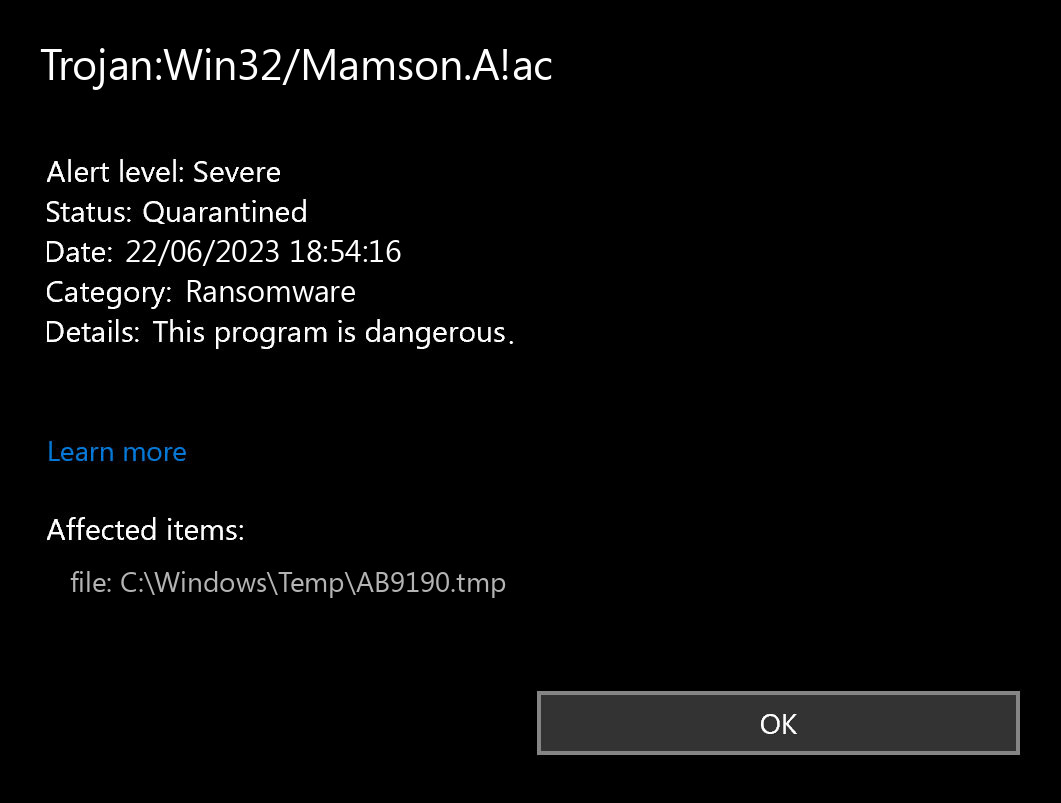
If you spectate the notification of Trojan:Win32/Mamson.A!ac detection, it looks like that your computer has a problem. All malicious programs are dangerous, with no deviations. Mamson.A is a virus that makes your system weaker for further infections.
Trojan:Win32/Mamson.A!ac is a malware that corresponds to AgentTesla remote-access trojan (RAT). This malware is often used as a stage 1 malware in ransomware attacks, which preceeds the final payload. Using AgentTesla, hackers can prepare the system to accept further infections.
Any malware exists with the only target – make money on you. And the developers of these things are not thinking about ethicality – they utilize all possible methods. Grabbing your personal data, receiving the payments for the banners you watch for them, exploiting your system components to mine cryptocurrencies – that is not the full list of what they do. Do you like to be a riding horse? That is a rhetorical question.
What is Trojan:Win32/Mamson.A!ac detection mean?
Trojan:Win32/Mamson.A!ac is a specific detection name used by Microsoft Defender. Trojan Mamson.A are a type of malware that disguises itself as legitimate files or software to trick users into executing them. Once activated, Mamson.A can perform a variety of harmful actions on the infected system.
In the case of Trojan:Win32/Mamson.A!ac, it is likely that this particular variant is designed to carry out specific malicious activities unique to its code. The specific actions of Mamson.A Trojan can vary, but common behaviors of Mamson malware include:
- Backdoor Functionality: Mamson Trojan can create a “backdoor” on the infected system, allowing remote attackers to gain unauthorized access and control over the computer. This enables cybercriminals to steal sensitive data, install additional malware, or use the compromised system for malicious activities.
- Data Theft: Some Trojans like Mamson can steal sensitive information such as login credentials, financial data, or personal files from the infected computer.
- Distributed Denial of Service (DDoS) Attacks: Mamson can be used to participate in DDoS attacks, where multiple infected computers are used to overwhelm a target server or network with a flood of traffic, causing it to become unavailable.
- Keylogging: Certain Mamson.A include keylogging functionality, which records keystrokes entered by the user. This information can be used to capture login credentials and other sensitive data.
- Adware and Spam: Some Mamson Trojans may install adware or display unwanted pop-up advertisements on the infected system, generating revenue for the attackers.
The Trojan:Win32/Mamson.A!ac detection you can see in the lower right side is displayed to you by Microsoft Defender. That anti-malware program is quite OK at scanning, however, prone to be basically unstable. It is unprotected to malware invasions, it has a glitchy user interface and bugged malware removal capabilities. Thus, the pop-up which says concerning the Mamson is rather just a notification that Defender has actually spotted it. To remove it, you will likely need to make use of another anti-malware program.
