Trojan:Win32/Tiggre!plock is a type of Trojan malware that poses a significant threat to computer systems. It belongs to the Tiggre family of Trojans and is known for its ability to perform various malicious activities on infected machines.
Trojan:Win32/Tiggre!plock is primarily distributed through malicious email attachments, software downloads from untrusted sources, and exploit kits. Once it infects a system, it can perform a range of harmful actions, such as:
- Data Theft: It can steal sensitive information, including login credentials, personal data, and financial information, by logging keystrokes or capturing data from web forms.
- System Modification: The Trojan can modify system settings, disable security software, and create new entries in the Windows registry to ensure its persistence on the infected system.
- Backdoor Access: Trojan:Win32/Tiggre!plock may open a backdoor on the infected computer, allowing remote attackers to gain unauthorized access and control over the system.
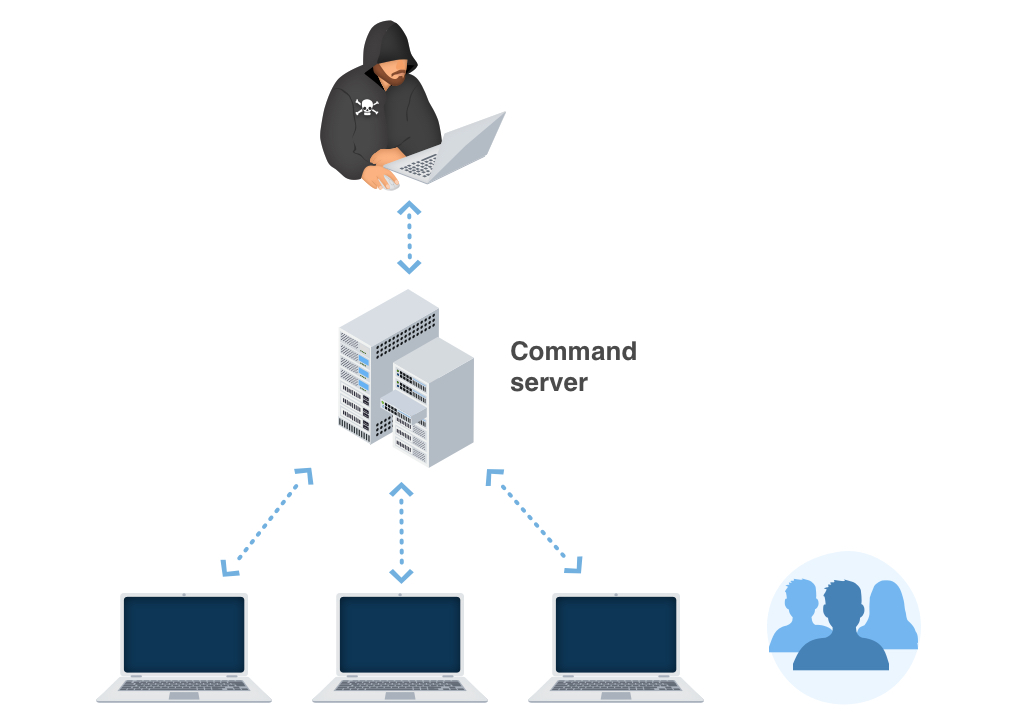
- Botnet Enrollment: The Trojan can also turn the infected computer into a part of a larger botnet, which can be used for various cybercriminal activities, such as distributed denial-of-service (DDoS) attacks.
Given its stealthy nature and the potential harm it can cause, it’s crucial to remove Trojan:Win32/Tiggre!plock promptly from an infected system. To protect your computer from such threats, it’s essential to use reputable antivirus software, keep your operating system and applications up to date, avoid downloading files from untrusted sources, and exercise caution when opening email attachments or clicking on suspicious links. Regularly scanning your system for malware and practicing safe online habits are key to staying protected from Trojans like Trojan:Win32/Tiggre!plock.
