What is Trojan:Win32/Wacatac.B!ml?
Trojan:Win32/Wacatac.B!ml is a highly concerning and sophisticated malware variant that falls under the category of trojans, which are malicious software programs designed to deceive users and provide unauthorized access to their systems. As a virus analyst, I would consider Trojan:Win32/Wacatac.B!ml a significant threat due to its ability to perform various malicious activities while evading traditional security measures.
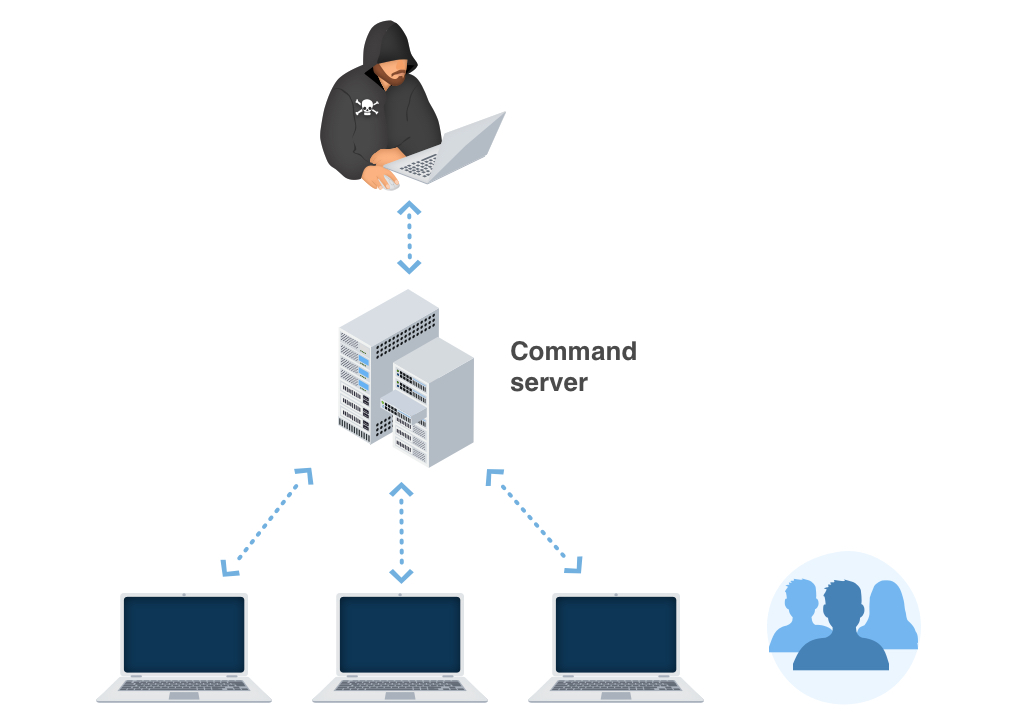
Wacatac.B!ml trojan is characterized by its use of advanced obfuscation techniques and polymorphic capabilities, making it challenging to detect using signature-based methods alone. It often employs social engineering tactics to deceive users into executing it, such as disguising itself as legitimate software or using enticing filenames. Once executed, Trojan:Win32/Wacatac.B!ml can perform actions like stealing sensitive information, downloading additional payloads, and enabling remote control by a malicious actor.
The “ml” in the malware’s name indicates that it’s part of a machine learning detection family, and Microsoft Defender employs machine learning algorithms to identify and combat this threat.
In most cases, the Trojan:Win32/Wacatac.B!ml shows no signs of its activity. Its main goal – data theft – depends heavily on remaining undetected. The more time Wacatac is active – the more harm it can do to you and your system.
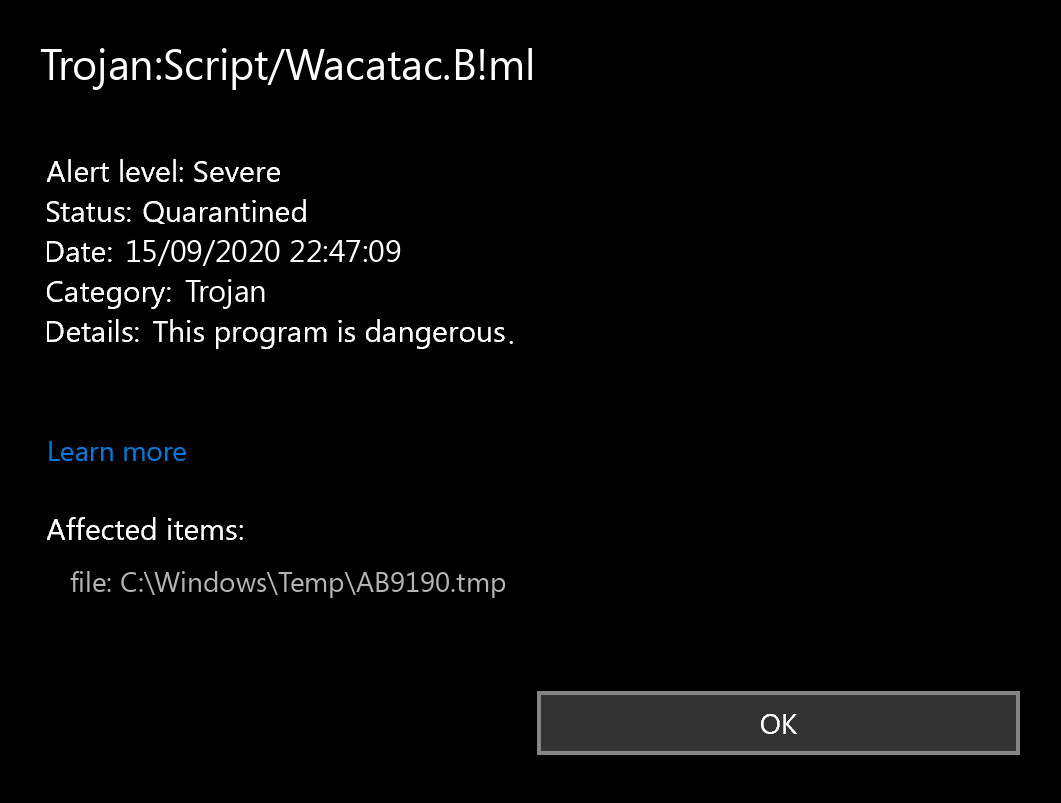
Trojan:Win32/Wacatac.B!ml Detection by Microsoft
Wacatac.B!ml In Details
This malware actively makes the following modifications:
- Cybercriminals often use binary packers to actively hinder the malicious code from being reverse-engineered by malware analysts. A packer is a tool that compresses, encrypts, and modifies the format of a malicious file. Sometimes, packers can be used for legitimate purposes, for example, to protect a program against cracking or copying.
