If you spectate the alert of Trojan:Win32/Detplock detection, it seems that your computer has a problem. All viruses are dangerous, with no exceptions. Detplock provides the criminals access to your system, or perhaps connects it to the botnet.
What does the notification with Trojan:Win32/Detplock detection mean?
The Trojan:Win32/Detplock detection you can see in the lower right corner is shown to you by Microsoft Defender. That anti-malware software is good at scanning, but prone to be basically unstable. It is prone to malware attacks, it has a glitchy interface and problematic malware clearing features. For this reason, the pop-up which says about the Detplock is simply a notification that Defender has recognized it. To remove it, you will likely need to use a separate anti-malware program.
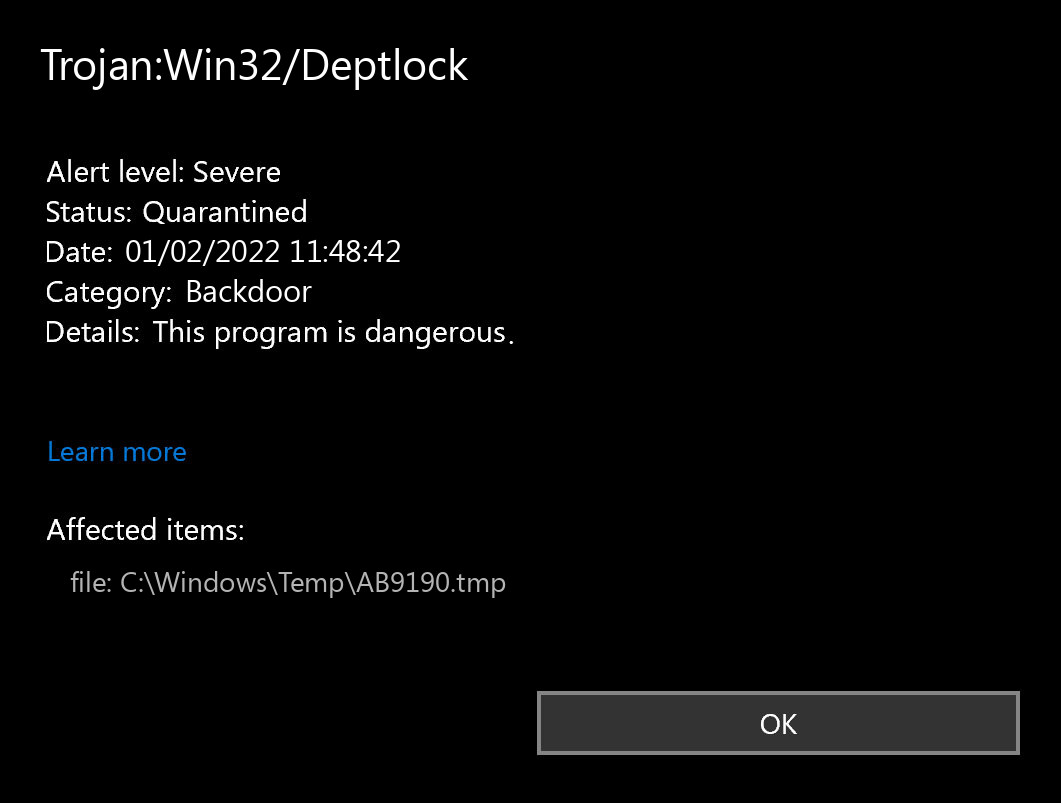
Trojan:Win32/Deptlock detection
The exact Trojan:Win32/Detplock virus is a very unpleasant thing. This malware is designed to be a sneaky intruder, which acts as a remote-access tool. When you grant someone else remote access willingly, it is OK, but Detplock will not ask you if you wish to give it. After connecting to your system, criminals are free to do whatever they want – getting your files, browsing your messages, gathering personal data, et cetera. Backdoors frequently carry an additional stealer – the virus that is developed to gather all available data about you. Nonetheless, far more common use of the backdoors is setting up the botnet. After that, the network of corrupted PCs can be used to conduct DDoS attacks or to inflate the vote results on various sites.
