The Pepecry virus belongs to the ransomware type of malicious agent. A harmful program of such sort encrypts all user’s data on the computer (images, documents, excel sheets, music, videos, etc) and adds its own extension to every file, opening a pop-up window as soon as the encryption is over.
What is Pepecry virus?
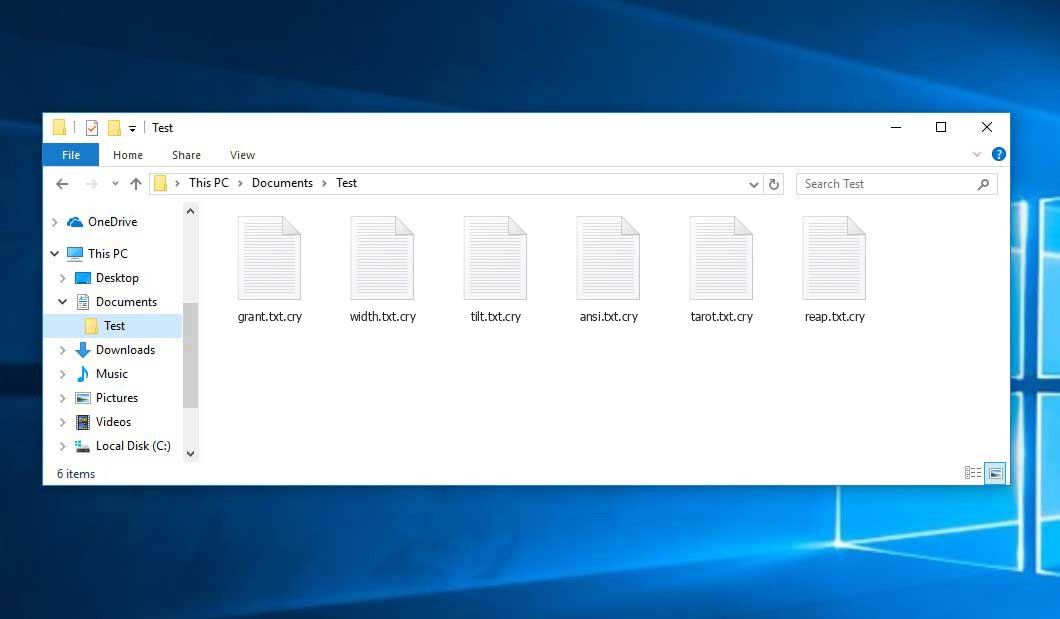
Pepecry will add its specific .cry extension to the title of each encrypted file. For example, an image named “photo.jpg” will be turned into “photo.jpg.cry”. Just like the Excel file with the name “table.xlsx” will become “table.xlsx.cry”, and so on.
In each directory containing the encrypted files, a pop-up window will appear. It is a ransom money note. It contains information about the ways of contacting the racketeers and some other information. The ransom note most probably contains instructions on how to buy the decryption tool from the tamperers. That is how they do it.
Pepecry Overview:
| Name | Pepecry Virus |
| Extension | .cry |
| Ransomware note | pop-up window |
| Ransom | 1 BTC |
| Detection | Trojan:Win32/CryptRan.SA!MTB, Trojan:Script/Phonzy.B!ml, Trojan:MSIL/SnakeKeylogger.SPAQ!MTB |
| Symptoms | Your files (photos, videos, documents) get a .cry extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Pepecry virus |
The pop-up window coming in package with the Pepecry malware provides the following dispiriting information:
PepeCry YOUR FILES HAVE BEEN ENCRYPTED! OPS YOUR FILES HAS BEEN ENCRYPTED BY PEPE SI FINALIZAS EL PROCESO NO PODRAS RECUPERAR TUS ARCHIVOS COMO RECUPERO MIS ARCHIVOS? FACIL METE LA CLAVE DE DESENCRIPTADO AES256 WALLET ADDRESS: 12mdKVNfAhLbRDLtRWQFhQgydgU6bUMjay BITCOIN FEE: 1.0
In the screenshot below, you can see what a directory with files encrypted by the Pepecry looks like. Each filename has the “.cry” extension added to it.
How did Pepecry ransomware end up on my PC?
There are many possible ways of ransomware infiltration.
There are currently three most exploited methods for malefactors to have the Pepecry virus working in your system. These are email spam, Trojan injection and peer file transfer.
- Another thing the hackers might try is a Trojan horse model. A Trojan is a program that gets into your PC disguised as something else. For instance, you download an installer of some program you need or an update for some service. But what is unboxed turns out to be a harmful agent that encodes your data. Since the installation file can have any name and any icon, you have to make sure that you can trust the resource of the stuff you’re downloading. The optimal thing is to trust the software companies’ official websites.
- As for the peer-to-peer networks like BitTorrent or eMule, the danger is that they are even more trust-based than the rest of the Internet. You can never guess what you download until you get it. So you’d better be using trustworthy resources. Also, it is a good idea to scan the directory containing the downloaded objects with the antivirus as soon as the downloading is finished.
How do I get rid of ransomware?
It is crucial to note that besides encrypting your data, the Pepecry virus will most likely deploy Vidar Stealer on your PC to get access to credentials to different accounts (including cryptocurrency wallets). That spyware can extract your logins and passwords from your browser’s auto-filling data.
How to avert ransomware injection?
Pepecry ransomware doesn’t have a endless power, neither does any similar malware.
You can armour your system from its attack within three easy steps:
- Never open any emails from unknown mailers with unknown addresses, or with content that has nothing to do with something you are waiting for (can you win in a lottery without even taking part in it?). If the email subject is more or less something you are expecting, check all elements of the dubious email carefully. A hoax email will surely have a mistake.
- Avoid using cracked or unknown programs. Trojan viruses are often shared as an element of cracked products, most likely as a “patch” preventing the license check. Understandably, untrusted programs are difficult to distinguish from reliable ones, as trojans may also have the functionality you seek. You can try to find information on this program on the anti-malware forums, but the optimal way is not to use such software.
FAQ
🤔 How can I open “.cry” files?Can I somehow access “.cry” files?
There’s no way to do it, unless the files “.cry” files are decrypted.
🤔 The encrypted files are very important to me. How can I decrypt them quickly?
It’s good if you have fаr-sightedly saved copies of these important files elsewhere. If not, there is still a function of System Restore but it needs a Restore Point to be previously saved. The rest of the methods require patience.
🤔 What actions should I take if the Pepecry ransomware has blocked my PC and I can’t get the activation key.
🤔 And what should I do now?
Many of the blocked files might still be at your disposal
- If you sent or received your important files through email, you could still download them from your online mail server.
- You might have shared images or videos with your friends or family members. Just ask them to send those images back to you.
- If you have initially downloaded any of your files from the Web, you can try doing it again.
- Your messengers, social media pages, and cloud storage might have all those files too.
- It might be that you still have the needed files on your old PC, a laptop, phone, flash memory, etc.
USEFUL TIP: You can use data recovery utilities1 to retrieve your lost information since ransomware blocks the copies of your files, deleting the authentic ones. In the tutorial below, you can see how to recover your files with PhotoRec, but remember: you won’t be able to do it before you eradicate the ransomware itself with an anti-malware program.
I need your help to share this article.
It is your turn to help other people. I have written this article to help users like you. You can use the buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithReferences
- Here are Best Data Recovery Software Of 2023.


Leave a Comment