What is Ransom.MedusaReborn.J1 infection?
In this short article you will certainly find about the meaning of Ransom.MedusaReborn.J1 as well as its unfavorable impact on your computer. Such ransomware are a kind of malware that is clarified by online scams to demand paying the ransom money by a target.
Most of the instances, Ransom.MedusaReborn.J1 virus will certainly instruct its targets to start funds transfer for the function of neutralizing the amendments that the Trojan infection has actually introduced to the victim’s gadget.
Ransom.MedusaReborn.J1 Summary
These modifications can be as follows:
- Executable code extraction. Cybercriminals often use binary packers to hinder the malicious code from reverse-engineered by malware analysts. A packer is a tool that compresses, encrypts, and modifies a malicious file’s format. Sometimes packers can be used for legitimate ends, for example, to protect a program against cracking or copying.
- Creates RWX memory. There is a security trick with memory regions that allows an attacker to fill a buffer with a shellcode and then execute it. Filling a buffer with shellcode isn’t a big deal, it’s just data. The problem arises when the attacker is able to control the instruction pointer (EIP), usually by corrupting a function’s stack frame using a stack-based buffer overflow, and then changing the flow of execution by assigning this pointer to the address of the shellcode.
- Unconventionial language used in binary resources: Spanish (Colombia);
- The binary likely contains encrypted or compressed data. In this case, encryption is a way of hiding virus’ code from antiviruses and virus’ analysts.
- Collects information to fingerprint the system. There are behavioral human characteristics that can be used to digitally identify a person to grant access to systems, devices, or data. Unlike passwords and verification codes, fingerprints are fundamental parts of user’s identities. Among the threats blocked on biometric data processing and storage systems is spyware, the malware used in phishing attacks (mostly spyware downloaders and droppers), ransomware, and Banking Trojans as posing the greatest danger.
- Ciphering the papers found on the target’s disk drive — so the victim can no more use the data;
- Preventing routine access to the victim’s workstation. This is the typical behavior of a virus called locker. It blocks access to the computer until the victim pays the ransom.
Ransom.MedusaReborn.J1
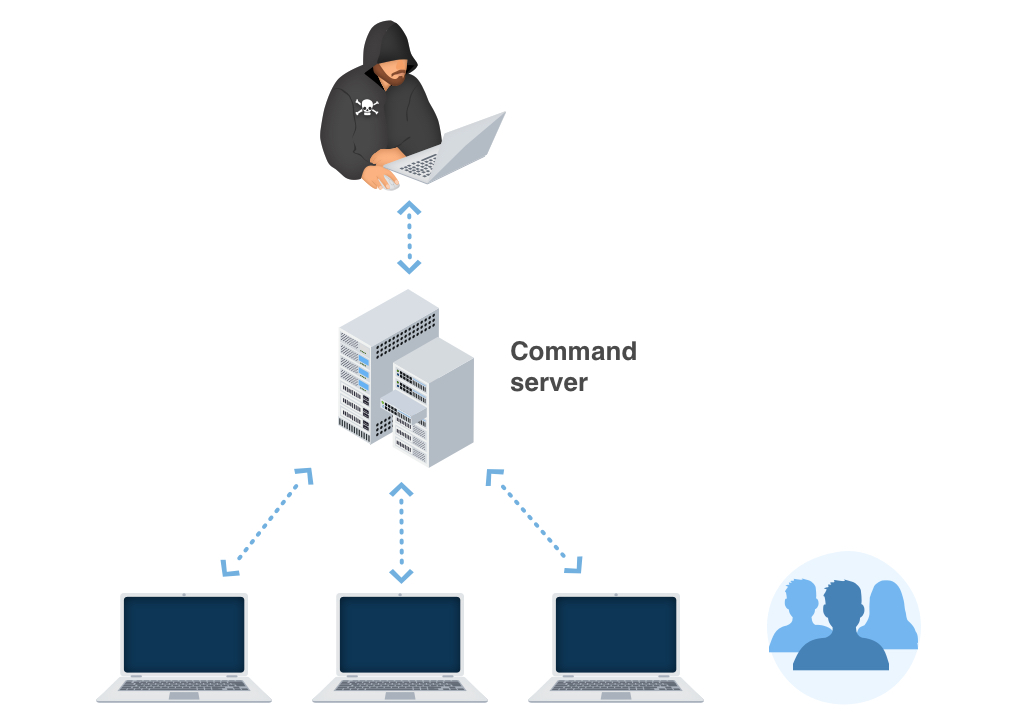
The most common networks where Ransom.MedusaReborn.J1 Trojans are infused are:
- By ways of phishing emails;
- As a repercussion of customer ending up on a resource that holds a malicious software application;
As soon as the Trojan is successfully infused, it will certainly either cipher the information on the victim’s PC or stop the gadget from working in a proper manner – while additionally positioning a ransom money note that discusses the requirement for the victims to impact the payment for the purpose of decrypting the files or restoring the file system back to the first condition. In most circumstances, the ransom money note will show up when the customer reboots the PC after the system has currently been harmed.
Ransom.MedusaReborn.J1 circulation networks.
In various corners of the globe, Ransom.MedusaReborn.J1 grows by jumps and bounds. However, the ransom money notes as well as methods of extorting the ransom money quantity might vary depending upon particular neighborhood (regional) setups. The ransom money notes as well as tricks of obtaining the ransom money amount may vary depending on particular regional (local) setups.
For instance:
Faulty alerts concerning unlicensed software program.
