Currently, Litar ransomware attacks a wide range of computers in various parts of the world. The degree of its distribution and the severity of the infection definitely requires for you to react immediately before Litar turns all your important data into files that cannot be opened.
Following this tutorial will give you detailed information on the danger associated with Litar, its distribution methods and will provide you with the solution to eliminate it effectively.
Litar – How bad is it?
Litar can be described as a typical ransomware-type threat.
Here is a summary for the Litar virus:
| Ransomware family1 | DJVU/STOP2 ransomware |
| Extension | .litar |
| Ransomware note | _readme.txt |
| Ransom | From $490 to $980 (in Bitcoins) |
| Contact | [email protected], [email protected] |
| Detection3 | MSIL/Kryptik.TYD, Win32/Kryptik.GYYS, Fugrafa.8955 (B) |
| Symptoms | Your files (photos, videos, documents) have a .LITAR extension and you can’t open it |
| Fix Tool | See If Your System Has Been Affected by .kuub file virus |
The infection originates from the Djvu ransomware family. Litar is not much different from other ransomware samples. So it encrypts all popular file types. As soon as the certain file is encrypted users are not able to open it. Litar sets the “.litar” extension into each file it encrypts. For instance, the file “my-photo.jpg”, upon being encrypted by Litar, will be changed into “my-photo.jpg.litar”. Upon the encryption completion, Litar generates a specific text file (for example “_readme.txt”) and puts it into every folder where the encrypted information is stored.
The scary notification produced by Litar warning demanding for the ransom to be paid is literally the same as the alerts presented by other ransomware samples that derive from the Djvu family. It basically indicates that the data is encrypted by it and that the only remedy to decrypt it is to apply a one-of-a-kind decryption key (decryptor). It is quite regretful to admit that this is an absolutely true statement.
The variant of the cryptography method implemented by Litar is yet not duly researched. At the same time, it is definitely true that each user whose data got encrypted may be issued a special decryption key, which is absolutely unique and there are no other variations of it. It is quite unlikely that users will manage to recover the data without the key in place.
Once Litar is active it is impossible for people to get access to the key, which is located on a remote server controlled by the criminals related to Litar ransomware.
In order to obtain the key and restore the necessary data users are forced to actually pay the ransom, which equals to $980. To get the payment information users are told to get in touch with the criminals by means of sending an email or by telegram.
The warning also states that the victims should contact the Litar representatives within 72 hours beginning from the moment of data encryption. The alert indicates that by contacting within 72 hours people will be given a 50% rebate, thus the ransom figure will be decreased to $490). However, no matter what the requested sum is, you should not pay the ransom!

Online crooks cannot be trusted, they totally don’t care what you feel about the trouble with your data, even when you do pay the ransom. For this reason, paying the amount asked by these frauds does not bring you to the positive resolution of your problem. So, you just waste your hard-earned funds for nothing.
I definitely recommend that you do not get in touch with these frauds and do not send money into their pockets. Currently, there are no applications capable of cracking Litar ransomware or restoring the encrypted information at no cost. Hence, the only feasible solution is to restore the lost information from the backup, as long as it is available.
