Loda RAT malware active since 2016, infiltrates systems primarily through phishing campaigns and drive-by downloads from compromised websites and steals sensitive information.
Loda RAT excels at stealing sensitive data, including passwords, via keystroke logging. It also captures screenshots, providing attackers with valuable information regarding victims’ activities. Loda is a potent threat with a wide range of capabilities, making it a significant concern in the cybersecurity landscape.
Loda RAT Overview
Loda RAT is a remote access trojan (RAT) that threat actors have actively utilized since 2016. It excels in tasks such as stealing passwords, gathering sensitive data, recording keystrokes, capturing screens, and distributing other malicious payloads. Phishing campaigns are the typical delivery method for Loda.
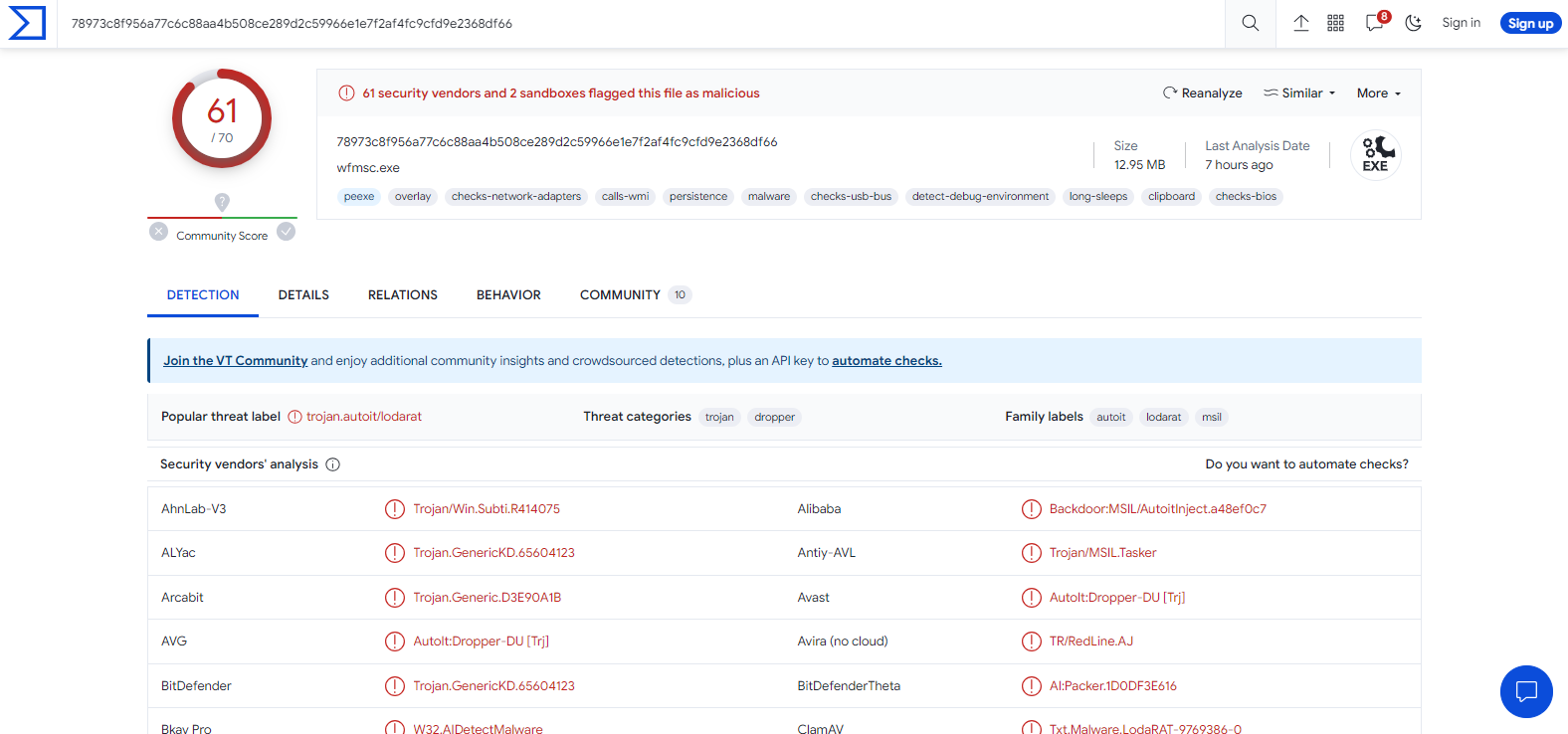
Loda RAT on VirusTotal site
| Name | Loda Remote access trojan |
| Threat Type | Remote Administration Trojan |
| Detection | Microsoft (Trojan:Win32/AutoitInject.RA!MTB) GridinSoft (Trojan:Win32/Autoit) |
| Symptoms | Remote Access Trojans are designed to stealthily infiltrate the victim’s computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Similar behavitor | HiatusRAT, Whiffy Recon, JanelaRAT |
| Distribution methods | Infected email attachments or links within emails, malicious online advertisements, social engineering, software ‘cracks’. |
| Damage | Stolen passwords and banking information, identity theft, the victim’s computer added to a botnet, additional malware injections, data encryption, and more. |
Technical Analysis of Loda RAT
Loda RAT primarily operates by pilfering sensitive data, with a particular focus on passwords and login credentials. It accomplishes this covertly by recording keystrokes as users input information on compromised devices. This allows malicious actors to seize usernames and passwords related to online accounts, including those for banking websites and various other platforms.
This pilfered data can subsequently be leveraged for financial profit or employed in subsequent cyber offensives. Additionally, Loda possesses a disconcerting capability to capture screenshots of the victim’s computer. This feature furnishes attackers with a visual window into the victim’s activities, potentially unveiling sensitive or confidential information.
Spreading methods
Another route is via compromised or malicious websites, which can subject users to drive-by downloads. These websites exploit vulnerabilities in the user’s web browser or plugins, allowing the automatic download and installation of malware, such as Loda, without any user interaction.
Additionally, cybercriminals target software vulnerabilities in outdated or unpatched applications. Furthermore, Loda and similar malware may be disseminated through P2P file-sharing networks, torrent sites, and similar platforms, often masquerading as cracked software or cracking tools.


Leave a Comment