The PUA:Win32/RemComSvc alert, is a sign that your PC has a problem. Allowing it to run may end up with some really bad consequences. Unwanted apps are not as dangerous as regular malware, but is still able to mischief and lead to system instability.
RemComSvc unwanted app can not be called full-fledged malware. However, it has enough marks to state that you will not be pleased with the changes this thing brings to your PC. PUAs like that may be just an irritating thing, as well as trigger a severe effect on your system’s functioning. Moreover, there are a lot of incidents when users state that this application collects user information or other sensitive stuff.
PUA:Win32/RemComSvc Detection Overview
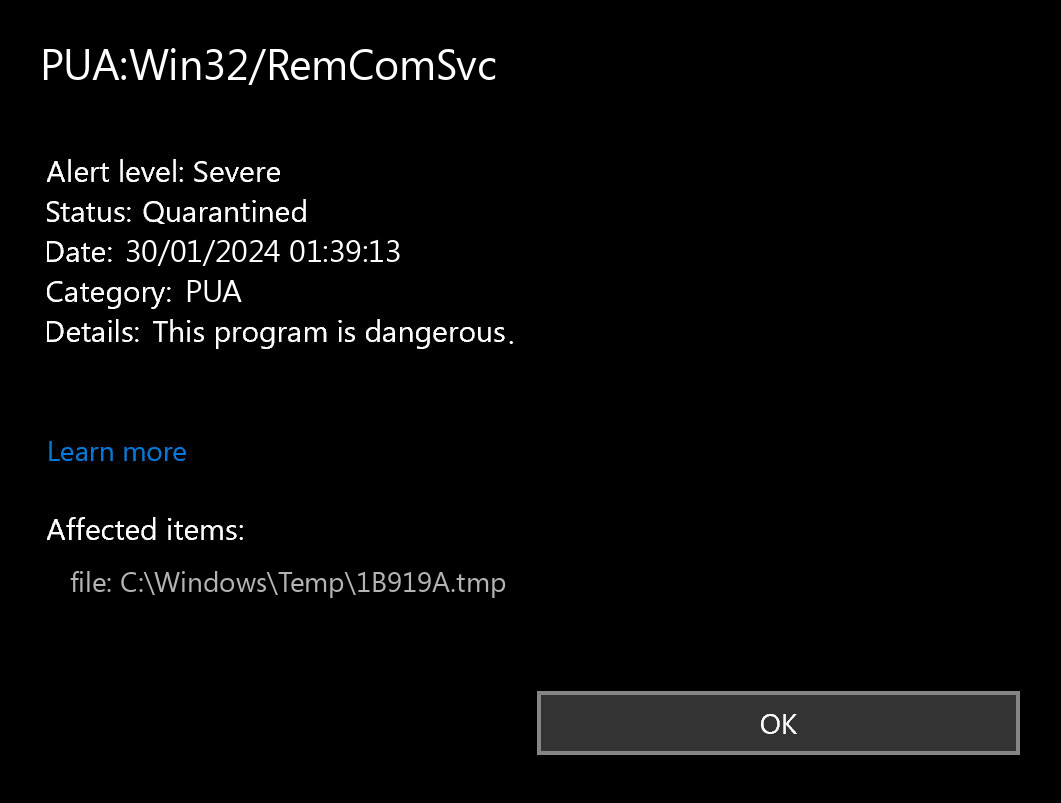
The PUA:Win32/RemComSvc detection you can see in the lower right side is demonstrated to you by Microsoft Defender. That anti-malware program is good at scanning, however, prone to be basically unreliable. It is prone to malware attacks, it has a glitchy interface and problematic malware removal capabilities. Therefore, the pop-up which states concerning the RemComSvc is simply a notification that Defender has actually detected it. To remove it, you will likely need to make use of another anti-malware program.
PUA:Win32/RemComSvc unwanted program is a case in point of PUA, which are pretty much common nowadays. Being free to use, it can offer you “the extended capabilities” for the extra payment. Some instances of this program type can have no useful performance whatsoever – only the shell with the kaleidoscopic interface. You can see it promoted as a system optimization tool, driver updater or torrent downloadings tracker. This or another way it does not provide you any actual performance, exposing you to risk instead.
Unwanted Program Summary:
| Name | RemComSvc PUA |
| Detection | PUA:Win32/RemComSvc |
| Damage | RemComSvc is at least useless, or can perform various malicious actions on your PC. |
| Fix Tool | See If Your System Has Been Affected by RemComSvc exploit |
Is PUA:Win32/RemComSvc dangerous?
I have already mentioned that PUA:Win32/RemComSvc PUA is not as safe as it claims to be. The “legitimate and useful” program can suddenly discover itself as a downloader trojan, spyware, backdoor, or coin miner virus. And you can never figure out what to anticipate even from different instances of RemComSvc unwanted program. That still does not mean that you have to panic – probably, this unpleasant thing has not succeeded to do poor things to your computer.
The particular damage to your system can be caused not only due to the malware injection. A significant share of doubtful programs, like the RemComSvc app is, is just badly made. Perhaps, their actions are fairly useful than worthless if done on particular system configurations, but not on each one. That’s how a simple system optimization program may create disorder with constant BSODs on your system. Any type of interruptions to the system registry are risky, and they are much more risky if performed with such programs.
Remove RemComSvc with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common PUA as shown from our tests with the software, and we assure you that it can remove RemComSvc as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “RemComSvc” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing RemComSvc and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.