The Cts1 virus gets into a computer system, it targets various types of files, like documents, videos, photos, and more. It modifies the file structure and adds the “.cts1” extension to each encrypted file, making them unusable without the decryption key.
Cts1 Virus Overview
The Cts1 virus is a malicious program that encrypts your files and coerces you into paying for their decryption. This malware ciphers different file types. Encrypted files become identifiable by a distinct “.cts1” extension. The files touched by ransomware become inaccessible and unusable.
Subsequently, the ransomware demands a ransom payment in Bitcoin from its victims, ranging from $490 to $980. Usually, a ransom text file is named as “_readme.txt“.
Cts1 Ransomware operates by Salsa20 encryption algorithms to scramble the contents of the targeted files. Since Cts1 virus utilizes such a strong encryption method, it becomes pretty hard, if not impossible, to pick the decryption key without cooperating with the attackers.
Once Cts1 malware finishes the encryption, it shows a ransom note to the user, asking for a ransom payment for the decryption key. The ransom note provides instructions on how to pay off the bill and often contains threats of system wipeout or increased ransom amounts if the ransom is not paid within a specified timeframe.
I have created an all-encompassing list of potential solutions, advice, and practices to remove the Cts1 virus and recover your files. In some cases, you can decrypt the files, but sometimes, it may be impossible.
The Cts1 virus bears resemblance to other ransomware variants like Jaqw, Jasa, Jaoy, and Taqw. This virus encrypts a wide range of common file types and appends its distinct “.cts1” extension to all files. For instance, a file named “1.jpg” would be altered to “1.jpg.cts1” and “2.png” to “2.png.cts1“.
After successful encryption, the virus spawns a special text file named “_readme.txt” and places it in every folder containing the encrypted files. It as well adds this file to the desktop, so the victim will not miss the attack even without opening folders.
The image below provides a visual representation of files with the “cts1” extension:
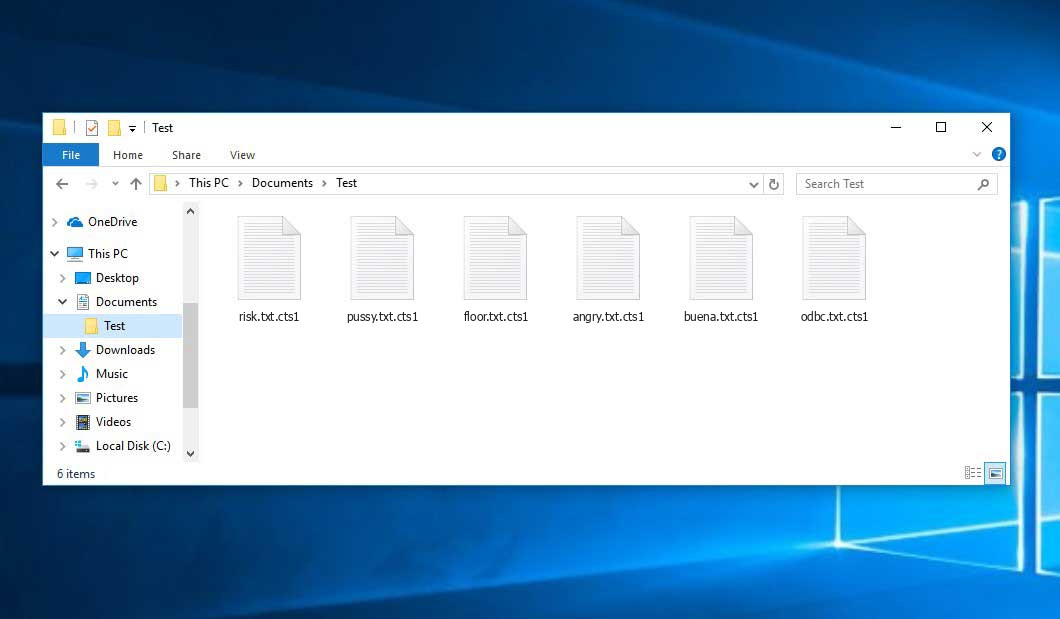
Encrypted Files by Ransomware
| Name | Cts1 Virus |
| Extension | .cts1 |
| Ransomware note | _readme.txt |
| Detection | Trojan:MSIL/AgentTesla.HU!MTB, Win32/Injector.ANIA, MSIL/Filecoder.ATX |
| Symptoms |
|
| Fix Tool |
To remove possible malware infections, scan your PC:
6-day free trial available. |
Cts1 ransomware arrives as a set of tasks that are meant to execute different tasks on a victim’s computer. One of the first processes being launched is winupdate.exe, a deceptive process that displays a fake Windows update alert during the attack. This is meant to convince the victim that their PC has become slow because of a Windows update.