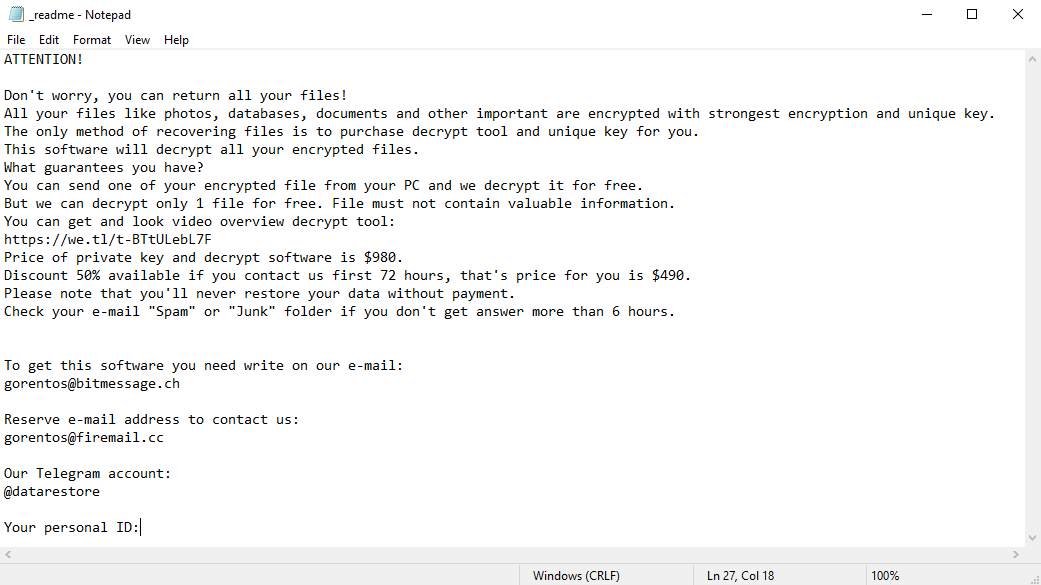
The scary alert demanding from users to pay the ransom to decrypt the compromised data contains these frustrating warnings
You ought to be aware that the online realm currently is full of infections that look pretty much the same as the Litar virus. Hazardous applications classified as ransomware are generally developed to encrypt crucial files and to express the demand before the victim to eventually transfer the ransom amount into the pockets of the frauds standing behind them.
The feature of all such ransomware infections is that they refer to a similar mechanism for generating the standalone decryption key to decrypt the compromised data.
Hence, unless the ransomware is still under development or has some concealed flaws, manually restoring the data is something you can’t really do. The only remedy to avoid the loss of your important files is to permanently make backups of your important data.
Keep in mind that even if you make such backups, they must be immediately put into a special location not associated with your main workstation.
For example, the backup may be stored on the USB flash drive or some other external hard drive device. Alternatively, you may use the service of online (cloud) data storage.
Of course, when you keep your backup data on your regular system, it may be easily encrypted as well as other documents.
Hence, storing the backup on your main computer is definitely not a reasonable decision.
How does Litar attack the PC?
Litar used different methods to inject its roots into the system. It is not really certain what particular method was used to infiltrate your computer.
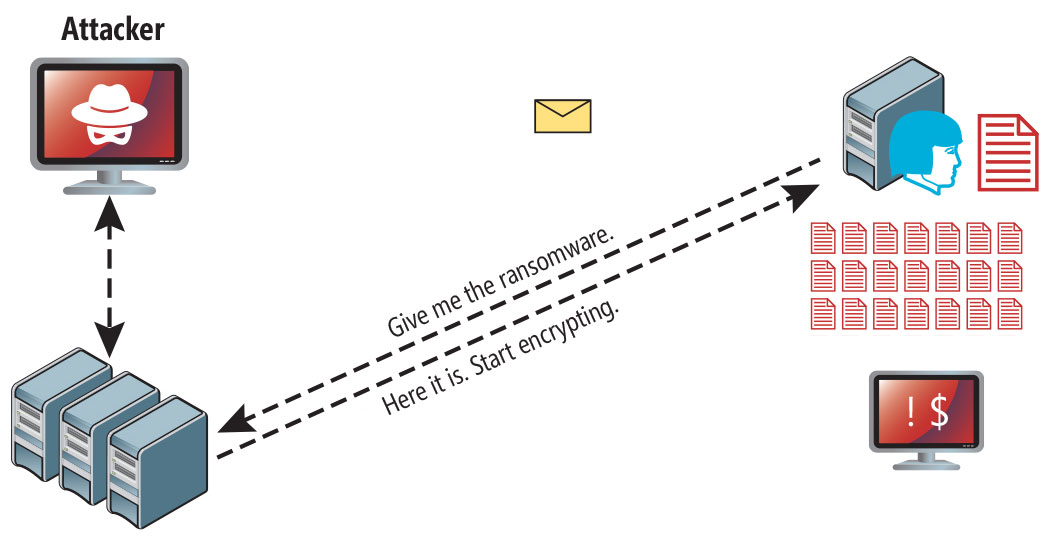
Litar ransomware attack following a successful phishing attempt.
- concealed installation together with other programs, especially the ones promoted on a free basis;
- links to Litar contained in unsolicited spam mail;
- online free hosting services;
- illegal crack downloads from peer-to-peer (P2P) resources.
There were instances when Litar ransomware was introduced as some legit app, for example, in the alerts suggesting to perform some necessary software or browser updates. This is typically how some online crooks aim to convince you into injecting Litar threat manually, through your direct role in the installation procedure.
Of course, the fake update alert will not mention that you are going to install ransomware. This installation will be masked under some claim stating that supposedly you need to update Adobe Flash Player or some other suspicious software.
Needless to mention, the cracked programs are not safe either. It is illegal to download them in the first place, but additionally, they may inject dangerous applications into your system, including Litar ransomware.
So, what can you do to prevent Litar from injecting its malicious roots into your system. In spite of the fact that there is no 100% guarantee to prevent your computer from getting infected. There are some recommendations I want to give you to avoid Litar intrusion. You ought to be careful while installing free applications.
Take time to read what the installers suggest in addition to the main free software. You also need to be careful not to open insecure email attachments. Especially if you are not familiar with the sender. It is very important that your existing anti-virus software is properly updated.
As mentioned, some malicious utilities in the system may perform their dangerous functions in a secret form in your system. I recommend that you scan your system with the proper anti-malware software to identify possible leaks in your system security.
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-BTtULebL7F Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: [email protected] Reserve e-mail address to contact us: [email protected] Our Telegram account: @datarestore Your personal ID: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXThe image below shows files with “.litar” extension appended by the Litar ransomware:
How to remove Litar infection?
In addition to encode a victim’s files, the Litar virus has also started to install the Azorult Spyware on computer to steal account credentials, cryptocurrency wallets, desktop files, and more.
Reasons why I would recommend GridinSoft
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes. Here is my short review about it:

Gridinsoft Anti-Malware Review 2025 – Is It Worth It?
In today’s digital landscape where malware evolves at breakneck speed, finding reliable protection has never been more crucial. After spending weeks testing Gridinsoft Anti-Malware, I’ve discovered a security tool that strikes an impressive balance between effectiveness and resource efficiency. While many security solutions bloat their offerings with countless features, Gridinsoft takes a refreshingly different approach. […]
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:Run the setup file.
When setup file has finished downloading, double-click on the install-antimalware-fix.exe file to install GridinSoft Anti-Malware on your computer. An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.
An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.
Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your computer for Litar infections and other malicious programs. This process can take a 20-30 minutes, so we suggest you periodically check on the status of the scan process.
Click on “Clean Now”.
When the scan has completed, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.
How to decrypt .Litar files?
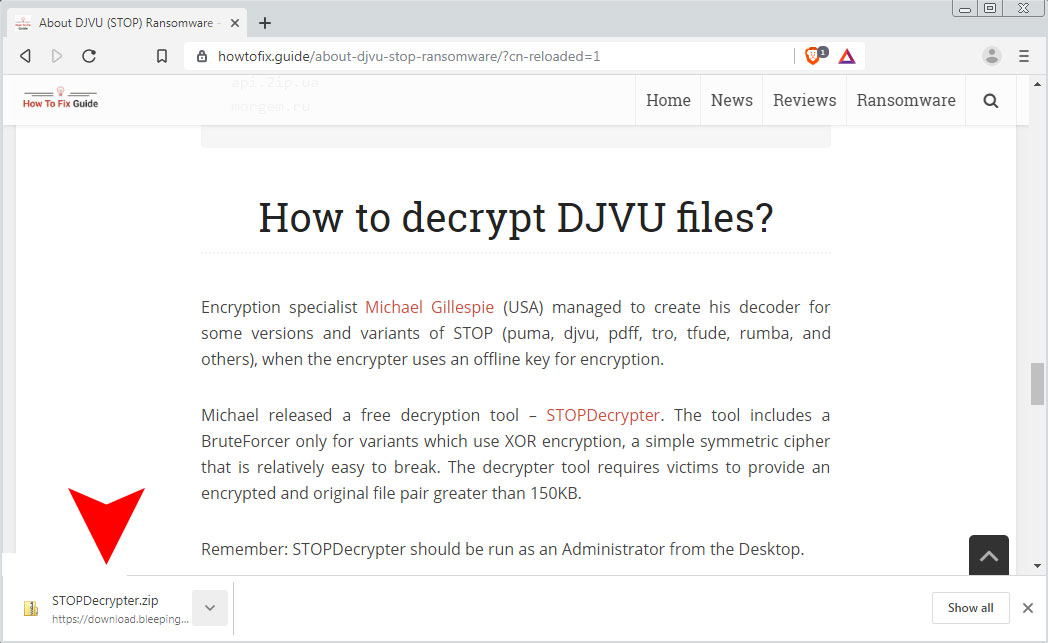
Encryption specialist Michael Gillespie (USA) managed to create his decoder for some versions and variants of this family ransomware (djvu, rumba, nusar, and others).
