The SettingsModifier:Win32/PossibleHostsFileHijack detection means a presence of a malicious program in your system. In particular, this one aims at changing your HOSTS file, so your browser will direct you to a different website.
The PossibleHostsFileHijack detection pretty much says for itself. It stands for a malware that changes system settings, particularly aiming for HOSTS file. The latter is a system-wide config file that is responsible for setting a specific IP address for the specific website. By modifying this file, hackers can make you see a phishing copy of the website even when you’re trying to open a genuine page.
Win32/PossibleHostsFileHijack Overview
“SettingsModifier:Win32/PossibleHostsFileHijack” is a designation employed by Microsoft Defender to identify a particular form of malware that alters the Windows Hosts file. The Hosts file serves the purpose of mapping hostnames to corresponding IP addresses.
When malware manipulates the HOSTS file, it has the capability to redirect your web traffic towards malicious websites or hinder your access to legitimate ones. This can give rise to various issues, such as phishing attacks, malware infections, and other potential security risks.
If Microsoft Defender has detected this threat on your PC, it is recommended that you take action immediately to remove it. You can start by following the instructions provided by Microsoft Defender to quarantine or remove the threat. Additionally, you should also consider running a full system scan with an updated antivirus or anti-malware tool to ensure that there are no other infections on your PC.
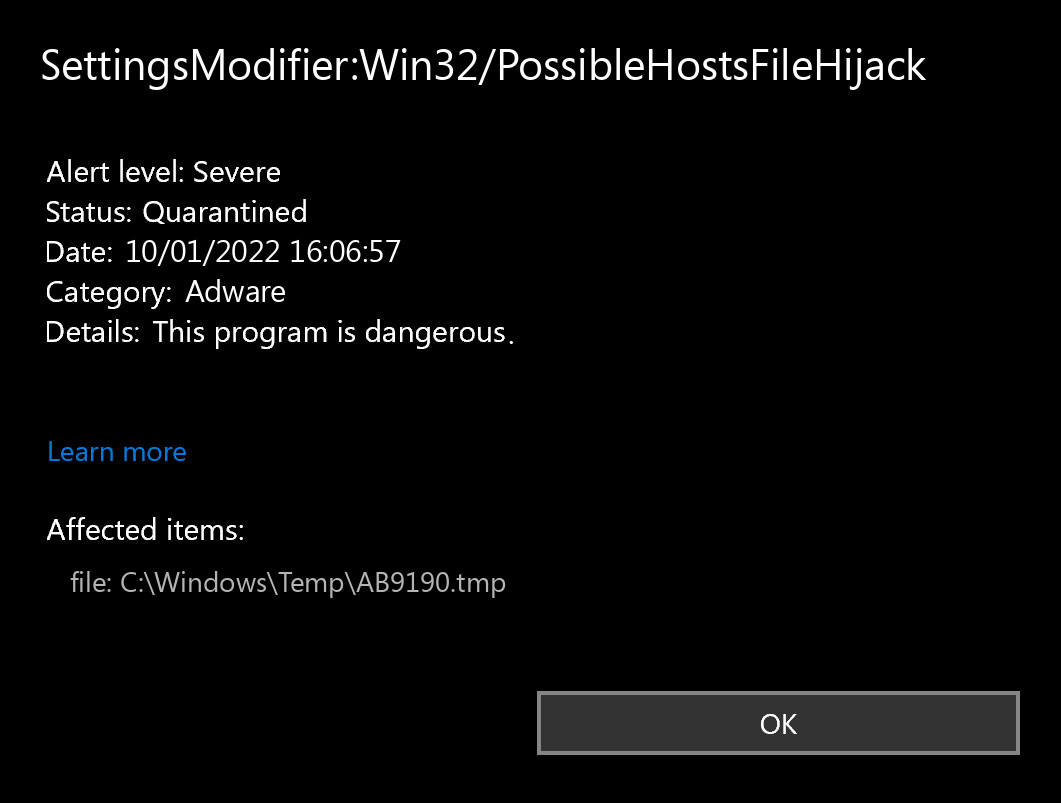
Microsoft Defender: “SettingsModifier:Win32/PossibleHostsFileHijack”
The exact SettingsModifier:Win32/PossibleHostsFileHijack virus is a very nasty thing. This malware demonstrates to you an extraordinary amount of commercials. Have you ever visited the doorway web pages? They are filled up only with banners – blinking, improperly designed, and with weird information. Threats does the identical thing to all sites you open. That virus brings profit to its developers in a really tricky way. You check the banners – they get money. Furthermore, these banners oftentimes contain fraudulent and sometimes shocking content. Penis enlargement, porn websites ads, Microsoft virus alerts – all these things are usual for such ads.
