What is Trojan:Win32/Azorult!ml infection?
In the majority of the situations, Trojan:Win32/Wacatac.D!ml infection will not try to show its presence in your system. The more time that virus will be active, the more data it will steal from the user’s PC.
Trojan:Win32/Azorult!ml Summary
These adjustments can be as complies with:
- Stealing Steam, Telegram, Skype login & password.
- Stealing cryptocurrency wallets.
- Downloading malware to the computer and running it.
- Stealing browser cookies, saved passwords, browsing history, and more.
- Viewing and manipulating files on victim’s computer.
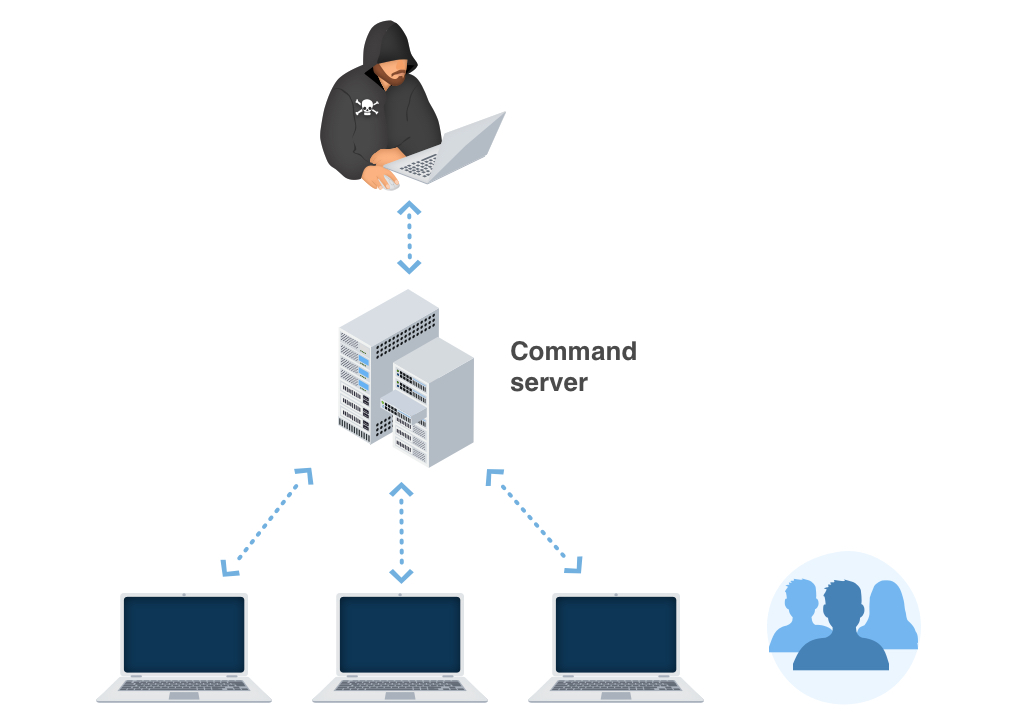
- Allowing the hackers to perform other tasks on the victim’s computer remotely.
- Executable code extraction. Cybercriminals often use binary packers to hinder the malicious code from reverse-engineered by malware analysts. A packer is a tool that compresses, encrypts, and modifies a malicious file’s format. Sometimes packers can be used for legitimate ends, for example, to protect a program against cracking or copying.
- Creates RWX memory. There is a security trick with memory regions that allows an attacker to fill a buffer with a shellcode and then execute it. Filling a buffer with shellcode isn’t a big deal, it’s just data. The problem arises when the attacker is able to control the instruction pointer (EIP), usually by corrupting a function’s stack frame using a stack-based buffer overflow, and then changing the flow of execution by assigning this pointer to the address of the shellcode.
- Possible date expiration check, exits too soon after checking local time;
- Expresses interest in specific running processes;
- The binary likely contains encrypted or compressed data. In this case, encryption is a way of hiding virus’ code from antiviruses and virus’ analysts.
