What is Win32/Kryptik.GJBR infection?
In this post you will discover concerning the definition of Win32/Kryptik.GJBR and its unfavorable effect on your computer system. Such ransomware are a type of malware that is clarified by on-line frauds to require paying the ransom money by a sufferer.
In the majority of the cases, Win32/Kryptik.GJBR ransomware will certainly instruct its targets to start funds move for the objective of neutralizing the changes that the Trojan infection has introduced to the victim’s gadget.
Win32/Kryptik.GJBR Summary
These adjustments can be as follows:
- Executable code extraction. Cybercriminals often use binary packers to hinder the malicious code from reverse-engineered by malware analysts. A packer is a tool that compresses, encrypts, and modifies a malicious file’s format. Sometimes packers can be used for legitimate ends, for example, to protect a program against cracking or copying.
- Attempts to connect to a dead IP:Port (2 unique times);
- Creates RWX memory. There is a security trick with memory regions that allows an attacker to fill a buffer with a shellcode and then execute it. Filling a buffer with shellcode isn’t a big deal, it’s just data. The problem arises when the attacker is able to control the instruction pointer (EIP), usually by corrupting a function’s stack frame using a stack-based buffer overflow, and then changing the flow of execution by assigning this pointer to the address of the shellcode.
- A process attempted to delay the analysis task.;
- Repeatedly searches for a not-found process, may want to run with startbrowser=1 option;
- Performs some HTTP requests;
- Unconventionial language used in binary resources: Estonian;
- Detects Sandboxie through the presence of a library;
- Attempts to remove evidence of file being downloaded from the Internet;
- Creates or sets a registry key to a long series of bytes, possibly to store a binary or malware config;
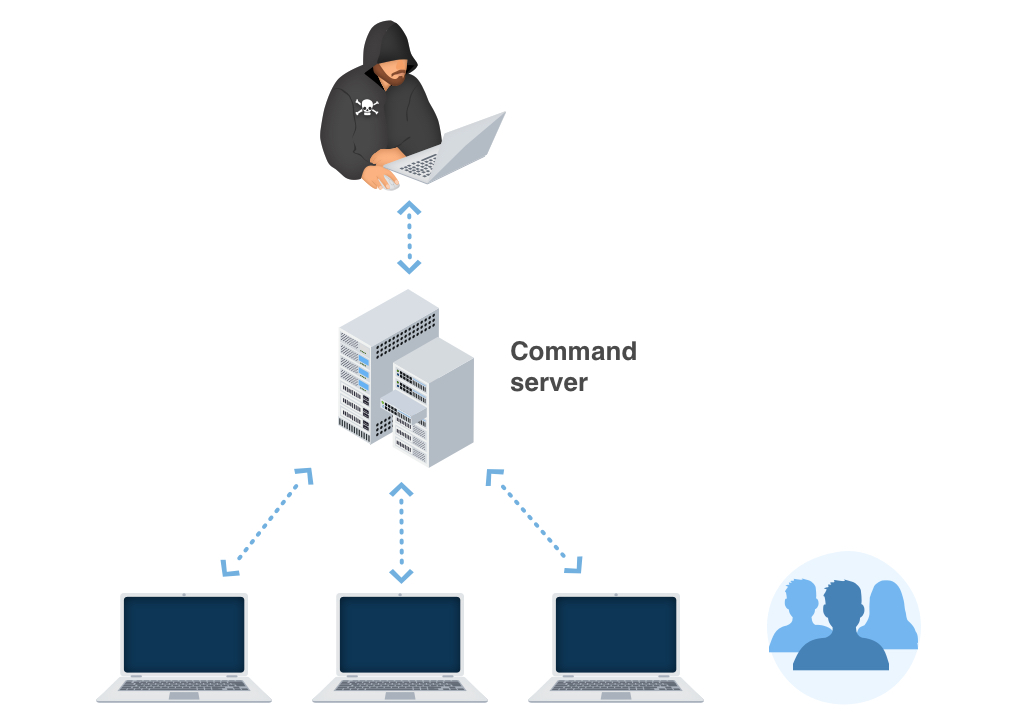
- A system process is generating network traffic likely as a result of process injection;
- Installs itself for autorun at Windows startup. There is simple tactic using the Windows startup folder located at:
C:\Users\[user-name]\AppData\Roaming\Microsoft\Windows\StartMenu\Programs\Startup. Shortcut links (.lnk extension) placed in this folder will cause Windows to launch the application each time [user-name] logs into Windows.The registry run keys perform the same action, and can be located in different locations:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- Creates a hidden or system file. The malware adds the hidden attribute to every file and folder on your system, so it appears as if everything has been deleted from your hard drive.
