What is Malware.Heuristic.1003?
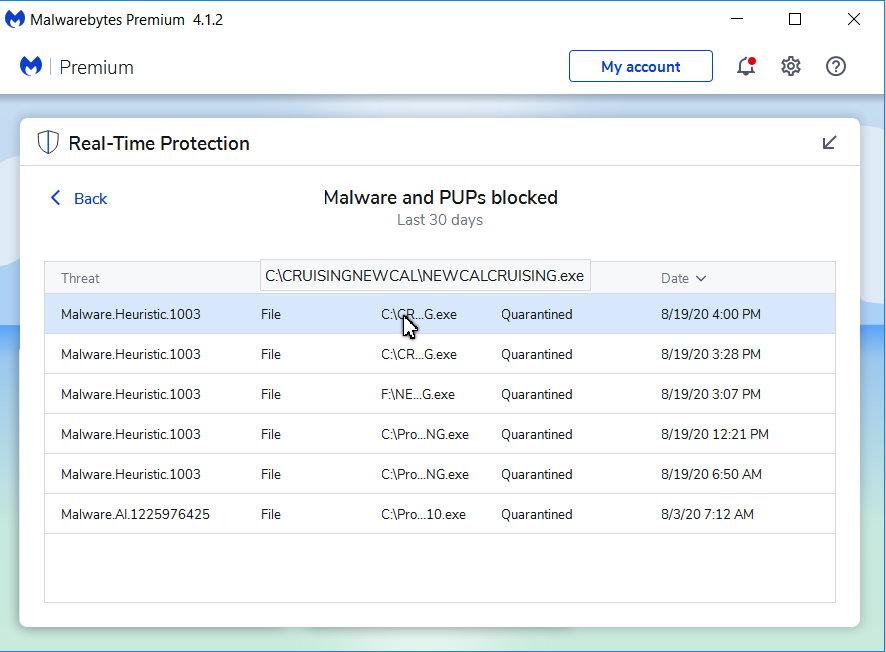
Malware.Heuristic.1003 is a detection present in Malwarebytes Anti-malware engine. It identifies a malicious item detected by a heuristic system. This system makes anti-malware solutions way more potent but is prone to false detections. To clear up whether it is hazardous or not, you should use another anti-malware software. Consider reading the article to see the details.
In the majority of the instances, Malware.Heuristic.1003 infection will advise its targets to initiate funds move for counteracting the modifications that the Trojan infection has actually presented to the victim’s tool.
If Malware.Heuristic.1003 real threat
In cases when this refers to a real threat, the possible damage may be critical. Samples marked as Malware.Heuristic.1003 performs a row of malicious actions, that clearly show it is spyware.
List of malware actions
Similar behaviorRelated domains
| api.ipify.org | Ransom.Phobos!8.10B6C (TFE:5:8mtWss1rAWC) |
Malware.Heuristic.1003
One of the most regular channels where Malware.Heuristic.1003 Virus are injected are:
- By means of phishing e-mails;
- Through cracked software, downloaded from third-party websites;
As soon as the Trojan is effectively injected, it will certainly either cipher the data on the victim’s PC or protect against the tool from functioning correctly – while likewise putting a ransom money note that states the need for the victims to effect the settlement for the objective of decrypting the files or restoring the file system to the first problem. In many circumstances, the ransom money note will turn up when the client restarts the computer after the system has actually currently been harmed.
Malware.Heuristic.1003 spreading ways
Currently, malware opts for pretty much same ways of spreading regardless of the country. Most popular options are email spam and pirated software. The former relies on users’ positive bias towards email messages – they simply don’t expect anything malicious to appear. Pirated a.k.a cracked programs, on the other hand, are illegal from the beginning. Burglars who hack them additionally embed malware in the package, so it is installing together with the crack.
Technical details
File information
Alternative detection names
How to remove Malware.Heuristic.1003 virus?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials, or crypt your documents for ransom.
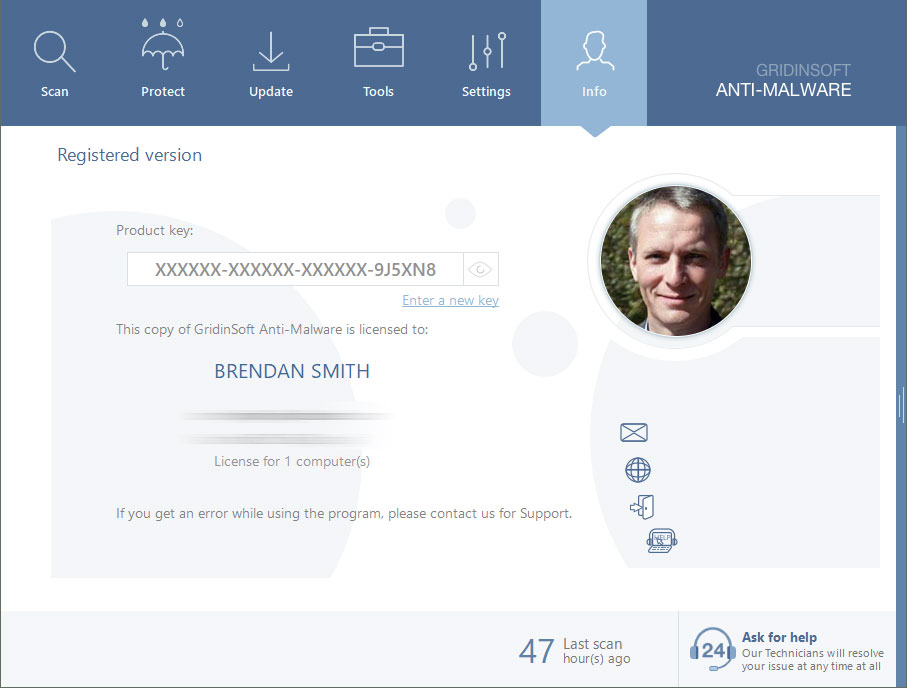
Reasons why I would recommend GridinSoft1
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes.2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When the setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Malware.Heuristic.1003 files and other malicious programs. This process can take 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in the right corner.

Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offers real-time protection for the first 2 days. If you want to be fully protected at all times – I can be recommended you purchase a full version:
Suppose the guide doesn’t help you to remove Malware.Heuristic.1003 you can always ask me in the comments to get help.
User Review
( votes)References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison