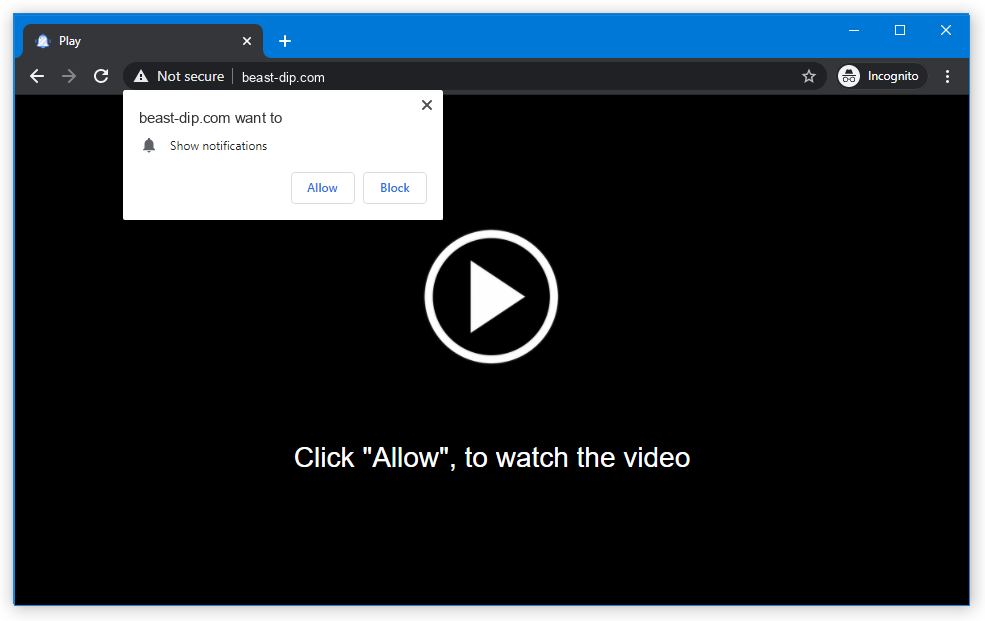
Beast-dip pop-up alerts can show up unexpectedly, covering the subject of the website you checked or opening your browser when you do not desire it to be opened.
Clicking on the Beast-dip advertisement can lead to the injection of various malware or unwanted programs. In this guide, you will see the tutorial of Beast-dip popups clearing in various manners, and also inspecting your PC for other viruses existence.
What are Beast-dip pop-ups?
Beast-dip popups are an outcome of adware activity. Adware is a type of malware that suggests you the pay-per-view of pay-per-click advertisements, which creates a significant volume of profit for adware distributors. These promotions might consist of sometimes shocking information, or have a web link to malevolent content/website, since adware maintainers have no purpose to check the goodness of the content they are going to reveal – their single target is money.
Pop-up promotions itself is a good, low-priced and very successful marketing instrument1. It permits the vendor to link the customers’ attention to their site, as well as the buyers to get the dynamic updates on the goods they wish to purchase. When the customer will receive a pop-up notification that the TV set he likes to purchase is available at the online store he/she saw previously with a 15% discount, one will certainly use this opportunity and get it. Taking into consideration the very small cost for the popups and their targeting, such an advertising and marketing tool is a much-loved thing amongst the advertising teams of huge internet retail stores.
Nonetheless, such a profitable plan could not be missed by malware developers. Option to show the popup ads by force to the people of malware invasion is a great basis for evil-minded adjustments with the popup ads. And Beast-dip.com advertisements is among hundreds that are “employed” in this scheme.
Here is a info for the Beast-dip site
| Site | Beast-dip.com |
| Hosting | AS13335 Cloudflare, Inc. United States, San Francisco |
| Infection Type | Adware, Push notifications, Unwanted Ads, Pop-up Ads |
| IP Address | 104.21.73.224 |
| Symptoms | Annoying pop-up ads in the right corner. |
| Similar behavior | Kopet, News, Bestcldantrack |
| Fix Tool |
To remove possible virus infections, try to scan your PC
|
How have I got the Beast-dip virus?
There are a lot of ways of getting contaminated by the adware that cause the Beast-dip popups storm. A lion’s part of this computer virus incidents is after the free software or cracked programs, that are spread on the peering networks. Free software may also be downloaded from the official web page, and the adware is supplied as a legal bundled program.
There is no need to blame yourself. A huge amount of people oftentimes make use of the unreliable programs from untrusted providers: abandonware, a wide range of tools that are free of cost, or even hacked programs. Every one of these types of programs are dangerous, since it is quite simple to integrate a Beast-dip malware under the guise of part of the license hacking script, or as a part of the self-made algoritm within the Windows optimization tool.