Threat Summary:
| Name | PossibleHostsFileHijack |
| Detection | SettingsModifier:Win32/PossibleHostsFileHijack |
| Damage | Display advertisements in the browser, which are not related to the sites the affected users are visiting. |
| Similar | Eakwhenspo Work Popup, Mydesktopdefence Removal, Trybellyfeilicia Best Removal, Imsemy, News Ficubo Cc, Watervery Work Removal, Checkthesafety, Arriedstro Work Removal |
| Fix Tool | See If Your System Has Been Affected by PossibleHostsFileHijack |
Is SettingsModifier:Win32/PossibleHostsFileHijack dangerous?
Virus like PossibleHostsFileHijack one is not something contrasty, compared to other advertising malware. However, as it was pointed out, the banners it demonstrates to you are quite often loaded with phony information. Even if you can distinguish fraud from ads – do you really like seeing ads for free? Specifically, ones that cover your web browser window and disturb you from your working process? It looks that we actually know the reply.
How did I get this virus?
It is hard to trace the sources of malware on your PC. Nowadays, things are mixed up, and spreading tactics chosen by adware 5 years ago may be used by spyware nowadays. However, if we abstract from the exact spreading method and will think of why it has success, the explanation will be really basic – low level of cybersecurity awareness. Individuals click on promotions on strange websites, open the pop-ups they get in their web browsers, and call “Microsoft tech support” thinking that the scary banner that says about malware is true. It is necessary to understand what is legitimate – to prevent misunderstandings when trying to identify a virus.
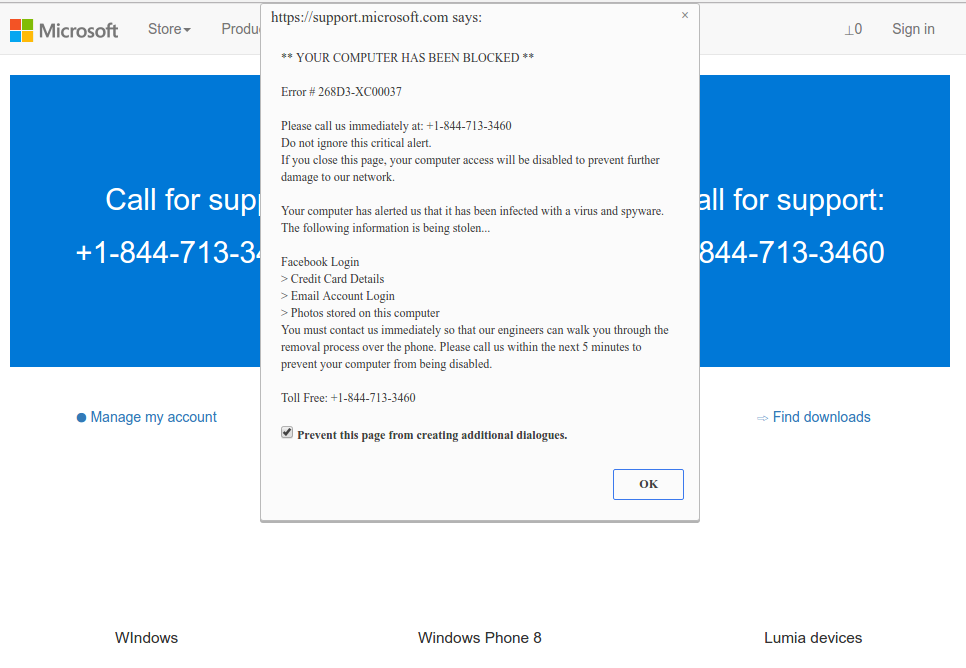
Microsoft Tech Support Scam
Nowadays, there are two of the most extensive tactics of malware spreading – lure emails and injection into a hacked program. While the first one is not so easy to evade – you should know a lot to recognize a fake – the second one is very easy to get rid of: just do not utilize cracked apps. Torrent trackers and other sources of “totally free” applications (which are, exactly, paid, but with a disabled license checking) are really a giveaway place of malware. And SettingsModifier:Win32/PossibleHostsFileHijack is simply among them.
How to remove the SettingsModifier:Win32/PossibleHostsFileHijack from my PC?
Virus like PossibleHostsFileHijack is quite easy to clear away by hand. However, it is not so easy to revert the system changes it did in the process of the activity. Because a lot of various system elements are touched, it is quite easy to miss something. That’s why I ‘d recommend you to utilize anti-malware program. My preference for adware clearing is GridinSoft Anti-Malware.