The exact Trojan:Win32/Mamson.A!ac virus is a very undesirable thing. It is present into your system disguised as a part of something benevolent, or as a piece of the tool you downloaded at a forum. Then, it makes all possible steps to make your system weaker. At the end of this “party”, it injects other viruses – ones which are wanted by crooks who control this malware. Hence, it is likely impossible to predict the effects from Mamson actions. And the unpredictability is one of the most unwanted things when it comes to malware. That’s why it is better not to choose at all, and don’t give it even a single chance to complete its task.
Threat Summary:
| Name | Mamson Ransomware |
| Detection | Trojan:Win32/Mamson.A!ac |
| Details | Mamson is attached to another program (such as a document), which can replicate and spread after an initial execution. |
Malware activities
File info
Other detection names
Is Trojan:Win32/Mamson.A!ac dangerous?
As I have stated previously, non-harmful malware does not exist. And Trojan:Win32/Mamson.A!ac is not an exception. This malware alters the system configurations, alters the Group Policies and Windows registry. All of these things are critical for proper system functioning, even when we are not talking about Windows security. Therefore, the virus which Mamson contains, or which it will download after some time, will try to get maximum profit from you. Cybercriminals can grab your personal information, and then sell it at the black market. Using adware and browser hijacker functionality, built in Trojan:Win32/Mamson.A!ac malware, they can make profit by showing you the ads. Each view gives them a penny, but 100 views per day = $1. 1000 victims who watch 100 banners per day – $1000. Easy math, but sad conclusions. It is a bad choice to be a donkey for crooks.
How did I get this virus?
It is hard to trace the sources of malware on your PC. Nowadays, things are mixed, and distribution methods utilized by adware 5 years ago can be used by spyware nowadays. However, if we abstract from the exact distribution method and will think about why it has success, the explanation will be quite basic – low level of cybersecurity understanding. People click on ads on odd websites, open the pop-ups they get in their browsers, call the “Microsoft tech support” believing that the scary banner that states about malware is true. It is very important to recognize what is legitimate – to prevent misunderstandings when trying to figure out a virus.
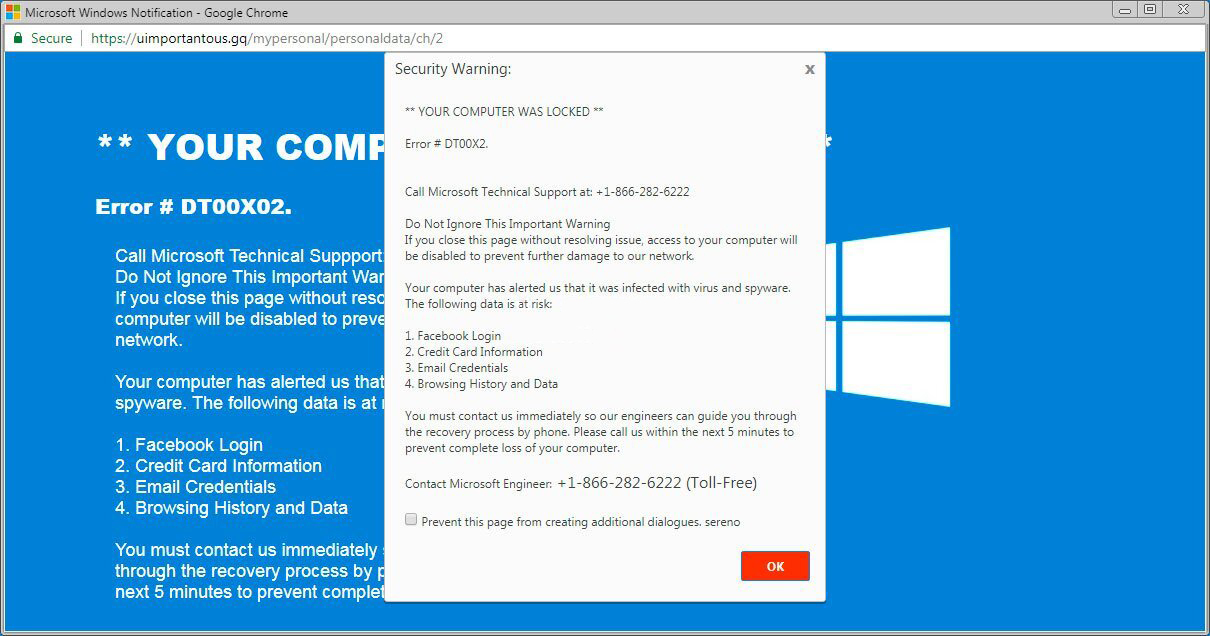
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most common tactics of malware distribution – bait e-mails and injection into a hacked program. While the first one is not so easy to stay away from – you must know a lot to understand a fake – the second one is easy to get rid of: just don’t use hacked applications. Torrent-trackers and other providers of “totally free” applications (which are, exactly, paid, but with a disabled license checking) are just a giveaway point of malware. And Trojan:Win32/Mamson.A!ac is just one of them.


Leave a Comment