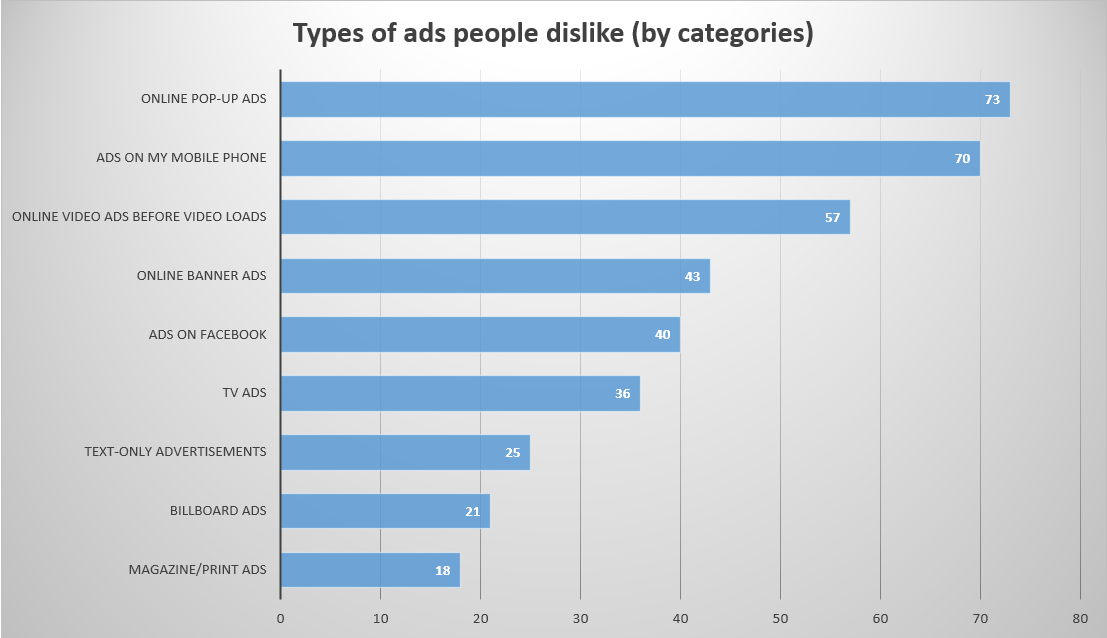
The statistic shows that people dislike popup advertising more than other types of promotions
How can I get rid of Beast-dip pop-up advertisements?
The manual of Beast-dip adware elimination contains 2 parts. First, we need to remove the malware, and after that fix the consequences of its activity. The elimination task is pretty easy, since it may be performed even with making use of Microsoft Defender – anti-malware software that is present on all computers with Windows 8/10. However, due to its significant resources consumption, along with some errors that can be pivotal for some groups of individuals, Defender is frequently disabled by the