Remove SettingsModifier:Win32/PossibleHostsFileHijack with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common malware as shown from our tests with the software, and we assure you that it can remove SettingsModifier:Win32/PossibleHostsFileHijack as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “SettingsModifier:Win32/PossibleHostsFileHijack” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing SettingsModifier:Win32/PossibleHostsFileHijack and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
Reset Browser settings after the hijacker attack
Hijacker makes a lot to keep annoying you even after being removed from your computer. It distorts the browser configurations, so it will not work correctly. Until you reset it, of course. Each browser has its own way to restore the default settings. Here are the guides for the most popular ones:
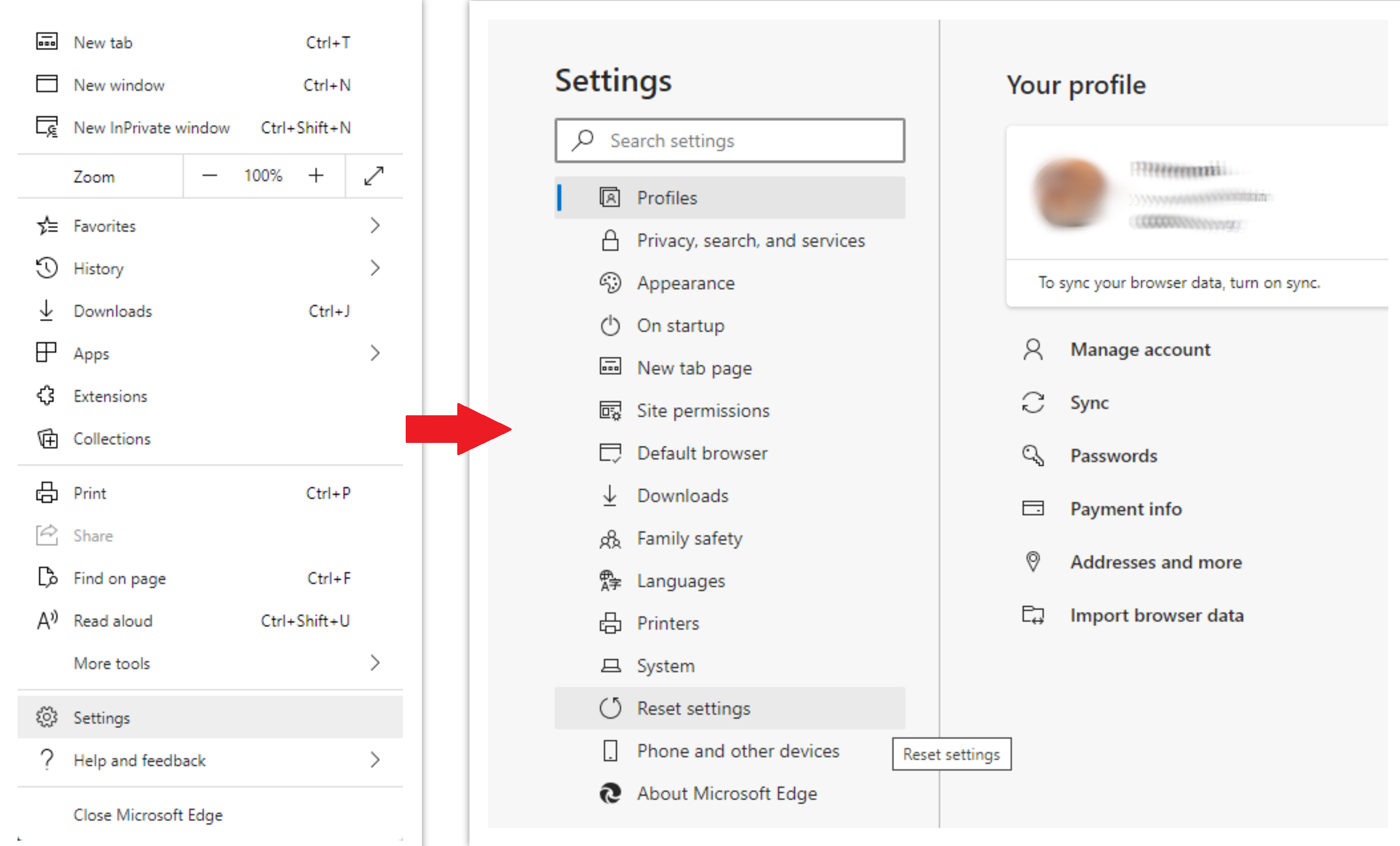
To reset Edge, do the following steps:
- Open the “Settings and more” tab in the upper right corner, then find here “Settings” button. In the appeared menu, choose “Reset settings” option :
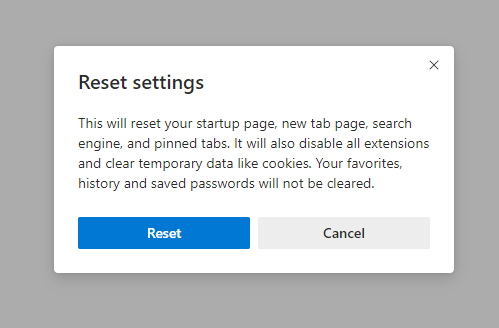
- After picking the Reset Settings option, you will see the following menu, stating about the settings which will be reverted to original :
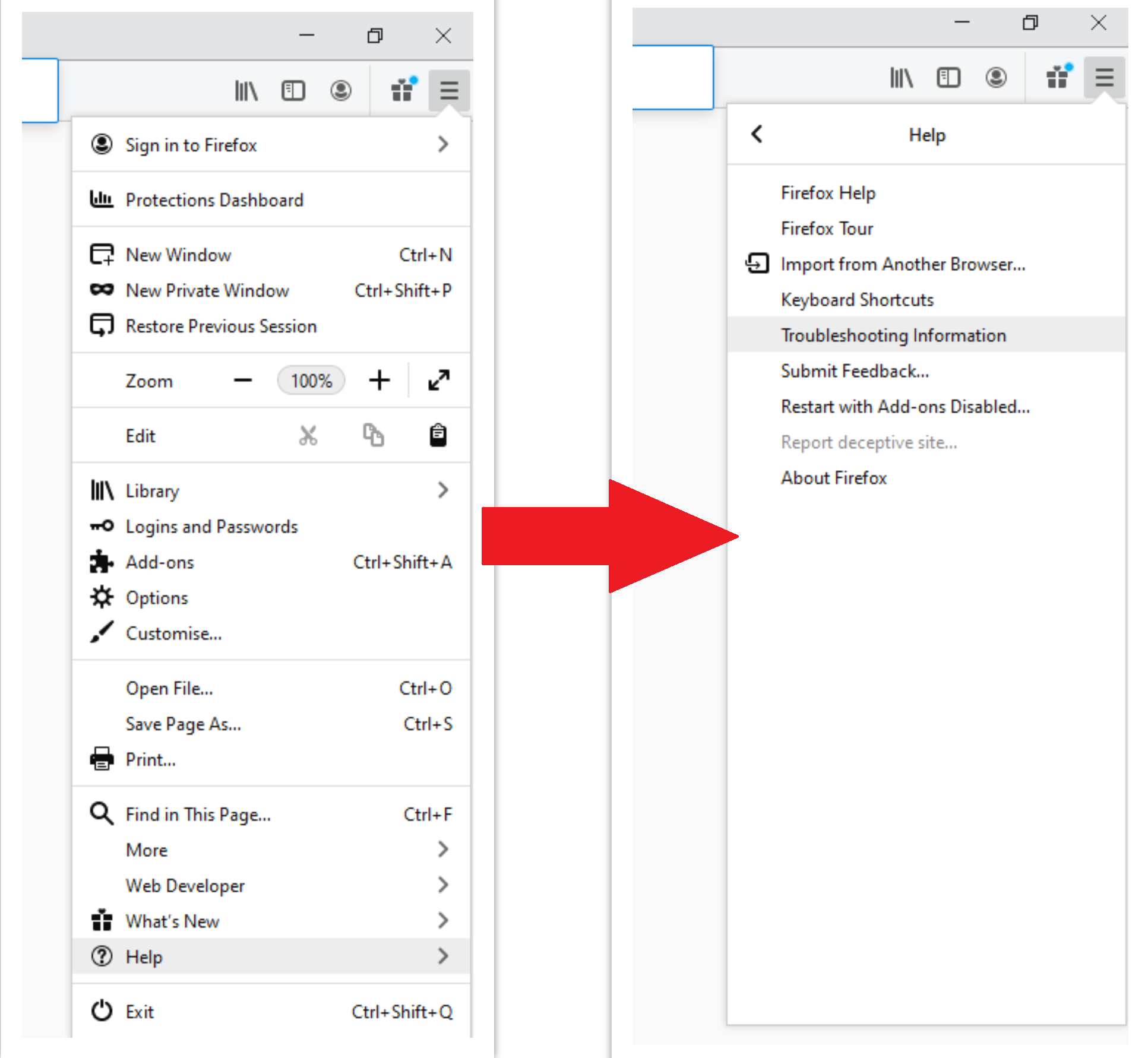
For Mozilla Firefox, do the next actions :
- Open Menu tab (three strips in upper right corner) and click the “Help” button. In the appeared menu choose “Troubleshooting information” :
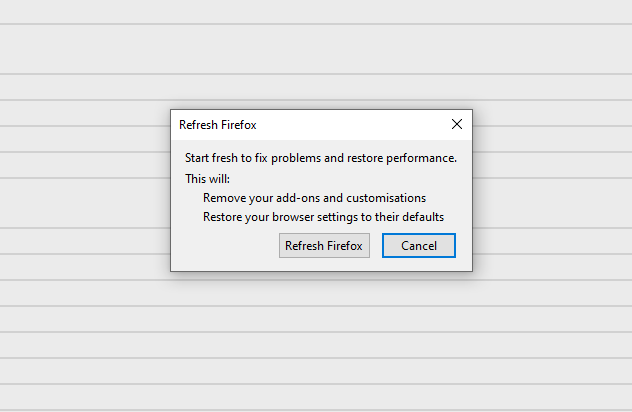
