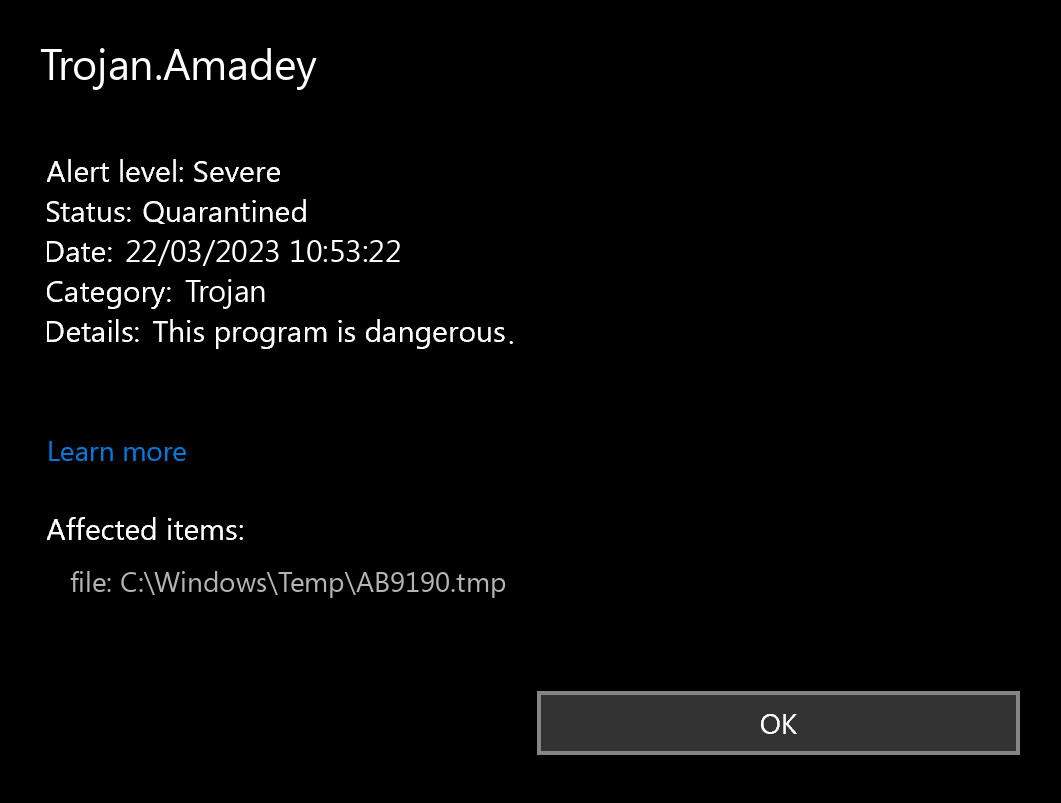
If you spectate the alert of Trojan.Amadey detection, it seems that your system has a problem. All viruses are dangerous, without any deviations. Amadey is a malware that aims at opening your system to further malware injection. Most of of the modern malware samples are complex, and can inject other viruses. Getting the Trojan.Amadey malware often means getting a thing which can act like spyware or stealer, downloader, and a backdoor. Seeing this detection means that you must to perform the removal as fast as you can.
What does the notification with Trojan.Amadey detection mean?
The Trojan.Amadey detection you can see in the lower right corner is shown to you by Microsoft Defender. That anti-malware software is quite OK at scanning, however, prone to be generally unreliable. It is unprotected to malware attacks, it has a glitchy user interface and bugged malware removal features. Hence, the pop-up which says about the Amadey is just a notification that Defender has spotted it. To remove it, you will likely need to use another anti-malware program.
The exact Trojan.Amadey infection is a very undesirable thing. It digs into your system disguised as a part of something legit, or as a part of the tool you have got on a forum. After that, it makes everything to weaken your system. At the end of this “party”, it injects other malicious things – ones which are choosen by cybercriminals who manage this malware. Hence, it is likely impossible to predict the effects from Amadey actions. And the unpredictability is one of the baddest things when it comes to malware. That’s why it is rather not to choose at all, and don’t let the malware to complete its task.
Threat Summary:
| Name | Amadey Trojan |
| Detection | Trojan.Amadey |
| Details | Amadey tool that looks legitimate but can take control of your computer. |
Is Trojan.Amadey dangerous?
