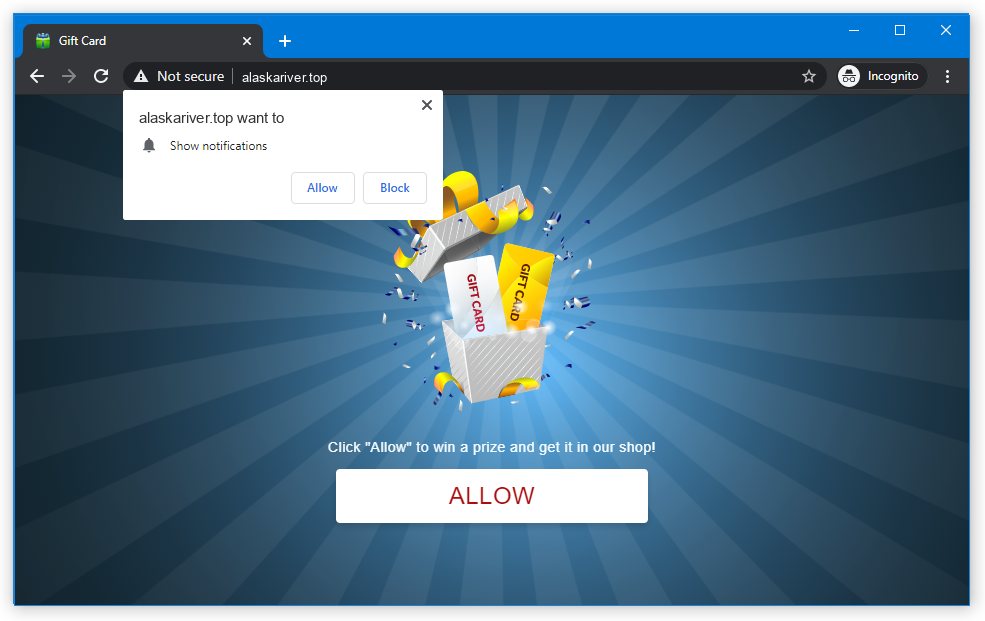
Alaskariver.top pop-ups that you can see while surfing the Web are a consequence of a malicious software infection that resides in your web browser. Such pop-ups emerge in abundant quantities, diverting and irritating you.
Most of the pop-ups from Alaskariver.top site are not relevant, as it displays any advertising material it receives a deal for. Given that a lot of pages promoted in this manner are not benevolent, it is obvious to expect them to contain dangerous content. Specifically, they can expose you to various forms of web deceptions.
What are Alaskariver.top push notifications?
By some of the characteristics, Alaskariver.top pop-ups are comparable to typical pop-ups you may experience on regular sites. However, all the difference – and malignancy – originates from this specific website. Pages like Alaskariver.top are commonly established with just one purpose – to propose unsuspecting users to activate pop-ups and then start spamming them.
Short summary of the Alaskariver.top pop-ups:
| Name | Alaskariver.top |
| Hosting | AS13335 Cloudflare, Inc. United States, San Francisco |
| IP Address | 104.21.32.172 |
| Malware type | Adware1 |
| Effect | Unwanted pop-up advertisements |
| Hazard level | Medium |
| Malware source | Apps from third-party websites, ads on dubious websites |
| Similar behavior | Pirophackeri, Phipsougri, Everestriver |
| Removal method | To remove possible virus infections, try to scan your PC |
Ads by the Alaskariver.top site are not legit either. At best, those will be entirely irrelevant ads, that will still be bothersome considering their frequency. Nevertheless, more common cases include advertisements of mysterious deals with 90% off, adult web pages ads or phishing attempts. Presented here are some of the standard patterns for push ads spam:
- Discover 5, 10, 20, or even 50 women near you who are eager to chat.
- Sign in on this new crypto exchange website and receive a substantial crypto bonus.
- Your system is infected with 15 viruses. Contact our tech support or perform an immediate scan.
- You’ve received a new message on Facebook, Twitter, or WhatsApp. Beware of phishing links.
- Visit this new, totally legitimate shopping site and claim your discount coupon.
- up your computer with an incredibly effective system cleaner.
Due to the illegal marketing strategy of Alaskariver.top, no lawful enterprises will actually employ their advertisement services. Meanwhile, the whole array of subjects I’ve named above is controlled by the same deceitful individuals as those who stand behind Alaskariver.top. At times, upon clicking to the pop-up promotion, you might be thrown to another page that suggests activating pop-up advertisements. The activity of multiple origins of pop-ups can transform your browser into an avenue of a pop-up surge.
Where did Alaskariver.top pop-ups come from?
The primary and most widespread technique to access the pop-up spamming site is to navigate through content on warez sites, pages containing pirated content, and the like. The individuals responsible for such uncertain venues aim to compensate for expenses via redirects, often as a promotional strategy. This type of redirection is commonly known as an “anti-bot verification”.
An additional plausible source of pop-up advertisements is adware, currently active within your system. It changes browser settings in a manner so it starts displaying Alaskariver.top pop-ups without your consent. However, this situation is relatively uncommon, as such malware employs its own, more productive method to showcasing advertisements.
Are Alaskariver.top pop-up ads dangerous?
