PUA:Win32/HackTool is a generic detection name used by Microsoft Defender and other security software to identify potentially unwanted applications (PUAs) that fall under the category of “HackTools.” These are software tools or utilities that can be misused for illicit purposes or to gain unauthorized access to systems, networks, or sensitive information.
HackTools are not inherently malicious; they often serve legitimate purposes in the hands of system administrators, cybersecurity professionals, or other authorized users. However, they can also be used by malicious actors to compromise security or violate privacy.
Examples of HackTools include password-cracking utilities, network scanning tools, keyloggers, and other software designed for unauthorized system access, password theft, or exploiting vulnerabilities in systems and software.
Since HackTools have the potential to be misused for malicious activities, antivirus programs and security software flag them as potentially unwanted applications. When PUA:Win32/HackTool is detected, it is recommended to carefully assess the tool’s intended use, ensure it is being used responsibly and within the boundaries of the law and ethical standards.
Users should avoid downloading HackTools from untrusted sources or using them for any malicious purposes. Instead, they should rely on authorized and legal means to access or recover sensitive information and maintain the security of their systems and data.
Any type of malware exists with the only target – generate profits on you. And the programmers of these things are not thinking about morality – they use all possible ways. Grabbing your private data, getting the payments for the banners you watch for them, exploiting your system to mine cryptocurrencies – that is not the full list of what they do. Do you like to be a riding steed? That is a rhetorical question.
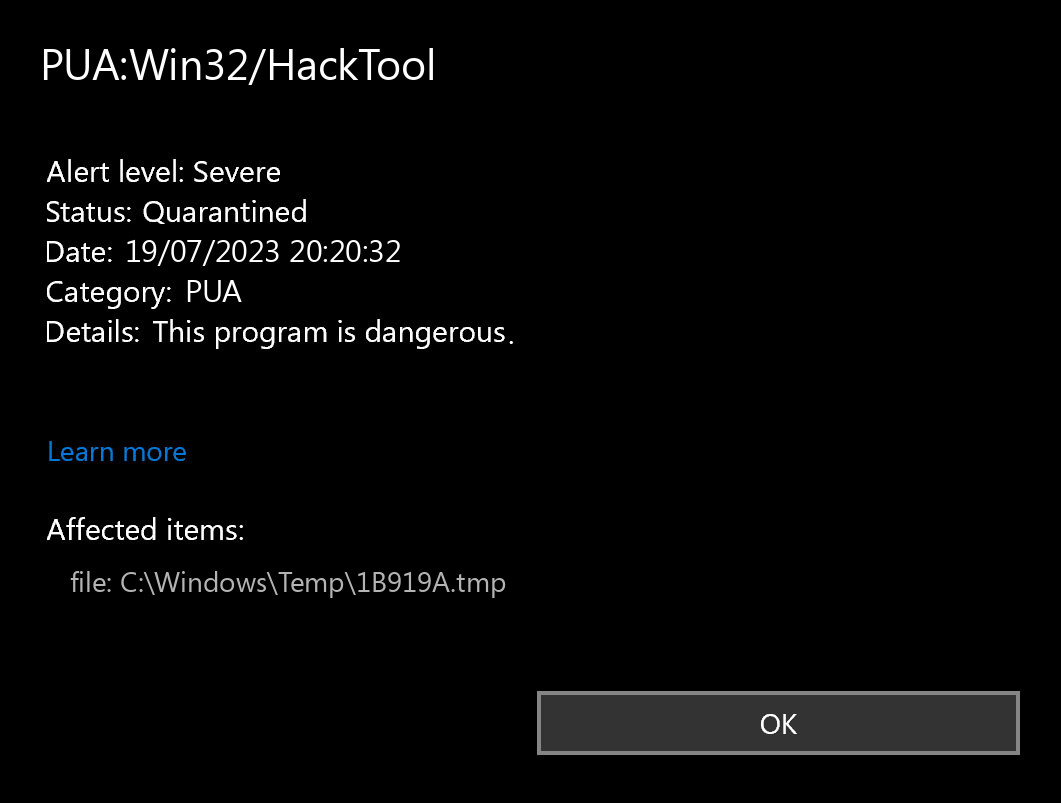
What does the pop-up with PUA:Win32/HackTool detection mean?
The PUA:Win32/HackTool detection you can see in the lower right corner is shown to you by Microsoft Defender. That anti-malware program is good at scanning, but prone to be mainly unstable. It is vulnerable to malware invasions, it has a glitchy interface and bugged malware removal capabilities. Therefore, the pop-up which says concerning the HackTool is simply an alert that Defender has detected it. To remove it, you will likely need to use a separate anti-malware program.
