Specialists of the Chinese company Tencent Security spoke1 about the MrbMiner malware that installed cryptocurrency miners on Microsoft SQL servers (MSSQL) formerly. According to experts, thousands of MSSQL databases were already infected.
The researchers also named the group behind these attacks MrbMiner, after one of the domains used by cybercriminals to host malware. Experts write that the botnet is expanding solely by scanning the Internet searching for MSSQL servers and subsequent brute force attacks on them. Attempts to use an administrator account with various weak passwords were also noticed.Having penetrated the system, the attackers download the assm.exe file, which they then use to gain a foothold in the system and create a new account that acts as a backdoor for future access. This account typically uses the username Default and the password @fg125kjnhn987 . The last stage of the infection is to connect to the C&C server and download an application that extracts Monero(XMR) cryptocurrency using the infected system’s power.
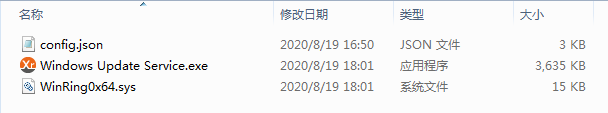
Windows Update Service.exe (MrbMiner malware)
Although so far, Tencent Security experts have observed attacks only on MSSQL servers. They write that the MrbMiner control server contains other malware for Linux and ARM-based systems inclusive.
MrbMiner files similar to the normal Windows service:
After examining MrbMiner for Linux, experts found out the wallet’s address to which the malware transferred Monero. The wallet contains 3.38 XMR (about $300), which means Linux malware is already in use, although the details of these attacks are still unknown. In turn, the wallet used by the MSSQL version of MbrMiner contains 7 XMR (about $630). Although these amounts are small, mining hackers usually use multiple wallets for their operations, so the MbrMiner group is likely to make more profits.
References
- Tencent Security: The cross-platform mining Trojan MrbMiner has controlled thousands of servers [CN]


Leave a Comment