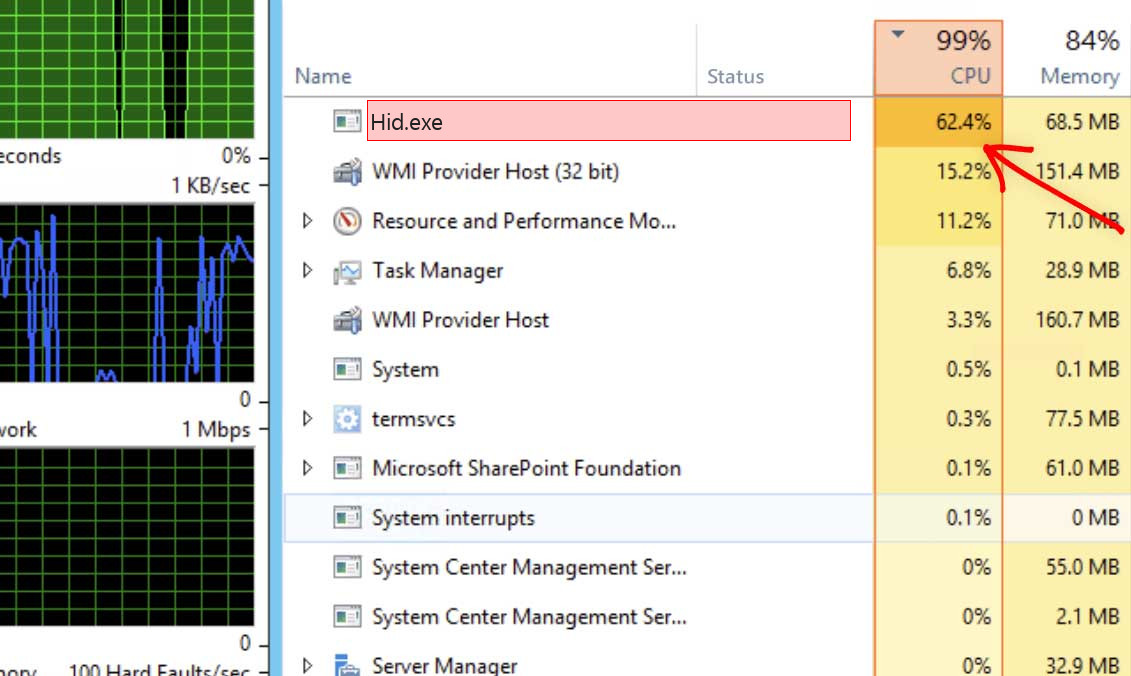
Hid.exe process is associated with Human Interface Device (HID) service. HID is a protocol that allows input devices to communicate with the operating system. The Hid.exe process typically does not create any issues and consumes tiny amounts hardware power. But if it does take a lot of CPU, you definitely have a virus that hijacked this name.
The Hid.exe service is an essential component of the operating system and is necessary for proper interaction with HID devices. The process itself should not consume excessive CPU resources or cause performance issues on your computer. However, malicious programs, particularly coin miners, can take its name to disguise itself in the Task Manager. In this case, you will see high CPU load coming from that process. Let me show you how to recognize this process and remove it, once it is malicious
What is Hid.exe process?
Hid.exe process itself is legitimate, but coin miner malware can use this name as a disguise.
As I just said, Hid.exe is a benevolent process that should not create any problems. However, malware can sometimes masquerade under legitimate process names to avoid detection. The most definite sign of such a situation is high CPU load generated by this process. Malware may take up to 80% of your processor power, which makes your system nearly impossible to use.
Another way to review the benevolence is to check the file location and properties of the Hid.exe process. The legitimate Hid.exe file is usually located in the “System32” folder within the Windows directory (C:\Windows\System32). This file never appears in other locations, so seeing it elsewhere means it is a malicious process with the same name. You can right-click on the process in the Task Manager, select “Open File Location,” and examine the file properties.
Shortly about cryptocurrency mining
List of the typical coin miner symptoms
How dangerous is the Hid.exe miner?