In the majority of cases, Trojan:Win32/Tiggre!plock activity is stealthy and aimed at weakening your system. These actions facilitate the entry of other malware, including spyware, worms, and even ransomware, into your system.
To prevent trojans like Trojan:Win32/Tiggre!plock from infecting your system, it is important to practice safe browsing habits, avoid downloading files from untrusted sources, be cautious with email attachments, keep your operating system and software up to date with the latest security patches, and use a reliable antivirus solution with real-time protection.
What is Trojan:Win32/Tiggre!plock?
These alterations can be as follows:
- Executable code extraction. Cybercriminals often use binary packers to hinder the malicious code from reverse-engineered by malware analysts. A packer is a tool that compresses, encrypts, and modifies a malicious file’s format. Sometimes packers can be used for legitimate ends, for example, to protect a program against cracking or copying.
- Creates RWX memory. There is a security trick with memory regions that allows an attacker to fill a buffer with a shellcode and then execute it. Filling a buffer with shellcode isn’t a big deal, it’s just data. The problem arises when the attacker is able to control the instruction pointer (EIP), usually by corrupting a function’s stack frame using a stack-based buffer overflow, and then changing the flow of execution by assigning this pointer to the address of the shellcode.
- Attempts to connect to a dead IP:Port (5 unique times);
- A process created a hidden window;
- Performs some HTTP requests;
- Unconventionial language used in binary resources: Russian;
- The binary likely contains encrypted or compressed data. In this case, encryption is a way of hiding virus’ code from antiviruses and virus’ analysts;
- Executed a very long command line or script command which may be indicative of chained commands or obfuscation;
- A scripting utility was executed;
- Uses Windows utilities for basic functionality;
- Attempts to modify proxy settings. This trick used for inject malware into connection between browser and server;
- Anomalous binary characteristics. This is a way of hiding virus’ code from antiviruses and virus’ analysts;
- Ciphering the records situated on the sufferer’s hard drive — so the victim can no longer make use of the information;
- Preventing regular accessibility to the victim’s workstation;
Similar behavior
Related domains
| z.whorecord.xyz | BScope.TrojanRansom.Crusis |
| a.tomx.xyz | BScope.TrojanRansom.Crusis |
| sslupdate1.top | BScope.TrojanRansom.Crusis |
| iplogger.org | BScope.TrojanRansom.Crusis |
| apps.identrust.com | BScope.TrojanRansom.Crusis |
| isrg.trustid.ocsp.identrust.com | BScope.TrojanRansom.Crusis |
| sslupdate2.top | BScope.TrojanRansom.Crusis |
| ocsp.int-x3.letsencrypt.org | BScope.TrojanRansom.Crusis |
Trojan:Win32/Tiggre!plock distribution
The biggest share of Trojan:Win32/Tiggre!plock virus distribution is after these methods:
- Email spam or spamming in the Facebook/Twitter
- Unlicensed software usage
- Malvertising on the Web (ads with a malicious redirect inside)
Software bundling is a widespread practice among the virus developers. Users who hack the programs to make them usable without purchasing a license approve any offer to include another program to the pack, because they are gaining money in such a way. Check precisely the installation window for signs like “Advanced installation settings” or so. The ability to switch off the malware installation often hides under such items.
Email spamming became a very popular malware distribution method, since the users do not raise suspicion on notifications from DHL or Amazon about the incoming delivery. However, it is quite easy to distinguish the malevolent email from the original one. One which is send by a cybercriminals has a strange sender address – something like [email protected], while the original email address has a specific domain name (@amazon.com or @dhl.us) and can also be seen on the official website in the “Contact us” tab.
Malicious advertisements on the web, however, is an old-timer of malware distribution. And the advice to stop clicking the blinking advertisements on untrustworthy websites exists as long as the ads on the Internet. You can also install ad blocking plugins for your web browser – they will deal with any kind of ads. However, if they are generated by adware which is already present on your PC, ad blockers will be useless.
