GoPIX is a malicious program targeting Pix and cryptocurrency transactions in Brazil. It spreads through malvertising campaigns and deceptive websites.
Once on a victim’s system, it operates as a clipper, intercepting Pix platform transactions and rerouting them to the attacker’s control. This clipper also targets cryptocurrency transactions by replacing wallet addresses. The malware poses severe privacy and financial risks, making it vital for users to stay vigilant and employ strong security measures to protect their digital assets.
GoPIX Overview
GoPIX is a malicious program designed to target the Pix instant payment platform. It functions as a clipper, redirecting transactions made through the Pix platform. Additionally, it can also target cryptocurrency transactions. GoPIX has been active since at least December 2022. It primarily operates in Brazil because it focuses on Pix, a payment platform created and managed by the Central Bank of Brazil. This malware is tailored to exploit Pix users, predominantly in Brazil.
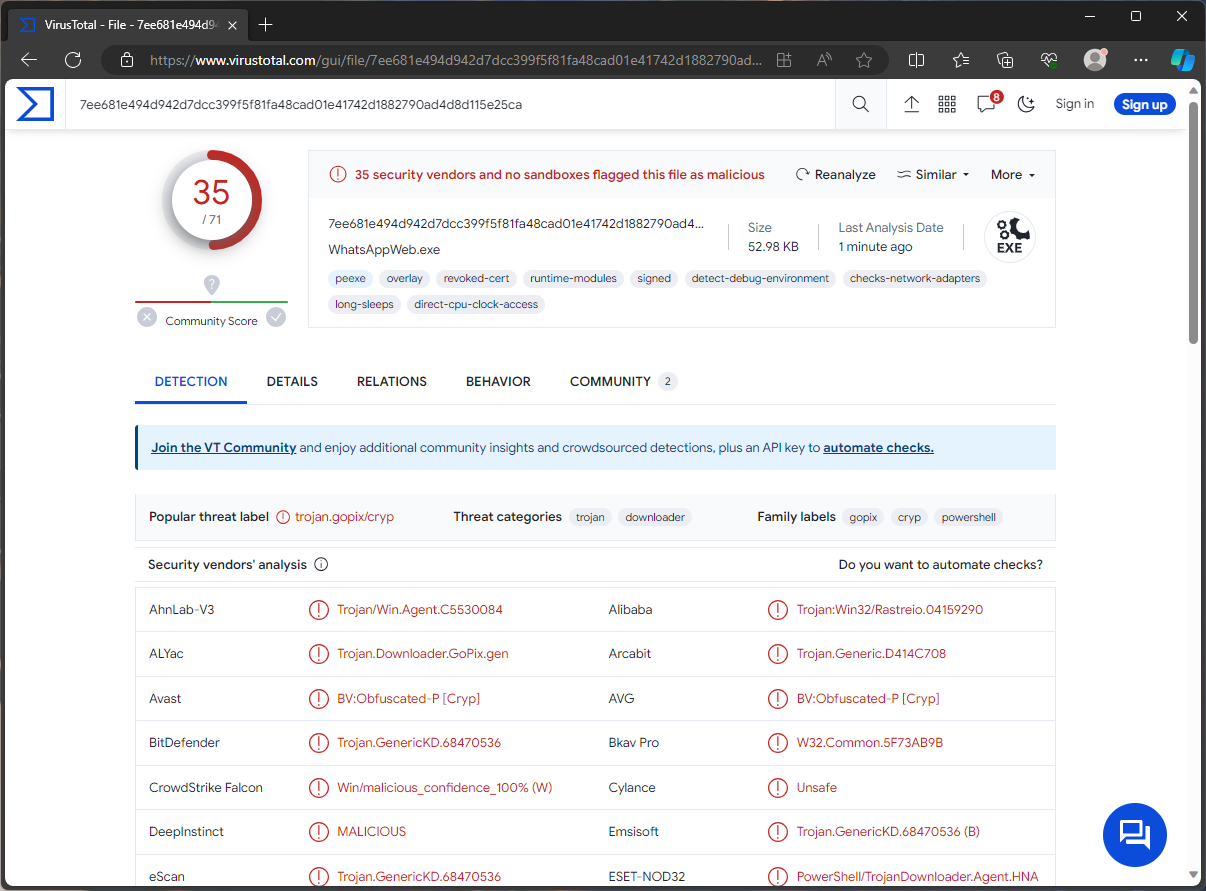
Detection results for Virustotal
| Name | GoPIX |
| Detection | Trojan:Win32/Rastreio.RPZ!MTB (Microsoft) |
| Threat Type | Trojan, banking malware, clipper, clipboard hijacker. |
| Damage | Stolen passwords and banking information, identity theft, the victim’s computer added to a botnet. |
| Similar Behavitor | Clipper.Trojan.Stealer.DDS, Trojan.Clipper.MSIL |
Technical Analysis
GoPIX is a clipper malware that monitors the clipboard for copied content and replaces it with different information. In the case of GoPIX, it explicitly targets Pix transfers. When a Pix payment request is detected, GoPIX alters the data, redirecting the transaction to cybercriminals. Notably, the attacker’s information is retrieved from a Command and Control (C&C) server, making it flexible and adaptable.
GoPIX also functions as a clipper targeting cryptocurrency wallet addresses with predetermined addresses for Bitcoin and Ethereum. In summary, the presence of GoPIX on a device can lead to significant privacy issues and financial losses, making it a considerable threat.
Spreading Methods
The specific file downloaded onto the victim’s computer depended on whether the machine had an Avast product that utilized port 27275. So, if this software was detected, a ZIP file containing an LNK file with an embedded PowerShell script was downloaded. If the Avast product was not present, an NSIS installer package with multiple PowerShell scripts was used to initiate the infection chain.
It is important to note that GoPIX could potentially be distributed through other methods as well. Phishing and social engineering techniques are standard in malware distribution, and malicious programs often hide within or alongside legitimate software and media files. Malicious files can take various formats, such as archives, executables, documents, JavaScript, etc. These files can be disseminated through spam emails, online scams, deceptive downloads, and even self-spreading via local networks and removable storage devices like USB drives and external hard drives. Therefore, vigilance and strong security practices are essential in safeguarding against such threats.


Leave a Comment