If you receive a notification about detecting the Trojan:Win32/Raccoon.N!MTB virus, it indicates that your PC has a problem. All malicious programs are dangerous, and there are no exceptions. The Raccoon virus focuses on stealing various categories of information from your computer.
The Trojan:Win32/Raccoon, also known as “Raccoon Infostealer,” is a type of malware that actively steals sensitive information from infected systems. It falls under the category of Trojan stealers, with its main objective being the collection of valuable data such as login credentials, credit card details, cryptocurrency wallets, and other personal information.
Raccoon Stealer commonly spreads through phishing campaigns, exploit kits, or malicious email attachments. Once it infiltrates a system, it operates discreetly, striving to evade detection by security software. It can extract data from web browsers, email clients, FTP programs, and other applications frequently used for storing sensitive information.
The stolen data is typically transmitted back to a command-and-control (C2) server controlled by the attackers. They can then exploit it for various malicious purposes, including identity theft, financial fraud, or selling the information on underground markets.
To safeguard against Trojan:Win32/Raccoon and similar threats, it is vital to maintain up-to-date security software. Additionally, exercising caution when opening email attachments or clicking on suspicious links is crucial. Regularly updating and patching software to address known vulnerabilities is also essential. Moreover, practicing good cybersecurity hygiene, such as using strong and unique passwords and enabling two-factor authentication, can significantly reduce the risk of falling victim to such malware.
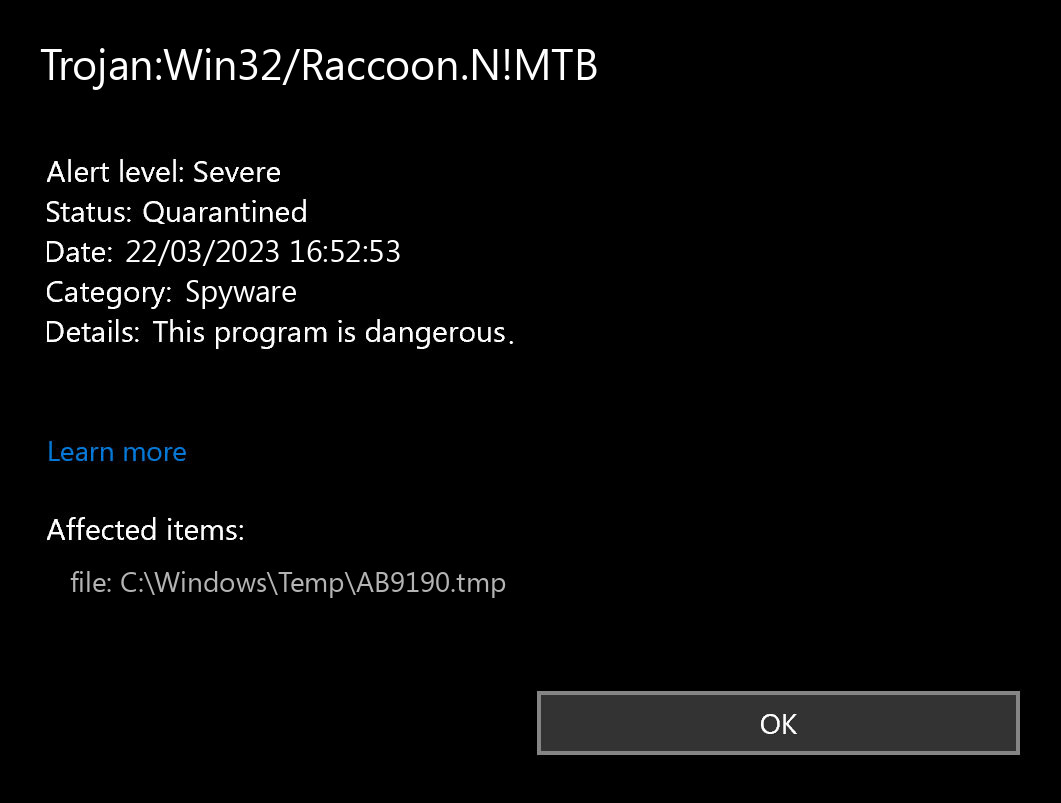
What does the notification with Trojan:Win32/Raccoon.N!MTB detection mean?
The Trojan:Win32/Raccoon.N!MTB detection you can see in the lower right corner is shown to you by Microsoft Defender. That anti-malware application is pretty good at scanning, but prone to be basically unreliable. It is prone to malware invasions, it has a glitchy interface and problematic malware removal capabilities. Therefore, the pop-up which says about the Raccoon is simply a notification that Defender has identified it. To remove it, you will likely need to use another anti-malware program.
Having Trojan:Win32/Raccoon.N!MTB malware on your PC is a bad thing from any point of view. The worst issue is that you will barely see anything wrong. Key trick of any spyware is being as secretive as possible. Some Raccoon samples also can perform self-deletion after gathering all the data available on the PC. Then, it will be almost impossible to recover the flow of events and figure out how your accounts were hacked. Variants of spyware that aim at long-term action can target the specific directory or file type. Then, files grabbed in such a way will be put for sale on the Darknet – at one of its numerous forums with stolen data.