users, so its usage is likely impossible. Moreover, a variety of trojan viruses have the ability to shut off the embedded antivirus. It is better to use the separated program that will not have such weakness.
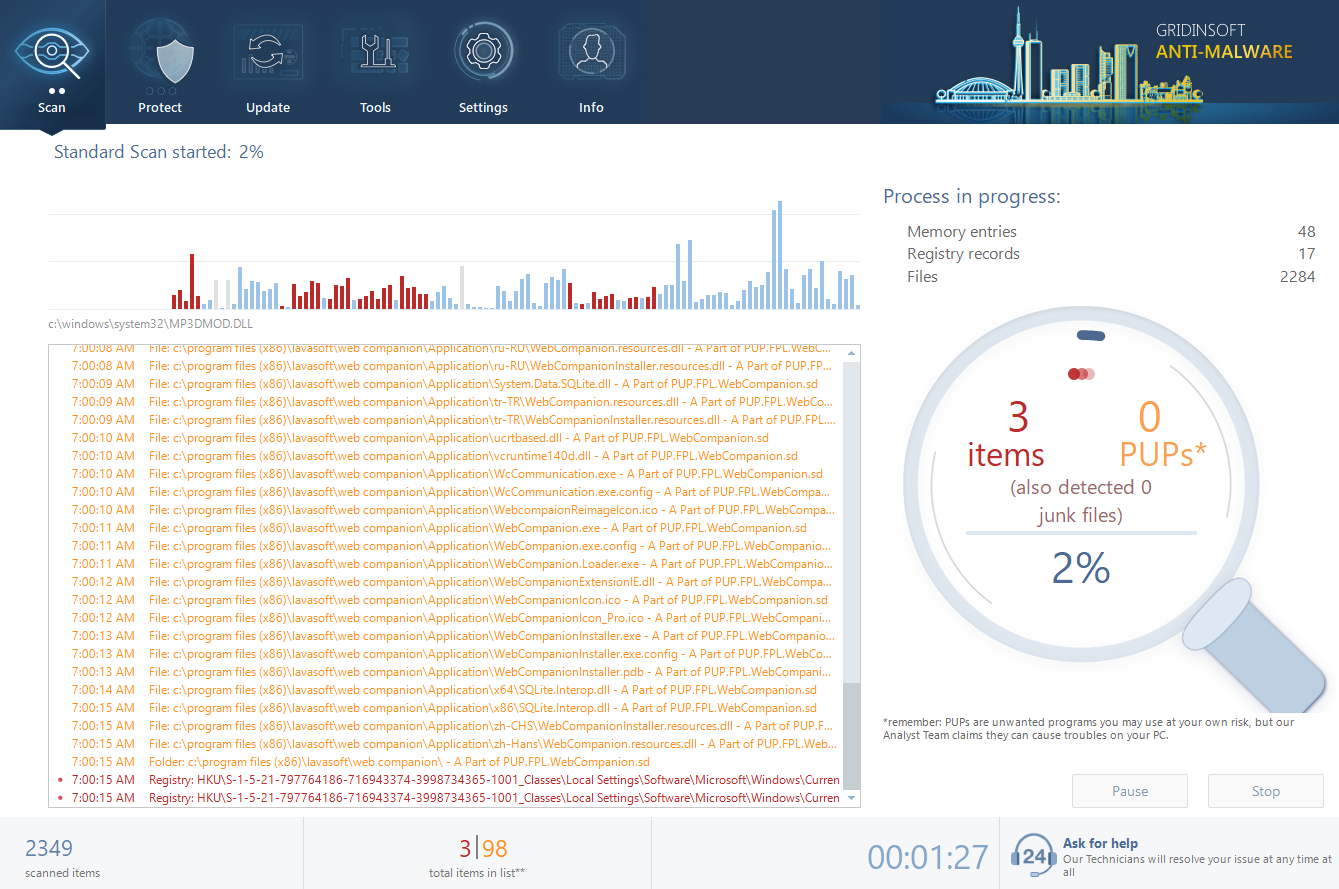
- Standard scan checks the logical disk where the system files are stored, together with the files of programs you have already installed. The scan lasts up to 6 minutes.
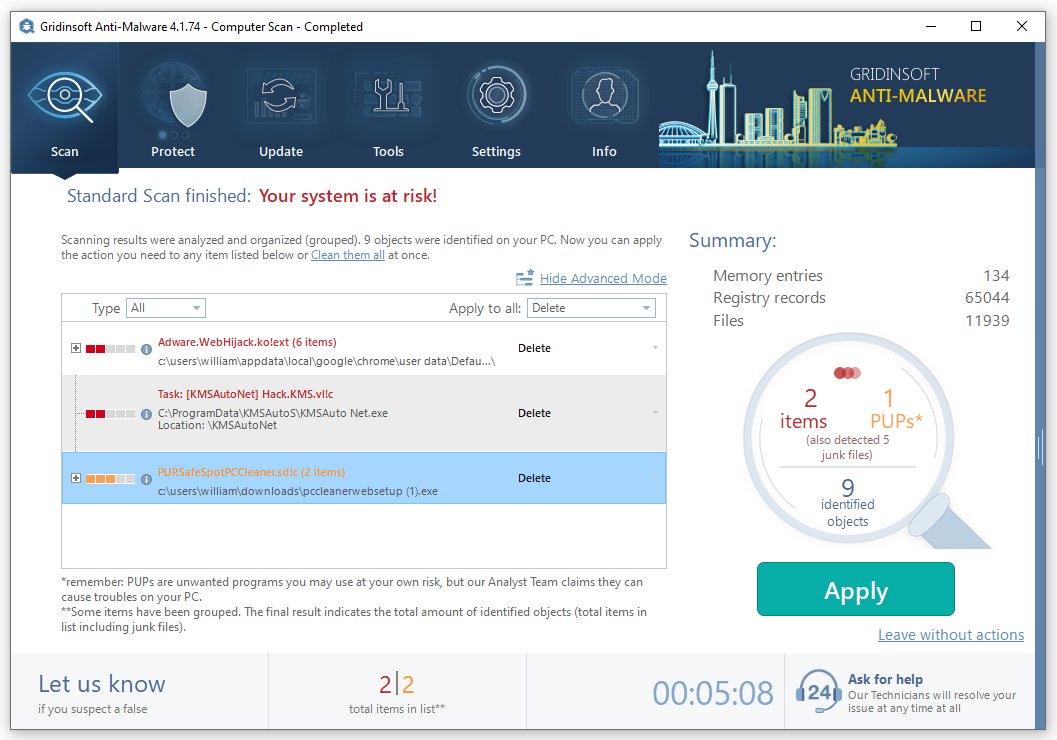
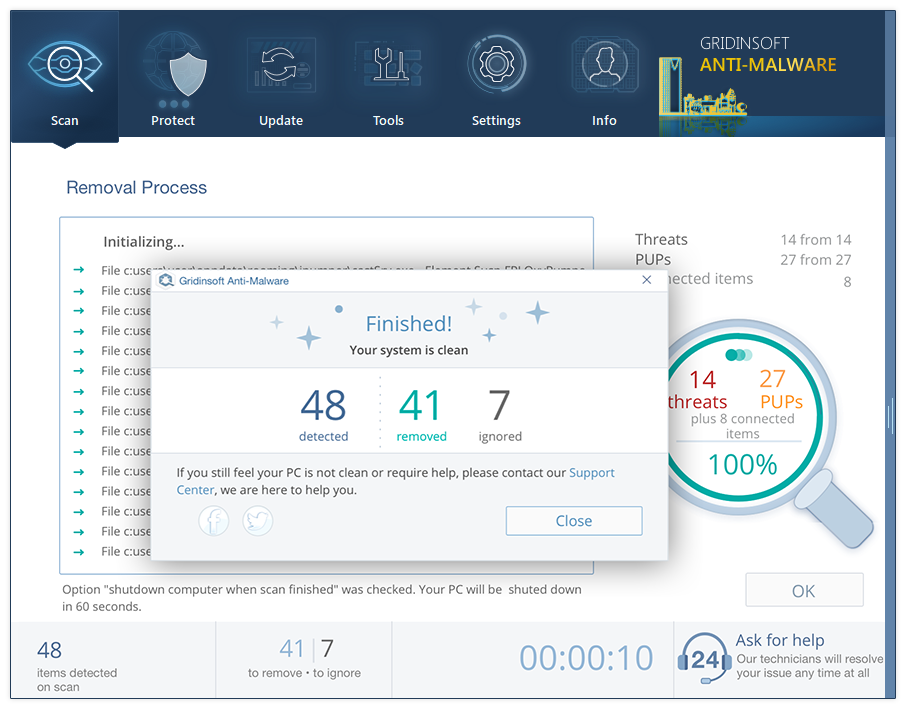
- When the scan is over, you may choose the action for each detected virus. For all files of Beast-dip malware the default option is “Delete”. Press “Apply” to finish the malware removal.