- It creates RWX memory, a security trick involving memory regions that allows an attacker to fill a buffer with a shellcode and then execute it. This becomes a problem when the attacker can control the instruction pointer (EIP) by corrupting a function’s stack frame using a stack-based buffer overflow and changing the execution flow by assigning this pointer to the address of the shellcode.
- The binary likely contains encrypted or compressed data, concealing virus code from antiviruses and virus analysts.
- Network activity is detected but not explicitly expressed in API logs. Microsoft integrated an API solution into its Windows operating system, which reveals network activity for all apps and programs that ran on the computer in the past 30 days. However, this malware hides network activity.
- Changes in networking settings. The virus makes several additional entries in the HOSTS file and modifies various registry keys.
By being aware of these details about Trojan:Win32/Wacatac.B!ml, users can take necessary precautions to protect their systems from this dangerous Trojan. Using reputable antivirus software, keeping systems updated, and practicing safe computing habits are essential in defending against malware threats.
Trojan:Win32/Wacatac.B!ml Distribution Methods
The biggest share of Wacatac.B!ml virus distribution is after these methods:
Email spamming became a prevalent malware distribution method since the users do not raise suspicion on notifications from DHL or Amazon about the incoming delivery. However, it is quite easy to distinguish the malevolent email from the original one. One sent by cybercriminals has a strange sender address – something like [email protected]. At the same time, the original email address has a specific domain name (@amazon.com or @dhl.us) and can also be seen on the official website in the “Contact us” tab.
Malicious advertisements on the web are an old-timer of malware distribution. The advice to stop clicking the blinking advertisements on untrustworthy websites exists as long as the ads are on the Internet. You can also install ad-blocking plugins for your web browser – they will deal with any ads. However, if they are generated by adware already present on your PC, ad blockers will be useless.
Software bundling is widespread among virus developers. Users who hack the programs to make them usable without purchasing a license approve any offer to include another program in the pack because they are gaining money in such a way. Check precisely the installation window for signs like “Advanced installation settings” or so. The ability to switch off the malware installation often hides under such items.
Signs of Trojan:Win32/Wacatac.B!ml presence.
In different edges of the world, victims of the Wacatac.B!ml say about different signs of virus activity. Nonetheless, the common sign that your PC was infected is that its behavior differs from the one you used to.
Wacatac.B!ml activity is hard to detect. And it is not a thing you must wonder about – viruses like this must stay undetected to be more effective and bring more effects. All changes it does are far away from the places where the user works. Group Policies, notifications settings, registry, Task Scheduler – these parts of the operating system are visited only when something goes wrong. And users get the fact that something is wrong only after the successful Wacatac activity.
It is quite hard to detect the changes done in the registry and Group Policies because of the huge amount of entries in these system elements. But the notifications settings, especially Task Scheduler, are elementary to control. If you see that the programs you are used to receiving notifications have stopped sending them to you or several programs have been added to the list, it is better to raise suspicion. The scheduler is a rare-used application, so if you had nothing scheduled and now see that something appeared in it, launch the anti-malware program.
Technical details
Wacatac.B!ml also known as:
Remove Wacatac.B!ml with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Trojans as shown from our tests with the software, and we assure you that it can remove Wacatac.B!ml as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “Wacatac.B!ml” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing Wacatac.B!ml and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
Frequently Asked Questions (FAQ) about Wacatac.B!ml
This detection name is a specific detection name used by Microsoft Defender to identify a variant of the Wacatac Trojan. The detection is used to mark different malware strains that have 2 capabilities to share – info stealing and malware delivery.
Trojan:Win32/Wacatac.B!ml typically spreads through malicious email attachments, software downloads from untrusted sources, or exploiting software vulnerabilities. It may also be distributed through compromised websites.
It can steal sensitive data, such as login credentials and financial information, compromise system security, and create a backdoor for remote attackers to gain unauthorized access.
Manual removal of Trojan:Win32/Wacatac.B!ml is not recommended for most users, as it involves dealing with system files and registry entries that may lead to further damage if mismanaged. It is best to rely on reputable antivirus software to remove the malware safely.
Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offers real-time protection for the first two days. If you want to be fully protected at all times – I can recommend you purchase a full version:
If the guide doesn’t help you remove Wacatac.B!ml, you can always ask me in the comments to get help.


This virus is making this thing called “steroids” and some other thing run in the background, it is disabling my windows defender, and I need to pay money for this software that I need desperately, is there any other software that IS FREE that can help. Please respond as soon as you can!
GridinSoft Anti-Malware has 6 days Free Trial. Did you try it?
i was not able to clean the virus after scan, how?