The Trojan:Win32/Lockbit is a dangerous ransomware that spreads through various malicious avenues such as trojans, spam campaigns, and deceptive software updates. Detection of Lockbit can cause serious problems for your computer
Once inside a system, Trojan:Win32/Lockbit encrypts files, demanding a ransom in Bitcoin. Victims are cautioned not to attempt manual decryption, as this could lead to permanent data loss. This ransomware has gained notoriety for targeting high-profile organizations and demanding substantial ransoms, making it a significant threat in the digital landscape.
Trojan:Win32/Lockbit Detection Overview
Trojan:Win32/Lockbit is a malicious ransomware program that poses a significant threat to computer users. This ransomware, once infiltrated into a system, encrypts files, rendering them inaccessible, and demands a ransom from victims in exchange for decryption tools. Detection of Trojan:Win32/Lockbit is critical, as allowing it to run can lead to severe consequences, including permanent data loss.
Upon infection, this ransomware renames files with the “.abcd“, “.lockbit“, “.lock2bits“, “.luckyday” extensions and drops a “Restore-My-Files.txt” text file into every affected folder. This text file serves as a ransom message, informing victims about the encryption and providing instructions on how to contact the ransomware developers via provided email addresses. After verification of the decryption file, victims are instructed to pay the ransom in Bitcoin. Attempting manual decryption or renaming encrypted files is discouraged, as it risks permanent data loss.
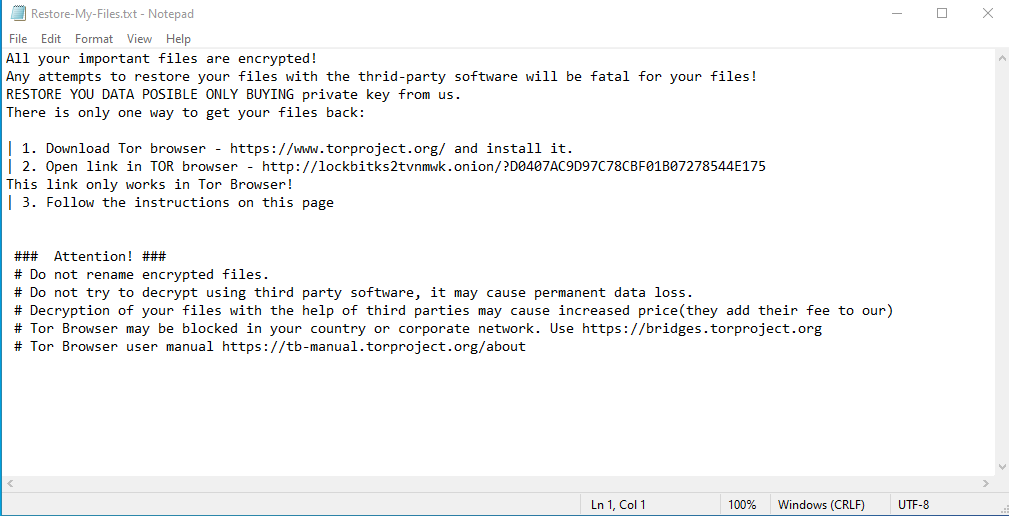
Screenshot of a message encouraging users to pay a ransom
In some high-profile cases, Trojan:Win32/Lockbit has targeted prominent organizations, demanding substantial ransoms, often in the millions of dollars. To protect against such infections, it is crucial to maintain backups on separate and unplugged storage devices or remote servers. Having multiple backup copies stored in different locations is advisable.
Detection is essential, but it’s worth noting that removing the ransomware does not restore compromised data. The only viable solution for data recovery is restoring files from a backup made before the infection occurred. In terms of how this ransomware spreads, it primarily proliferates through trojans, spam campaigns, illegal software activation tools, fake updaters, and untrusted download channels. These malicious methods underscore the importance of cautious online behavior and keeping software updated to minimize vulnerability to such threats.
Threat Summary:
| Name | Lockbit Ransomware |
| Detection | Trojan:Win32/Lockbit |
| Encrypted Files Extension | “.abcd“, “.lockbit“, “.lock2bits“, “.luckyday” |
| Details | All files are encrypted and cannot be opened without paying a ransom. Additional password-stealing trojans and malware infections can be installed together with a ransomware infection. |
| Fix Tool | See If Your System Has Been Affected by Lockbit Ransomware |
Is Trojan:Win32/Lockbit dangerous?
- The primary action of Trojan:Win32/Lockbit is the encryption of files on infected computers. It employs strong encryption algorithms to lock victims out of their own data. Once files are encrypted, they become inaccessible, and victims are left with limited options for data recovery.
- Lockbit’s operators demand a ransom payment in exchange for providing the decryption tools or keys. These ransoms can vary widely, sometimes reaching into the millions of dollars. The financial burden of such demands can be crippling for individuals and devastating for organizations.
- Victims are explicitly warned not to attempt manual decryption or rename encrypted files, as these actions can lead to permanent data loss. This means that without paying the ransom or having a secure backup in place, recovering the encrypted files becomes extremely challenging.
- Lockbit’s operators prefer to receive ransom payments in cryptocurrencies, making transactions difficult to trace, thereby ensuring their anonymity and evasion of law enforcement.