- Checks the presence of disk drives in the registry, possibly for anti-virtualization;
- Creates a copy of itself;
- Ciphering the documents located on the victim’s hard drive — so the sufferer can no longer utilize the information;
- Preventing normal access to the sufferer’s workstation. This is the typical behavior of a virus called locker. It blocks access to the computer until the victim pays the ransom.
Similar behavior
Related domains
| milliaoin.info | Ransom.GandCrypt!8.F33E (CLOUD) |
| lionoi.adygeya.su | Ransom.GandCrypt!8.F33E (CLOUD) |
| ionoiddi.mangyshlak.su | Ransom.GandCrypt!8.F33E (CLOUD) |
| missidiowi.xyz | Ransom.GandCrypt!8.F33E (CLOUD) |
| io90s8dudi.xyz | Ransom.GandCrypt!8.F33E (CLOUD) |
Win32/Kryptik.GJBR
One of the most normal networks where Win32/Kryptik.GJBR Ransomware Trojans are injected are:
- By means of phishing emails;
- As a consequence of individual ending up on a resource that holds a malicious software;
As soon as the Trojan is effectively infused, it will certainly either cipher the information on the target’s computer or prevent the tool from working in a correct fashion – while also putting a ransom money note that points out the need for the victims to effect the payment for the function of decrypting the documents or restoring the data system back to the first problem. In the majority of circumstances, the ransom note will turn up when the client reboots the COMPUTER after the system has actually already been damaged.
Win32/Kryptik.GJBR distribution channels.
In various edges of the globe, Win32/Kryptik.GJBR expands by jumps and also bounds. However, the ransom notes as well as techniques of extorting the ransom amount might differ depending on certain neighborhood (local) settings. The ransom money notes and methods of obtaining the ransom money quantity may differ depending on specific local (local) setups.
For instance:
Faulty signals concerning unlicensed software application.
In certain areas, the Trojans often wrongfully report having actually found some unlicensed applications made it possible for on the sufferer’s device. The alert after that demands the individual to pay the ransom.
Faulty declarations concerning unlawful web content.
In countries where software piracy is much less popular, this method is not as effective for the cyber fraudulences. Additionally, the Win32/Kryptik.GJBR popup alert may wrongly claim to be deriving from a law enforcement establishment and also will report having situated child porn or other illegal information on the device.
Win32/Kryptik.GJBR popup alert may falsely claim to be acquiring from a law enforcement organization and will certainly report having situated child porn or various other unlawful data on the gadget. The alert will similarly include a need for the customer to pay the ransom money.
