temp.exe is a Trojan Coin Miner that uses the contaminated computer system’s sources to mine digital money without your approval. It can be Monero, Bitcoin, DarkCoin or Ethereum.
About “temp.exe”
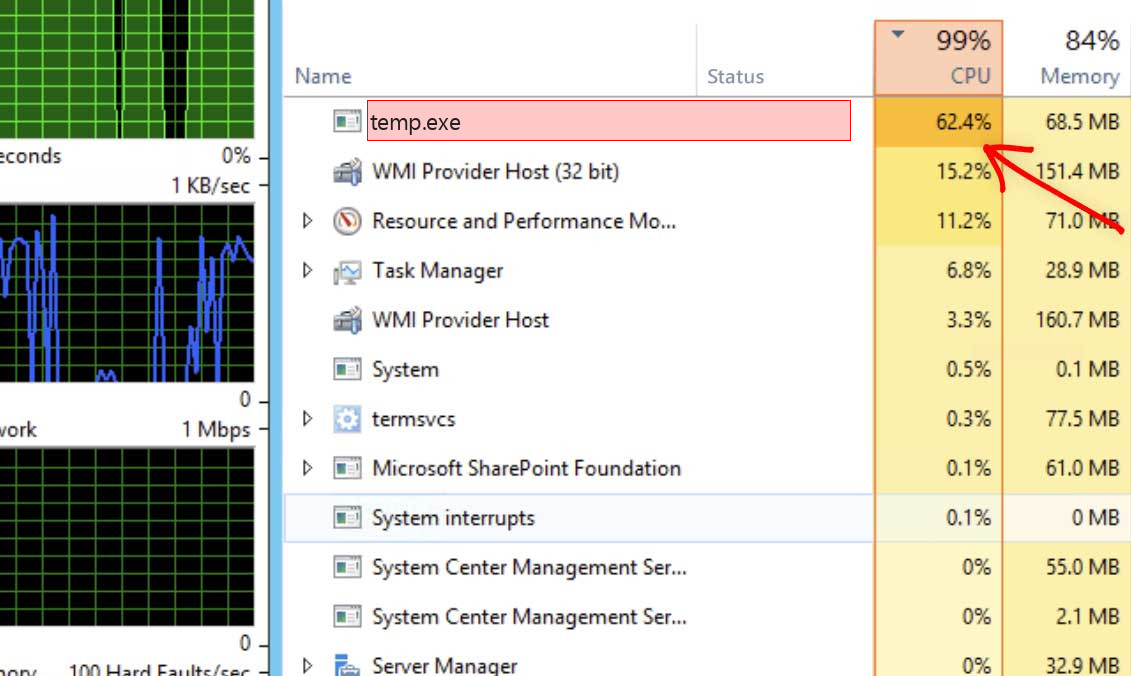
temp.exe will certainly utilize greater than 70% of your CPU’s power and also graphics cards sources
What this indicates, is that when the miners are running you will certainly find that your computer system is running slower and also video games are stammering or freezing because the temp.exe is using your computer’s sources to create income for themselves. This will trigger your CPU to perform at very hot temperature levels for extended amount of times, which can reduce the life of the CPU.
temp.exe Technical Summary.
| File Name | temp.exe |
| Type | Trojan Coin Miner |
| Detection Name | Trojan:Win32/CoinMiner |
| Distribution Method | Software bundling, Intrusive advertisement, redirects to shady sites etc. |
| Similar behavior | Ss, Spoolsv, Taskhost |
| Removal | Download and install GridinSoft Anti-Malware for automatic temp.exe removal. |
Besides slowing down your computer, going for peek level for very long times might create damages to your maker as well as increase power expenses.
When a computer is infected with temp.exe trojan, typical symptoms consist of:
- Really high CPU and graphics cards use
- Windows decrease and also make best use of slowly, and also programs run slower.
- Programs don’t release as quickly.
- General slowness when using the computer.
How to detect temp.exe Coin Miner Trojan?
Unlike ransomware, cryptocurrencies mining threats are not obtrusive and also are most likely to continue to be unnoticed by the victim.
Spotting temp.exe threat is reasonably simple. If the target is making use of a GridinSoft Anti-Malware it is virtually particular to detect any type of mining malware. Even without a safety solution, the victim is most likely to believe there is something incorrect due to the fact that mining bitcoin or various other cryptocurrencies is a really resource intensive process. The most common symptom is an obvious and typically consistent decrease in performance.
This symptom alone doesn’t tell the victim what the specific trouble is. The individual can experience comparable concerns for a selection of reasons. Still, temp.exe malware can be really disruptive due to the fact that it will hog all offered computer power and also the sudden change in the means the contaminated gadget does is likely to make the sufferer try to find remedies. If the hardware of the affected device is powerful sufficient, and the target does not find as well as remove the threat quickly, the power consumption as well as as a result the electricity expense will certainly go up visibly too.
Exactly how to Remove temp.exe Malware?
When the victim has identified that their problem is temp.exe danger, for the typical customer there are a number of solutions.
First and foremost use GridinSoft Anti-Malware would be the most effective remedy. There is no lack of offered cybersecurity software that will find and also eliminate mining malware.
Conversely, if the contaminated equipment does not consist of important information or the victim has actually backed up such data in a tidy place, as well as the customer has some experience, formatting the hard disks might work. This option might not suffice if the infection has penetrated one or more networks the device belongs of.
Download Removal Tool.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for temp.exe file and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.

If the guide doesn’t help you to remove temp.exe infection, please download the GridinSoft Anti-Malware that I recommended. Also, you can always ask me in the comments for getting help. Good luck!
User Review
( votes)References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison