If you spectate the alert of Trojan:MSIL/Redline.RA!MTB detection, it seems that your system has a problem. All malicious programs are dangerous, with no exceptions. Redline is malicious software that targets on grabbing different types of information from your system. It applies a lot of tricks to dodge security software detection and uses secured connections to exfiltrate data. The activity of this malware usually ends up with losing access to your accounts and exposing your identity. Moreover, some samples are also able to deliver other malicious programs to the system.
Any type of malware exists with the only target – generate profits on you1. And the developers of these things are not thinking about ethicality – they utilize all available ways. Taking your personal data, receiving the comission for the advertisements you watch for them, exploiting your system components to mine cryptocurrencies – that is not the complete list of what they do. Do you want to be a riding equine? That is a rhetorical question.
What does the pop-up with Trojan:MSIL/Redline.RA!MTB detection mean?
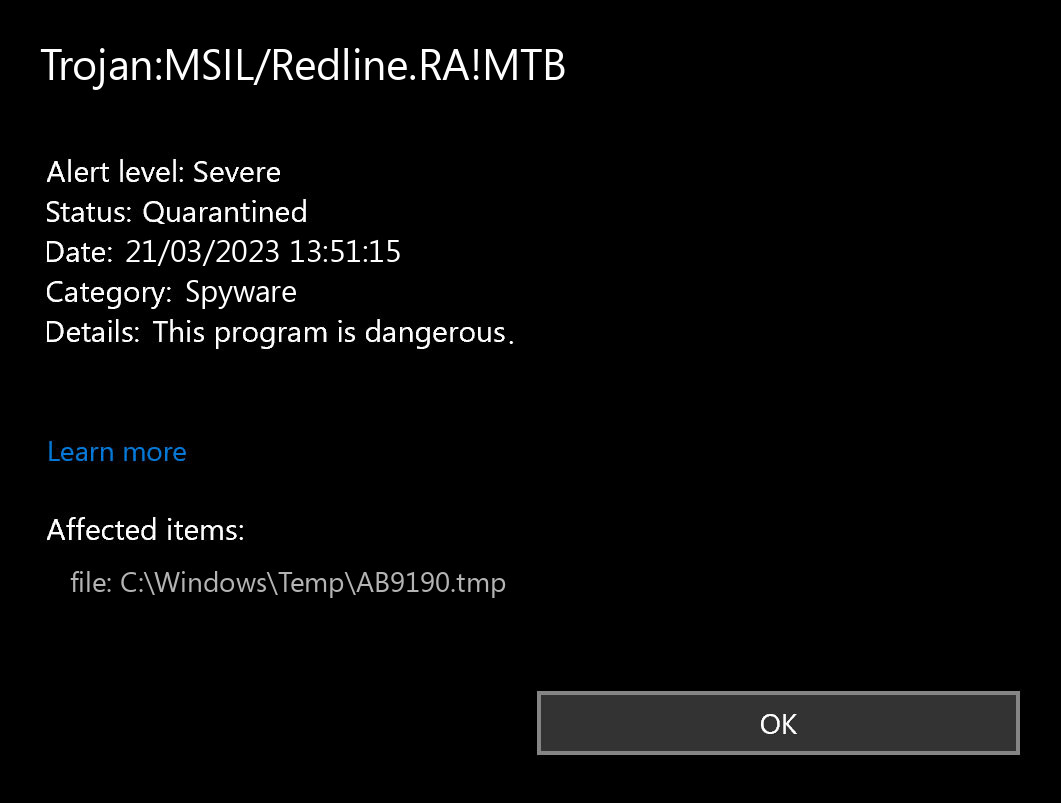
The Trojan:MSIL/Redline.RA!MTB detection you can see in the lower right corner is shown to you by Microsoft Defender. That anti-malware software is pretty good at scanning, but prone to be mainly unstable. It is prone to malware invasions, it has a glitchy interface and problematic malware removal capabilities. Therefore, the pop-up which states concerning the Redline is rather just an alert that Defender has spotted it. To remove it, you will likely need to use a separate anti-malware program.