Yes, they are. Initially, they may look non-threatening – just a blinking pop-up that appears a couple times in an hour. However, the things this window promotes differ sharply from what you used to see in pop-up notifications. Alaskariver.top website is ruled by crooks, who intentionally throw hundreds and thousands of malicious ads in pop-ups. They also don’t follow any common sense and can make sporadic pop-up ads into a storm of ads. For weak computers, that may be enough to make the system slower. But troubles are not over at this point.
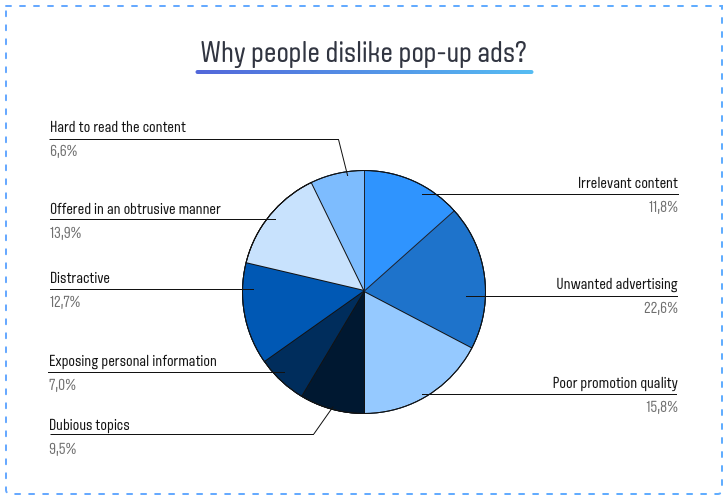
As any other thing related to illegal ads, Alaskariver.top pop-up advertisements do not contain any legit offers. Even though crooks make the ads looking similar to ones from Walmart or Amazon, the website these banners will throw you to are completely different. And these pages may offer you to turn on other pop-ups, install a “useful” program, or pay for a thing at a big discount and never receive it. Let’s leave aside the cases when pop-ups promote phishing pages or straightforward malware. There’s no way these pages will bring you any good, thus interacting with them is a very bad idea. For the same reason, Alaskariver.top pop-up ads are not recommended to click on either, and the best solution is to disable them as soon as possible.
How to remove Alaskariver.top pop-ups?
Fortunately, Alaskariver.top push notifications removal is pretty easy. They parasite in the browser and can’t conceal themselves in the system. Nevertheless, as I told above, some pop-up notifications can deliver malicious software to your system. It is nearly impossible to describe all cases, and manual attempts to remove malware is a poor idea. Therefore, after getting rid of the pop-ups it is recommended to use anti-malware software. That is especially recommended in the case when you have never allowed pop-ups, and they still appeared. That can point at malicious software activity. GridinSoft Anti-Malware will be the best both recovery and malware removal purposes, thanks to its abilities of system recovery and multi-component detection system.
Remove Alaskariver.top with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common malicious pop-ups as shown from our tests with the software, and we assure you that it can remove Alaskariver.top as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

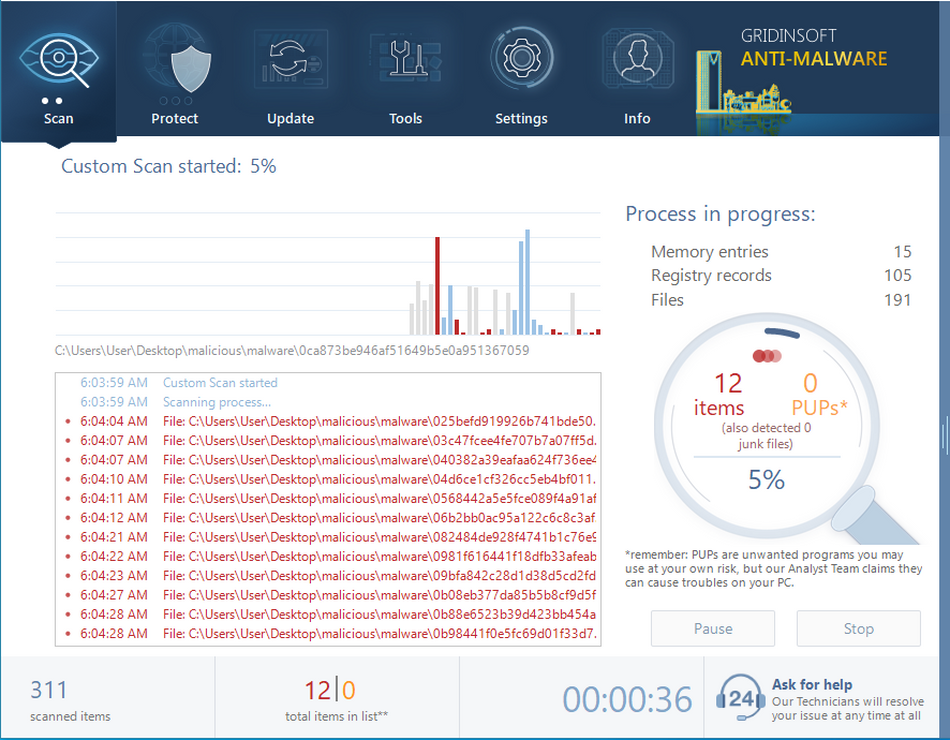
4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
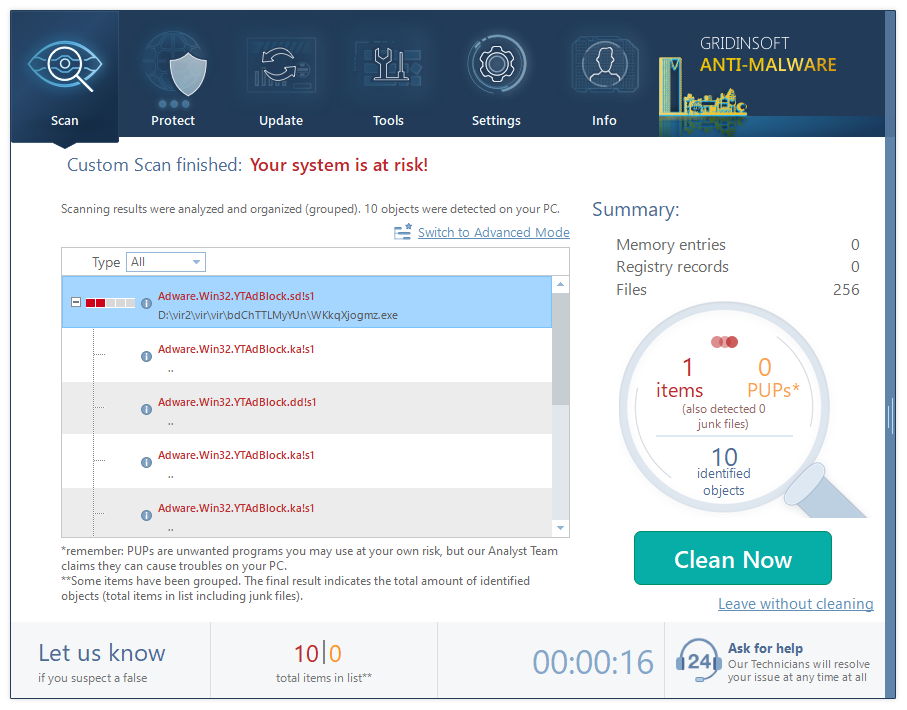
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “Alaskariver.top” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing Alaskariver.top and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
Now, you should reset your browser settings. You can do that in manual or automated way. The former, obviously, requires more time to complete and may be somewhat complicated if you have never done that. Automated supposes the use of anti-malware programs that can reset all browser settings at once.
Reset your browsers with GridinSoft Anti-Malware
To reset your browser with GridinSoft Anti-Malware, open the Tools tab, and click the “Reset browser settings” button.
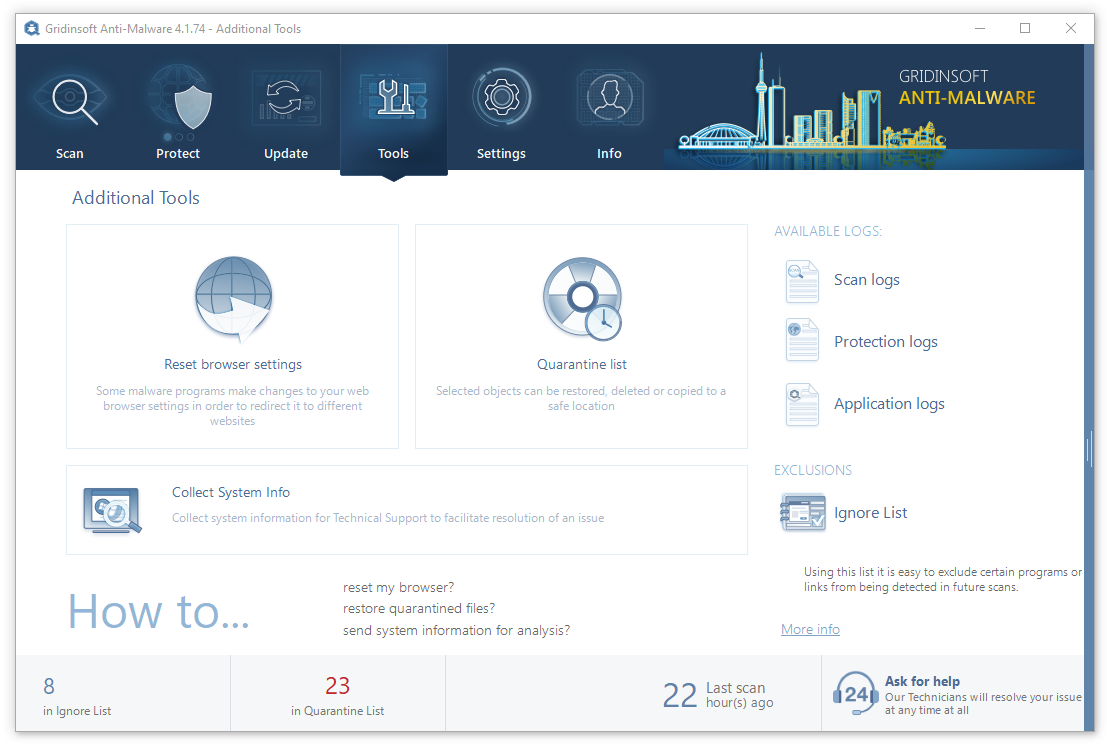
You can see the list of options for each browser. By default, they are set up in a manner that fits the majority of users. Press the “Reset” button (lower right corner). In a minute your browser will be as good as new.