PUA:Win32/HackTool unwanted program is a typical example of PUA, which are quite common nowadays. Being free to use, it may give you “the extended functions” for the additional payment. Some instances of this program type can have no real functions whatsoever – only the shell with the kaleidoscopic interface. You can see it advertised as a system optimization software, driver updater or torrent downloadings tracker. This or another way it does not give you any type of true capability, exposing you to risk instead.
Unwanted Program Summary:
| Name | HackTool PUA |
| Detection | PUA:Win32/HackTool |
| Damage | HackTool is at least useless, or can perform various malicious actions on your PC. |
| Fix Tool | See If Your System Has Been Affected by HackTool exploit |
Is PUA:Win32/HackTool dangerous?
I have actually mentioned that PUA:Win32/HackTool PUA is not as harmless as it pretends to be. The “legitimate and useful” application can abruptly unveil itself as a downloader trojan, spyware, backdoor, or coin miner virus. And you can never foresee what to look for even from different variants of HackTool unwanted program. That still does not imply that you need to panic – possibly, this unpleasant thing has not succeeded to do bad things to your PC.
The particular harm to your system may be caused not just because of the malware injection. A large share of questionable programs, like the HackTool application is, is just poorly developed. Potentially, their actions are fairly effective than pointless if done on certain system setups, however, not on each one. That’s how a basic system optimization program may cause disorder with continuous BSODs on your system. Any interruptions to the system registry are unsafe, and they are a lot more unsafe if done with such programs.
How did I get this virus?
It is difficult to line the sources of malware on your computer. Nowadays, things are mixed, and distribution tactics utilized by adware 5 years ago can be used by spyware these days. But if we abstract from the exact spreading method and will think of why it works, the answer will be pretty simple – low level of cybersecurity awareness. People click on ads on weird sites, click the pop-ups they get in their web browsers, call the “Microsoft tech support” assuming that the weird banner that says about malware is true. It is necessary to recognize what is legitimate – to avoid misunderstandings when attempting to identify a virus.
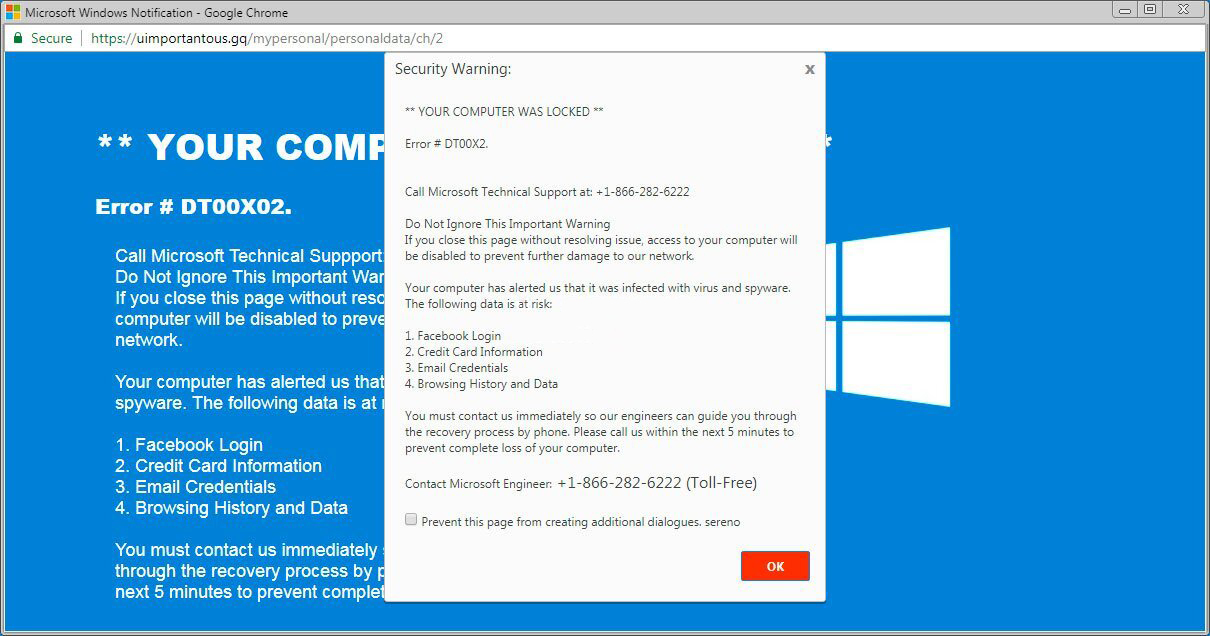
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most common tactics of malware spreading – bait emails and injection into a hacked program. While the first one is not so easy to avoid – you must know a lot to recognize a counterfeit – the second one is simple to address: just do not use cracked applications. Torrent-trackers and other providers of “free” applications (which are, actually, paid, but with a disabled license checking) are really a giveaway point of malware. And PUA:Win32/HackTool is just within them.


Leave a Comment