What is BDDY file infection?
Also referred to as Matrix ransomware, it modifies your documents by means of encrypting them and demanding the ransom to be paid allegedly to restore access to them. [email protected] email using as a channel for contacting the ransomware authors.
Matrix Ransomware is installed on computers running Windows with the help of exploit kits on sites that display malicious and regular ads that target vulnerabilities in Internet Explorer (CVE-2016-0189) and Flash (CVE-2015-8651). Both of these vulnerabilities target visitors to these sites using the already unsupported and outdated versions of Internet Explorer and Flash Player. To get infected, it is enough for the user to simply open such a site in his browser and the exploit will work anyway, having delivered the crypto-ransomware to the vulnerable computer.
Warning! BDDY virus also actively distributed by hacking through an insecure RDP configuration. How to change RDP port read here
The Matrix virus is active again through its new cryptovirus bearing the name of BDDY.
BDDY Threat Main Facts
| Name | BDDY or Matrix virus |
| Extension | [[email protected]].XXX-XXX.BDDY |
| Type | Ransomware |
| Author | [email protected] |
| Detection | Win32/Injector.EJPK, Trojan:Win32/BDDY, Trojan.Yakes |
| Short Description | The ransomware encrypt the documents on the attacked PC and asks for the ransom to be paid by the victim supposedly to restore them. |
| Symptoms | The file virus encrypts the data, also generating the one-of-a-kind identifier. |
| Distribution Method | Spam, Email attachments, Compromised legitimate downloads, Attacks exploiting weak or stolen RDP credentials1. |
| Fix Tool | See If Your System Has Been Affected by BDDY file virus |
BDDY File Virus – Matrix Ransomware
What Is It and How Did I Get It?
The BDDY ransomware is most commonly spread by means of a payload dropper. It runs the malicious script that eventually installs the file virus. The threat circulates actively on the web, considering the facts about the ransomware mentioned in the VirusTotal database. The BDDY ransomware may also promote its payload files through popular social networks and via file-sharing platforms. Alternatively, some free applications hosted on many popular resources may also be disguised as helpful tools, whereas they instead may lead to the malicious scripts that injected the ransomware. Your personal caution to prevent the BDDY virus attack matters a lot!
Quotation of the
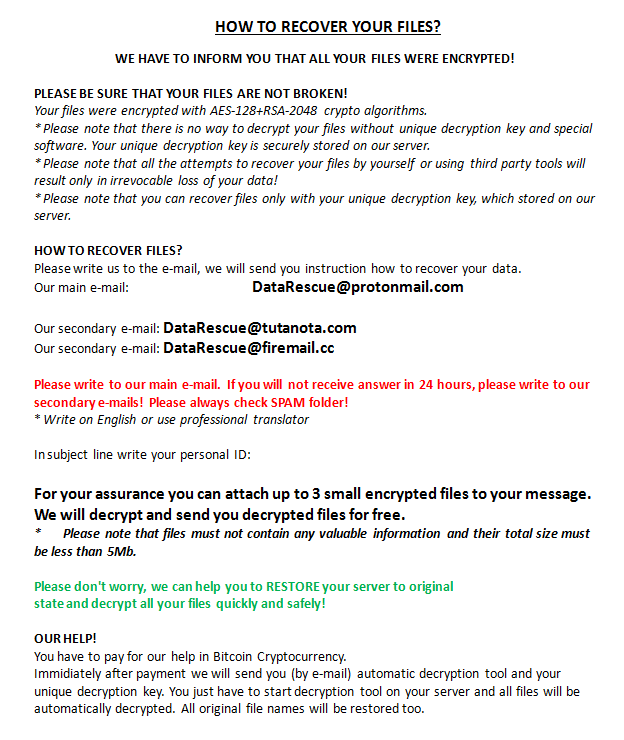
Matrix scary message
HOW TO RECOVER YOUR FILES? WE HAVE TO INFORM YOU THAT ALL YOUR FILES WERE ENCRYPTED! PLEASE BE SURE THAT YOUR FILES ARE NOT BROKEN! Your files were encrypted with AES-128+RSA-2048 crypto algorithms. * Please note that there is no way to decrypt your files without unique decryption key and special software. Your unique decryption key is securely stored on our server. * Please note that all the attempts to recover your files by yourself or using third party tools will result only in irrevocable loss of your data! * Please note that you can recover files only with your unique decryption key, which stored on our server. HOW TO RECOVER FILES? Please write us to the e-mail, we will send you instruction how to recover your data. Our main e-mail: [email protected] Please write to our main e-mail. If you will not receive answer in 24 hours, please write to our secondary e-mails! Please always check SPAM folder! * Write on English or use professional translator In subject line write your personal ID: ***** For your assurance you can attach up to 3 small encrypted files to your message. We will decrypt and send you decrypted files for free. * Please note that files must not contain any valuable information and their total size must be less than 5Mb. Please don't worry, we can help you to RESTORE your server to original state and decrypt all your files quickly and safely! OUR HELP! You have to pay for our help in Bitcoin Cryptocurrency. Immidiately after payment we will send you (by e-mail) automatic decryption tool and your unique decryption key. You just have to start decryption tool on your server and all files will be automatically decrypted. All original file names will be restored too.
Remove [email protected] File Virus (Matrix)
Reasons why I would recommend GridinSoft2
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

What the next?
References
- How To Change Remote Desktop (RDP) Port: https://howtofix.guide/change-remote-desktop-port-on-windows-10/


Leave a Comment