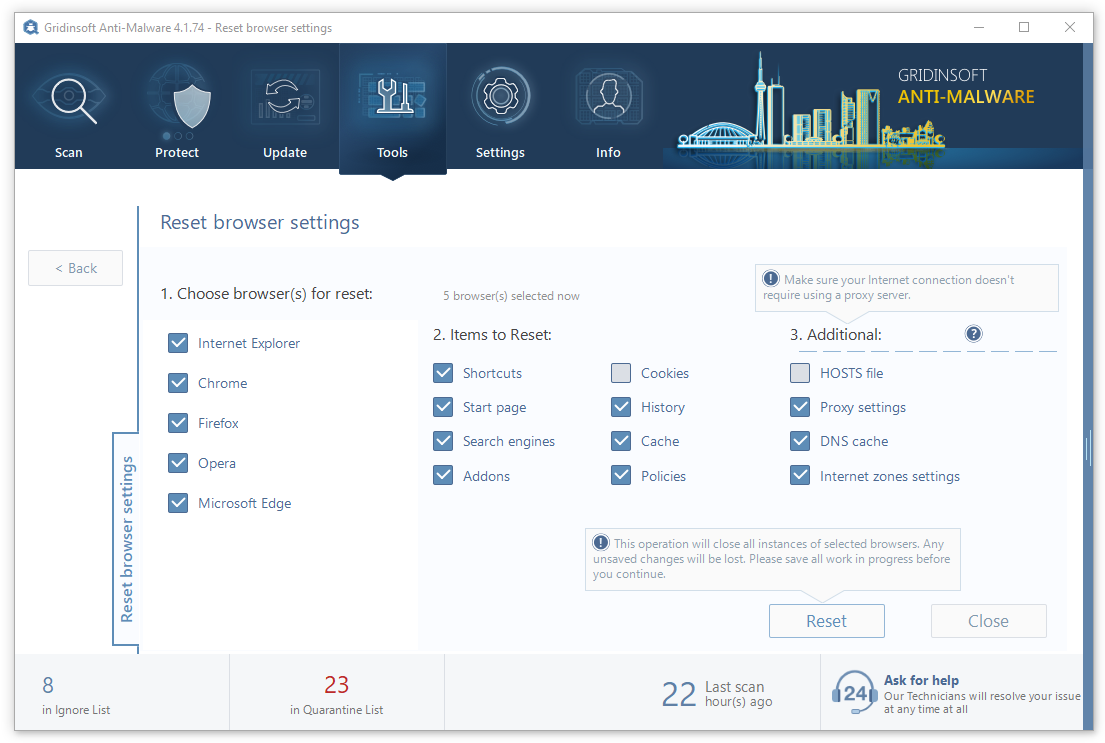
The browser reset is recommended to perform through the antivirus tool by GridinSoft, because the latter is also able to reset the HOSTS file without any additional commands.
Reset your browsers manually
Manual method of browser reset
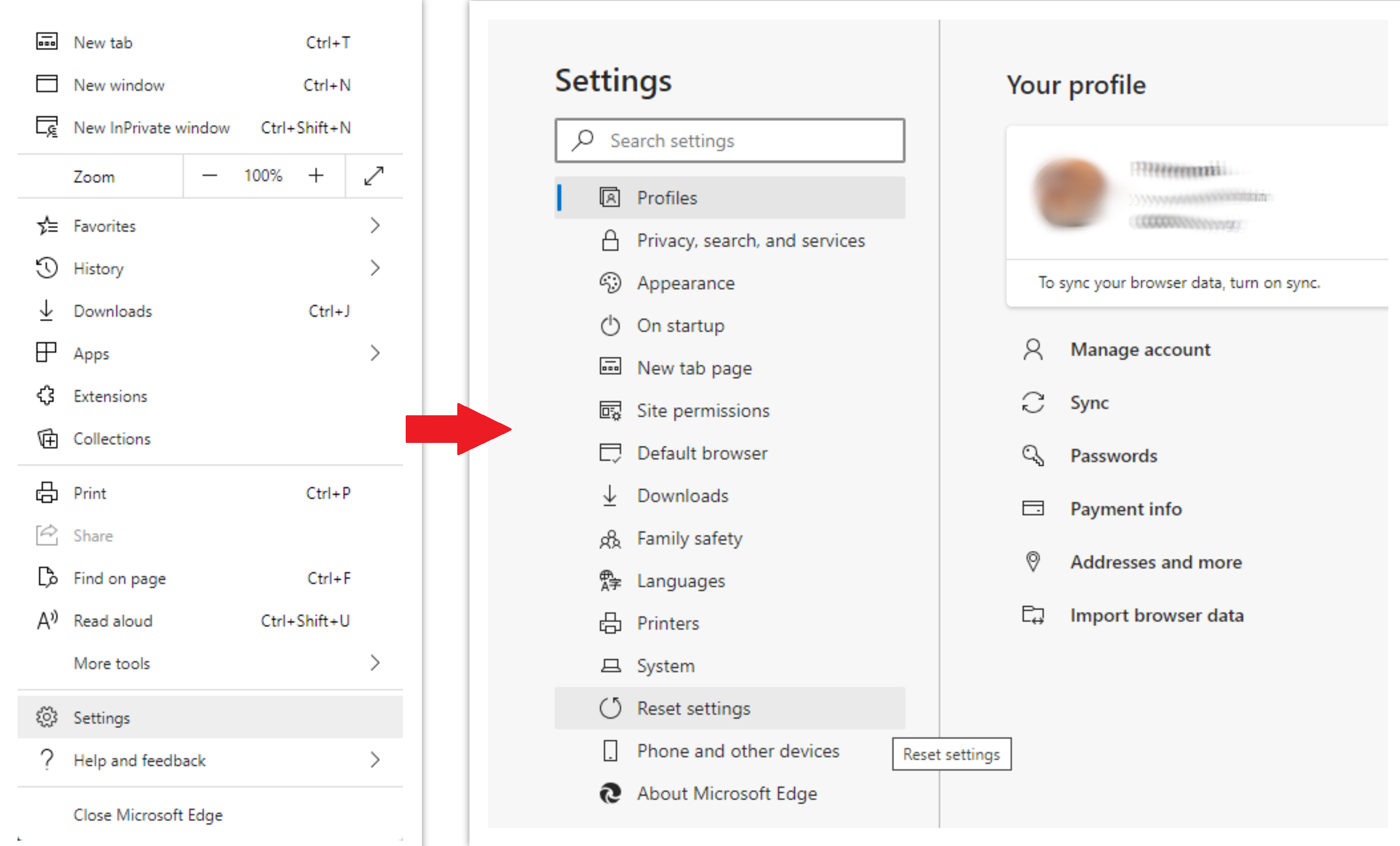
To reset Edge, do the following steps:
- Open “Settings and more” tab in upper right corner, then find here “Settings” button. In the appeared menu, choose “Reset settings” option:
- After picking the Reset Settings option, you will see the following menu, stating about the settings which will be reverted to original:
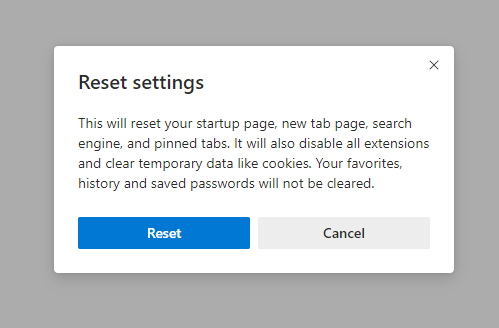
