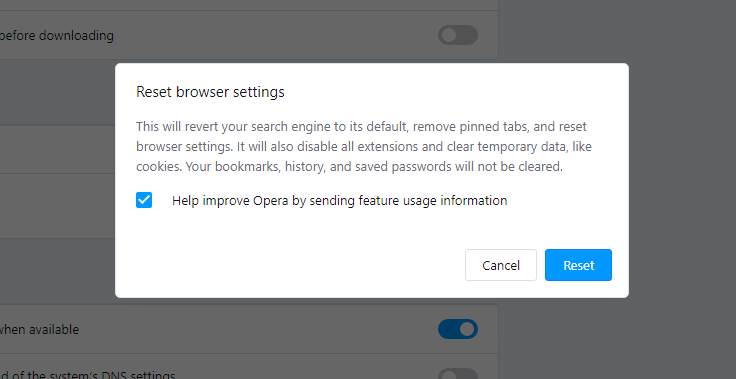
- After clicking the “Restore settings…” button, you will see the window, where all settings, which will be reset, are shown:
When the browsers are reset, you need to ensure that your browser will connect the right DNS while connecting to the site you need. Create a text file titled “hosts” on your pc’s desktop, then open it and fill it with the following lines1:
# Copyright (c) 1993-2006 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handle within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
Find the hosts.txt file in C:/Windows/System32/drivers/etc directory. Rename this file to “hosts.old.txt” (to distinguish it from the new one), and then move the file you created on the desktop to this folder. Remove the hosts.old from this folder. Now you have your hosts file as good as new.
Scan your system for possible viruses
Once the scan is complete, you will see the detections or a notification about a clean system. Proceed with pressing the Clean Up button (or OK when nothing is detected).
Frequently Asked Questions (FAQ)
-
What is searchmenow.gg?
Searchmenow.gg is a search engine that has raised concerns about its reliability and credibility due to its categorization as a shady search engine. It is associated with browser hijackers, which can modify browser settings without user consent.
-
How did we come across searchmenow.gg?
Our team discovered searchmenow.gg while intentionally installing a browser hijacker on a web browser as part of our testing process.
-
What is the “Managed by your organization” feature in Chrome browsers?
The “Managed by your organization” feature is a capability that can be integrated into Chrome browsers by applications aiming to promote searchmenow.gg. This feature may appear when the browser settings have been modified without the user’s knowledge or consent.
-
Why should the search results from searchmenow.gg be treated with caution?
The search results displayed by searchmenow.gg should be approached with caution due to its categorization as a shady search engine and its association with browser hijackers. These factors raise doubts about the accuracy, relevance, integrity, and trustworthiness of the information provided by the search engine.
-
How can searchmenow.gg compromise the integrity of search results?
Searchmenow.gg is associated with browser hijackers that can modify browser settings without user consent. These unauthorized modifications can manipulate search results, potentially promoting suspicious or misleading websites, thereby compromising the integrity and trustworthiness of the search engine’s outcomes.
-
Should I rely on search results from searchmenow.gg?
No, it is advisable to exercise caution and avoid relying on search results from searchmenow.gg. The search engine’s credibility and reliability are questionable, and there are concerns about the accuracy, impartiality, and trustworthiness of the information it provides.
-
How can users be directed to searchmenow.gg?
Users can be directed to searchmenow.gg through searchesmia.com, which serves as a redirecting mechanism to lead users to the search engine.
References
- Official Microsoft guide for hosts file reset.


Leave a Comment