Coin miners does not deal damage to your files. However, they make a lot of unpleasant things with the whole system
Firstly, Hid.exe virus makes your computer overloaded. It is not able to run your applications anymore, as all processor power is used by a virus. That malware does not care for your necessities, all it pays attention to is making money on you. Even if you are patient, and you waited until browser is open, you will likely experience exceptionally sluggish efficiency. Pages will open up for years, any kind of logins will take about a minute – just a headache for a person that does a job online.
Hid.exe Technical Summary.
| File Name | Hid.exe |
| Type | Trojan Coin Miner |
| Detection Name | Trojan:Win32/CoinMiner |
| Distribution Method | Software bundling, Intrusive advertisement, redirects to shady sites etc. |
| Similar behavior | Armourysocketserver.exe, Spovelt.exe, Armouryliveupdate.exe |
| Removal | Download and install GridinSoft Anti-Malware for automatic Hid.exe removal. |
“Visible” damage is not a single bad activity coin miners do to your PC. Hid.exe coin miner also deals damage to your operating system. To perform all malicious operations correctly, it ruins the security features of your system. You will likely see your Microsoft Defender disabled – malware stops it to prevent recognition. If you open the HOSTS file, you will likely see a lot of new notes – they are brought in by this coin miner to connect your PC to a malicious cryptomining network. All these changes shall be thrown back to the original in the process of PC recovery.
Hardware effects of coin miner activity