- In the next screen, find the “Refresh Firefox” option :
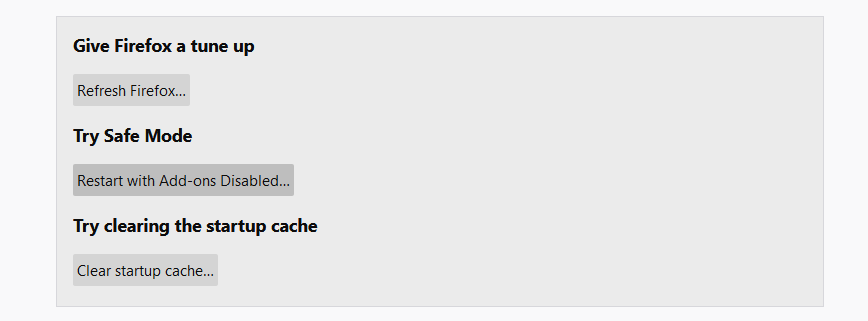
After choosing this option, you will see the next message :
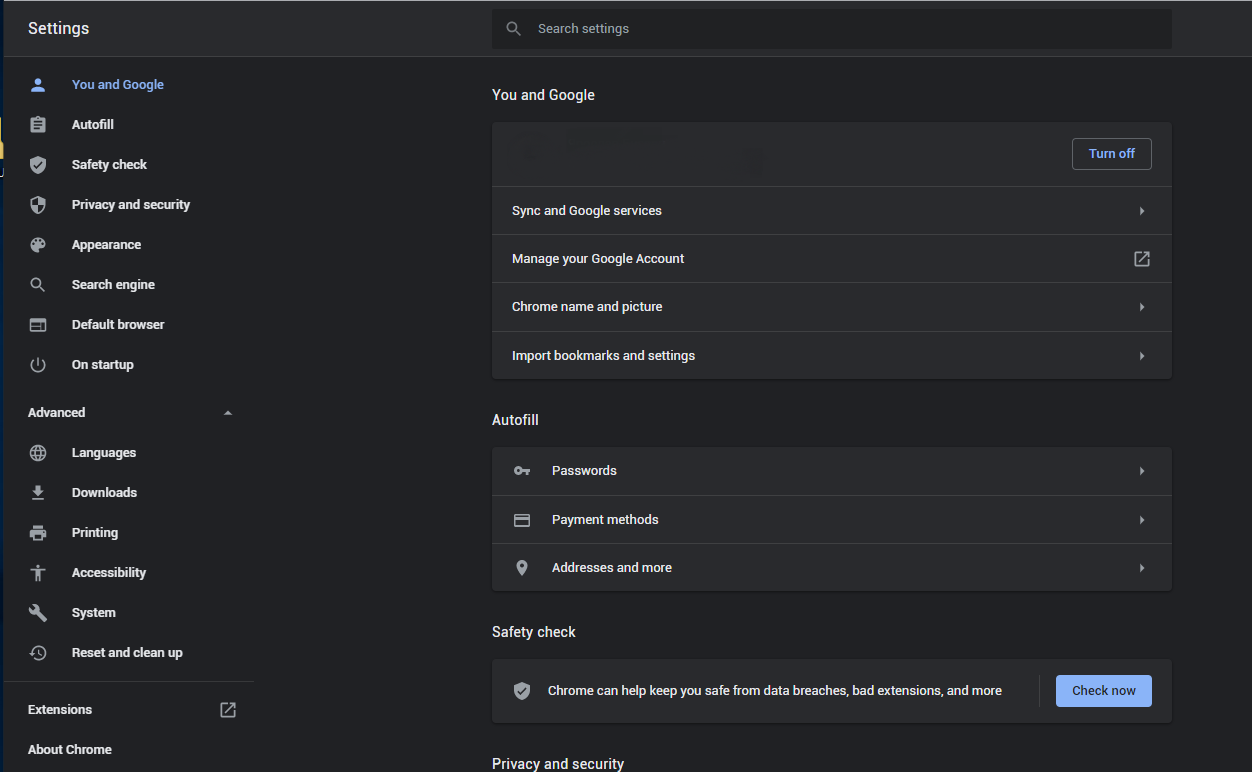
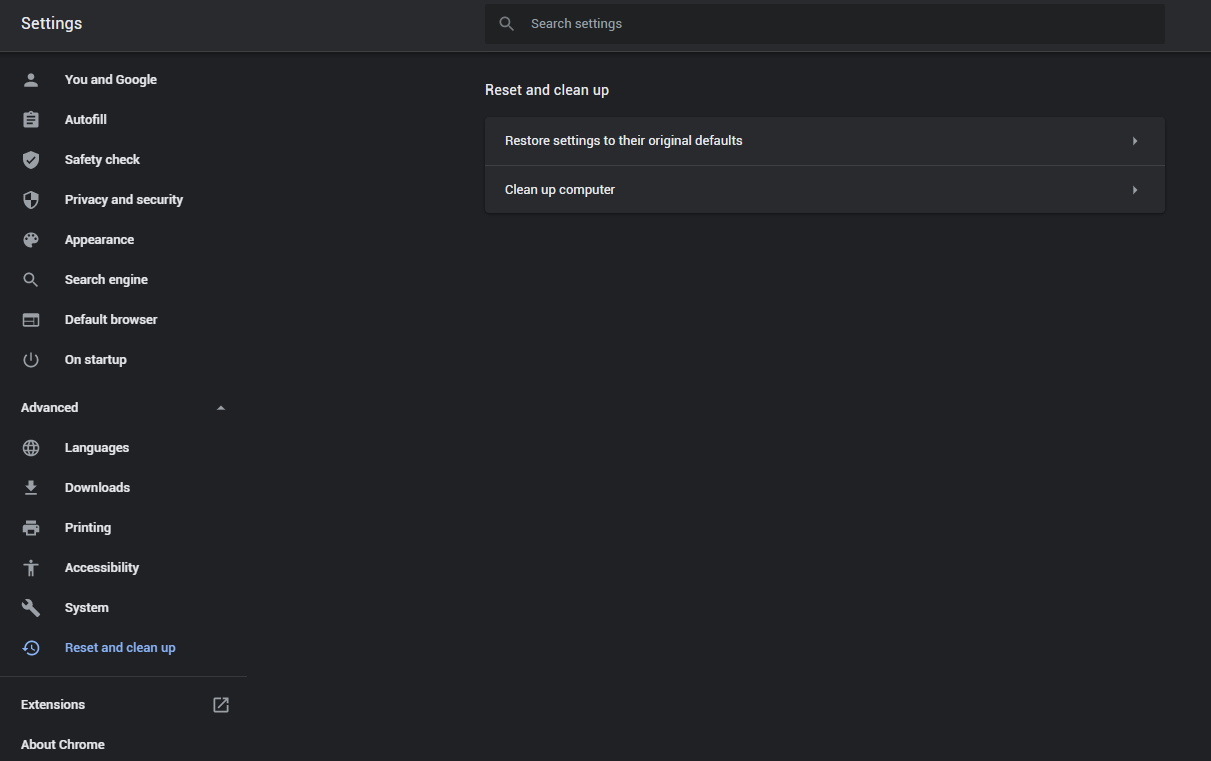
If you use Google Chrome
- Open Settings tab, find the “Advanced” button. In the extended tab choose the “Reset and clean up” button :
- In the appeared list, click on the “Restore settings to their original defaults” :
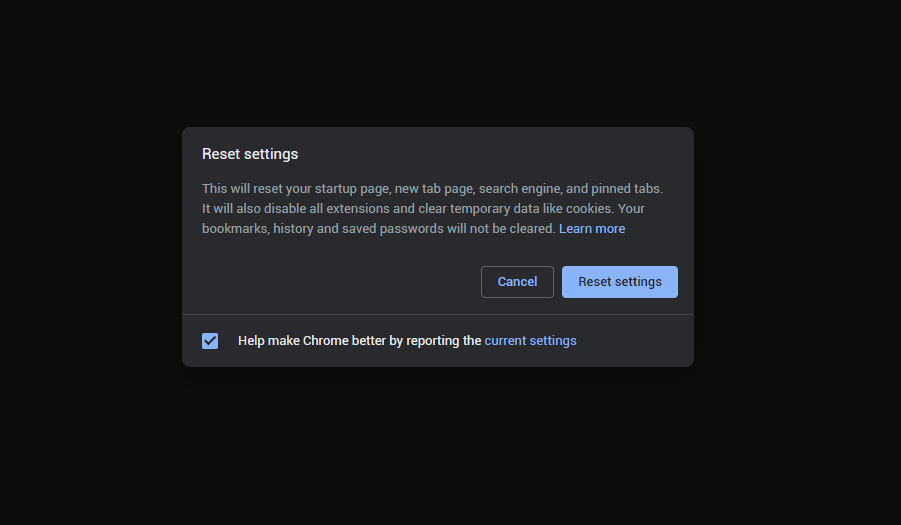
- Finally, you will see the window, where you can see all the settings which will be reset to default :
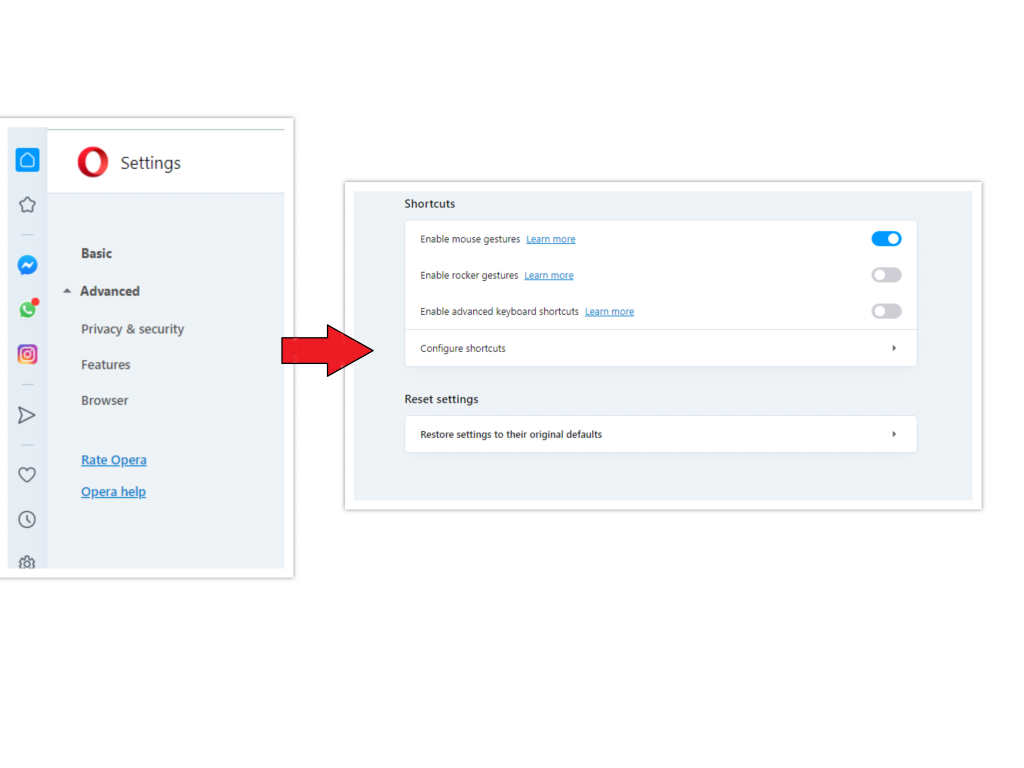
Opera can be reset in the next way
- Open Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click “Advanced” option, and choose “Browser” button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there “Restore settings to their original defaults” option :
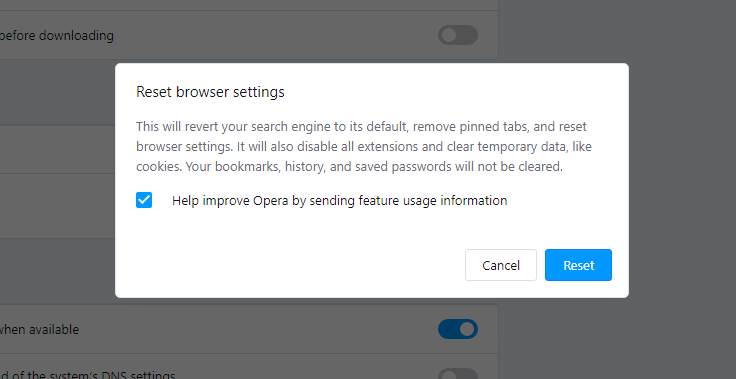
- After clicking the “Restore settings…” button, you will see the window, where all settings, which will be reset, are shown :
When the browsers are reset, you need to make sure that your browser will be connected the proper DNS while connecting to the web page you need. Make a text file named “hosts” on your desktop, after that open it and fill it with the following content1:
# Copyright (c) 1993-2006 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handle within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
Find the hosts.txt file in “C:/Windows/System32/drivers/etc” directory. Rename this file to “hosts.old.txt” (to distinguish it from the new one), and then move the file you created on the desktop to this folder. Remove the hosts.old from this folder. Now you have your hosts file as good as new.
Reset Browser settings with GridinSoft Anti-Malware
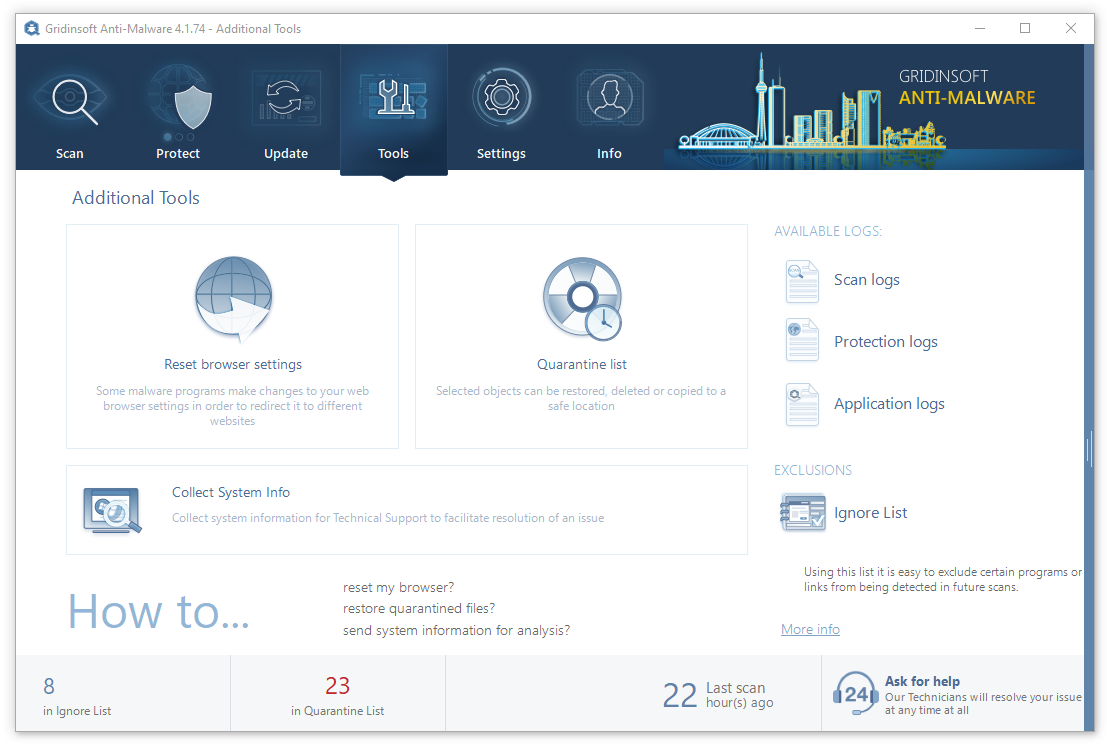
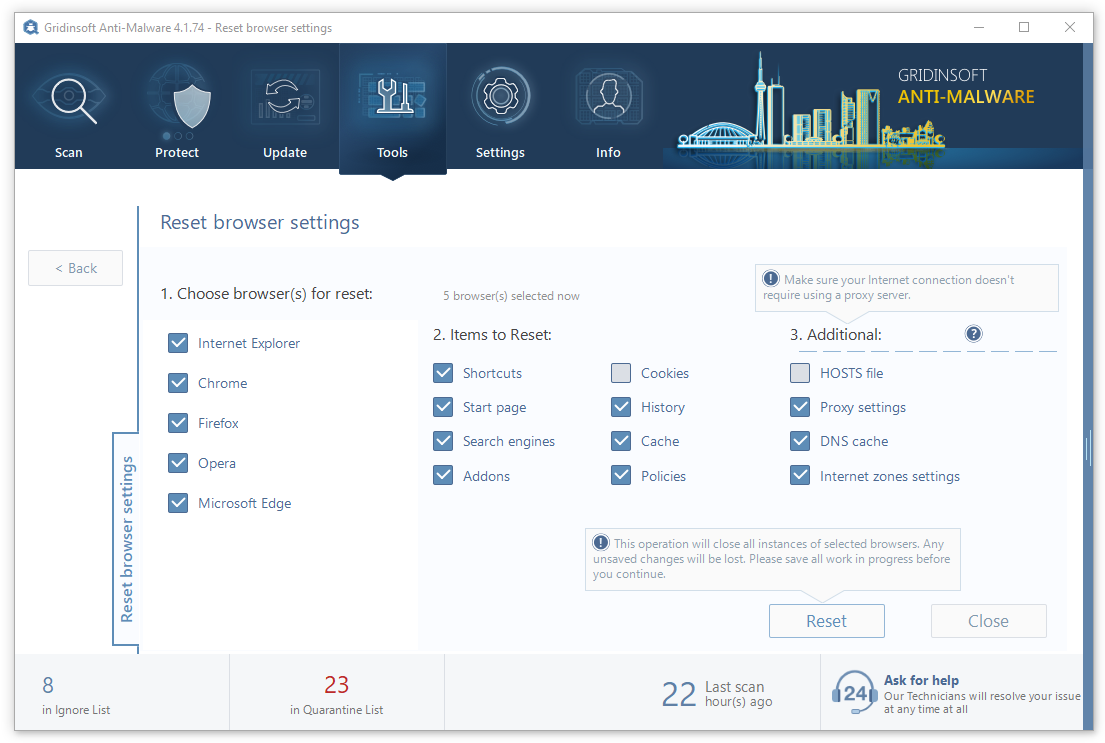
GridinSoft Anti-Malware offers its own way to reset browsers. With the help of this program, you can reset all your browsers in just several clicks. It also resets the HOSTS file automatically, so you don’t need to make any excessive actions. To reset your browser with GridinSoft Anti-Malware, open the Tools tab, and click the “Reset browser settings” button.
You can see the list of the options for each browser. By default, they are set up in the manner which fits the majority of users. Press the “Reset” button (lower right corner). In a minute your browser will be as good as new.
How to Remove SettingsModifier:Win32/PossibleHostsFileHijack Malware
Name: SettingsModifier:Win32/PossibleHostsFileHijack
Description: SettingsModifier:Win32/PossibleHostsFileHijack is a detection name used to identify a malicious utility that aims at changing the HOSTS file. It may appear as a part of a chain attack, and further steps will include throwing you to a phishing site or an exploit landing.
Operating System: Windows
Application Category: Adware
User Review
( votes)References
- Official Microsoft guide for hosts file reset.
