What is Trojan:Win32/CryptInject!MSR infection?
In this article you will find about the interpretation of Trojan:Win32/CryptInject!MSR and its adverse effect on your computer. This trojan-downloader is often used to deliver ransomware on your PC. Exactly, this feature is displayed in its detection name. To make ransomware functioning possible, that virus makes several changes deeply in your system.
About 30 minutes ago, windows defender asked me to restart to remove a trojan, so I did.
After it restarted, WD notified me again that it found a trojan (I looked at the name, the same trojan). I looked at windows support about this trojan. All it said is that WD removes this Trojan.
But I removed/Quarantined and restarted multiple times now, and it’s the same. After I saw the virus the second time, I disconnected my pc from the internet.Reddit
In the majority of the situations, Trojan:Win32/CryptInject!MSR will not try to show its presence in your system. The more time that virus will be active, the more additional viruses it will bring into your system.
Trojan:Win32/CryptInject!MSR Summary
The changes done by that virus are next:
- Executable code extraction. Cybercriminals often use binary packers to hinder the malicious code from reverse-engineered by malware analysts. A packer is a tool that compresses, encrypts, and modifies a malicious file’s format. Sometimes packers can be used for legitimate ends, for example, to protect a program against cracking or copying.
- Creates RWX memory. There is a security trick with memory regions that allows an attacker to fill a buffer with a shellcode and then execute it. Filling a buffer with a shellcode isn’t a big deal. It’s just data. The problem arises when the attacker can control the instruction pointer (EIP), usually by corrupting a function’s stack frame using a stack-based buffer overflow and then changing the flow of execution by assigning this pointer to the address of the shellcode.
- Reads data out of its own binary image. The trick that allows the malware to read data out of your computer’s memory.
Everything you run, type, or click on your computer goes through the memory. This includes passwords, bank account numbers, emails, and other confidential information. With this vulnerability, there is the potential for a malicious program to read that data.
- A process created a hidden window;
- Network activity detected but not expressed in API logs. Microsoft built an API solution right into its Windows operating system. It reveals network activity for all apps and programs that ran on the computer in the past 30-days. This malware hides network activity.
- Anomalous binary characteristics. This is a way of hiding the virus code from antiviruses and virus analysts.
Similar behavior
Related domains
| z.whorecord.xyz | BehavesLike.Win32.Ransom.fc |
Ways of Trojan:Win32/CryptInject!MSR dirstribution
The biggest share of Trojan:Win32/CryptInject!MSR virus distribution is after these methods:
Email spamming became a trendy malware distribution method since the users do not raise suspicion on notifications from DHL or Amazon about the incoming delivery. However, it is quite easy to distinguish the malevolent email from the original one. One which is sent by cybercriminals has a strange sender address – something like [email protected]. Simultaneously, the original email address has a specific domain name (@amazon.com or @dhl.us) and can also be seen on the official website in the “Contact us” tab.
Malicious advertisements on the web, however, is an old-timer of malware distribution. And the advice to stop clicking the blinking advertisements on untrustworthy websites exists as long as the ads on the Internet. You can also install ad-blocking plugins for your web browser – they will deal with any ads. However, if they are generated by adware already present on your PC, ad blockers will be useless.
Software bundling is a widespread practice among the virus developers. Users who hack the programs to make them usable without purchasing a license approve any offer to include another program in the pack because they are gaining money in such a way. Check precisely the installation window for signs like “Advanced installation settings” or so. The ability to switch off the malware installation often hides under such items.
How can I detect that Trojan:Win32/CryptInject!MSR is present on my PC?
In different edges of the world, victims of the Trojan:Win32/Masson.A!ac say about different signs of virus activity. Nonetheless, the common sign that a trojan downloader infected your PC is a tremendous slowdown of your system. It is tough to miss that moment because even the most powerful PCs become slow as snails when 3-5 viruses begin working simultaneously. This specific trojan is concentrated on injecting the ransomware, so you will not see a huge pack of viruses. But it still does not make things easier since ransomware is one of the most dangerous viruses in the present modern computer world.