It work when the litar virus used an offline key for encryption.
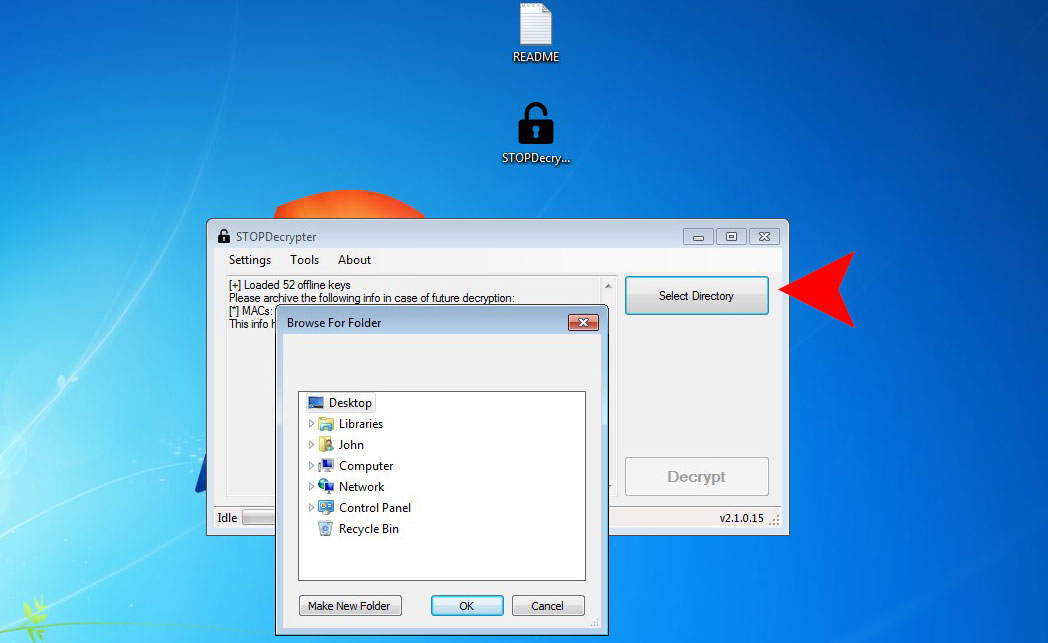
You can download free decryption tool here: STOPDecrypter. This tool includes a BruteForcer only for variants which use XOR encryption, a simple symmetric cipher that is relatively easy to break. The decrypter tool requires victims to provide an encrypted and original file pair greater than 150KB.
