If you spectate the alert of Win32/Yandex.K detection, it appears that your system has a problem. All viruses are dangerous, without any deviations. Yandex unwanted application can not be called full-size malware. Nevertheless, this app collects data beyond measure. Additionally, there are a number of cases when users mention that this app acts like spyware or backdoor.
Any kind of malware exists with the only target – gain money on you. And the developers of these things are not thinking of morality – they use all available tactics. Taking your personal data, receiving the comission for the promotions you watch for them, utilizing your CPU and GPU to mine cryptocurrencies – that is not the complete list of what they do. Do you want to be a riding horse? That is a rhetorical question.
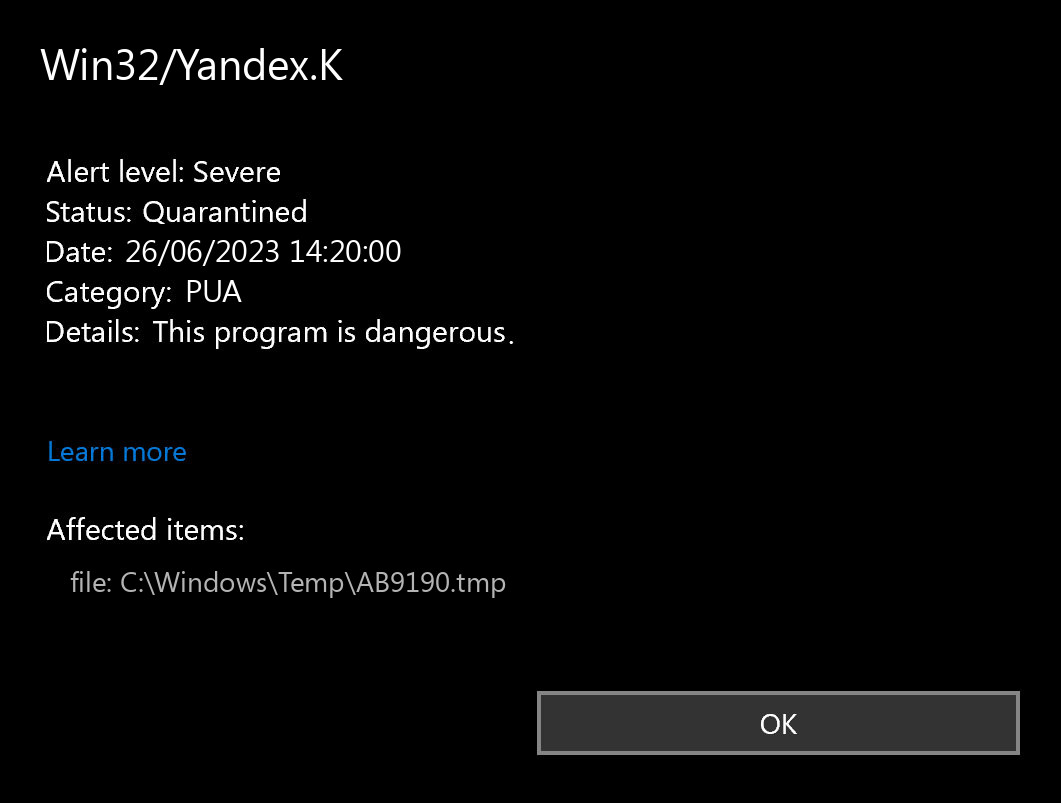
What does the pop-up with Win32/Yandex.K detection mean?
The Win32/Yandex.K detection you can see in the lower right side is demonstrated to you by Microsoft Defender. That anti-malware program is pretty good at scanning, however, prone to be basically unreliable. It is defenseless to malware invasions, it has a glitchy user interface and problematic malware removal features. Thus, the pop-up which says about the Yandex is rather just an alert that Defender has actually recognized it. To remove it, you will likely need to make use of a separate anti-malware program.
Win32/Yandex.K unwanted program is a typical example of PUA, which is widespread nowadays. It collects all your data and can share it ti third parties. Some examples of this program type can have no helpful functionality – only the shell with the colorful interface. It is promoted as a all in one and can change your browser settings and switch home page and search engine to yandex. This or another way, it does not give you any actual capability, exposing you to risk instead.
Unwanted Program Summary:
| Name | Yandex PUA |
| Detection | Win32/Yandex.K |
| Damage | Yandex is at least useless, or can perform various malicious actions on your PC. |
| Fix Tool | See If Your System Has Been Affected by Yandex exploit |
Is Win32/Yandex.K dangerous?
I have already detailed that Win32/Yandex.K PUA is not as harmless as it pretends to be. The “legit and useful” program may abruptly uncover itself as a downloader trojan, spyware, backdoor, or coin miner virus. And you can never predict what to look for even from different instances of Yandex unwanted program. That still does not mean that you have to panic – probably, this unpleasant thing has not succeeded to do negative things to your PC.