As I mentioned before, XXXXXX downloader makes several changes to the system configurations. It disables the Microsoft Defender – the embedded anti-malware solution for Windows. A lot of users do not make use of third-party antivirus programs because of the Defender availability. But the fact that it can be disabled in several clicks through the Group Policies settings creates a big risk.
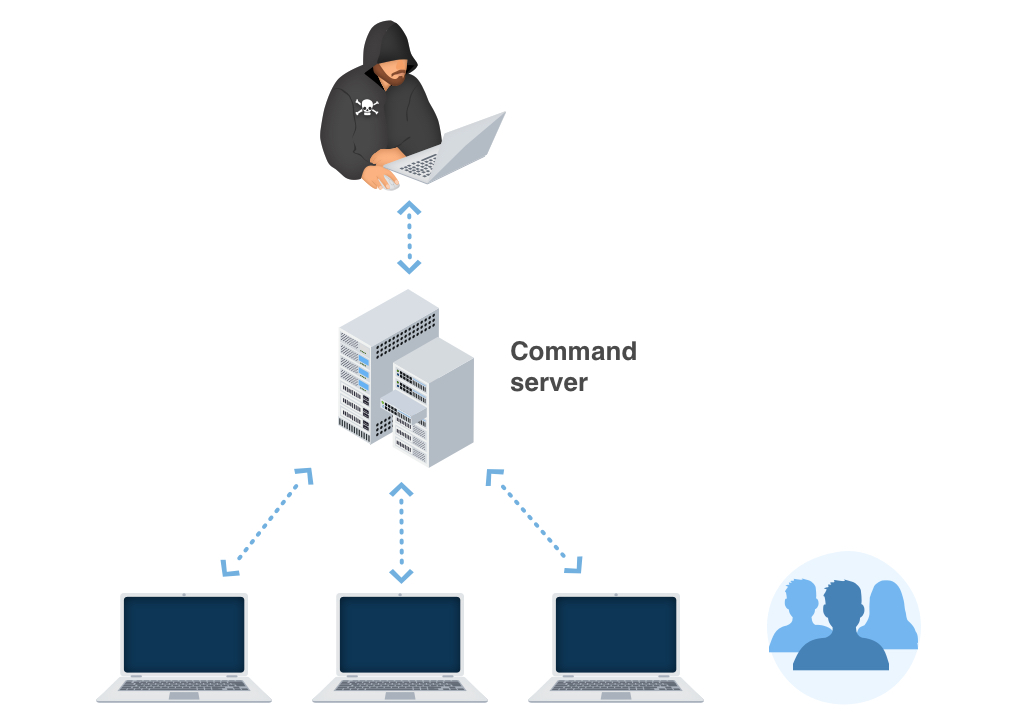
Another thing changed by this Trojan virus is networking settings. Exactly, the thing which became changed is the HOSTS file. That file contains DNS settings for the specific websites. When it comes to XXXXXXXX activity, several additional entries are added. These entries allow the virus to connect to malware distributors’ control server and get the other viruses. Malware can also block the connection to different anti-malware forums and same-themed sites to prevent searching the malware removal guide.