As I have actually pointed out before, non-harmful malware does not exist. And Trojan.Amadey is not an exclusion. This virus modifies the system configurations, edits the Group Policies and registry. All of these elements are vital for correct system operating, even when we are not talking about system safety. Therefore, the virus which Amadey contains, or which it will inject after some time, will squeeze out maximum revenue from you. Cyber burglars can steal your personal data, and then sell it at the black market. Using adware and browser hijacker functions, embedded in Trojan.Amadey virus, they can make profit by showing you the banners. Each view gives them a penny, but 100 views per day = $1. 1000 victims who watch 100 banners per day – $1000. Easy math, but sad conclusions. It is a bad choice to be a donkey for crooks.
How did I get this virus?
It is difficult to line the origins of malware on your PC. Nowadays, things are mixed up, and distribution tactics chosen by adware 5 years ago may be used by spyware nowadays. However, if we abstract from the exact distribution method and will think of why it works, the answer will be pretty simple – low level of cybersecurity understanding. Individuals click on advertisements on odd sites, open the pop-ups they get in their web browsers, call the “Microsoft tech support” thinking that the odd banner that states about malware is true. It is necessary to understand what is legitimate – to stay away from misconceptions when attempting to determine a virus.
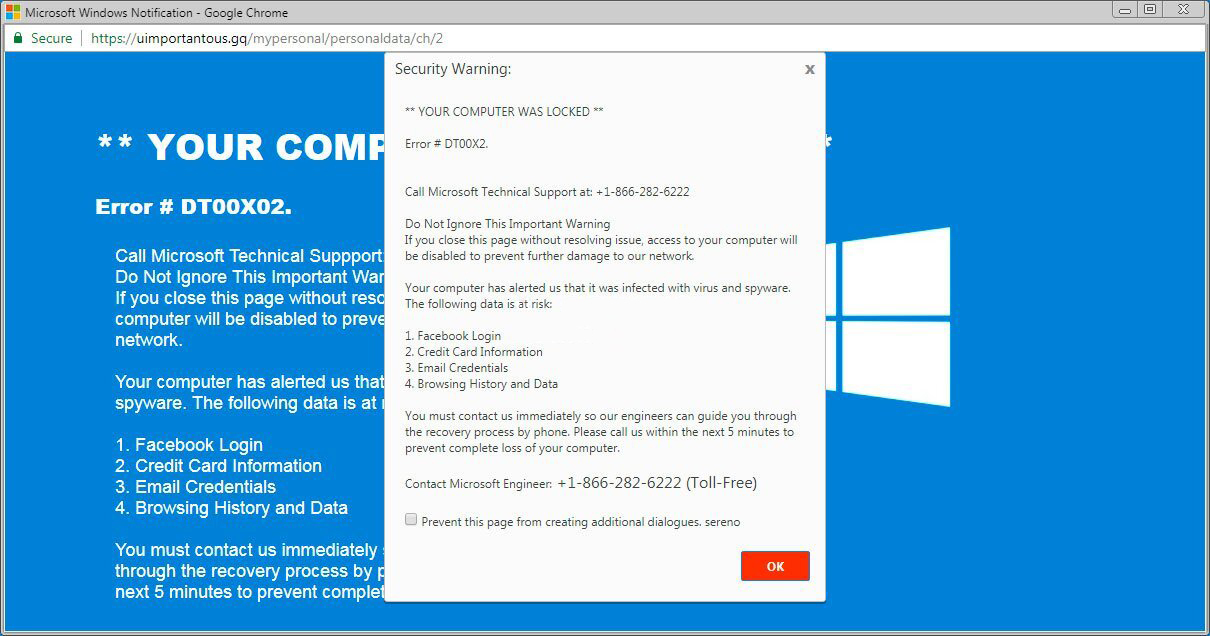
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most widespread methods of malware distribution – lure emails and also injection into a hacked program. While the first one is not so easy to evade – you should know a lot to understand a fake – the second one is easy to get rid of: just don’t utilize hacked apps. Torrent-trackers and various other sources of “totally free” applications (which are, actually, paid, but with a disabled license checking) are really a giveaway place of malware. And Trojan.Amadey is simply amongst them.


I love the article, very thorough and enlightening; however, I have a debian machine and I had VirusTotal CLI scan of my ip address and it gave me the name of this trojan. But no one seems to know how to remove it from a linux machine, your help would be greatly appreciated.