Reset browser settings to default
Manual method of browser reset
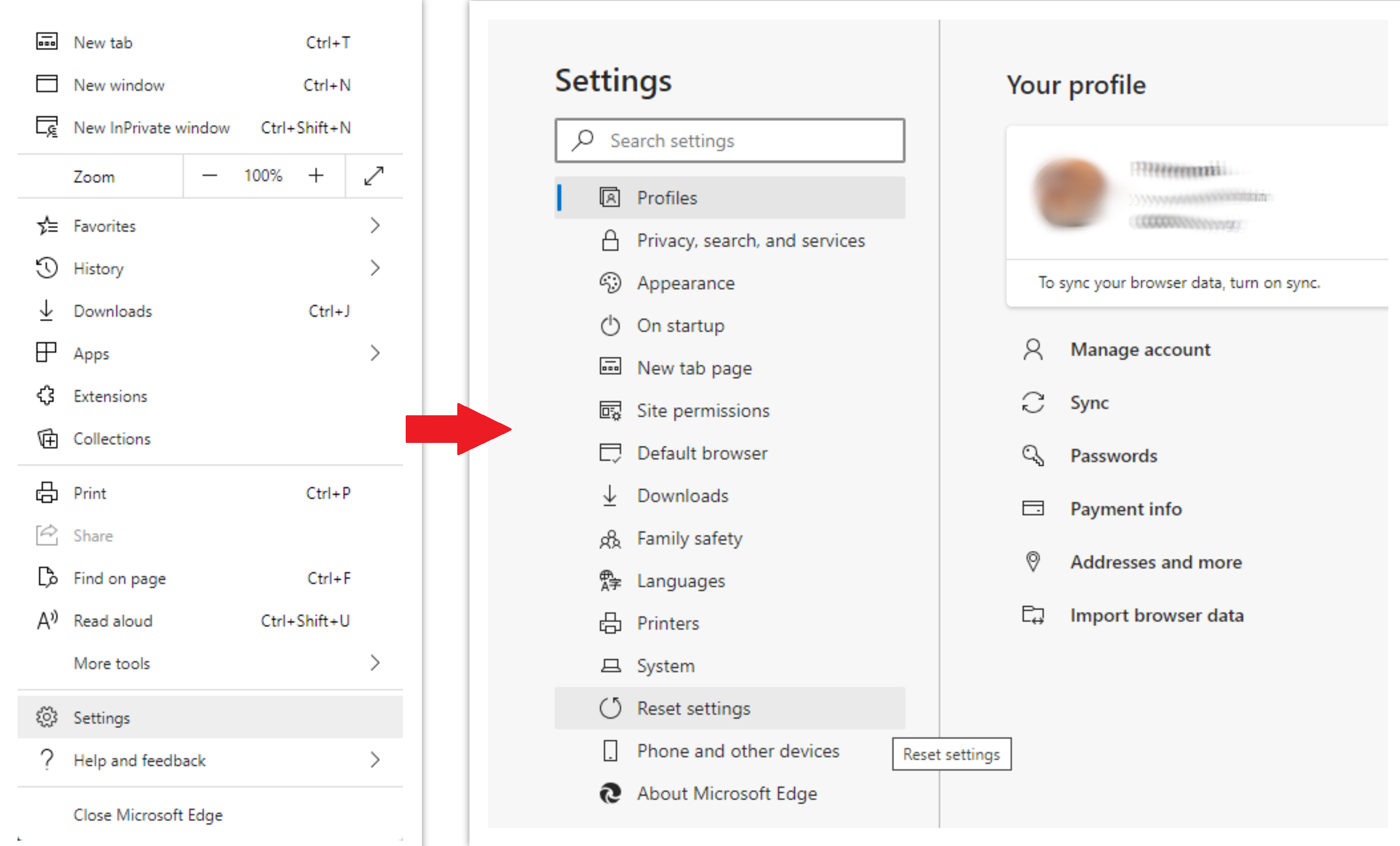
To reset Edge, do the following steps :
- Open “Settings and more” tab in upper right corner, then find here “Settings” button. In the appeared menu, choose “Reset settings” option :
- After picking the Reset Settings option, you will see the following menu, stating about the settings which will be reverted to original :
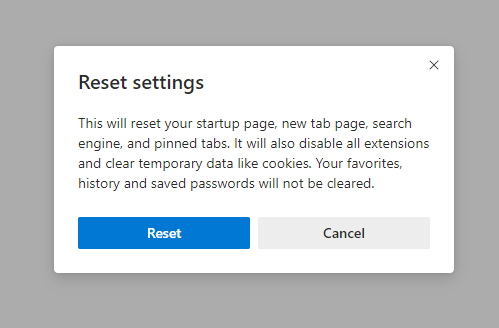
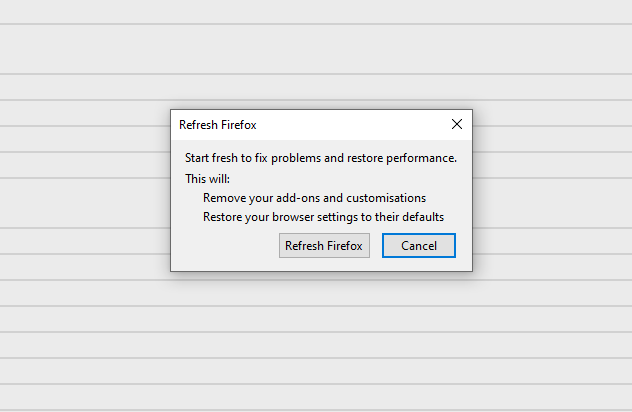
For Mozilla Firefox, do the next actions :
- Open Menu tab (three strips in upper right corner) and click the “Help” button. In the appeared menu choose “troubleshooting information” :