Technical details
File Info:
crc32: FC8EC4B0md5: f13a3dcedc065a5d78902b34a31e5da4name: dbvghvxczs.exesha1: 06f5665cfbea544b19f00621c82bbff63c0a493esha256: c8e5fe3ab420cf3a756868068d8f498e22f9f03a9f598219af8ee955a8b2d5a4sha512: ed7735ce396092f5dc8fcff1381e49ee5687dc9e4fa4892bda489c9f706a7db0d98bf07a68e7dde9a3cff8eb6437d09f0cb645937d112669b78c3ac08093532dssdeep: 6144:W1kBLmHZCCxtbKjiXHyleVrmDBmfIIrZnRd:W1kIHZB+j+SlWQstype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
LegalCopyright: Copyright (C) hemipinnate 2019InternalName: sleuthhound.exeFileVersion: 1.5.5.3CompanyName: hoo-haProductName: bopyridProductVersion: 6.6.1.8FileDescription: copastorsOriginalFilename: embryoma.exeTranslation: 0x0409 0x04b0
Trojan:Win32/CryptInject!MSR also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Cylance | Unsafe |
| Sangfor | Malware |
| Cybereason | malicious.cfbea5 |
| BitDefenderTheta | Gen:NN.ZexaF.32519.xu3@aaEOspli |
| Symantec | ML.Attribute.HighConfidence |
| APEX | Malicious |
| Kaspersky | UDS:DangerousObject.Multi.Generic |
| Rising | [email protected] (RDML:FUxwgqJIVkVr6Kd0JQGRRw) |
| F-Secure | Heuristic.HEUR/AGEN.1044893 |
| Invincea | heuristic |
| McAfee-GW-Edition | BehavesLike.Win32.Ransom.fc |
| Avira | HEUR/AGEN.1044893 |
| Endgame | malicious (high confidence) |
| ZoneAlarm | Trojan-Dropper.Win32.Scrop.aafc |
| Microsoft | Trojan:Win32/CryptInject!MSR |
| ESET-NOD32 | a variant of Win32/GenKryptik.DZQT |
| AVG | FileRepMalware |
| CrowdStrike | win/malicious_confidence_100% (D) |
| Qihoo-360 | HEUR/QVM20.1.C3C1.Malware.Gen |
How to remove Trojan:Win32/CryptInject!MSR ransomware?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials, or crypt your documents for ransom.
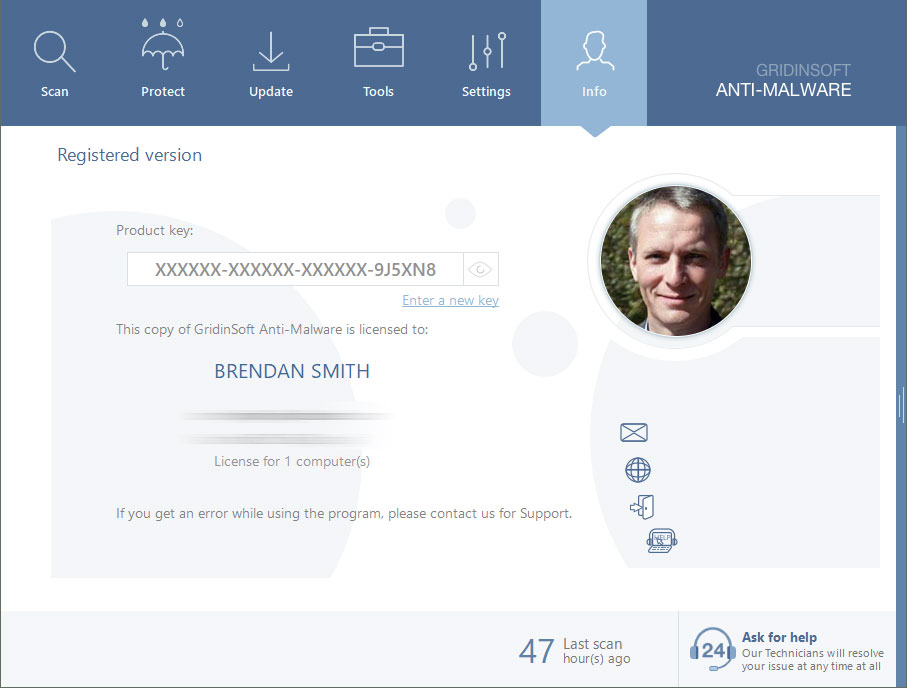
Reasons why I would recommend GridinSoft1
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes.2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When the setup file has finished downloading, double-click on the install-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Trojan:Win32/CryptInject!MSR files and other malicious programs. This process can take 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in the right corner.

Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
If the guide doesn’t help you to remove Trojan:Win32/CryptInject!MSR you can always ask me in the comments to get help.
User Review
( votes)References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison



My pc is infected with this torjan i will be glad if you help me please