Trojan:Win32/Dropper is a type of malicious software that falls under the broader category of Trojans. As a virus analyst at Microsoft Defender Team, my analysis of this threat reveals that it operates as a delivery mechanism for various types of malware onto compromised systems. This particular Trojan is designed to appear harmless or even legitimate while carrying a malicious payload, often in the form of additional malware like ransomware, spyware, or keyloggers.
Trojan:Win32/Dropper typically employs sophisticated techniques to evade detection by security software, such as obfuscation, encryption, and exploiting vulnerabilities in the target system. It may exploit social engineering tactics to trick users into executing the malicious payload, which can be hidden within seemingly innocuous files or attachments. Once executed, the Trojan’s primary objective is to establish a foothold on the compromised system and provide a backdoor for remote attackers, enabling them to gain unauthorized access and carry out various malicious activities.
To combat Trojan:Win32/Dropper and its associated threats, continuous updates to security software signatures and heuristic algorithms are crucial. Employing behavior-based detection methods, sandboxing, and network traffic analysis can also aid in identifying and mitigating the impact of such Trojans.
What does the pop-up with Trojan:Win32/Dropper detection mean?
The Trojan:Win32/Dropper detection you can see in the lower right corner is demonstrated to you by Microsoft Defender. That anti-malware application is pretty good at scanning, but prone to be basically unreliable. It is defenseless to malware attacks, it has a glitchy interface and bugged malware clearing capabilities. Thus, the pop-up which says concerning the Dropper is simply an alert that Defender has detected it. To remove it, you will likely need to make use of a separate anti-malware program.
The exact Trojan:Win32/Dropper virus is a really undesirable thing. It digs into your computer under the guise of something normal, or as a piece of the application you downloaded at a forum. After that, it makes everything to make your system weaker. At the end of this “party”, it injects other malicious things – ones which are wanted by crooks who control this malware. Hence, it is almost impossible to predict the effects from Dropper actions. And the unpredictability is one of the most upleasant things when it comes to malware. That’s why it is better not to choose at all, and don’t give it even a single chance to complete its task.
Threat Summary:
| Name | Dropper Trojan |
| Detection | Trojan:Win32/Dropper |
| Details | Dropper tool that looks legitimate but can take control of your computer. |
Is Trojan:Win32/Dropper dangerous?
As I have actually pointed out , non-harmful malware does not exist. And Trojan:Win32/Dropper is not an exception. This virus alters the system settings, edits the Group Policies and Windows registry. All of these components are crucial for correct system operating, even in case when we are not talking about Windows security. Therefore, the virus which Dropper carries, or which it will download later, will squeeze out maximum profit from you. Crooks can grab your personal data, and then push it at the black market. Using adware and browser hijacker functionality, embedded in Trojan:Win32/Dropper malware, they can make profit by showing you the banners. Each view gives them a penny, but 100 views per day = $1. 1000 victims who watch 100 banners per day – $1000. Easy math, but sad conclusions. It is a bad choice to be a donkey for crooks.
How did I get this virus?
It is difficult to line the origins of malware on your PC. Nowadays, things are mixed up, and spreading tactics utilized by adware 5 years ago may be utilized by spyware these days. However, if we abstract from the exact spreading way and will think of why it has success, the explanation will be very basic – low level of cybersecurity awareness. People click on promotions on strange sites, click the pop-ups they receive in their browsers, call the “Microsoft tech support” believing that the weird banner that says about malware is true. It is essential to recognize what is legitimate – to stay away from misconceptions when attempting to find out a virus.
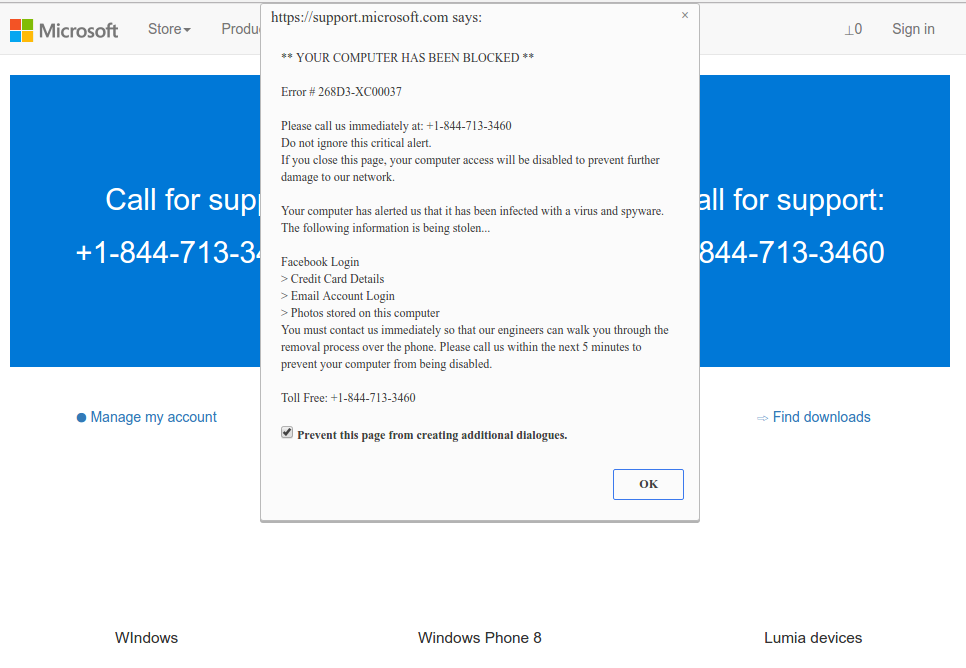
Microsoft Tech Support Scam
Nowadays, there are two of the most widespread tactics of malware distribution – lure emails and also injection into a hacked program. While the first one is not so easy to avoid – you need to know a lot to understand a counterfeit – the second one is very easy to handle: just do not utilize cracked apps. Torrent-trackers and other sources of “free” applications (which are, exactly, paid, but with a disabled license checking) are just a giveaway point of malware. And Trojan:Win32/Dropper is just within them.



Leave a Comment