Having Trojan:MSIL/Redline.RA!MTB malware on your PC is a bad thing from any point of view. The worst issue is that you will not discover anything wrong. The key trick of any spyware is being as stealthy as possible. Some Redline samples are also able to perform self-deletion after gathering all the valuable information present in the system. After that, it will be practically impossible to recover the flow of events and figure out how your accounts were hacked. Variants of spyware that aim at long-term action can target the specific folder in the system or file type. Then, files grabbed in that way will be put for sale on the Darknet – at one of its numerous marketplaces with leaked data.
Spyware Summary:
| Name | Redline Spyware |
| Detection | Trojan:MSIL/Redline.RA!MTB |
| Damage | Steal personal data contained in the attacked system. |
| Similar | Trojan:Win32/Redline.SHL!MTB, Trojan:Win32/Redline.UR!MTB |
| Fix Tool | See If Your System Has Been Affected by Redline Spyware |
Trojan:MSIL/Redline.RA!MTB Technical Details
Behavioural patterns
Alternative detection names
Is Trojan:MSIL/Redline.RA!MTB dangerous?
As I said before, any malware is dangerous. And Trojan:MSIL/Redline.RA!MTB is not even near of distracting you rather than harming. The most deceptive characteristic of Redline is the fact you cannot witness its activity