- In the next screen, find the “Refresh Firefox” option :
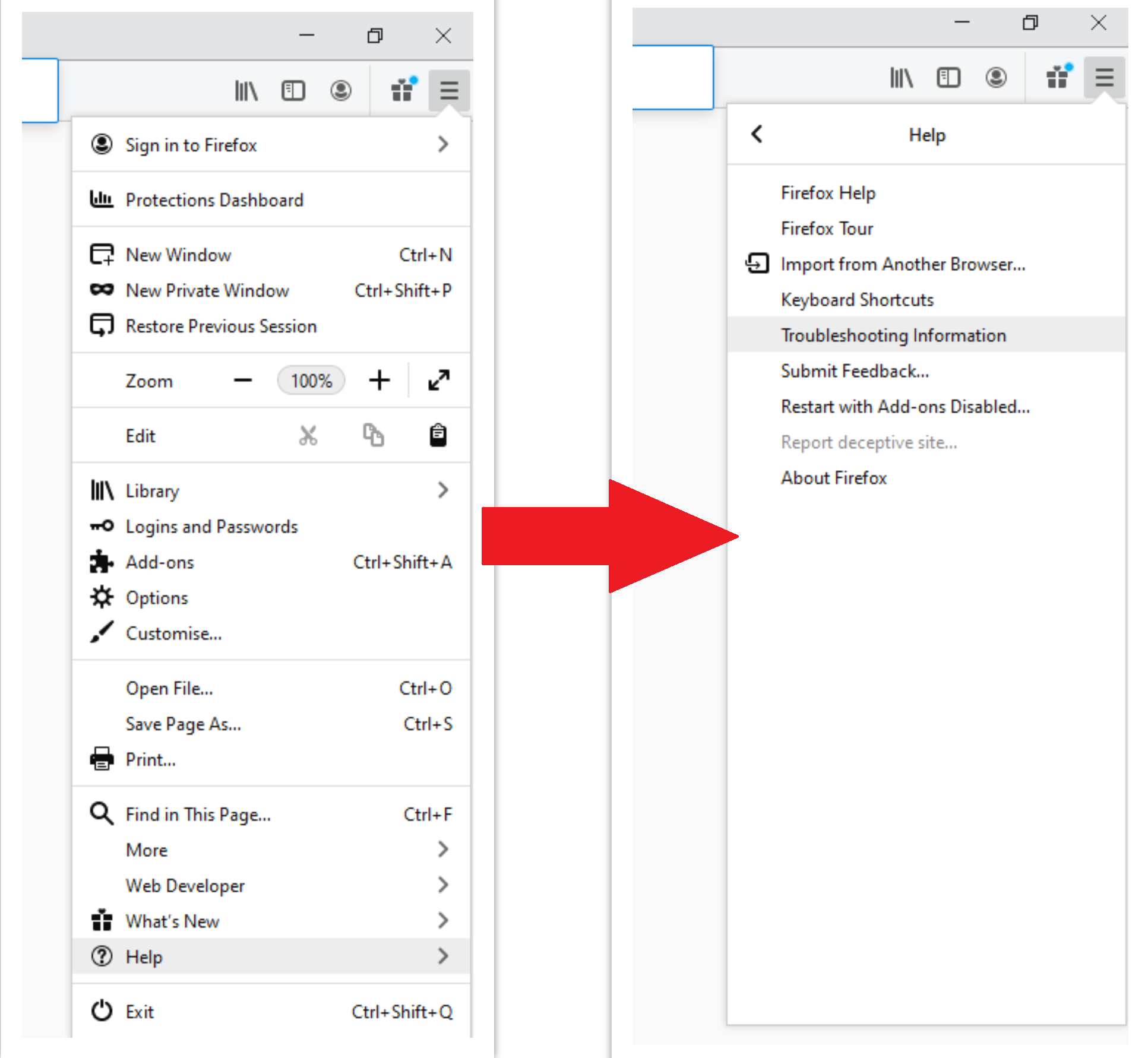
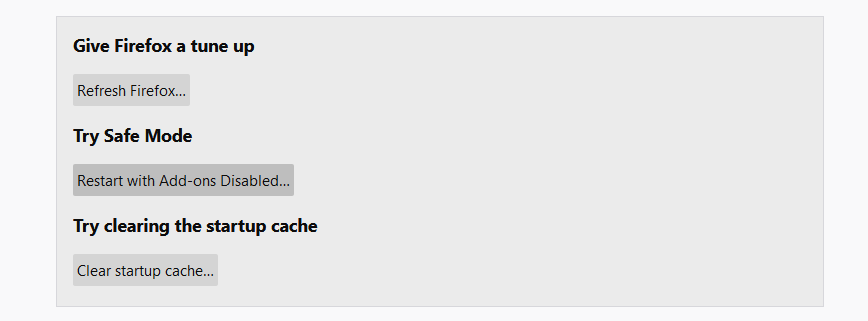
After choosing this option, you will see the next message :
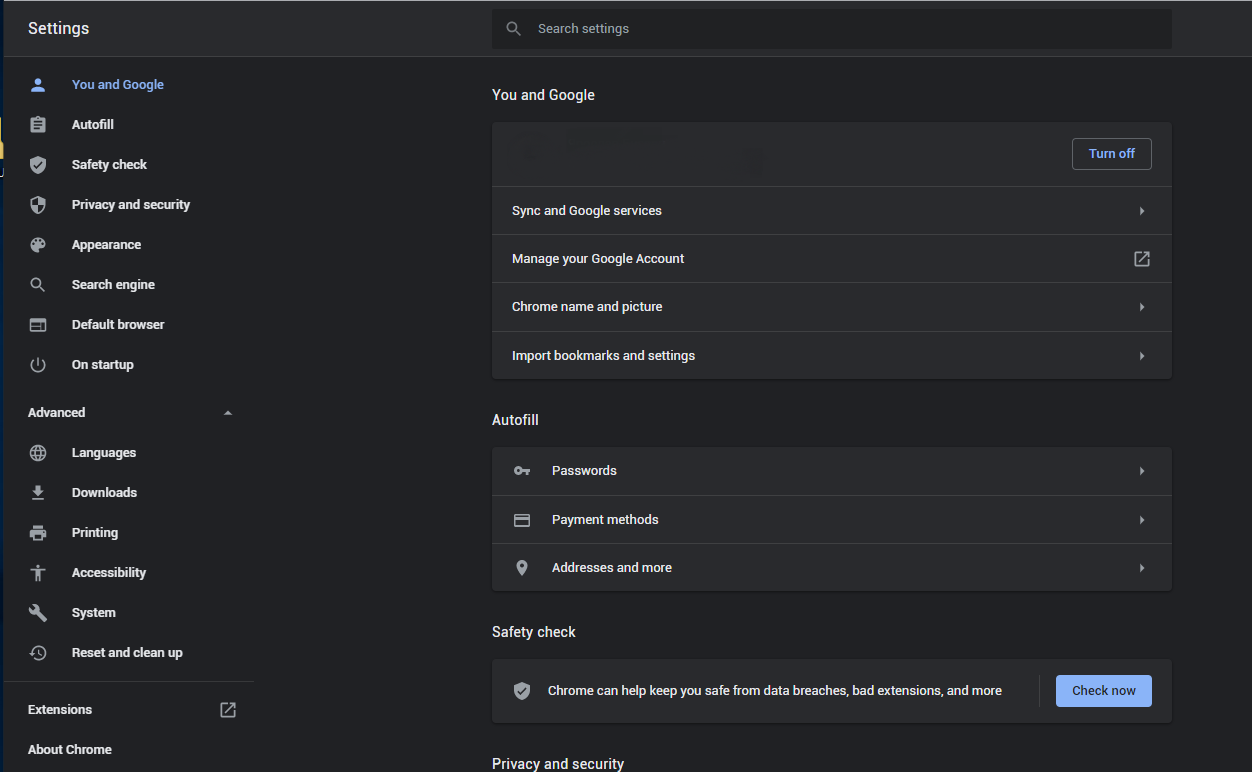
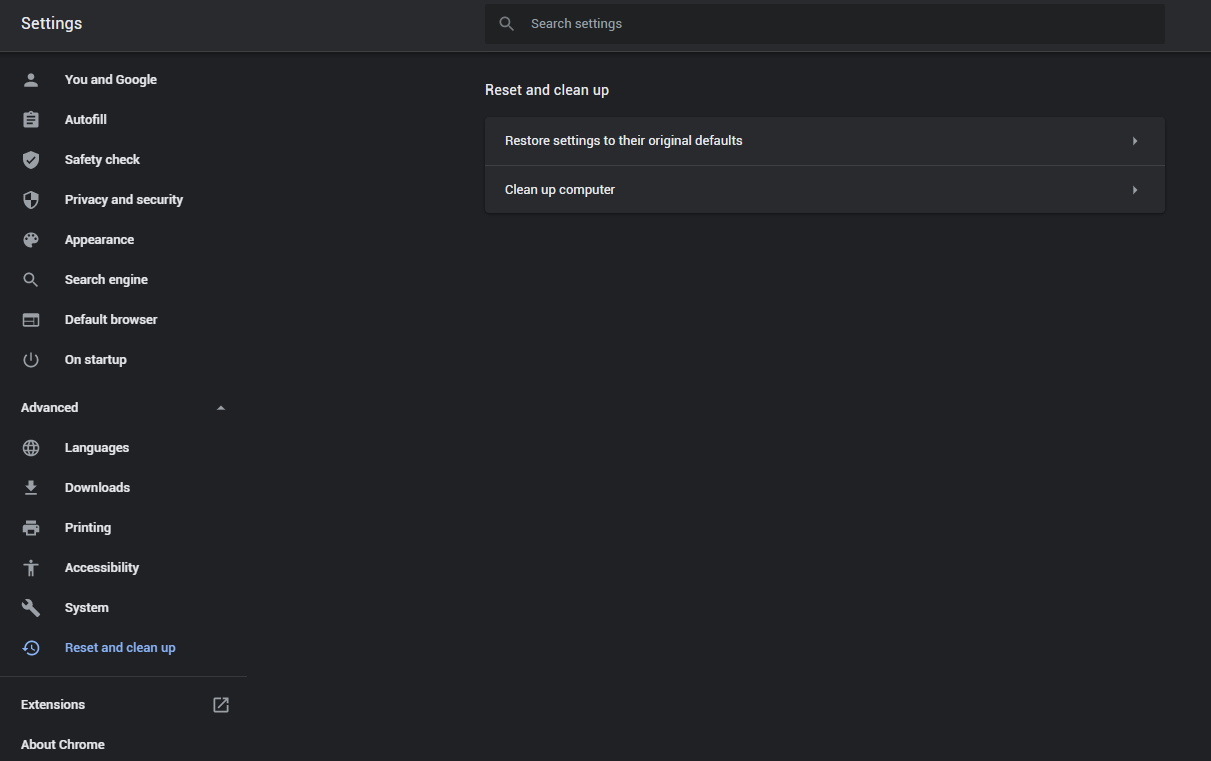
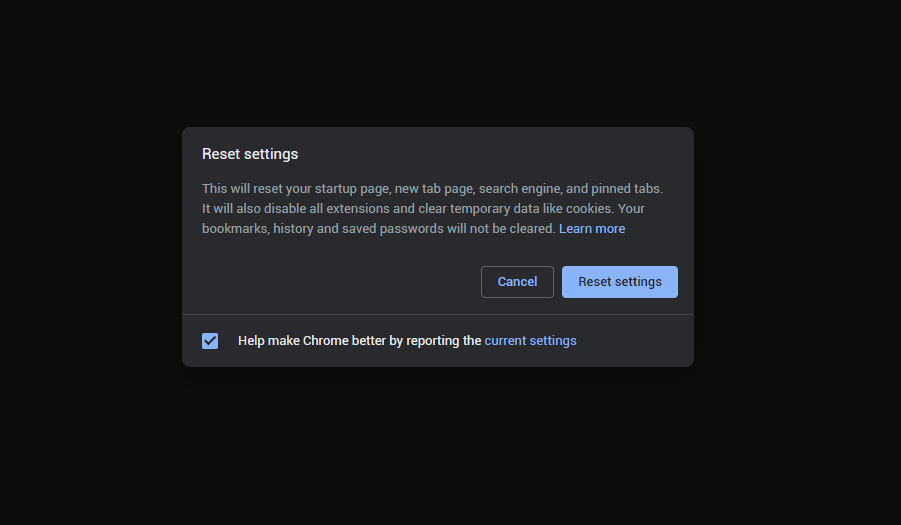
If you use Google Chrome
- Open Settings tab, find the “Advanced” button. In the extended tab choose the “Reset and clean up” button :
- In the appeared list, click on the “Restore settings to their original defaults” :
- Finally, you will see the window, where you can see all the settings which will be reset to default :
