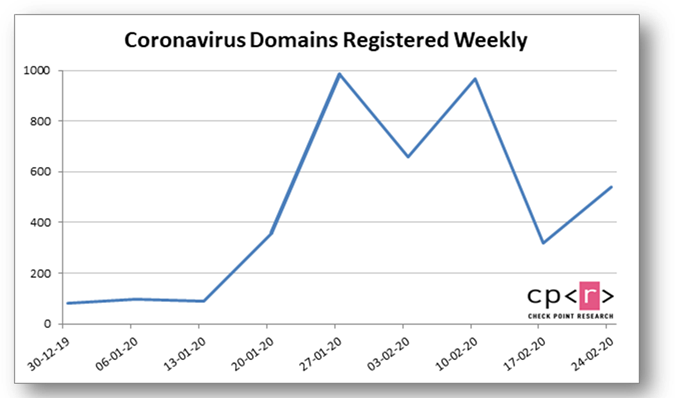
Check Point experts revealed that coronavirus has become a tool for hacker attacks on users and businesses. Currently registered more than 4000 domains, associated with COVID-19, and some of them are used by cybercriminals.
According to experts, since January 2020, more than 4,000 domains linked with coronavirus, have been registered in the world. 3% of these websites are already recognized as malicious, and another 5% are suspicious.According to experts, such sites are often just one element of an attack. Attackers send spam with links to a malicious website on behalf of trusted organizations in order to induce a potential victim to follow the link.
In the case of COVID-19, it may be recommendations from health organizations or data on the spread of the virus that may be interesting to the recipient. At the moment of clicking on the link on the user’s device, the malware is automatically installed”, – say the experts.
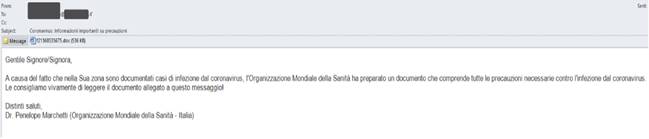
Check Point discovered a phishing attack allegedly on behalf of the World Health Organization, which spreads in Italy. Experts noted that 10% of organizations in Italy were subjected to this attack. Here is an example of a spam email that cybercriminals sent:
“In connection with the growth of recorded cases of coronavirus in your region, the World Health Organization has prepared a document that includes all the necessary precautions against coronavirus.
We strongly recommend that you familiarize yourself with the document attached to this letter.
Best wishes,
Dr. Penelope Marchetti
World Health Organization, Italy»
Another example is the vaccinecovid-19 [.] Com site, which was registered in Russia in February 2020. Attackers offer to buy on it “the best and fastest test for detecting coronavirus at a fantastic price – 238 Euro”.
In addition, a major spam campaign was recorded in Japan. There cybercriminals send spam on behalf of the Japanese organizations to help people with disabilities. Emails report the spread of coronavirus in several cities in Japan, prompting the recipient to open the document. If the user becomes interested and opens the attachment, the Emotet Trojan is downloaded on its computer.
Attackers use every opportunity to conduct a successful attack. Since the human factor is the most vulnerable security place, social engineering techniques are of particular interest to hackers, said a representative of Check Point Software Technologies. – Hackers often use the agenda to send phishing emails, and use both negative and positive events to attract users. For example, in November, a few weeks before Black Friday, we observed a significant increase in fake domains that mimic official online stores.”
As the spread of coronavirus continues, attackers will continue to exploit the coronavirus theme to launch attacks on users and businesses. Cybersecurity experts recommend resisting the first impulse, if you receive such message, and not to open attachments and not to follow links in suspicious letters. You should pay attention to spelling errors contained in messages or on sites – this is one of the signs of potential suspicious activity.


Leave a Comment