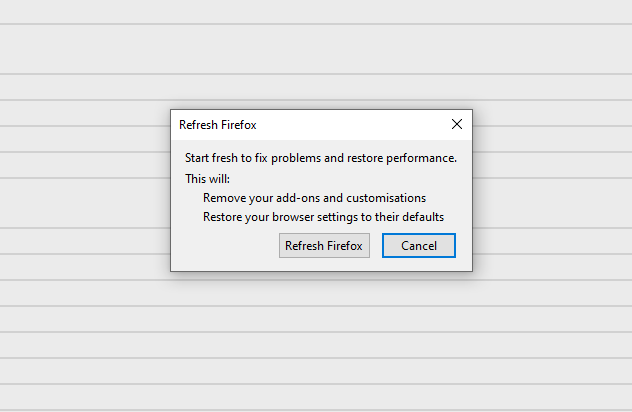
For Mozilla Firefox, do the next actions:
- Open Menu tab (three strips in upper right corner) and click the “Help” button. In the appeared menu choose “troubleshooting information”:
- In the next screen, find the “Refresh Firefox” option:
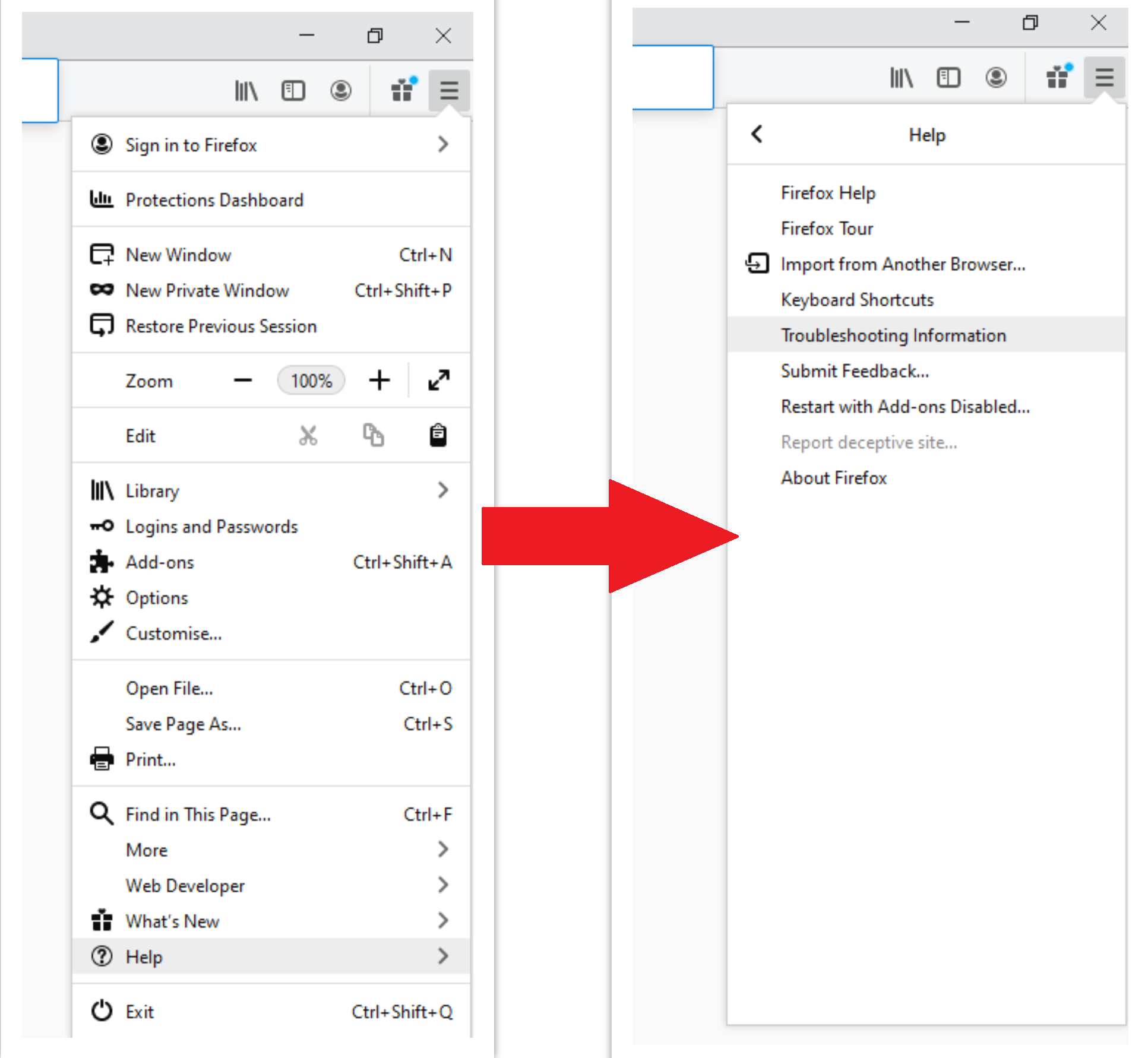
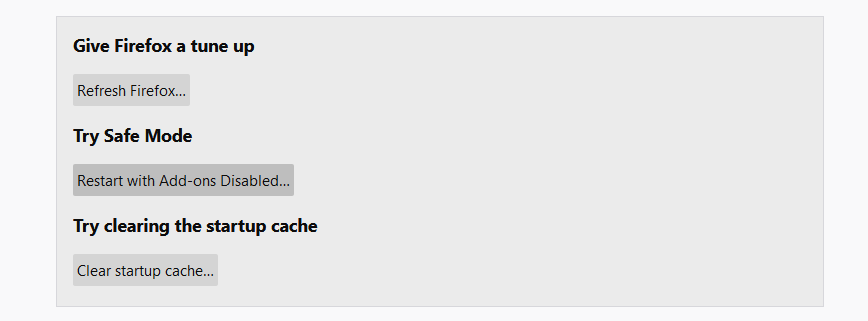
After choosing this option, you will see the next message:
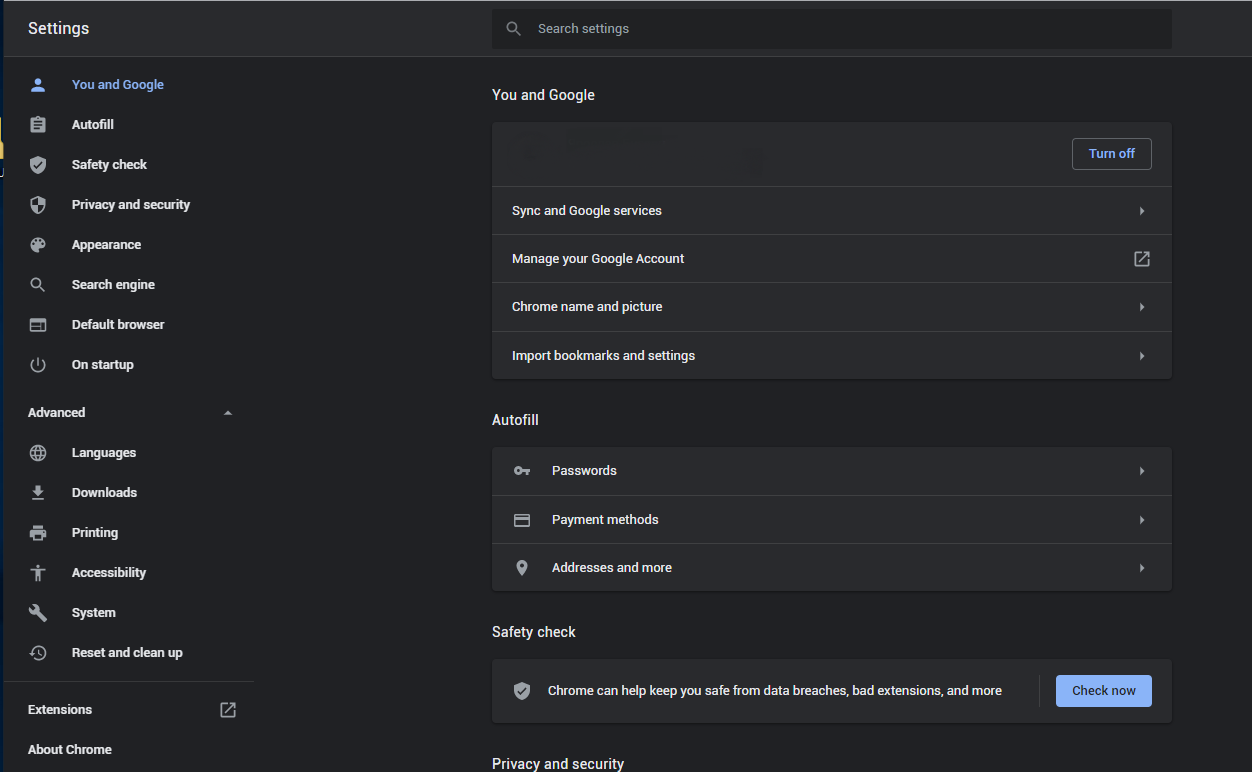
If you use Google Chrome
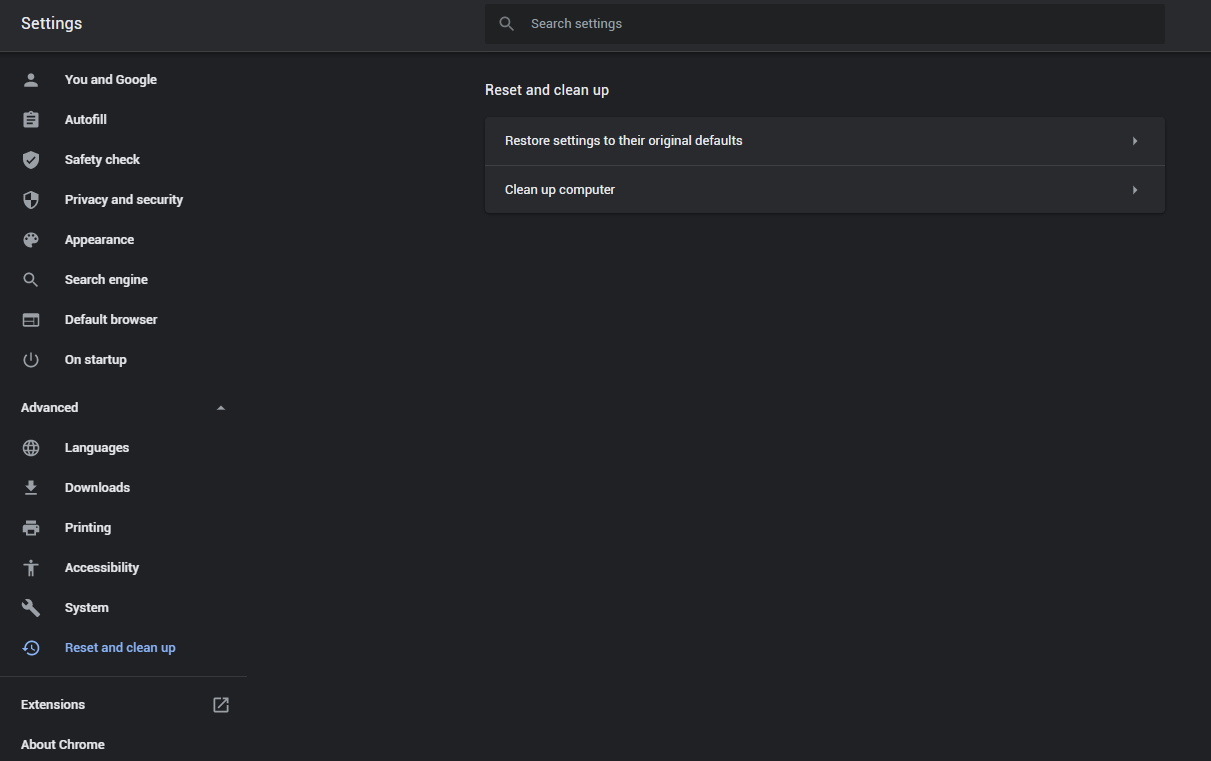
- Open Settings tab, find the “Advanced” button. In the extended tab choose the “Reset and clean up” button:
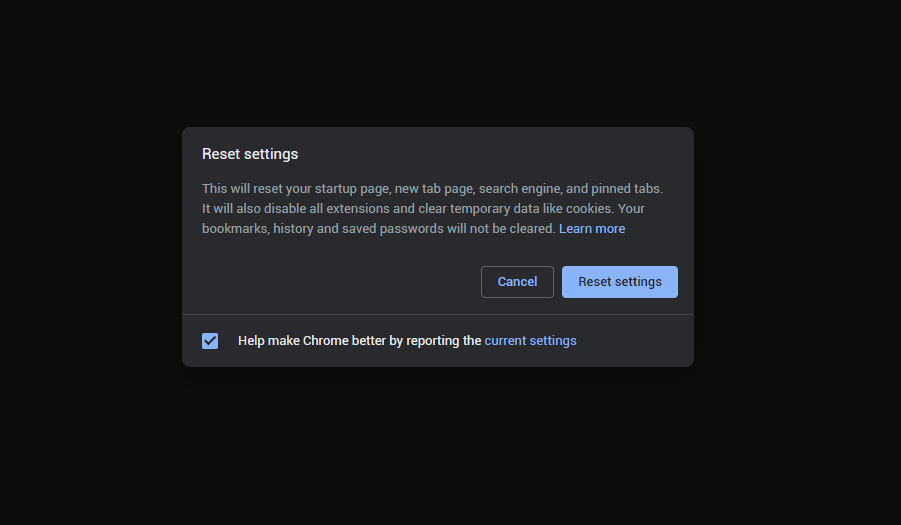