The particular harm to your system may be caused not only due to the malware injection. A huge share of doubtful programs, like the Yandex app is, is just poorly designed. Possibly, their actions are rather helpful than worthless if done on particular system configurations, but not on each one. That’s how an uncomplicated system optimization application can create chaos with continuous BSODs on your system. Any interruptions to the system registry are not very safe, and they are much more risky if performed with such programs.
How did I get this virus?
It is difficult to line the sources of malware on your PC. Nowadays, things are mixed up, and spreading methods utilized by adware 5 years ago can be utilized by spyware nowadays. However, if we abstract from the exact distribution method and will think about why it has success, the explanation will be really basic – low level of cybersecurity awareness. Individuals click on promotions on weird sites, open the pop-ups they receive in their web browsers, call the “Microsoft tech support” thinking that the scary banner that states about malware is true. It is necessary to understand what is legitimate – to prevent misunderstandings when trying to figure out a virus.
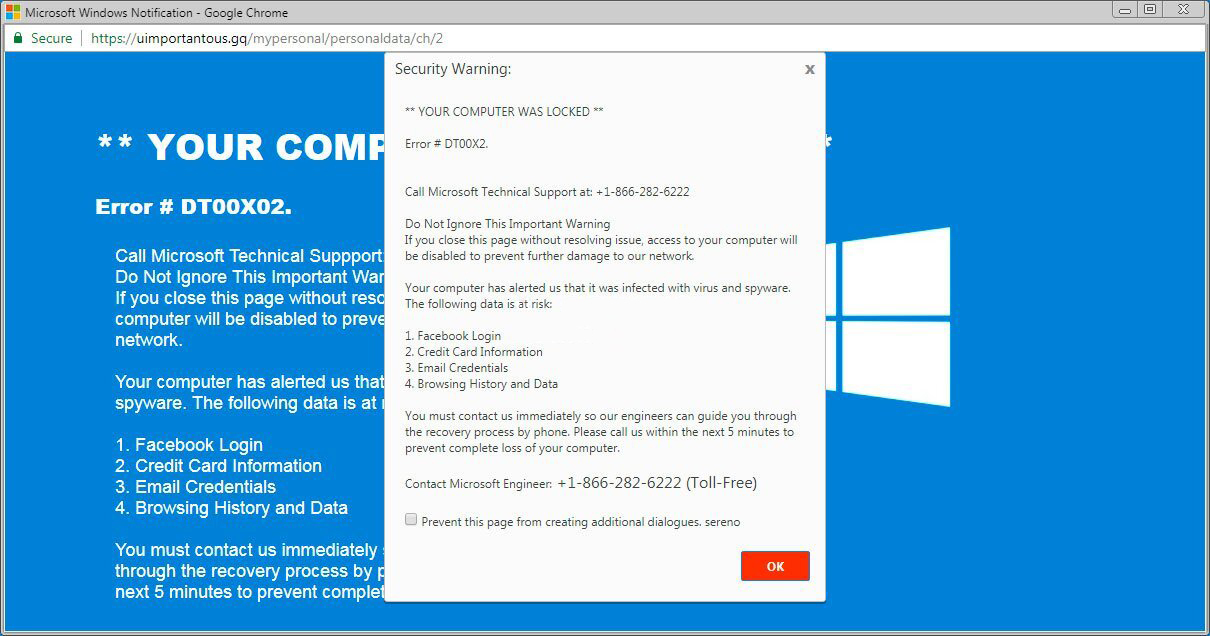
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most common ways of malware spreading – lure emails and also injection into a hacked program. While the first one is not so easy to stay away from – you need to know a lot to recognize a fake – the second one is simple to solve: just do not utilize hacked applications. Torrent-trackers and various other providers of “free” applications (which are, in fact, paid, but with a disabled license checking) are just a giveaway point of malware. And Win32/Yandex.K is just within them.
Technical details
File Info:
crc32: 66D40CE7md5: 511e1a8d9b95687629c36884cea69ed4name: 511E1A8D9B95687629C36884CEA69ED4.mlwsha1: 1ece566e9d615d8b17dc89617c6e25908c661ddasha256: 1766255e3087e04b69eb40a0ac7469be0247dfca6dfb53cecf2ab76f5fd096d4sha512: cc96d75a03c7c5a0b7c293e1135375a39c2e549ff6cc9d8d2a9d932077c87cca99021d22f24d833af87b7f6caf7bd7d882225376a84460bc644cc215dbe4644bssdeep: 49152:lqeNVZO5iBN36iiZQCu9f0BTHgXhfSUxV:0E3OwjagJ0ZgXxxxVtype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
LegalCopyright: FileVersion: 1.2.02.3 CompanyName: vkx43enatktx435_DJ Comments: This installation was built with Inno Setup.ProductName: x412x43aox43dx430x442x43ax442ex414x438x434x435x436x439 ProductVersion: 1.00075153 FileDescription: x412x43aox43dx430x442x43ax442ex414x438x434x435x436x439 Setup OriginalFileName: Translation: 0x0000 0x04b0


Leave a Comment