- Checks the CPU name from registry, possibly for anti-virtualization;
- Collects information to fingerprint the system. There are behavioral human characteristics that can be used to digitally identify a person to grant access to systems, devices, or data. Unlike passwords and verification codes, fingerprints are fundamental parts of user’s identities. Among the threats blocked on biometric data processing and storage systems is spyware, the malware used in phishing attacks (mostly spyware downloaders and droppers), ransomware, and Banking Trojans as posing the greatest danger.
- Anomalous binary characteristics. This is a way of hiding virus’ code from antiviruses and virus’ analysts.
- Slows down the disk responses due to the heavy disk usage. Especially actual for obsolete systems with HDD as a main storage device.
Similar behavior
Related domains
| z.whorecord.xyz | Ransomeware.CRAB.gen |
| a.tomx.xyz | Ransomeware.CRAB.gen |
Trojan:Win32/Azorult!ml – how is it distributed?
The majority of cases of Trojan:Win32/Azorult!ml malware delivery goes to these ways:
Email spamming became a prevalent malware distribution method since the users do not raise suspicion on notifications from DHL or Amazon about the incoming delivery. However, it is quite easy to distinguish the malevolent email from the original one. One which is sent by cybercriminals has a strange sender address – something like [email protected], while the original email address has a specific domain name (@amazon.com or @dhl.us) and can also be seen on the official website in the “Contact us” tab.
Malicious advertisements on the web, however, is an old-timer of malware distribution. And the advice to stop clicking the blinking advertisements on untrustworthy websites exists as long as the ads on the Internet. You can also install ad-blocking plugins for your web browser – they will deal with any ads. However, if they are generated by adware already present on your PC, ad blockers will be useless.
Software bundling is a widespread practice among the virus developers. Users who hack the programs to make them usable without purchasing a license approve any offer to include another program in the pack because they are gaining money in such a way. Check precisely the installation window for signs like “Advanced installation settings” or so. The ability to switch off the malware installation often hides under such items.
How can I see that my computer is damaged with Trojan:Win32/Azorult!ml?
Trojan:Win32/Azorult!ml activity is quite hard to detect. And it is not a thing you need to wonder about – viruses like this one must stay undetected to be more effective and bring more effects. All changes it does are far away from the places where the user works. Group Policies, notifications settings, registry, Task Scheduler – these parts of the operating system are visited only when something goes wrong. And users get the fact that something is wrong only after the successful Wacatac activity.
It is quite hard to detect the changes in registry and Group Policies because of the huge number of entries in these system elements. But the notifications settings, and, especially, Task Scheduler, are elementary to control. If you see that the programs you are used to receiving notifications have stopped sending them to you or several programs are added to the list, it is better to raise suspicion. The scheduler is a rare-used application, so if you had nothing scheduled and now see that something appeared in it, launch the anti-malware program.