- In the appeared list, click on the “Restore settings to their original defaults”:
- Finally, you will see the window, where you can see all the settings which will be reset to default:
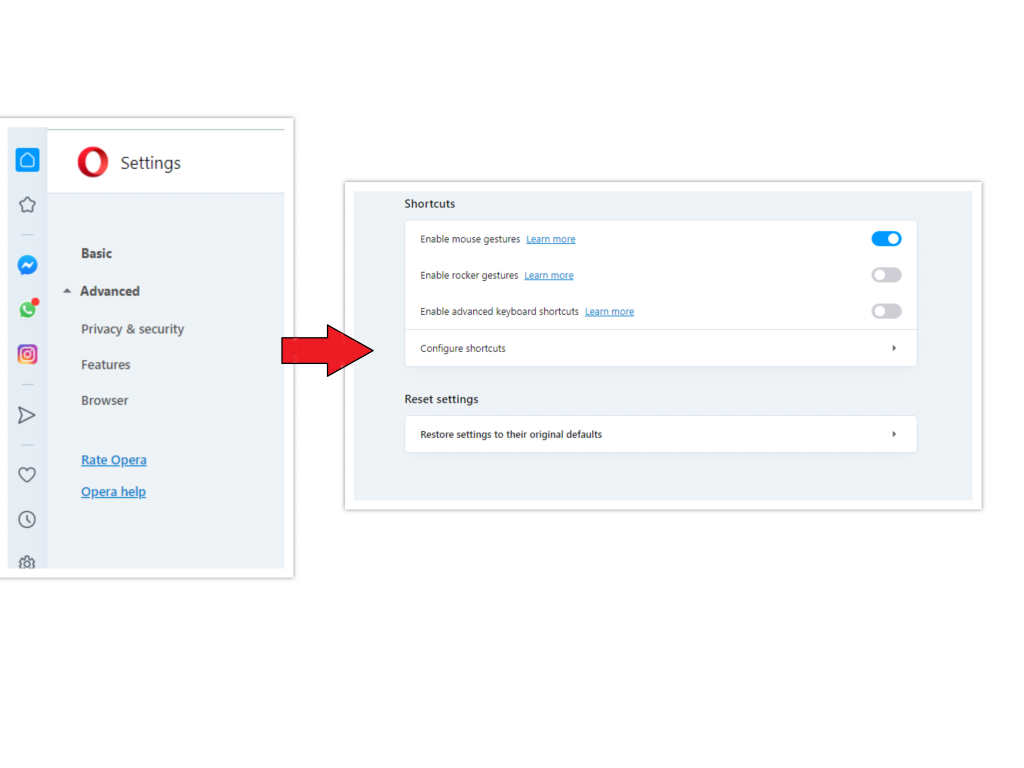
Opera can be reset in the next way
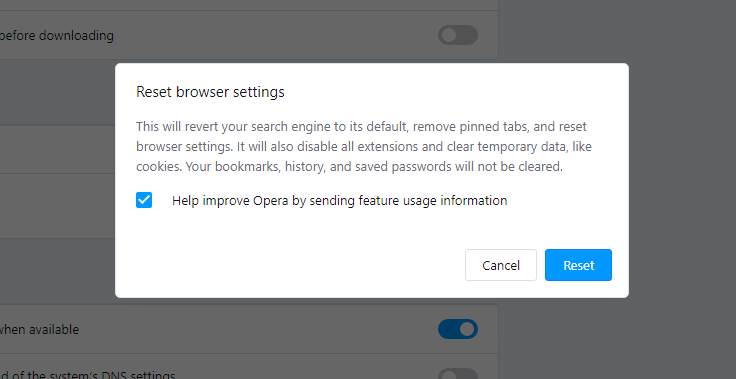
- Open Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click “Advanced” option, and choose “Browser” button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there “Restore settings to their original defaults” option:
- After clicking the “Restore settings…” button, you will see the window, where all settings, which will be reset, are shown:
When the browsers are reset, you need to ensure that your browser will connect the right DNS while connecting to the web page you need. Create a text file titled “hosts” on your pc’s desktop, then open it and fill it with the following lines2:
# Copyright (c) 1993-2006 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handle within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
Find the hosts.txt file in C:/Windows/System32/drivers/etc directory. Rename this file to “hosts.old.txt” (to distinguish it from the new one), and then move the file you created on the desktop to this folder. Remove the hosts.old from this folder. Now you have your hosts file as good as new.
Scan your system for possible viruses
After removing the Alaskariver.top push notifications, it’s time to see if these pop-ups brought any threat to your system. Launch GridinSoft Anti-Malware, and then click on Standard scan. It will be enough in most cases to find and remove malware. The scan will last 5-10 minutes; you are free to use your system during that process.
Once the scan is complete, you will see the detections or a notification about a clean system. Proceed with pressing the Clean Up button (or OK when nothing is detected).
User Review
( votes)References
- More about this malware type on GridinSoft Encyclopedia.
- Official Microsoft guide for hosts file reset.