The encryption algorithm is AES-256. So, if your data got encrypted with an online decryption key, the possibility to get your files back without paying the ransom are quite low. Thing is, this key is unique for each victim, and brute forcing it will take exceptionally big amount of time.
Do not pay the ransom!
Please, try to use the available backups, or Decrypter tool
_readme.txt file also states that the system owners must get in touch with the hackers during 72 hours since the file encryption. On the condition of getting in touch within 72 hours, hackers grant a 50% off. This decreases the ransom sum down to $490.
Yet, stay away from paying the ransom! I highly recommend that you do not contact these scammers and do not pay. One of the most real working solution to recover the lost data is just using the backups you have, or using Decrypter tool from Emsisoft.
The peculiarity of such malware is the employment a similar set of actions for decryption key generation. Thus, unless the ransomware is still under the stage of development or has some hard-to-track encryption, manual data recovery is a thing you can’t perform. The exclusive resolution to prevent the data loss is to regularly make backups of your crucial files.
Note that even if you do create such backups regularly, they ought to be located into a specific location without loitering, not being connected to your main workstation. For instance, the backup may be kept on the USB flash drive or some optional external hard drive storage. Optionally, you may refer to the help of online (cloud) information storage.
Needless to say, when you store your backup data on your regular device, it may be encrypted together with your files. For this reason, placing the backup on your computer’s disk is surely not a wise idea.
How I was infected?
Ransomware has a various methods to built into your system. But it doesn’t really matter what way had place in your case.
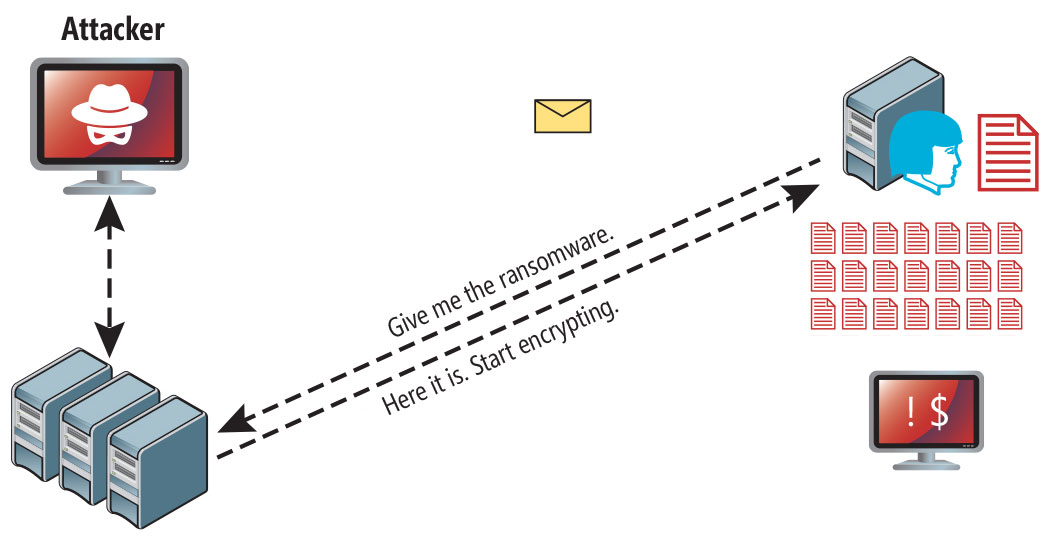
Ransomware attack following a successful phishing attempt.