by any means, other than with the use of anti-malware software scanning. And when you are having no clue, cybercriminals who delivered their nasty thing to your system are starting to count the money. Darknet offers a lot of opportunities to sell malware logs for a hefty sum – especially when these logs are newly-collected. And you’d better not imagine what will happen to your accounts when other rascals will put their hands on your login credentials.
However, things may have much faster turnover. In some situations, crooks are deploying their virus precisely to the user they are trying to rob. Spyware is invaluable when it comes to collecting credentials, and some examples aim precisely at online banking accounts or crypto wallets. One may say, giving spyware a run equals to sending all your money to criminals.
How did I get this virus?
It is difficult to trace the sources of malware on your computer. Nowadays, things are mixed up, and spreading ways used by adware 5 years ago can be used by spyware these days. But if we abstract from the exact spreading way and will think of why it has success, the reply will be really basic – low level of cybersecurity understanding. Individuals press on ads on strange websites, click the pop-ups they receive in their browsers, call the “Microsoft tech support” thinking that the weird banner that states about malware is true. It is very important to understand what is legitimate – to avoid misconceptions when attempting to determine a virus.
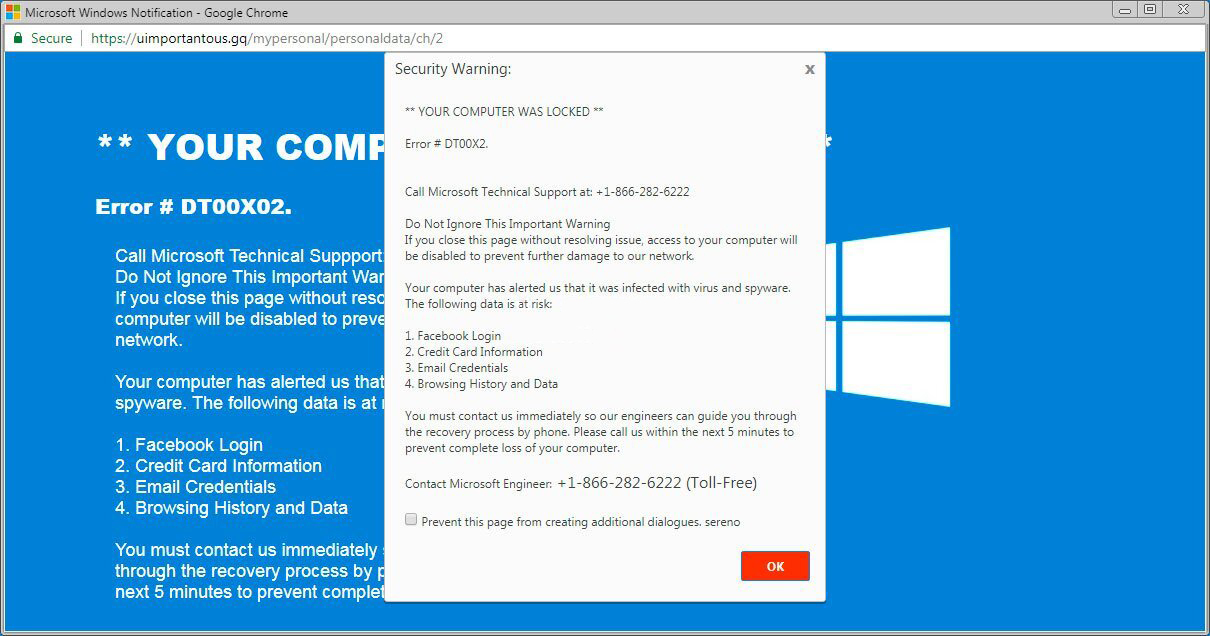
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most common methods of malware distribution – lure e-mails and also injection into a hacked program. While the first one is not so easy to evade – you need to know a lot to understand a fake – the 2nd one is simple to handle: just don’t utilize hacked programs. Torrent-trackers and various other providers of “totally free” applications (which are, actually, paid, but with a disabled license checking) are just a giveaway point of malware. And Trojan:MSIL/Redline.RA!MTB is just among them.
How to remove the Trojan:MSIL/Redline.RA!MTB from my PC?
Trojan:MSIL/Redline.RA!MTB malware is incredibly difficult to remove manually. It places its documents in a variety of places throughout the disk, and can restore itself from one of the parts. Furthermore, a range of changes in the registry, networking configurations and also Group Policies are fairly hard to locate and return to the original. It is far better to make use of a special program – exactly, an anti-malware tool. GridinSoft Anti-Malware will definitely fit the most ideal for virus removal goals.