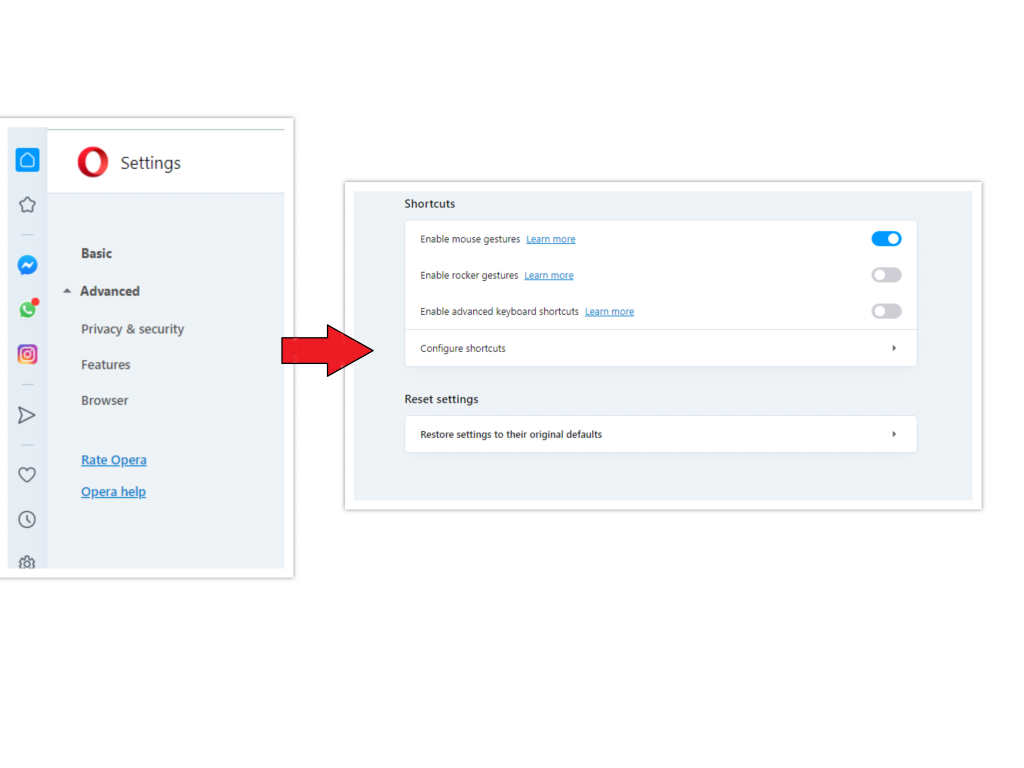
Opera can be reset in the next way
- Open Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click “Advanced” option, and choose “Browser” button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there “Restore settings to their original defaults” option :
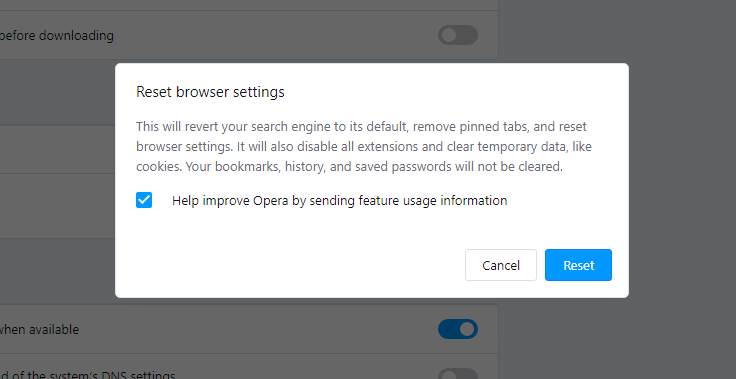
- After clicking the “Restore settings…” button, you will see the window, where all settings, which will be reset, are shown :
When the browsers are reset, you need to make sure that your browser will connect the accurate DNS while connecting to the web page you want. Create a text file titled “hosts” on your pc’s desktop, after that open it and fill it with the following lines3:
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a ‘#’ symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handle within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
Find the hosts.txt file in C:/Windows/System32/drivers/etc directory. Rename this file to “hosts.old.txt” (to distinguish it from the new one), and then move the file you created on the desktop to this folder. Remove the hosts.old from this folder. Now you have your hosts file as good as new.
Nevertheless, there is one problem that makes the things much more difficult to restore, particularly without the anti-malware software. A lot of adware variations that are used to show you the Beast-dip pop-up promotions are changing the deep browser settings, disabling an access to the settings tab. So, if you attempt to change your browser settings after your computer was penetrated by pop-up-related malware, your browser will certainly crash quickly. In some cases, you will see no crash, but huge lag spike after pressing the “settings” key. Browser will stop responding for ~ 30 seconds, and afterwards it will be back to the normal, up until you attempt to open settings again.
References
- More about pop-up ads on Wikipedia.
- Official Microsoft guide for hosts file reset.


Leave a Comment