Trojan.Clicker is a type of malicious software, specifically classified as a trojan, that is designed to generate fraudulent clicks or traffic on advertisements or websites. It operates stealthily in the background, often without the user’s knowledge, and performs automated clicks on various elements, such as banner ads, links, or buttons.
The primary purpose of Trojan.Clicker is to manipulate online advertising systems or affiliate programs to generate revenue for the attackers. By artificially inflating click counts or website visits, the attackers can profit from pay-per-click schemes or increase the visibility of certain websites for financial gain.
Trojan.Clicker infections can lead to financial losses for businesses relying on legitimate advertising, disrupt online marketing campaigns, and compromise the user’s privacy and security. Additionally, the presence of a Trojan.Clicker may indicate a compromised system that could be susceptible to further malware infections or unauthorized activities.
To protect against Trojan.Clicker and similar threats, it is important to maintain up-to-date security software, exercise caution when downloading files or clicking on suspicious links, and regularly scan your system for malware. Promptly removing any detected infections is crucial to safeguarding your computer and maintaining a secure online environment.
Most of the cases, Trojan.Clicker virus will certainly advise its targets to initiate funds move for the function of neutralizing the changes that the Trojan infection has actually introduced to the victim’s tool.
Trojan.Clicker Summary
These modifications can be as complies with:
- A process created a hidden window;
- Drops a binary and executes it;
- Installs itself for autorun at Windows startup;
- Creates a hidden or system file;
- Network activity detected but not expressed in API logs;
- Creates a copy of itself;
- Anomalous binary characteristics;
- Ciphering the papers located on the sufferer’s hard disk drive — so the sufferer can no more utilize the data;
- Preventing routine access to the victim’s workstation;
Related domains:
| z.whorecord.xyz | Ransom.Win32.Wacatac.sa |
| a.tomx.xyz | Ransom.Win32.Wacatac.sa |
Trojan.Clicker
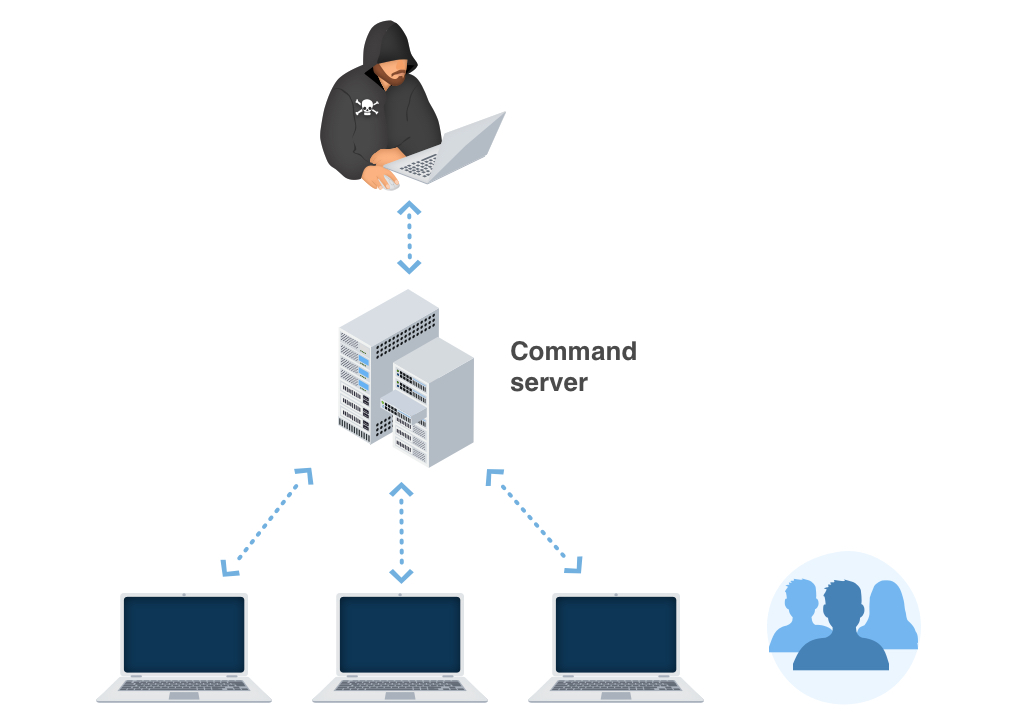
One of the most normal networks through which Trojan.Clicker Ransomware Trojans are infused are:
- By means of phishing emails;
- As a repercussion of individual winding up on a resource that organizes a malicious software program;
As quickly as the Trojan is successfully injected, it will either cipher the information on the sufferer’s computer or prevent the device from operating in a proper fashion – while likewise positioning a ransom note that mentions the need for the sufferers to impact the payment for the function of decrypting the papers or bring back the file system back to the first condition. In most instances, the ransom note will turn up when the client restarts the PC after the system has currently been harmed.
Trojan.Clicker circulation networks.
In numerous edges of the world, Trojan.Clicker expands by jumps and bounds. However, the ransom notes as well as techniques of extorting the ransom amount might vary depending on specific neighborhood (regional) setups. The ransom notes as well as methods of extorting the ransom amount may vary depending on certain local (local) settings.
For instance:
Faulty notifies about unlicensed software.
In certain areas, the Trojans frequently wrongfully report having actually spotted some unlicensed applications made it possible for on the target’s tool. The alert after that requires the individual to pay the ransom money.
Faulty declarations concerning prohibited web content.
In nations where software application piracy is much less popular, this technique is not as effective for the cyber fraudulences. Conversely, the Trojan.Clicker popup alert might incorrectly declare to be stemming from a law enforcement institution and will report having situated youngster porn or other unlawful data on the device.