Why GridinSoft Anti-Malware? It is pretty light-weight and has its detection databases updated almost every hour. Moreover, it does not have such bugs and exposures as Microsoft Defender does. The combination of these facts makes GridinSoft Anti-Malware perfect for eliminating malware of any kind.
Remove the viruses with GridinSoft Anti-Malware
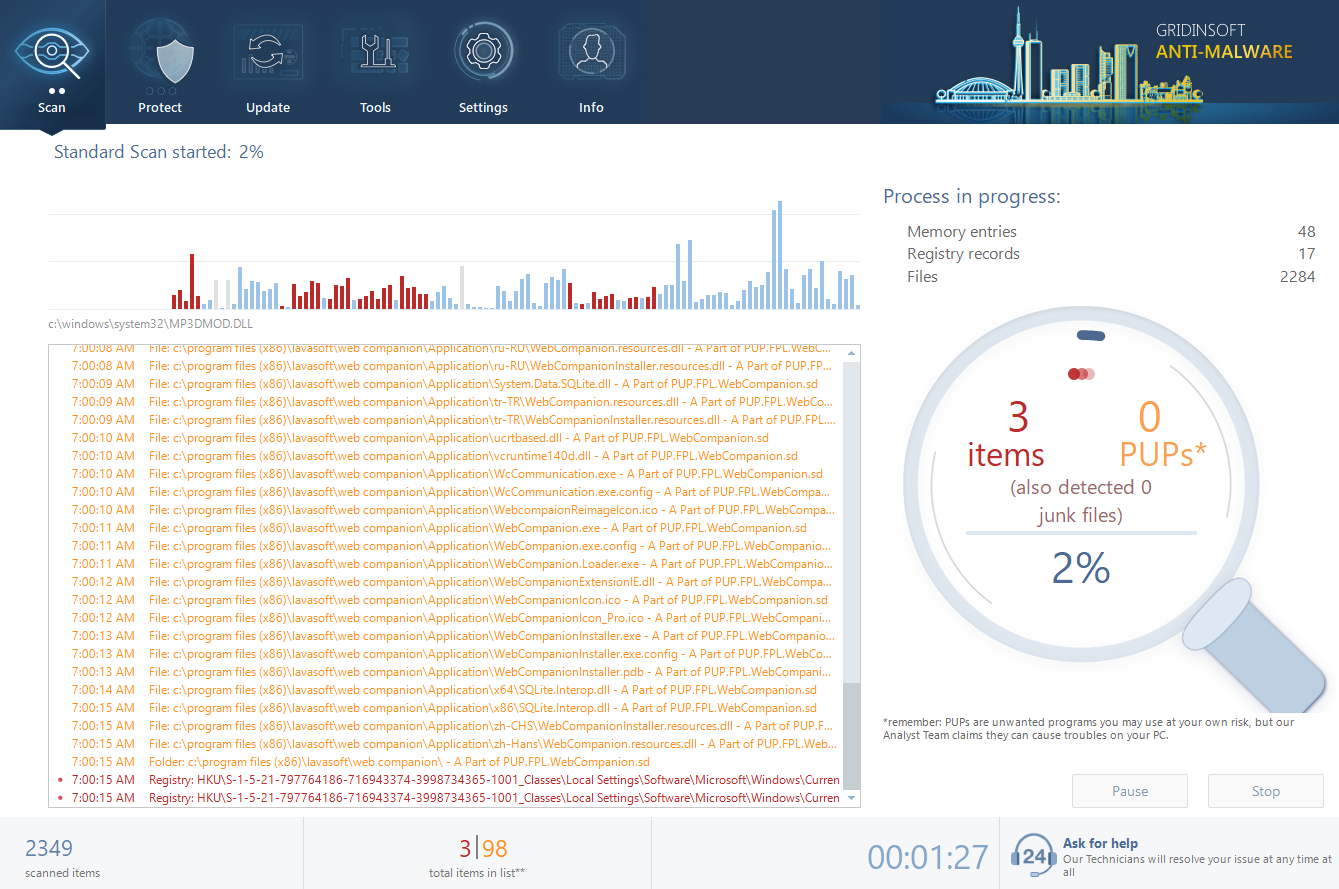
- Download and install GridinSoft Anti-Malware. After the installation, you will be offered to perform the Standard Scan. Approve this action.
- Standard scan checks the logical disk where the system files are stored, together with the files of programs you have already installed. The scan lasts up to 6 minutes.
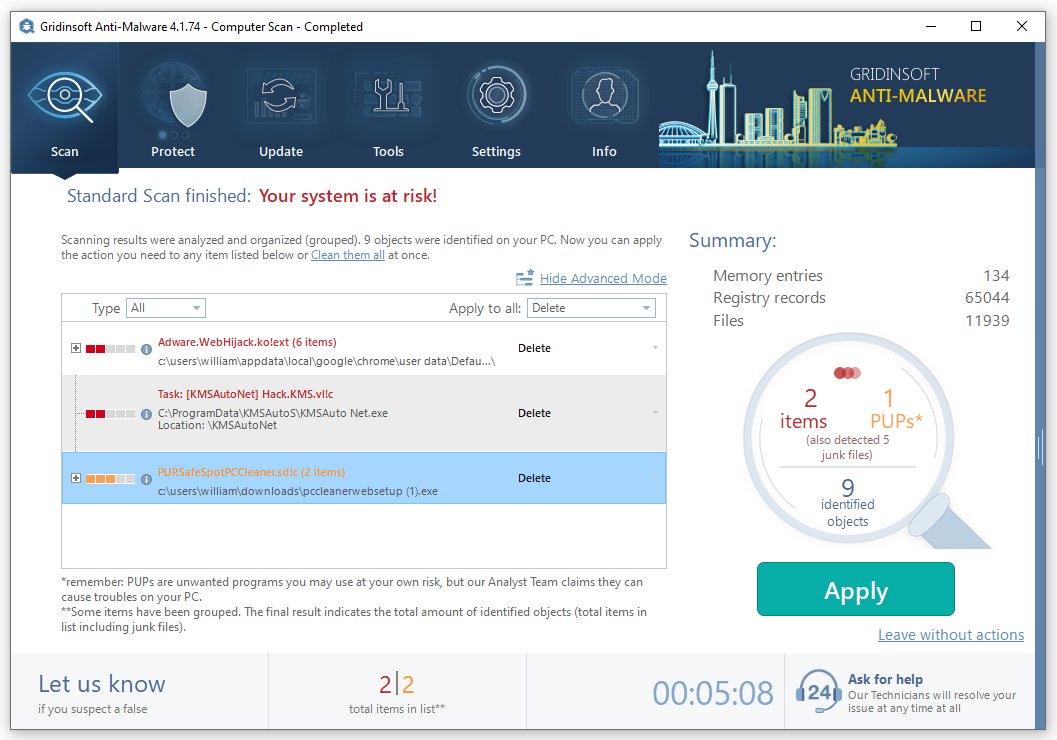
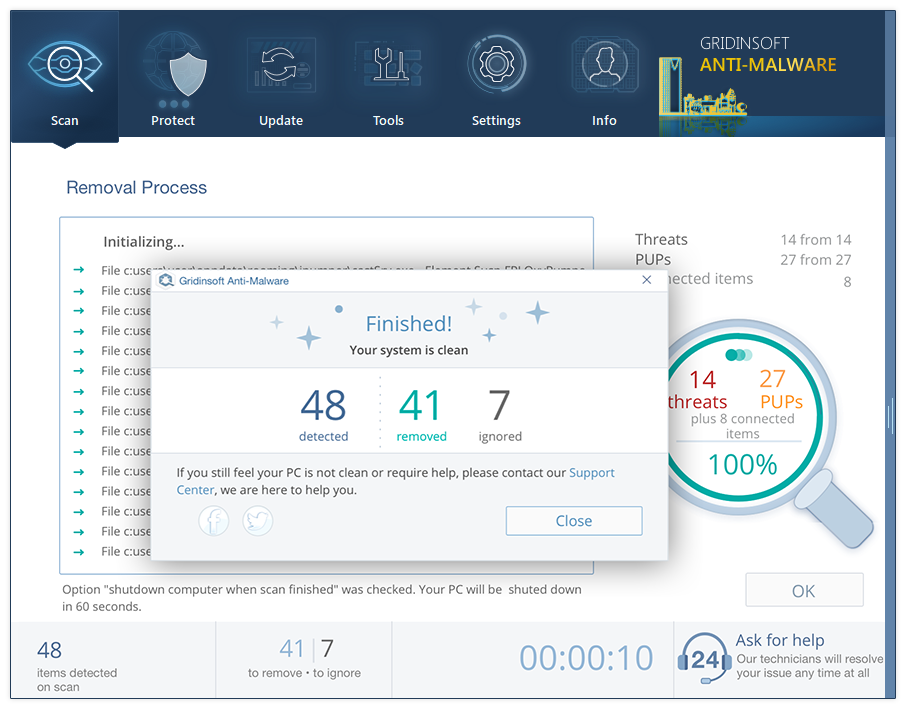
- When the scan is over, you may choose the action for each detected virus. For all files of Redline the default option is “Delete”. Press “Apply” to finish the malware removal.
User Review
( votes)References
- Read about malware types on GridinSoft Threat encyclopedia.


hi robert
to make sure i have something to work on until well after my death, i am trying to use visual basic 2022 to create my own computer language.
? will i be able to use msbuild or vbc to compile a (text) file into an (exe) file .. or does the compiling process involve a non-text file ?
thanks for your time .. jerry