Technical details
File Info:
crc32: DCBFDAAAmd5: 50e22beb41a5ef7a0cbde8bb3e2a1eaaname: 50E22BEB41A5EF7A0CBDE8BB3E2A1EAA.mlwsha1: 39428298425f223f7bce33aae0e272a165dfb5e4sha256: 4e4700b68451c8fc77c6ed0991293458e5054cf6d3e483a5cd83d7c0d7ae9a65sha512: e959986026e2a07effa51b316989e12131a14fca6cb18e59505aee21fb86b6b75511d4b014a4c22118091801f329c6d5548627e7c68561b4b5f6ee9fd6e5fadfssdeep: 3072:7B7hD9c5sAYoy3a5KSLN6EorlHfJ5IhqBoNtT4q0c8saCvv:7rWsADyRSLwEoryU6tkqThaCntype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
Translation: 0x0809 0x04b0
Win32/Kryptik.GJBR also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Bkav | W32.AIDetect.malware1 |
| Elastic | malicious (high confidence) |
| MicroWorld-eScan | Trojan.BRMon.Gen.4 |
| FireEye | Generic.mg.50e22beb41a5ef7a |
| CAT-QuickHeal | Trojan.Chapak.ZZ6 |
| McAfee | Packed-FJJ!50E22BEB41A5 |
| Cylance | Unsafe |
| AegisLab | Trojan.Win32.GandCrypt.trv4 |
| Sangfor | Trojan.Win32.Save.a |
| K7AntiVirus | Riskware ( 0040eff71 ) |
| BitDefender | Trojan.BRMon.Gen.4 |
| K7GW | Riskware ( 0040eff71 ) |
| Cybereason | malicious.b41a5e |
| Cyren | W32/Kryptik.HB.gen!Eldorado |
| Symantec | Packed.Generic.525 |
| APEX | Malicious |
| Avast | Win32:Malware-gen |
| Kaspersky | HEUR:Trojan.Win32.Generic |
| Alibaba | Trojan:Win32/Bunitu.8fa6475f |
| NANO-Antivirus | Trojan.Win32.GandCrypt.ffqvhp |
| Rising | Ransom.GandCrypt!8.F33E (CLOUD) |
| Ad-Aware | Trojan.BRMon.Gen.4 |
| Emsisoft | Trojan.BRMon.Gen.4 (B) |
| Comodo | TrojWare.Win32.TrojanDownloader.Godzilla.B@7tk49d |
| F-Secure | Heuristic.HEUR/AGEN.1102756 |
| DrWeb | Trojan.Encoder.24384 |
| Zillya | Trojan.GenericKDZ.Win32.2111 |
| TrendMicro | Ransom_GANDCRAB.SMALY-3 |
| McAfee-GW-Edition | BehavesLike.Win32.Generic.ch |
| Sophos | Mal/Generic-R + Mal/GandCrab-B |
| Ikarus | Trojan.Win32.Crypt |
| Jiangmin | Trojan.GandCrypt.hm |
| MaxSecure | Ransomeware.GandCrypt.Gen |
| Avira | HEUR/AGEN.1102756 |
| MAX | malware (ai score=88) |
| Antiy-AVL | Trojan[Ransom]/Win32.GandCrypt |
| Microsoft | TrojanProxy:Win32/Bunitu.Q!bit |
| Arcabit | Trojan.BRMon.Gen.4 |
| SUPERAntiSpyware | Trojan.Agent/Gen-Emotet |
| ZoneAlarm | HEUR:Trojan.Win32.Generic |
| GData | Trojan.BRMon.Gen.4 |
| Cynet | Malicious (score: 100) |
| AhnLab-V3 | Win-Trojan/Gandcrab04.Exp |
| Acronis | suspicious |
| BitDefenderTheta | Gen:NN.ZexaF.34590.muW@aSz2DdnI |
| ALYac | Trojan.Ransom.GandCrab |
| VBA32 | BScope.Trojan.Vigorf |
| Malwarebytes | Generic.Malware/Suspicious |
| Panda | Trj/Genetic.gen |
| ESET-NOD32 | a variant of Win32/Kryptik.GJBR |
| TrendMicro-HouseCall | Ransom_GANDCRAB.SMALY-3 |
| Tencent | Win32.Backdoor.Mokes.Swba |
| Yandex | Trojan.GandCrypt!BsBSXOn0sxo |
| SentinelOne | Static AI – Suspicious PE |
| Fortinet | W32/Kryptik.GJBV!tr |
| AVG | Win32:Malware-gen |
| Paloalto | generic.ml |
| CrowdStrike | win/malicious_confidence_100% (D) |
| Qihoo-360 | Win32/Trojan.e2e |
How to remove Win32/Kryptik.GJBR ransomware?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials, or crypt your documents for ransom.
Reasons why I would recommend GridinSoft1
There is no better way to recognize, remove and prevent PC threats than to use an anti-malware software from GridinSoft2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Win32/Kryptik.GJBR files and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.

Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
If the guide doesn’t help you to remove Win32/Kryptik.GJBR you can always ask me in the comments for getting help.
User Review
( votes)References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison