Zegost is a sophisticated malware that primarily infiltrates systems via targeted email attacks, malvertising, and social engineering tactics. It stealthily gathers sensitive information, including operating system details, network connections, and keystrokes, and transmits this data to remote servers.
Characterized by its unique evasion techniques, such as clearing event logs and detecting sandbox environments, Zegost stands out for its multifaceted spying capabilities, including webcam capture, making it a formidable cyber threat.
Zegost Overview
Zegost is a type of malware that steals information. Since its emergence around 2011, cybercriminals have distributed it via targeted email attacks. The groups behind Zegost are notorious for their persistent and innovative tactics, using multiple exploits to establish and sustain connections with their targets.
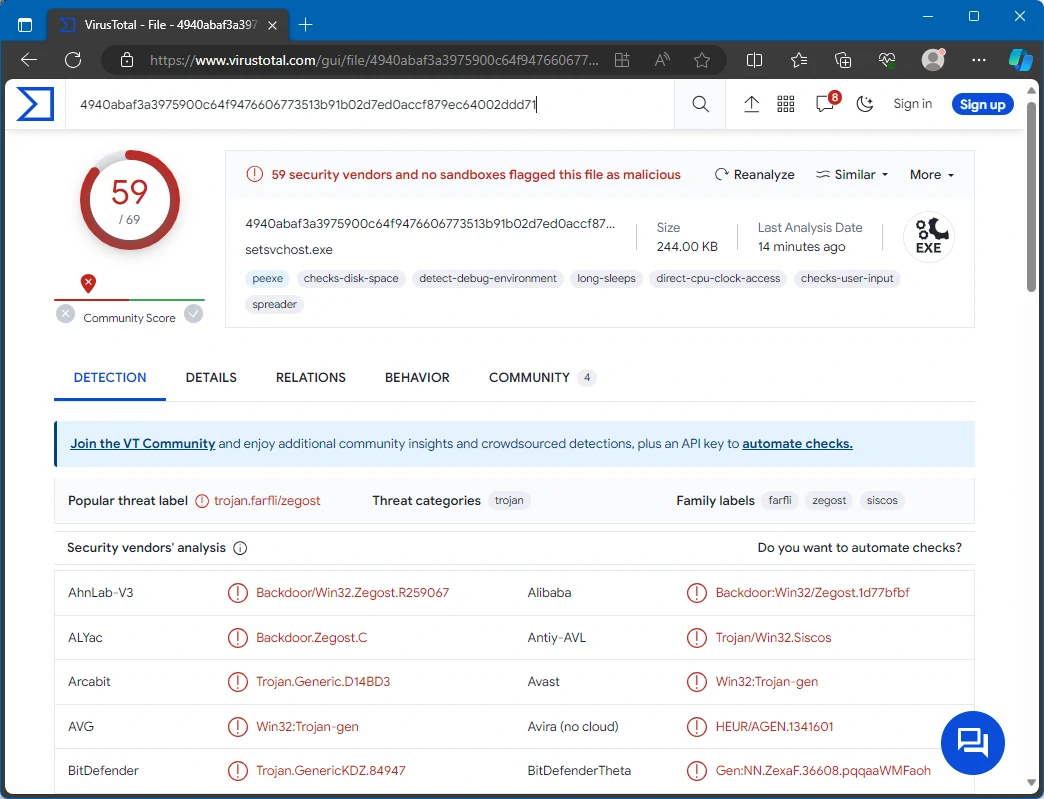
Zegost scan result on VirusTotal
| Name | Zegost information stealer |
| Threat Type | Information Stealer |
| Detection | Trojan.Win32.Kryptik.sa, Backdoor:Win32/Farfli!pz (Microsoft) |
| Damage | Stolen sensitive information, identity theft, monetary loss, privacy issues, and more. |
| Similar Behavitor | SapphireStealer, Luca Stealer |
Technical Analysis
To stay under the radar, Zegost deliberately wipes event logs (including Application, Security, and System logs) and initiates specific processes, setting it apart from standard infostealers. It functions in visible and hidden windows. It ensures continual operation by automatically launching as a service and manipulating registry keys. Over time, this malware has evolved to incorporate Component Object Model (COM) programming, a relatively rare technique in malware. Its comprehensive surveillance capabilities now include capturing video through the device’s webcam and employing the DirectShow capture filter to identify devices. Additionally, it can detect sandbox environments, further refining its avoidance mechanisms.
Spreading Methods
Zegost infiltrates computers primarily through targeted email attacks, showcasing its perpetrators’ methodical and precise approach. In these attacks, the malware is often hidden in seemingly harmless email attachments or links, leveraging recipients’ trust to access their systems.
Additionally, the malware spreads through malvertising, a tactic where attackers embed malicious code in online ads, leading unsuspecting users to download the malware. Moreover, social engineering tactics, like counterfeit software updates or deceptive alerts, deceive users into running the malware.
Other prevalent distribution methods include pirated software, cracking tools, peer-to-peer (P2P) networks, third-party downloaders, and exploiting software vulnerabilities.
How To Remove Malware
While it’s possible to remove malware manually, it’s generally not advisable. Malware often aims to establish persistence by creating multiple instances of itself, making complete tracing and removal very challenging. Consequently, manual removal efforts tend to be time-consuming and often ineffective.


Leave a Comment