Visible effects
In different edges of the world, victims of the Trojan:Win32/Tiggre!plock say about different signs of virus activity. Nonetheless, the common sign of the fact that you PC was hijacked with the use of backdoor is that lives its own life – mouse pointer moves without any mouse move, windows are appearing and closing autonomously; your browser may start searching something while you are sitting in front of the monitor with your hands off the input devices.
After being injected into the victim’s PC, Trojan:Win32/Tiggre!plock starts its malicious activity by connecting to the server of its distributors. After the successful connection, the backdoor receives the instructions and begins making the deep system changes. Group Policies and system registry are one of the most “loved” targets. The manner in which these elements are changed depends on the purpose the backdoor distributors choose – joining to the botnet, injecting other viruses, scaring the target or getting access to its data.
Technical details
File Info:
crc32: 559F2D45md5: ad389201c02e4edbeff9b26be6b0ea58name: eupanda.exesha1: 08b174b3890840b275aec4b6942772c61e07f4e4sha256: 2891b08c134238beeb08582e3465d77c0fff2ac4bf2cd67162b7402b7246ace4sha512: b30a496bed466136c662f9b69b9504161203458d9fc5e5afbce6175a446402526705eb9c82637e6d4bcd264b26978704829786cb8ea5e6030fc6dedef611cd82ssdeep: 49152:04PPcN/45z7p9PgYGG8BQBCqnNya/jK7:0UcO5F8eC+NT/type: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
0: [No Data]
Trojan:Win32/Tiggre!plock also known as:
| MicroWorld-eScan | Trojan.GenericKD.32763267 |
| McAfee | Artemis!AD389201C02E |
| VIPRE | Trojan.Win32.Generic!BT |
| Sangfor | Malware |
| K7AntiVirus | Trojan-Downloader ( 005594821 ) |
| Alibaba | TrojanDownloader:Win32/Generic.bae578a0 |
| K7GW | Trojan-Downloader ( 005594821 ) |
| Cybereason | malicious.389084 |
| Arcabit | Trojan.Generic.D1F3ED83 |
| BitDefenderTheta | Gen:NN.ZexaF.32515.VvW@aCEhDXhk |
| ESET-NOD32 | a variant of Win32/TrojanDownloader.Agent.ETU |
| Paloalto | generic.ml |
| Kaspersky | HEUR:Trojan-Downloader.Win32.Generic |
| BitDefender | Trojan.GenericKD.32763267 |
| APEX | Malicious |
| Rising | Downloader.Agent!1.BB58 (CLASSIC) |
| Endgame | malicious (high confidence) |
| F-Secure | Trojan.TR/Dldr.Agent.nhczh |
| DrWeb | BackDoor.Remcos.268 |
| Invincea | heuristic |
| McAfee-GW-Edition | BehavesLike.Win32.PWSZbot.tc |
| Trapmine | malicious.moderate.ml.score |
| FireEye | Generic.mg.ad389201c02e4edb |
| Sophos | Mal/Generic-S |
| SentinelOne | DFI – Suspicious PE |
| Cyren | W32/Trojan.DGWS-4195 |
| MAX | malware (ai score=84) |
| Microsoft | Trojan:Win32/Tiggre!plock |
| ViRobot | Trojan.Win32.Z.Wacatac.1821696 |
| ZoneAlarm | HEUR:Trojan-Downloader.Win32.Generic |
| Acronis | suspicious |
| VBA32 | BScope.TrojanRansom.Crusis |
| ALYac | Trojan.Agent.Wacatac |
| Ad-Aware | Trojan.GenericKD.32763267 |
| Malwarebytes | Trojan.Downloader |
| Ikarus | Worm.Win32.Ainslot |
| GData | Trojan.GenericKD.32763267 |
| AVG | FileRepMetagen [Malware] |
| Avast | FileRepMetagen [Malware] |
| CrowdStrike | win/malicious_confidence_80% (W) |
| Qihoo-360 | HEUR/QVM41.2.836B.Malware.Gen |


Leave a Comment