Trojan:Win32/Lockbit is dangerous not only because of its ability to encrypt data and demand ransoms but also due to its potential for widespread damage, targeting of high-profile entities, and the complex nature of its propagation methods. Defending against this threat requires a proactive approach, including robust cybersecurity measures, regular backups, and user education to recognize and avoid the malicious channels through which it spreads.
How did I get this virus?
You may be wondering how you ended up with Trojan:Win32/Lockbit ransomware on your computer. Ransomware infections can occur through several cunning methods:
- Frequently, ransomware enters your system through trojans, malicious software concealed as legitimate files or programs. Trojans can sneak into your computer via deceptive email attachments, compromised downloads, or by exploiting vulnerabilities in software. Once inside, they pave the way for the ransomware to take hold.
- Another common vector is spam emails. Cybercriminals craft convincing emails that appear official, important, or urgent, tricking you into opening attached files or clicking on links. These attachments may contain ransomware payloads, and a single click can initiate the infection.
- Ransomware often arrives disguised as seemingly harmless file formats like ZIP, RAR, or executable (.exe) files. Attackers also use Microsoft Office or PDF documents with embedded malicious scripts to trigger the infection when you open them. Executing these files unknowingly launches the ransomware.
- Illegitimate activation tools or “cracks” for software are a risky path. While attempting to bypass paid software licensing, you might inadvertently download malware, including ransomware, instead.

Screenshot of the updated LockBit ransomware
To protect your system, exercise caution when dealing with email attachments, avoid downloading files from unverified sources, keep your software up to date, and refrain from using illegal activation tools. Regularly backing up your data to separate and secure locations can also mitigate the impact of a ransomware attack. Use anti-virus programs such as Gridinsoft Anti-Malware.
Remove Lockbit with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Ransomwares as shown from our tests with the software, and we assure you that it can remove Lockbit as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “Lockbit” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing Lockbit and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
What is Trojan:Win32/Lockbit Virus?
Name: Trojan:Win32/Lockbit
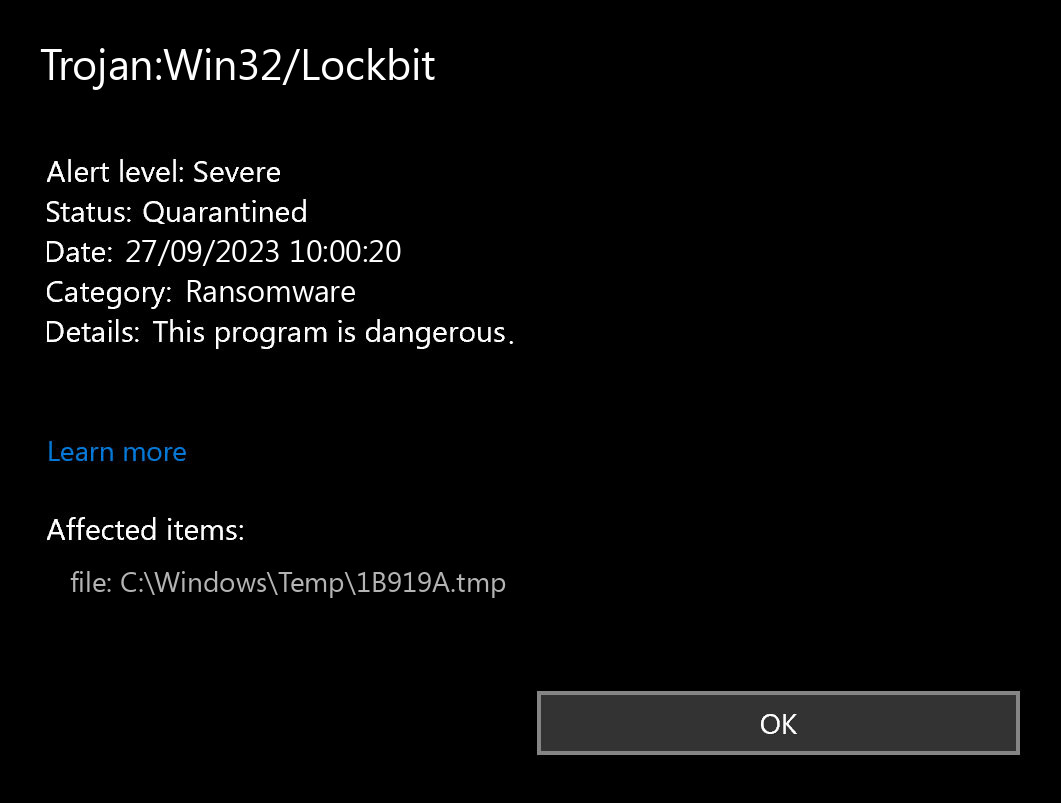
Description: If you have seen a message showing the “Trojan:Win32/Lockbit found”, it seems that your system is in trouble. The Lockbit virus was detected, but to remove it, you need to use a security tool. Windows Defender, which has shown you this message, has detected the malware. However, Defender is not a reliable thing - it is prone to malfunction when it comes to malware removal. Getting the Trojan:Win32/Lockbit malware on your PC is an unpleasant thing, and removing it as soon as possible must be your primary task.
Operating System: Windows
Application Category: Ransomware