Spyware Summary:
| Name | Raccoon Spyware |
| Detection | Trojan:Win32/Raccoon.N!MTB |
| Damage | Steal personal data contained in the attacked system. |
| Similar | Trojan:Win32/Raccoon.RE!MTB, Trojan:Win32/RaccoonStealer!MSR |
| Fix Tool | See If Your System Has Been Affected by Raccoon Spyware |
Trojan:Win32/Raccoon Technical Description
Malware Behaviour
Alternative detection names
Is Trojan:Win32/Raccoon.N!MTB dangerous?
As I said before, any malware is dangerous. And Trojan:Win32/Raccoon.N!MTB is not even near of distracting you rather than harming. The most misleading characteristic of Raccoon is the fact you cannot witness its activity by any means, other than with the use of anti-malware software scanning. And when you don’t have a clue, hackers who successfully deployed their nasty thing to your system are starting to count the money. Darknet offers numerous opportunities to sell spyware logs for a large sum – especially when these logs are newly-collected. And it is a bad idea to imagine what will happen to your accounts when other crooks will put their hands on your credentials.
However, things may have way faster turnover. In some cases, hackers are deploying their virus precisely to the user they are going to steal from. Spyware is invaluable when it comes to collecting login credentials, and some samples target precisely at online banking accounts or crypto wallets. One may say, giving spyware a run is the same as sending all your money to fraudsters.
How did I get this virus?
It is hard to line the origins of malware on your computer. Nowadays, things are mixed, and spreading methods utilized by adware 5 years ago may be utilized by spyware these days. But if we abstract from the exact distribution way and will think about why it has success, the answer will be really simple – low level of cybersecurity understanding. Individuals click on ads on weird websites, open the pop-ups they receive in their browsers, call the “Microsoft tech support” assuming that the weird banner that states about malware is true. It is very important to know what is legitimate – to stay away from misconceptions when trying to identify a virus.
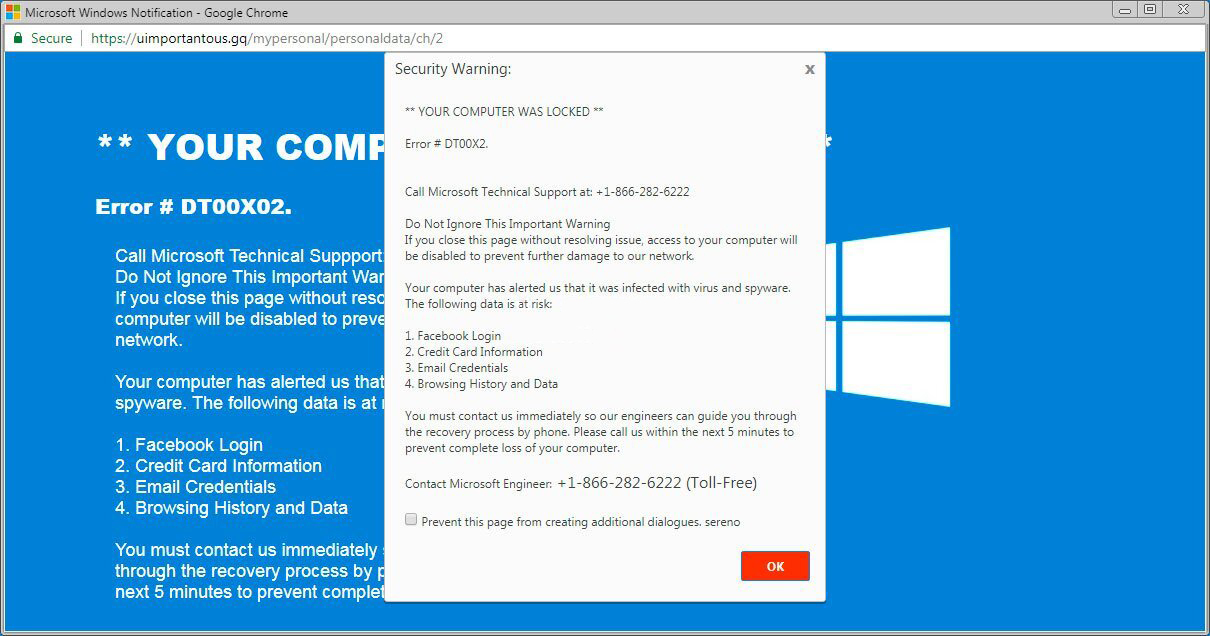
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most common tactics of malware spreading – bait e-mails and also injection into a hacked program. While the first one is not so easy to avoid – you should know a lot to recognize a fake – the second one is easy to get rid of: just don’t use cracked programs. Torrent-trackers and other sources of “totally free” applications (which are, in fact, paid, but with a disabled license checking) are really a giveaway point of malware. And Trojan:Win32/Raccoon.N!MTB is simply among them.


Leave a Comment