Backdoor Summary:
| Name | Detplock Backdoor |
| Detection | Trojan:Win32/Detplock |
| Damage | Gain access to the operating system to perform various malicious actions. |
| Similar | Pcclient, Darkkomet, Bifrose, Ircbot, Patched, Win64 Sandcat, Msil Turtleloader, Blacknet |
| Fix Tool | See If Your System Has Been Affected by Detplock backdoor |
Shortly about backdoors
Is Trojan:Win32/Detplock dangerous?
As I have pointed out before, non-harmful malware does not exist. And Trojan:Win32/Detplock is not an exception. This backdoor does not deal a lot of harm exactly after it releases. Nonetheless, it will likely be a really unpleasant surprise when a random online forum or website in the Internet will not let you in, due to the fact that your IP-address is disallowed after the DDoS attack. However, even if it is not vital for you – is it pleasurable at all to know that someone else can simply access your computer, check out your conversations, open your files, as well as spectate what you do?
List of the actions Deptlock Trojan does on your PC
The spyware that is usually present as a supplement to the Trojan:Win32/Detplock virus will likely be just another reason to remove it as fast as you can. Nowadays, when users’ data is priced remarkably high, it is too illogical to give the crooks such a chance. Even worse if the spyware will somehow manage to grab your financial info. Seeing 0 on your financial account is the most awful problem, in my opinion.
How did I get this virus?
It is difficult to line the origins of malware on your computer. Nowadays, things are mixed up, and spreading methods used by adware 5 years ago can be used by spyware these days. However, if we abstract from the exact spreading method and will think of why it has success, the reply will be pretty uncomplicated – low level of cybersecurity knowledge. People press on ads on weird sites, click the pop-ups they get in their browsers, call the “Microsoft tech support” thinking that the scary banner that says about malware is true. It is important to know what is legit – to stay away from misconceptions when attempting to find out a virus.
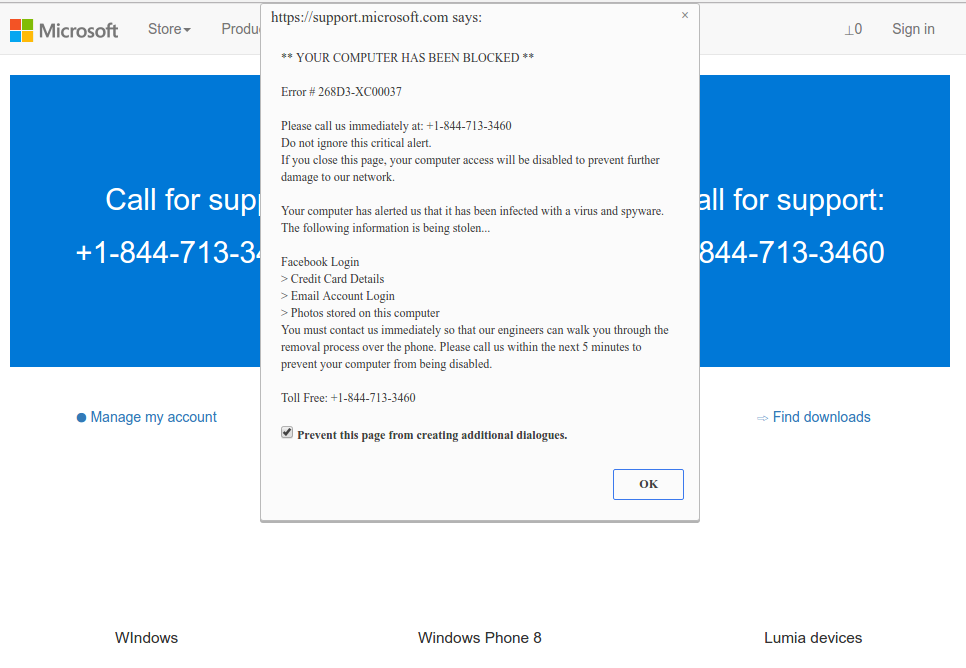
Microsoft Tech Support Scam
Nowadays, there are two of the most extensive methods of malware distribution – lure emails and injection into a hacked program. While the first one is not so easy to stay away from – you must know a lot to understand a fake – the second one is simple to address: just do not utilize cracked applications. Torrent-trackers and other sources of “free” applications (which are, exactly, paid, but with a disabled license checking) are really a giveaway place of malware. And Trojan:Win32/Detplock is just within them.
How to remove the Trojan:Win32/Detplock from my PC?
References
- Gossip about the backdoor in Intel processors on Reddit.


Leave a Comment