- Concealing the virus within seemingly legitimate apps, especially utilities provided as freeware or shareware.
- Spreading the virus through spam emails containing suspicious links that lead to the virus installer.
- Exploiting online free hosting resources to host and distribute the virus files discreetly.
- Obtaining pirated software from illegal peer-to-peer (P2P) resources, which may unknowingly contain malware.
There were cases when the Cts1 virus was disguised as some legitimate thing, for example, the messages insisting to install a browser update or a vastly needed codec for online media playback. This is commonly the way how some online scams aim to force you into installing the ransomware manually, by actually making you directly involve in this process.
Surely, the bogus update alert will not tell that you are going to actually install the virus. This process will be disguised under some alert stating that you should install an urgent security update or some questionable program whatsoever.
Of course, the software cracks represent the damage as well. Using P2P is illegal and may result in the injection of serious malware, including the Cts1 ransomware.
To sum up, what can you do to avoid the penetration of the ransomware into your system? Even though there is no 100% assurance to prevent your PC from getting compromised, there are some tips I want to give you to avert the Cts1 penetration. You must be careful while setting up free software today.
Verify you always read what the installation window offers aside from the main free program. Keep away from opening questionable email attachments. Do not open files from the unknown recipients. Naturally, your current anti-malware program must always be updated.
The malware does not states openly about itself. It will not appear in the list of your available programs. However, it will be masked under some malicious process running regularly in the background, starting from the moment when you launch your computer.
How To Remove Ransomware?
Video Guide
Recovering your files with PhotoRec
PhotoRec is an open-source program, which is originally created for file retrieval from damaged disks, or for data recovery in case if they are unintentionally deleted. However, as time has gone by, this program received the ability to recover the files of 400 different extensions. Hence, it can be used for file restoration after the Cts1 attack.
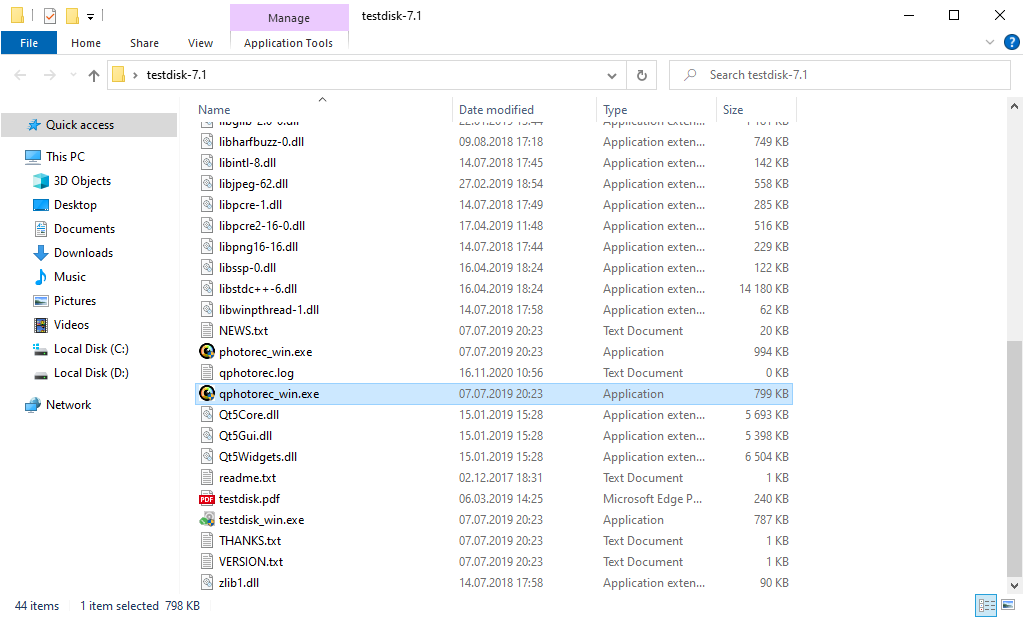
First, you need to download this app. It is 100% free, but the developer notifies that there is no warranty that your files will be retrieved. PhotoRec is spread in a pack with another program of the same developer – TestDisk. The resulting archive will bear TestDisk name, but don’t worry. PhotoRec files are right inside.