Download STOPDecrypter tool:
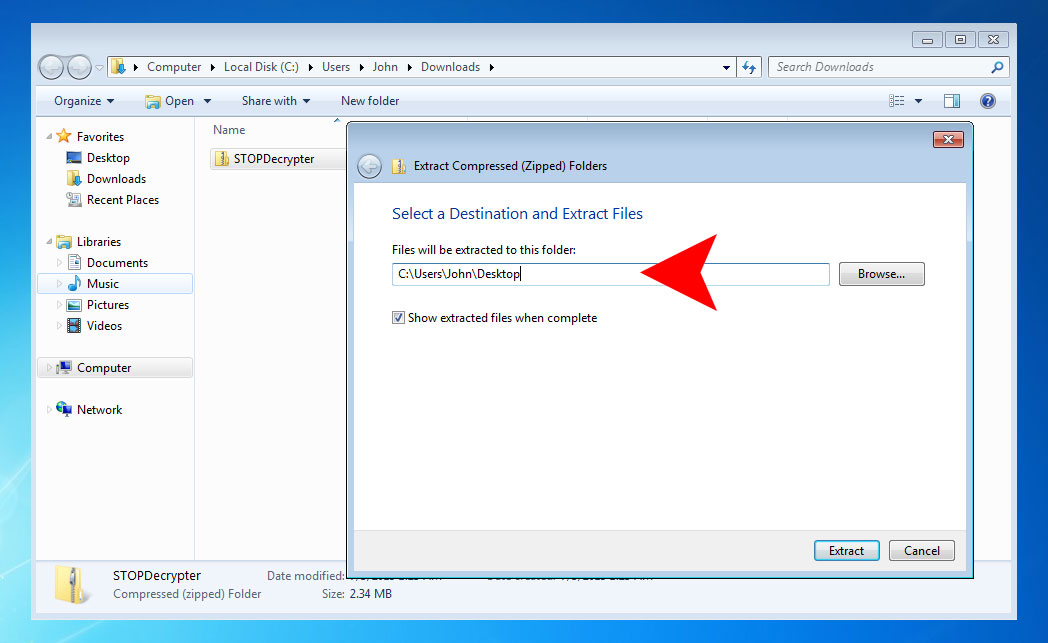
Extract STOPDecrypter tool to your Desktop folder:
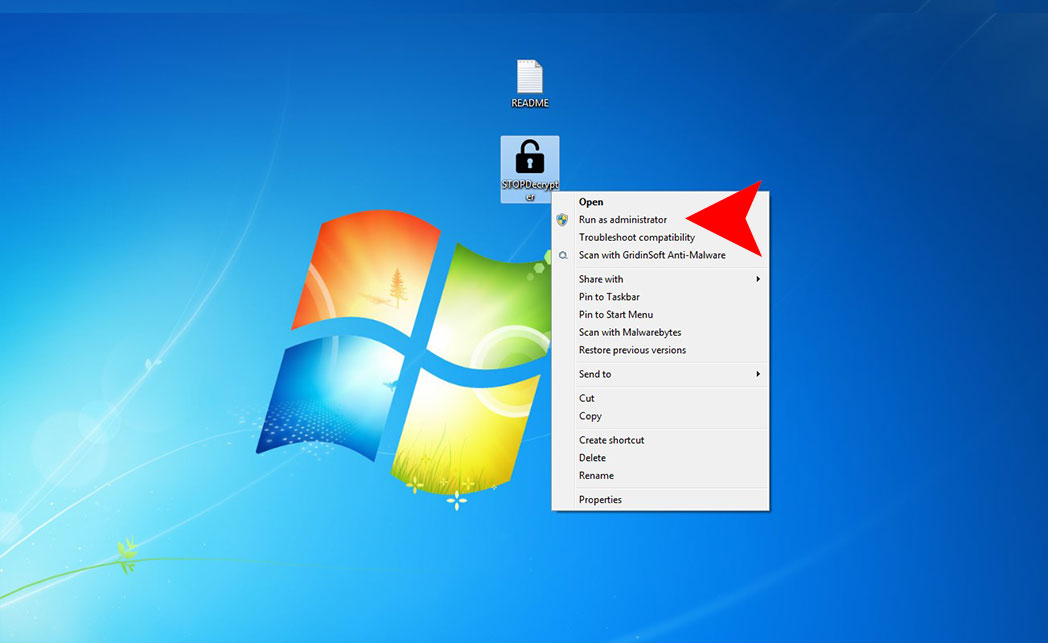
Run STOPDecrypter tool:
Remember: STOPDecrypter should be run as an Administrator from the Desktop.



is this work for real?
Hello mish,
Yes, for offline key it’s worked.
You will be able to recover files by the offline key when the private key for this variant will recovered.
I will write about the update here: https://howtofix.guide/how-to-decrypt-djvu-ransomware-files/