Besides decreasing your computer’s performance, performing at peak level for long times can trigger damage to your device as well as increase electricity expenses. PC elements are created to easily deal with high load, but they are good with it only when they are in a good shape.
Compact and well-protected CPU fan is quite hard to damage. Meanwhile, graphic cards have big and easy-to-access fans, which can be easily broke if affected while working, for instance, by the user much earlier before the malware injection. Malfunctioning cooling system, together with the very high load caused by Hid.exe malware can easily lead to graphic card failure1. Graphic cards are also prone to have very fast wearing when used for crypto mining. It is surely a bad case when the performance of your video card decreases on 20-30% only after several weeks of being used in such a way.
How did I get Hid.exe coin miner virus?
Coin miners are spread through different ways, but their main sources are malicious banners and programs from dubious sources
Coin miners are one of the most common malicious programs among “serious” viruses. Adware sometimes acts as a carrier for Hid.exe malware infiltration: it demonstrates you the banners, which contain a link to malware downloading. Sure, this abstract “malware” can belong to any type – an additional adware, spyware, rogue or backdoor. However, the statistics show that approximately 30% of all malware spread with the malicious banners are coin miners – and Hid.exe is right among them.
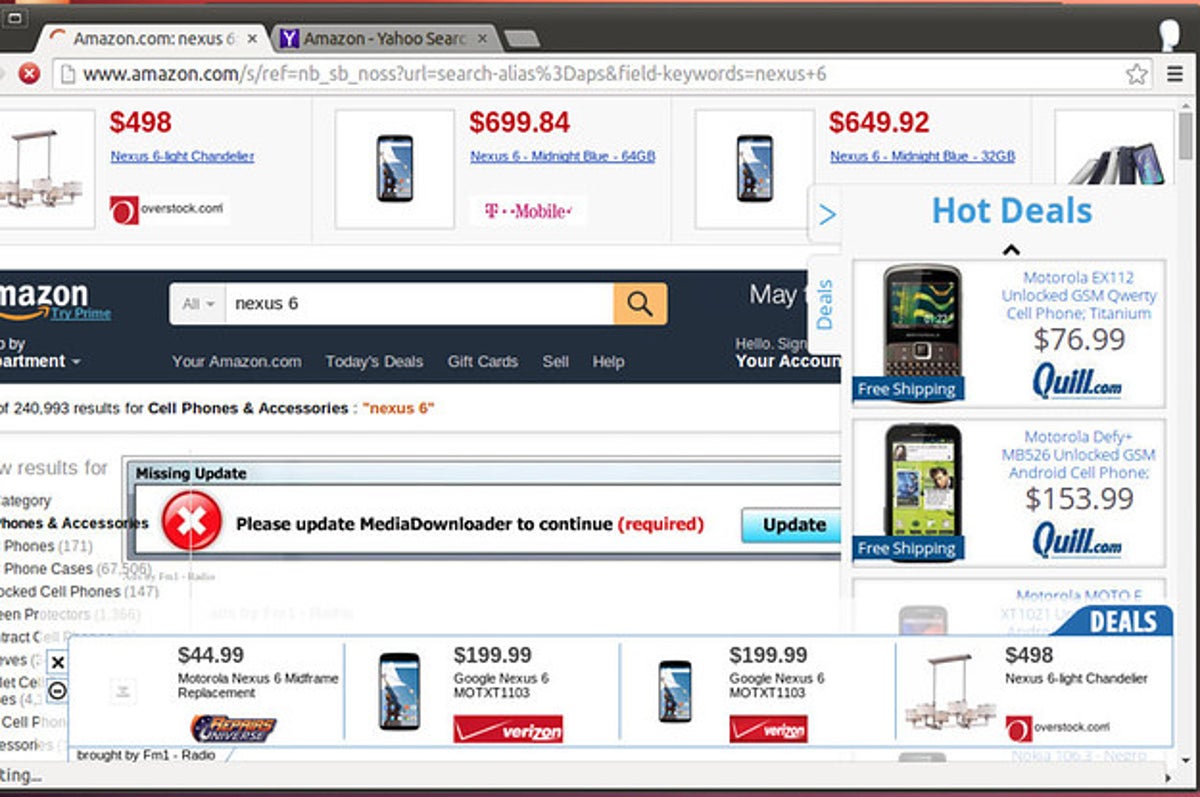