To open PhotoRec, you need to find and open “qphotorec_win.exe” file. No setup is needed – the program has all the files it need inside of the archive, hence, you can mount it on your USB drive, and help your friends/parents/anyone who has been attacked by Cts1 ransomware.
Upon the launch, you will witness the screen showing you the full list of your disks. However, this information is likely unhelpful, because the required menu is placed a bit higher. Click this bar, then choose the disk which was attacked by ransomware.
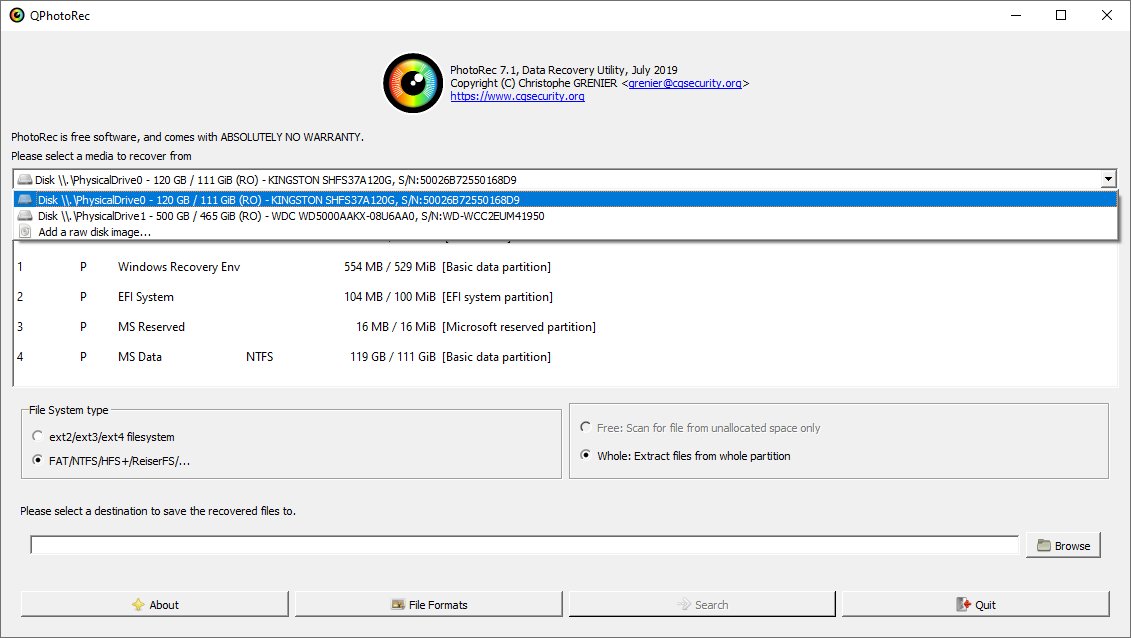
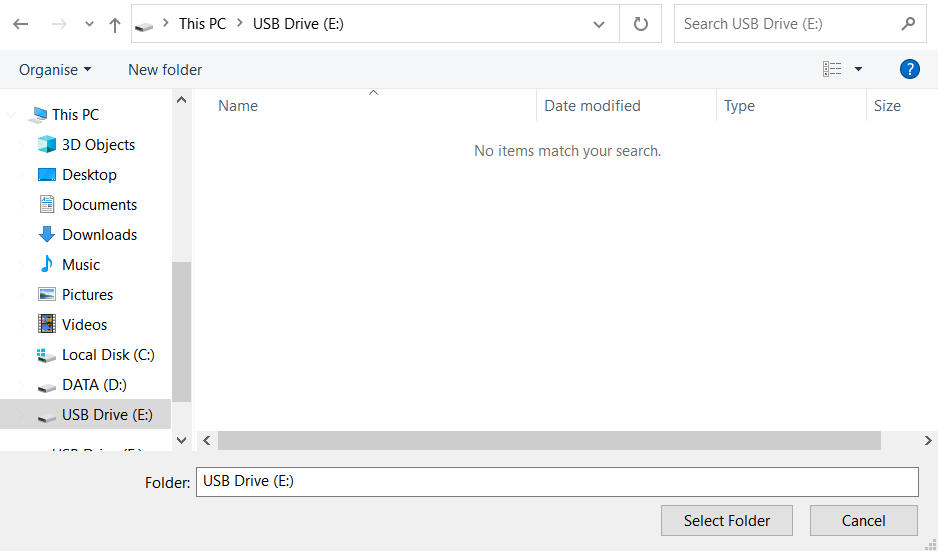
After opting for the disk, you need to choose the destination folder for the restored files. This menu is located at the lower part of the PhotoRec window. The best decision is to export them on USB drive or any other type of removable disk.
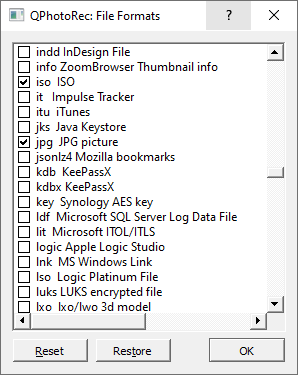