Technical details
File Info:
crc32: 23235217md5: 9d2525f509ceaca86c328966184108f9name: 9D2525F509CEACA86C328966184108F9.mlwsha1: b59d1b5a3017f49bc6d905ce8afce4e5158807b3sha256: 3d5fecc27cfebb7c9de41a880bcc0e3f068ee0e13ad2301ac43421211f71d692sha512: dfe39e2371ed4d493367bd99ce53d1d6e4f312a066d40d4c6a3c6307a7069ecf6a8263fd48cb68e96fc3ae0b013696c0e7607fedce14ef8b332ce32078fceca1ssdeep: 49152:qX65oLuPfn1s01tZ+fx+sj0iDMt8a4cmN9glrccKJhVf0Ka1Q+tuyL0OZMhTc+0:qJiRwZ+riAl4cmNelYcflQRNZ0Fqtype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
LegalCopyright: WsegFileVersion: 67.0.0.55ProductVersion: 67.0.0.5Translation: 0x0409 0x07ec
Trojan:Win32/Azorult!ml also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Bkav | W32.AIDetectVM.malware1 |
| Elastic | malicious (high confidence) |
| Qihoo-360 | HEUR/QVM10.1.0A69.Malware.Gen |
| Cylance | Unsafe |
| Sangfor | Malware |
| Cybereason | malicious.a3017f |
| BitDefenderTheta | Gen:NN.ZexaF.34804.4t0@aK37cufG |
| Cyren | W32/Kryptik.DEA.gen!Eldorado |
| Symantec | ML.Attribute.HighConfidence |
| Paloalto | generic.ml |
| Rising | [email protected] (RDML:K/QNP7EnTXQGV63C+GLozQ) |
| McAfee-GW-Edition | BehavesLike.Win32.Emotet.wc |
| FireEye | Generic.mg.9d2525f509ceaca8 |
| Sophos | ML/PE-A |
| SentinelOne | Static AI – Malicious PE |
| Microsoft | Trojan:Win32/Azorult!ml |
| Cynet | Malicious (score: 100) |
| VBA32 | BScope.Trojan.Wacatac |
| Malwarebytes | Trojan.MalPack.GS |
| APEX | Malicious |
| Ikarus | Trojan.Win32.FakeAV |
| eGambit | Unsafe.AI_Score_99% |
| AVG | FileRepMalware |
| Avast | FileRepMalware |
| CrowdStrike | win/malicious_confidence_80% (D) |
| MaxSecure | Ransomeware.CRAB.gen |
How to remove Trojan:Win32/Azorult!ml virus?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials, or crypt your documents for ransom.
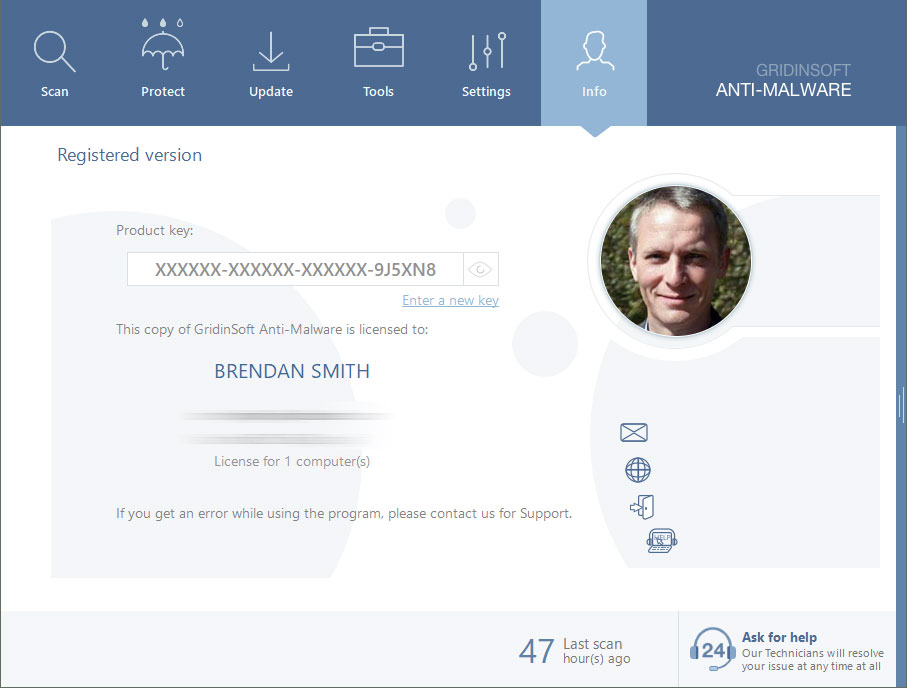
Reasons why I would recommend GridinSoft1
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

Are Your Protected?
If the guide doesn’t help you to remove Trojan:Win32/Azorult!ml, you can always ask me in the comments to get help.


Leave a Comment