The example of malicious banners you can see in the Internet
An additional way you could get this item on your PC is by downloading it from the suspicious web page as a part of a program. People who spread hacked variants of well-known programs (which do not demand the license key) have small chances to earn money. Hence, there is a huge lure to add in malware to the final package of the hacked app and receive a coin for every installation. Prior to blaming these individuals for hacking and also malware distribution, ask yourself – is it alright to avoid paying for the program in such a way? It is much cheaper to pay $20-$30 one time than to pay a much bigger sum for antivirus software and new parts for your PC.
How to remove the Hid.exe miner from my PC?
The best way to get rid of this coin miner virus is to use anti-malware software
Booting the PC into Safe Mode with Networking
Press the Start button, then choose Power, and click on Reboot while holding the Shift key on the keyboard.
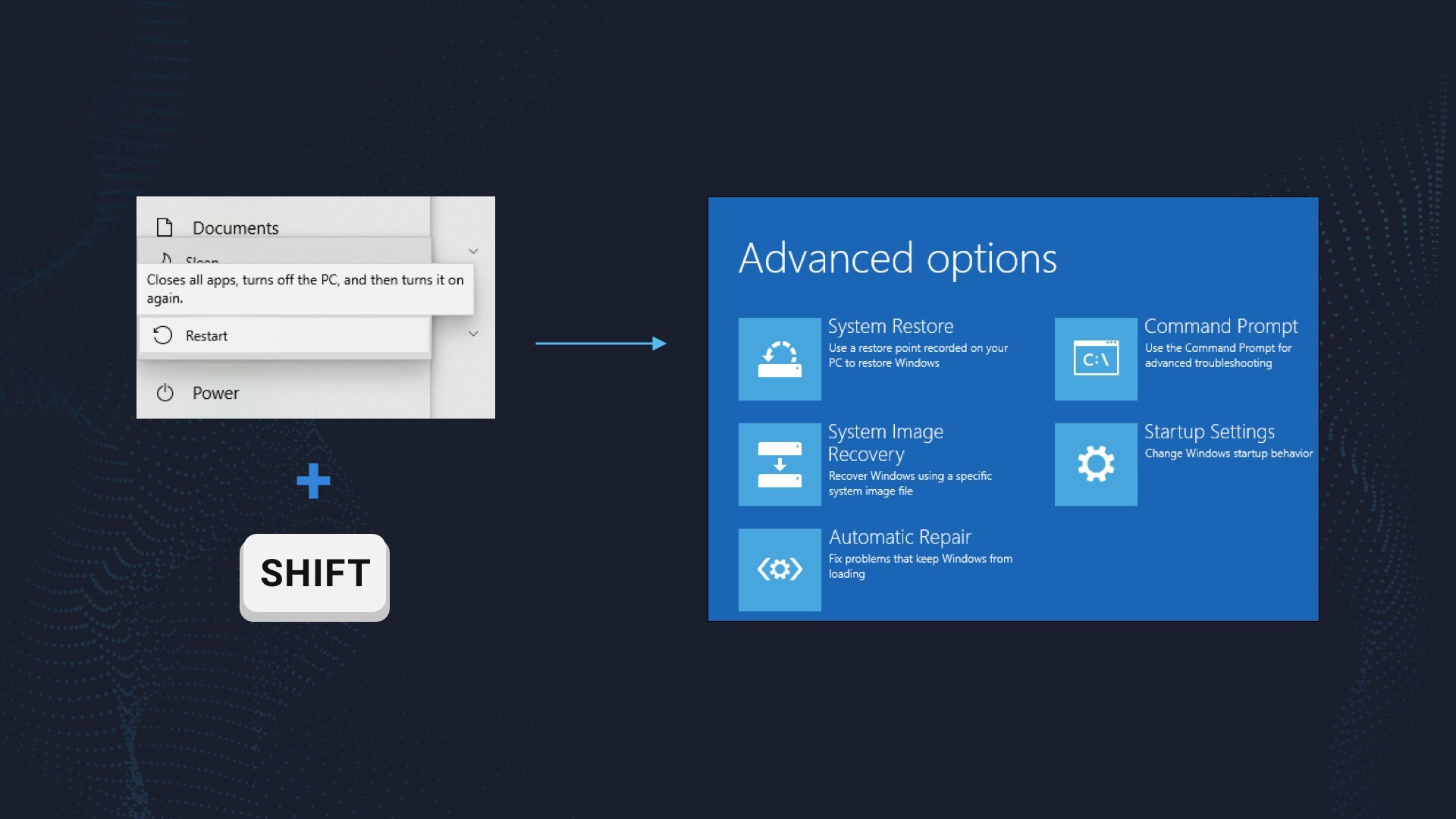
Windows will reboot into recovery mode. In that mode, choose Troubleshoot→ Startup Settings→ Safe Mode with Networking. Press the corresponding button on your keyboard to choose that option.
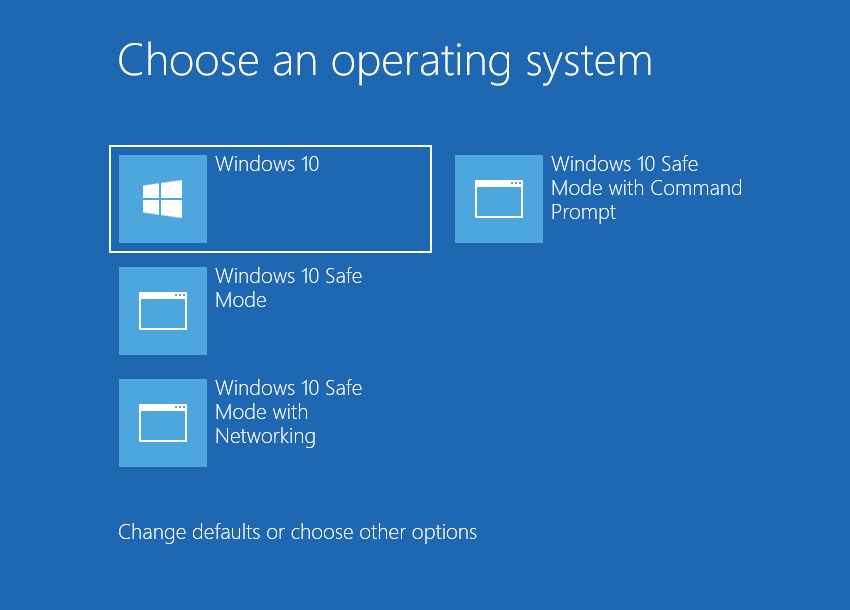
When your system is in Safe Mode, all third-party apps, along with the majority of non-crucial operating system components, are not launched with the system start. That gives you the ability to clean the PC without dealing with high CPU usage of the coin miner.
References
- About unwanted effects for GPUs in the process of cryptomining.


Leave a Comment