Legion Loader is a new trojan dropper that is already in large usage. It is unique by the wide variety of malware it has been attended drop, and also its proceeding advancement. The implication is that it is readily available for hire as part of the expanding malware-as-a-service black market.
While various other droppers typically become associated with certain malware – equally as Emotet is recognized to drop Trickbot, and also Trickbot is recognized to drop Ryuk and also Lockergoga ransomware (and extra recently web skimming malware) – Legion is already recognized to go down a wide variety of malware. This includes infostealers such as Vidar, Predator and Raccoon; and also a crypto stealer, a crypto miner and an RDP backdoor.
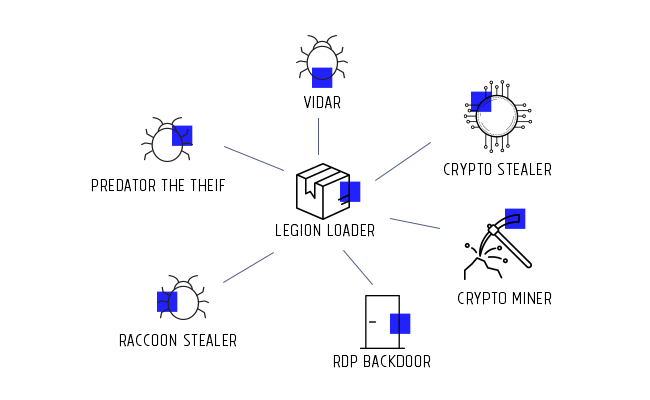
(Image Credit: Deep Instinct)
A Legion project has been discovered, and also the dropper utilized has actually been evaluated by scientists at Deep Instinct. The evaluation was ‘relatively uncomplicated’: although it includes a number of sandbox and study tool evasions, it lacks string obfuscation.
It is, they claim, “written in MS Visual C++ 8 (very likely by a Russian-speaking person) and reveals indications of remaining in energetic advancement.” They do not provide any kind of indication of just how Legion is originally installed on the victim, however rather describe what it does. The targets presently appear to be greatly in the U.S. and Europe. Every dropper is created to supply 2-3 additional malwares, and includes a built-in fileless crypto money stealer and also browser credential farmer.
It gets here with typical black hat black humor – identified user representative strings have consisted of autizm, satan, suspiria, fuck u, as well as lilith. Its primary step is to check in with its marked web server. If the predicted reply is not gotten, it terminates. If successful, it downloads the 2 or 3 added hauls usually from the C&C server, yet periodically from a complimentary organizing solution.
When the downloads are complete, Legion implements a lightly obfuscated PowerShell command that provides the crypto currency thief as well as a web browser credential harvester. The crypto thief contacts the C&C and also gets further PowerShell code that sweeps the system for stored wallets and also any kind of related credentials.
If any are discovered, Legion once more get in touches with the C&C, as well as gets a lot more PowerShell code (to set up the stealer) and also a DLL (utilized in additional communication security). When this is complete, it downloads an internet browser credential farmer. Credentials and also purse files are uploaded to the C&C.
It might also release an RDP-based backdoor. This gets here as a Nullsoft Scriptable Install System (NSIS), and uses an ingrained blowfish.DLL to decrypt strings which form a cmd.exe command. This carries out an embedded PowerShell script, which contains a big DES encrypted blob which is decrypted. This ball has various other balls that are gzip-compressed and also base64 inscribed.
“These blobs,” note the researchers, “are decoded and also unwinded making use of a collection of contained functions as well as are deployed by the PowerShell code to %programfiles%/windowsmail/appcache.xml or default_list.xml, based on the carrying out machine’s os. While the written file’s expansion is .xml they are actually .DLL files. After the required.DLL having ball has been released, it is signed up as a system service.”
It is prematurely to understand exactly how commonly Legion will be adopted by the criminal society in the future, however the range of malware it has actually been attended drop recommends that it has not been established by a criminal gang to supply a particular malware, however is designed to use a service to supply malware of choice. Among the infostealers it has provided – Raccoon – is itself an increasingly preferred product supplied as a service. This kind of criminal activity, where even more skilled programmers provide malware for the bigger variety of would-be cyberpunks is likely to grow.
Deep Instinct supplies a long list of IoCs comprising Legion Loader examples, went down malware samples, and Legion Loader as well as crypto stealer C&C domains.
How to remove viruses from your PC?
Malware has often come with other viruses and spyware.
Reasons why I would recommend GridinSoft1
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes.2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When setup file has finished downloading, double-click on the install-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Generic PUA GC files and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.

Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison


Leave a Comment