The PUAMiner:Win64/CpuMulti detection means that your PC has a problem. Giving it a go may end up with really bad consequences. CpuMulti can make your system slower, and even lead to hardware malfunction.
PUAMiner:Win64/CpuMulti Detection Overview
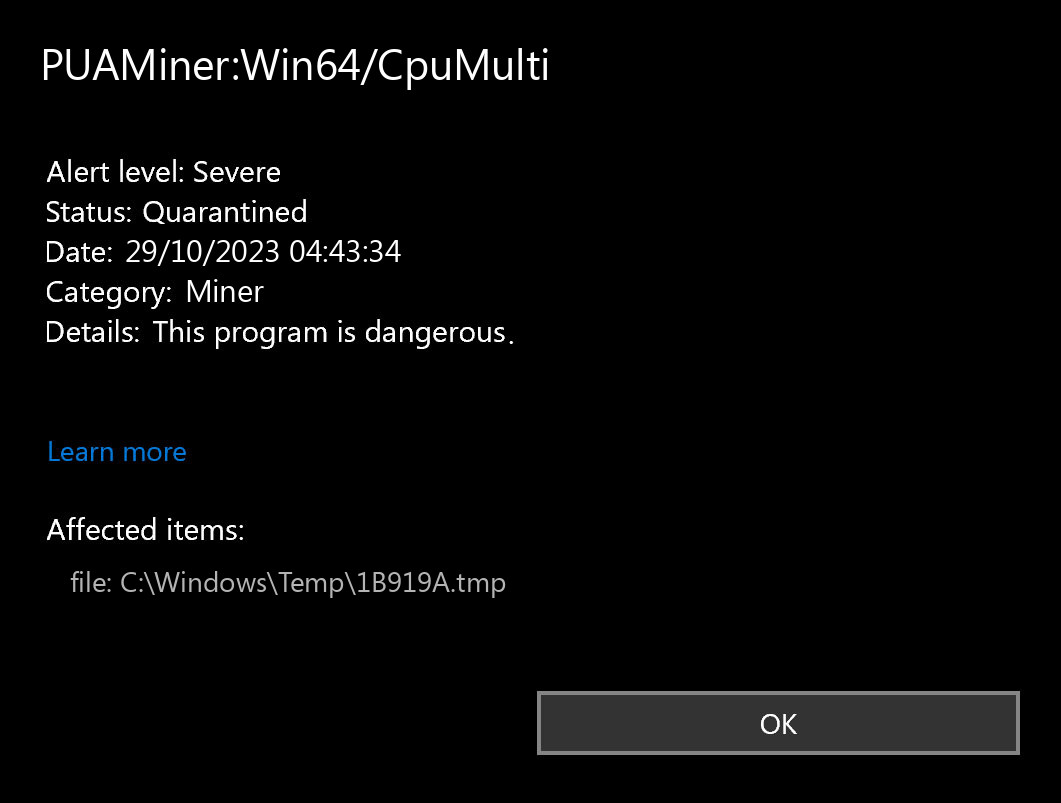
The PUAMiner:Win64/CpuMulti detection you can see in the lower right corner is demonstrated to you by Microsoft Defender. That anti-malware application is good at scanning, but prone to be mainly unreliable. It is unprotected to malware attacks, it has a glitchy user interface and bugged malware removal capabilities. Therefore, the pop-up which says concerning the CpuMulti is simply a notification that Defender has detected it. To remove it, you will likely need to use another anti-malware program.
The exact PUAMiner:Win64/CpuMulti virus is a really unpleasant thing. It uses your CPU and GPU to mine cryptocurrencies. This procedure needs a great computing power, and is generally conducted on specialized system configurations – so-called mining systems. Carrying out this job on an ordinary PC results in the inability even to start the internet browser. High CPU load – almost 80-90% – is among the typical symptoms of coin miner activity. System overloading result in a lot faster hardware wear, as well as potential malfunction of some of the components.
Coin Miner Summary:
| Name | CpuMulti Miner |
| Detection | PUAMiner:Win64/CpuMulti |
| Damage | Exploits your hardware to mine cryptocurrencies without your permission. |
Shortly about cryptocurrency mining
Lots of people think about crypto mining simply as a way of producing new coins. Crypto mining, however, additionally involves validating cryptocurrency operations on a blockchain network and adding them to a distributed journal. Most notably, crypto mining stops the double-spending of digital currency on a distributed network. Since distributed journals lack a centralized authority, the mining procedure is important for validating deals. Miners are, for that reason, incentivized to secure the network by participating in the operation verification procedure that boosts their chances of winning newly minted coins1.
Is PUAMiner:Win64/CpuMulti dangerous?
As I have stated previously, non-harmful malware does not exist. And PUAMiner:Win64/CpuMulti is not an exception. CpuMulti virus will certainly make your system slow, and likewise it will set your hardware at a risk. When it performs at such a high load, it can be affected because of overheating. Additionally, GPU wear out in the process of mining is several percent each week2. Giving the miner the option to work is not just about shedding the ability to operate as usual. This malware literally “thieves” the lifespan of your hardware.
Furthermore, several of the modern-day coin miner variations include spyware within. It is able not only to mine cryptocurrencies on your computer but additionally to grab all information about you and your system. And there is no chance to realise if the miner you have has an included spyware. The fact that NAME was found undoubtedly points out that you need to remove it immediately.
References
- Read more about cryptocurrency mining.
- Cryptocurrency mining wears you GPU pretty fast – the real-world tests approve that fact.


Leave a Comment