In particular locations, the Trojans commonly wrongfully report having actually discovered some unlicensed applications made it possible for on the target’s device. The alert then requires the customer to pay the ransom money.
Faulty statements regarding prohibited material.
In countries where software application piracy is less prominent, this technique is not as effective for the cyber fraudulences. Alternatively, the Ransom.MedusaReborn.J1 popup alert might incorrectly assert to be originating from a law enforcement establishment and also will report having situated youngster porn or various other illegal information on the tool.
Ransom.MedusaReborn.J1 popup alert may wrongly claim to be obtaining from a law enforcement establishment and will certainly report having located kid pornography or various other illegal information on the device. The alert will in a similar way consist of a demand for the individual to pay the ransom money.
Technical details
File Info:
crc32: FA87F27Amd5: 2052ca78f63f2352651cb345693fbba6name: 2052CA78F63F2352651CB345693FBBA6.mlwsha1: 67a75ef1f57d1e81f68870450fe6fb70df8c49f3sha256: 838b40ed5d99ffbbbc9e90b3f6a76aca8bea7899de70a6a2f791dbed49798a27sha512: 29d947bc8cee4a1b141ef401ae66ba95098d861a036f9c267bed574599ff989efe289e76e50be7d33482a7f9b6aedec5979f431e032d28f96b119ae7ea5d5198ssdeep: 12288:gBnLaxvVTYc3NzEKGRKHYW/kPvx5OQm1OFd:E0tTYc9zEdjHPvx5OWdtype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
ProductVersus: 1.5.8.28FileVerus: 1.0.2.27Translations: 0x0126 0x0226
Ransom.MedusaReborn.J1 also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Bkav | W32.AIDetect.malware2 |
| Elastic | malicious (high confidence) |
| CAT-QuickHeal | Ransom.MedusaReborn.J1 |
| Cylance | Unsafe |
| Sangfor | Trojan.Win32.Save.a |
| CrowdStrike | win/malicious_confidence_100% (D) |
| BitDefender | Gen:Variant.Babar.25502 |
| APEX | Malicious |
| Cynet | Malicious (score: 100) |
| MicroWorld-eScan | Gen:Variant.Babar.25502 |
| Sophos | ML/PE-A |
| BitDefenderTheta | Gen:NN.ZexaF.34628.GuW@ayZccMR |
| McAfee-GW-Edition | BehavesLike.Win32.Generic.hc |
| FireEye | Generic.mg.2052ca78f63f2352 |
| SentinelOne | Static AI – Malicious PE |
| Microsoft | Trojan:Win32/Wacatac.B!ml |
| GData | Gen:Variant.Babar.25502 |
| Acronis | suspicious |
| McAfee | Packed-GDK!2052CA78F63F |
| Malwarebytes | Trojan.MalPack.GS |
| Rising | Malware.Heuristic!ET#92% (RDMK:cmRtazo8WJMxrcBbbA9c9lHJisTo) |
| Qihoo-360 | HEUR/QVM10.1.FEDB.Malware.Gen |
How to remove Ransom.MedusaReborn.J1 ransomware?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials, or crypt your documents for ransom.
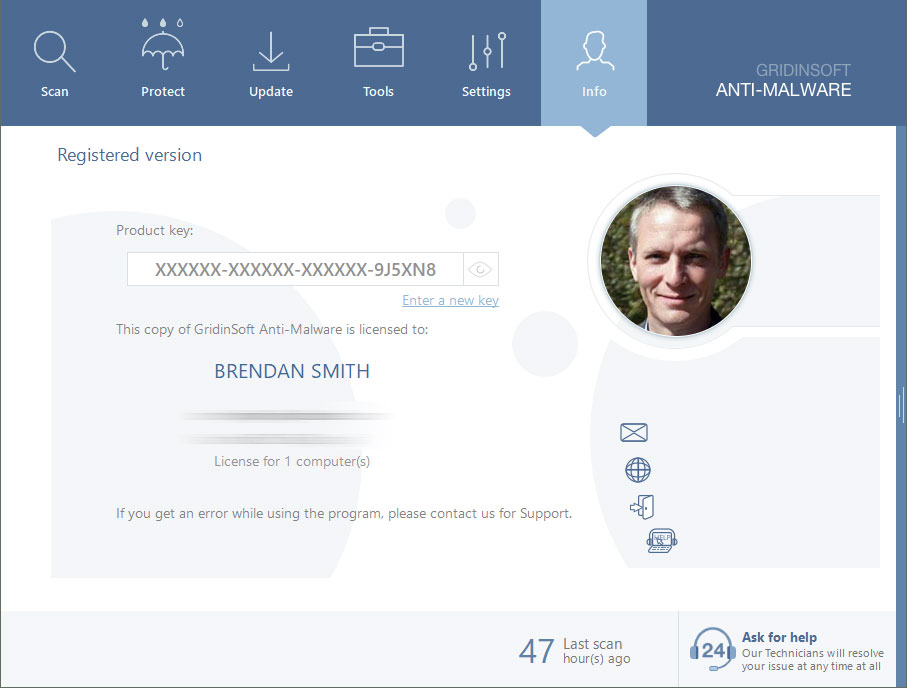
Reasons why I would recommend GridinSoft1
There is no better way to recognize, remove and prevent PC threats than to use an anti-malware software from GridinSoft2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Ransom.MedusaReborn.J1 files and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.

Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
If the guide doesn’t help you to remove Ransom.MedusaReborn.J1 you can always ask me in the comments for getting help.
User Review
( votes)References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison