The Koxic virus was originally discovered by virus analyst Tomas Meskauskas, and belongs to the ransomware type infection. This ransomware encrypts all user’s data on the PC (photos, documents, excel tables, music, videos, etc), adds its specific extension to every file.
Koxic Virus
☝️ Koxic can be correctly identify as a ransomware-type infection.
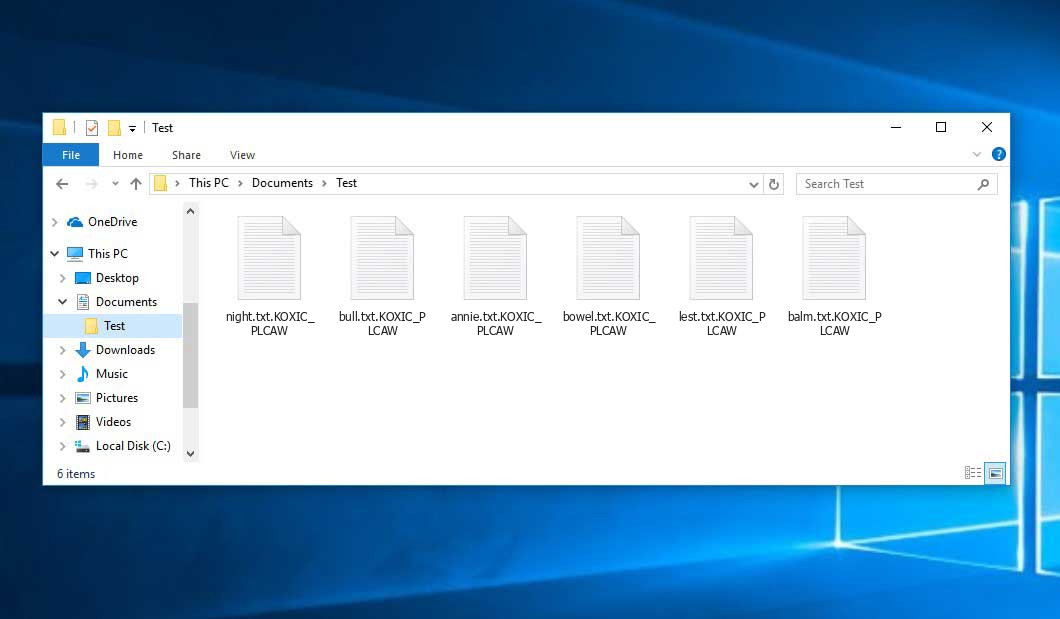
After the encryption process files will be renamed according to the pattern KOXIC, which is laid in ransomware. Your photo, named an example “me.jpg” will be altered to “me.jpg.KOXIC_PLCAW” after the encryption.
Inside of the ransom note, there is usually an instruction saying about purchasing the decryption tool. This decryption tool is created by ransomware developers, and can be obtained through the email, contacting [email protected], [email protected].
Here is a summary for the Koxic:
| Name | Koxic Virus |
| Extension | .KOXIC |
| Contact | [email protected], [email protected] |
| Detection | MSIL/Autorun.Spy.Agent.DE, Mal/Cerber-Y, MSIL/Runner.E |
| Symptoms | Your files (photos, videos, documents) have a .KOXIC extension and you can’t open it. |
| Fix Tool | See If Your System Has Been Affected by Koxic virus |
The information by the Koxic ransomware states the following frustrating information:
Hello, all your important files are encrypted and sensitive data leaked. To decrypt your files and avoid other unpleasant things you need to buy special decryption tool. Contact us via [email protected] or [email protected] and tell your UserID. This is the only way to decrypt your files and avoid publi? disclosure of data . Do not try to use third party software (it may corrupt your files). We respect black market rules. We can confirm the ability to decrypt your files (and of course the evidence of the leak ), Send us several unimportant files (do not try to deceive us). Your UserID (send it to us for decryption):
The image below gives a clear vision of how the files with “.KOXIC” extension look like:
How did I get Koxic ransomware on my computer?
That was a huge number of different ways of ransomware injection.
However, nowadays there are only two ways of Koxic injection – email spam and trojans. You may see a lot of messages on your email, stating that you need to pay different bills or to get your parcel from the local FedEx department. But all such messages are sent from unknown email addresses, not from familiar official emails of these companies. All such letters contain the attached file, which is used as a ransomware carrier. If you open this file – your system will get infected by Koxic.
In case of trojans presence, you will be offered to download and install ransomware on your PC under the guise of something legit, like a Chrome update, or update for the software you are storing on your computer. Sometimes, trojan viruses can be masked as legit programs, and ransomware will be offered for download as an important update, or a big pack of extensions which are essential for proper program functioning.
There is also the third way of ransomware injection, however, it becomes less and less popular day-to-day. I am talking about peering networks, such as torrents or eMule. No one can control which files are packed in the seeding, so you can discover a huge pack of different malware after downloading. If circumstances force you to download something from peering networks – scan every downloaded folder or archive with antivirus software.
How to remove Koxic virus?
In addition to encode a victim’s files, the Koxic infection has also started to install the Azorult Spyware on system to steal account credentials, cryptocurrency wallets, desktop files, and more.
To ensure the user that ransomware distributors really have the decryption tool, they may offer to decrypt several encrypted files. And they are the single owners of this decryption program: Koxic ransomware is a completely new type, so there is no legit program from anti-malware vendors, which can decrypt your files. But such a situation is in momentum: decryption tools are updating every month.
However, paying the ransom is a bad decision, too. There is no guarantee that Koxic ransomware developers will send you the decryption tool and a proper decryption key. And there are a lot of cases when ransomware distributors deceived their victims, sending the wrong key or even nothing. In the majority of cases, there is a way to recover your files for free. Search for available backups, and restore your system using it. Of course, there is a chance that the backup you found is too old, and does not contain a lot of files you need. But, at least you will be sure that there is no malware in your system. However, to ensure that there are no malicious programs in your system after the backup, you need to scan your PC with anti-malware software.
Koxic ransomware is not unique. There are more ransomware of this type: Spydr, Crm, Terkunci. These examples of ransomware act in a similar way: encrypting your files, adding a specific extension, and leaving a great number of ransom money notes in every folder. But there are two things which make difference between these ransomware – cryptography algorithm, which is used for file encryption, and ransom amount . In some cases, victims are able to decrypt their files without any payments, just using free solutions produced by several anti-malware vendors, or even with the decryption tool which is offered by ransomware creators. The last scenario is possible when ransomware distributors have typed your decryption key inside of a ransom money note. However, as you can already guess, such luck is a very rare thing. Ransomware is created for money gaining, not for jokes or scaring.
Reasons why I would recommend GridinSoft1
There is no better way to recognize, remove and prevent ransomware than to use an anti-malware software from GridinSoft2.
Download Removal Tool.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your computer for Koxic infections and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has completed, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.

Frequently Asked Questions
No way. These files are encrypted by Koxic ransomware. The contents of .KOXIC files are not available until they are decrypted.
If your data remained in the .KOXIC files are very valuable, then most likely you made a backup copy.
If not, then you can try to restore them through the system function – Restore Point. All other methods will require patience.
Of course not. Your encrypted files do not pose a threat to the computer. What happened has already happened.
You need GridinSoft Anti-Malware to remove active system infections. The virus that encrypted your files is most likely still active and periodically runs a test for the ability to encrypt even more files. Also, these viruses install keyloggers and backdoors for further malicious actions (for example, theft of passwords, credit cards) often.
In this situation, you need to prepare the memory stick with a pre-installed Trojan Killer.
You can try to find a copy of an original file that was encrypted:
- Files you downloaded from the Internet that were encrypted and you can download again to get the original.
- Pictures that you shared with family and friends that they can just send back to you.
- Photos that you uploaded on social media or cloud services like Carbonite, OneDrive, iDrive, Google Drive, etc)
- Attachments in emails you sent or received and saved.
- Files on an older computer, flash drive, external drive, camera memory card, or iPhone where you transferred data to the infected computer.
Also, you can contact the following government fraud and scam sites to report this attack:
- In the United States: On Guard Online;
- In Canada: Canadian Anti-Fraud Centre;
- In the United Kingdom: Action Fraud;
- In Australia: SCAMwatch;
- In New Zealand: Consumer Affairs Scams;
- In France: Agence nationale de la sécurité des systèmes d’information;
- In Germany: Bundesamt für Sicherheit in der Informationstechnik;
- In Ireland: An Garda Síochána;
To report the attack, you can contact local executive boards. For instance, if you live in USA, you can have a talk with FBI Local field office, IC3 or Secret Service.
How сan I avoid ransomware attack?
Koxic ransomware doesn’t have a superpower.
You can easily protect yourself from its injection in several easy steps :
- Ignore all emails from unknown mailboxes with a strange unknown address, or with content that has likely no connection to something you are waiting for (can you win in a lottery without taking part in it?). If the email subject is likely something you are waiting for, check carefully all elements of the suspicious letter. A fake email will surely contain a mistake.
- Do not use cracked or untrusted programs. Trojans are often distributed as a part of cracked software, possibly under the guise of “patch” which prevents the license check. But untrusted programs are very hard to distinguish from trustworthy software, because trojans may also have the functionality you need. You can try to find information about this program on the anti-malware forums, but the best solution is not to use such programs.
- And to be sure about the safety of the files you downloaded, use GridinSoft Anti-Malware. This program will surely be a perfect shield for your personal computer.
I need your help to share this article.
It is your turn to help other people. I have written this article to help people like you. You can use the buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithHow to Remove KOXIC Ransomware & Recover PC

Name: KOXIC Virus
Description: KOXIC Virus is a ransomware-type infections. This virus encrypts important personal files (video, photos, documents). The encrypted files can be tracked by a specific .KOXIC extension. So, you can't use them at all.
Operating System: Windows
Application Category: Virus
User Review
( votes)References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison