Wordfence specialists report that at the beginning of January, in the popular WordPress Database Reset plugin were discovered dangerous vulnerabilities, installed on more than 80,000 sites.
This plugin, developed by WebFactory Ltd, is designed to invest in database setup and quick reset to default settings.WP Database Reset is an easy to use database reset plugin that provides users with the ability to reset any database tables on their site to the same state as a fresh WordPress install. This is handy for administrators doing testing on their website and for administrators who want to start over without requiring a complete WordPress reinstallation. This plugin provides a powerful feature that, if left unprotected, could wreak havoc for site owners. Unfortunately, that was exactly what we found in this plugin”, — write Wordfence researchers.
The first issue, tracked as CVE-2020-7048, scored 9.1 on a ten-point CVSS vulnerability rating scale.
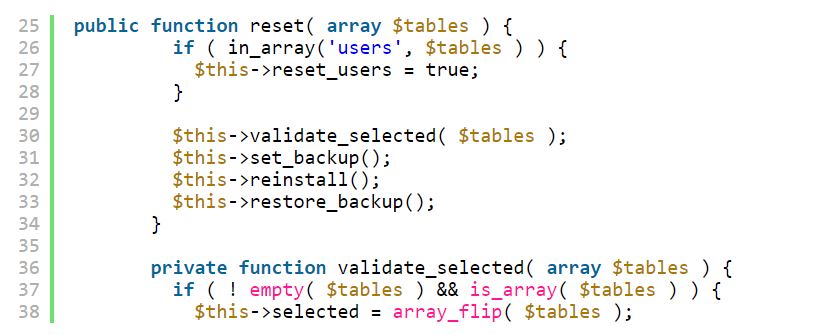
The experts found that any of the database functions are protected by any checks or warnings. Therefore, any user has the ability to reset any database tables without authentication.
All that is needed to reset the site is a simple request to delete messages, pages, comments, users, downloaded content, and so on.
The second vulnerability has the identifier CVE-2020-7047 and has 8.1 on the CVSS scale. This bug allows any authenticated user (regardless of privilege level) not to obtain administrative rights, but also to take away rights from other users with one simple request.
Thus, the attacker will remain the only administrator and completely take control of the site.
Each time a wp_users table is reset, all users are automatically deleted, including any administrators, except for the current user who is logged in. The user sending such a request will be automatically upgraded to administrator level, even if he is a simple subscriber”, – say the experts.
All users of a vulnerable plug-in recommended to immediately update it to the latest version (WP Database Reset 3.15). So far, only 8% of users have managed to do this.
The fact that WordPress plugins are vulnerable to attacks is perceived as a variant of norm, rather than something extraordinary. Only recently we wrote about dangerous vulnerabilities in the WordPress plugins WP Time Capsule and InfiniteWP. Pay attention to further recommendations and to avoid many problems.
Recommendations!
This vulnerability serves as an important reminder that maintaining site backups is an incredibly important component to maintaining the security and availability of your site.
Wordfence recommends that site owners:
- Backup regularly in intervals. Once a week would be a good place to start.
- Backup every time a major change is made on the site.
- Store backups on a server or device separate from WordPress installations. That way the integrity of your backup can be trusted in the event that the site or its server becomes compromised.


Leave a Comment