Then, you need to designate the file formats. This choice is located at the bottom, too. As it was mentioned, PhotoRec can retrieve the files of about 400 different formats.
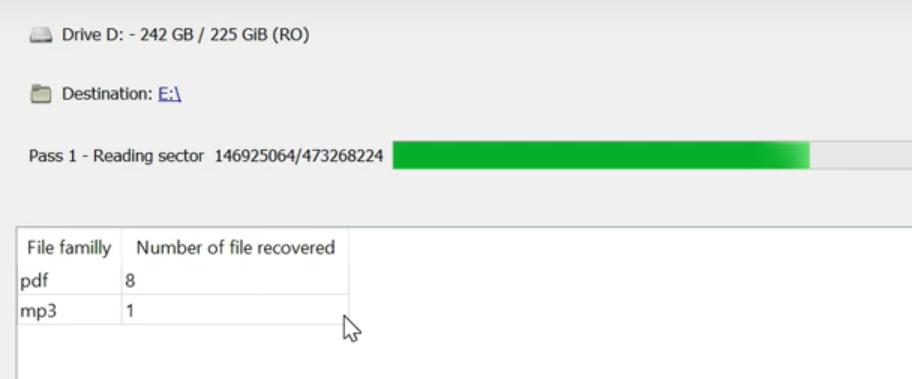
Finally, you can start files retrieval by pressing the “Search” button. You will observe the screen where the findings of the scan and recovery are shown.
Cts1 files recovery Video Guide.
Frequently Asked Questions
I need your help to share this article.
It is your turn to help other people. I have written this guide to help people like you. You can use buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan Smith
![]() German
German ![]() Japanese
Japanese ![]() Spanish
Spanish ![]() Portuguese (Brazil)
Portuguese (Brazil) ![]() French
French ![]() Turkish
Turkish ![]() Chinese (Traditional)
Chinese (Traditional) ![]() Korean
Korean ![]() Indonesian
Indonesian ![]() Hindi
Hindi ![]() Italian
Italian


Leave a Comment