Trojan.Clicker popup alert might falsely declare to be acquiring from a legislation enforcement institution as well as will report having located child pornography or other illegal data on the gadget. The alert will likewise include a requirement for the customer to pay the ransom.
Technical details
File Info:
crc32: 2D6B94EFmd5: 526700eb70652437a6e60283383e57f0name: 526700EB70652437A6E60283383E57F0.mlwsha1: 514d7ea9c0f7878df168767c195ac6cd32c2078fsha256: 1f999b3a4e3e0e34db3525ec4fc2ac849076670b716328add1000571a7c8fa11sha512: c8044ec03f244caff5e8058aa0bc21b3382571eabdb69e9f9d402ffa8b27b7b949cec067f99ebd5d83412913f034f9474f6619892e20356f620b86c736679e66ssdeep: 192:fHqT0FreBhcRMqOa5GlqyL1TTQotcx9PRTwGCcHEOvsKyBg:PSo41TTQQGCZOxyBgtype: PE32 executable (console) Intel 80386 (stripped to external PDB), for MS WindowsVersion Info:
0: [No Data]
Trojan.Clicker also known as:
| K7AntiVirus | Spyware ( 0058a6bf1 ) |
| Lionic | Trojan.Win32.Generic.4!c |
| DrWeb | Trojan.MulDrop18.54292 |
| Cynet | Malicious (score: 100) |
| Cylance | Unsafe |
| Zillya | Trojan.Agent.Win32.2557322 |
| Sangfor | Suspicious.Win32.Save.a |
| CrowdStrike | win/malicious_confidence_80% (W) |
| Alibaba | TrojanClicker:Win32/MalwareX.cd194b11 |
| K7GW | Spyware ( 0058a6bf1 ) |
| Cybereason | malicious.9c0f78 |
| Symantec | ML.Attribute.HighConfidence |
| ESET-NOD32 | a variant of Win32/TrojanClicker.Agent.OAW |
| APEX | Malicious |
| Avast | Win32:MalwareX-gen [Trj] |
| Kaspersky | UDS:Trojan.Win32.Generic |
| Tencent | Malware.Win32.Gencirc.11d7cb42 |
| Sophos | Mal/Generic-S |
| BitDefenderTheta | Gen:NN.ZexaF.34294.aCW@aS0amEd |
| McAfee-GW-Edition | Artemis!Trojan |
| FireEye | Generic.mg.526700eb70652437 |
| SentinelOne | Static AI – Malicious PE |
| Jiangmin | Trojan.Generic.hdoso |
| Avira | TR/Clicker.lstbg |
| Antiy-AVL | Trojan/Generic.ASMalwS.34CFA01 |
| Microsoft | Trojan:Win32/Wacatac.B!ml |
| Gridinsoft | Ransom.Win32.Wacatac.sa |
| GData | Win32.Trojan.Agent.IZTO7N |
| AhnLab-V3 | Trojan/Win.Clicker.C4773462 |
| McAfee | GenericRXQO-MV!526700EB7065 |
| VBA32 | Trojan.Wacatac |
| Malwarebytes | Trojan.Clicker |
| Panda | Trj/GdSda.A |
| TrendMicro-HouseCall | TROJ_GEN.R002H0CKI21 |
| Yandex | Trojan.Agent!wS7tzt+ir4E |
| Ikarus | Trojan.Win32.TrojanClicker |
| Fortinet | W32/TrojanClicker_Agent.OAW!tr |
| AVG | Win32:MalwareX-gen [Trj] |
| Paloalto | generic.ml |
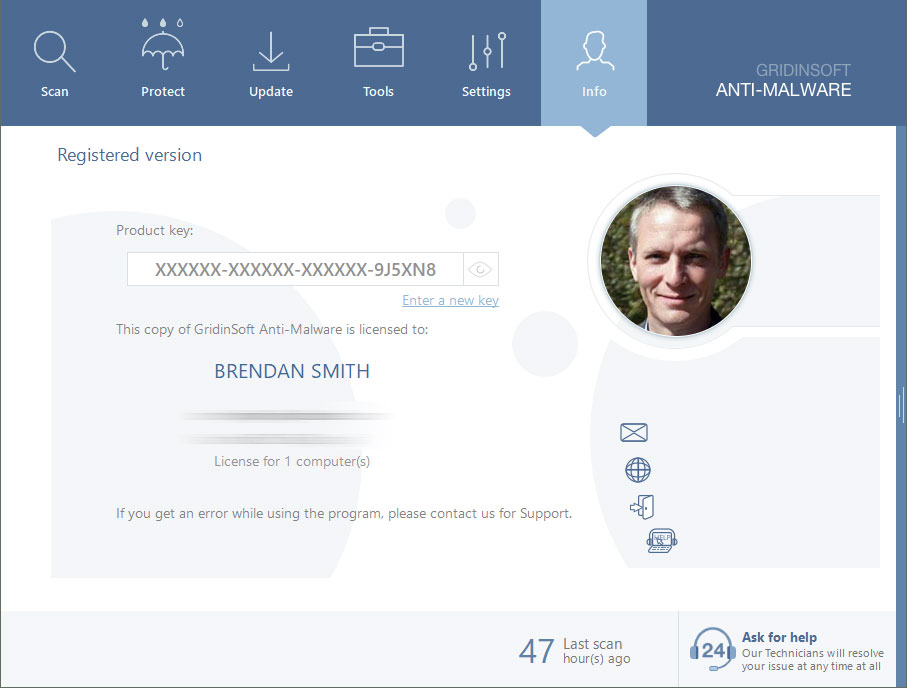
How to remove Trojan.Clicker ransomware?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials, or crypt your documents for ransom.
Reasons why I would recommend GridinSoft1
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

Are Your Protected?
If the guide doesn’t help you to remove Trojan.Clicker you can always ask me in the comments for getting help.


Leave a Comment