In the ever-evolving landscape of cybersecurity threats, malicious actors constantly seek innovative methods to compromise systems and steal sensitive information. One such threat that has emerged is the “Stealerium Stealer“.
This sophisticated tool combines the capabilities of a stealer, clipper, and keylogger, making it a potent weapon in the hands of cybercriminals. In this article, we delve into the mechanics, features, and potential implications of Stealerium Stealer.
What is Stealerium Stealer
Stealerium Stealer is a piece of malicious software crafted using the C# programming language. Its primary purpose is to infiltrate target systems, covertly gather sensitive data, and transmit it to a remote location via a Discord channel using a webhook. This multi-faceted threat is designed to evade various forms of analysis, including VirtualBox, Sandbox, Debugger, VirusTotal, and Any.Run, ensuring its activities remain hidden from security measures.
| Name | Stealerium Stealer |
| Detection | Trojan:Win32/Formbook!ml |
| Damage | Harvesting sensitive data, including passwords, financial details, and personal information, through advanced techniques such as keylogging, clipboard manipulation, and browser data extraction, thereby potentially leading to identity theft, financial loss, and unauthorized access. |
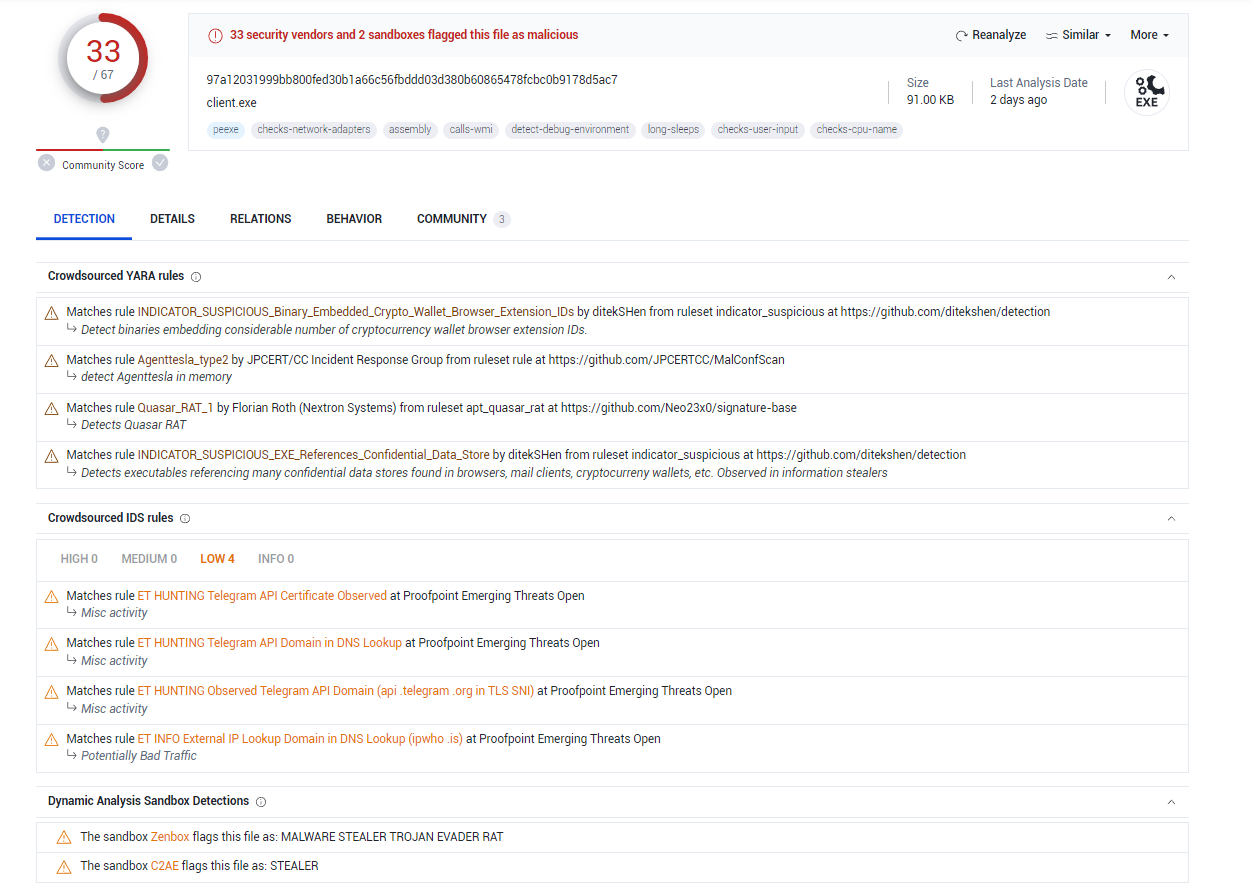
Stealerium Stealer on VirusTotal
Data Extraction Capabilities
Stealerium Stealer boasts an alarming array of data extraction capabilities:
- System Information: It extracts detailed system information, including version details, CPU specifications, GPU details, RAM information, IPs, BSSID, geographical location, screen metrics, and installed applications.
- Browser Data: The stealer targets Chromium-based browsers (e.g., Chrome, Edge) and Firefox-based browsers, pilfering passwords, credit card details, cookies, browsing history, autofill data, and bookmarks.
- Internet Explorer/Edge Passwords: It specifically targets saved passwords in Internet Explorer and Microsoft Edge browsers.
- Wi-Fi Networks: The tool gathers information about saved Wi-Fi networks and scans for networks in proximity (SSID, BSSID).
- File Grabber: Stealerium Stealer is capable of extracting a wide range of file types, including documents, images, source code, databases, and USB-connected files.
- Banking and Cryptocurrency Services: The threat can detect and extract data related to banking and cryptocurrency services accessed through browsers.
- Gaming Platforms: It targets gaming sessions on platforms like Steam, Uplay, Battle.Net, and Minecraft.
- Crypto Wallets: The stealer is capable of extracting sensitive data from a variety of cryptocurrency wallets, including Zcash, Armory, Bytecoin, and more.
- Crypto Wallet Extensions: It targets cryptocurrency wallet extensions from popular browsers, potentially compromising wallets associated with Binance, Metamask, BitApp, and others.
- Messenger Data: The threat compromises messenger sessions, accounts, and tokens from platforms such as Discord, Telegram, Skype, and Signal.
Advanced Features
Stealerium Stealer goes beyond traditional data extraction with its advanced features:
- Keylogger: The keylogger component activates when users engage in text input or access a banking website, capturing keystrokes and potentially stealing sensitive information.
- Clipper: The clipper component monitors clipboard activity and replaces cryptocurrency wallet addresses with malicious ones when users engage in transactions.
- Webcam Screenshots: This feature captures screenshots from a user’s webcam if they access inappropriate content online, potentially invading privacy and security.
Frequently Asked Questions (FAQ)
Conclusion
The emergence of Stealerium Stealer highlights the increasing sophistication of cyber threats that target users’ personal information, sensitive data, and financial assets. Its ability to combine a stealer, clipper, and keylogger into a single tool presents a significant challenge for individuals and organizations striving to maintain cybersecurity. As cybercriminals continue to refine their tactics, staying informed and implementing robust security measures remains paramount to safeguard against such threats.


Leave a Comment