Microsoft products are one of the most exploitable things that are currently available on the software market. People who use it constantly not only meet different bugs, but also risk getting their systems infected through the vulnerabilities. MS Exchange Server – a quite popular mail server – is full of such security breaches.
Is it really so bad?
In March 2021, Microsoft reported about four Exchange Server vulnerabilities that were used to perform the cyberattack. In fact, those security breaches can easily be used to steal the email (that can easily contain sensitive information), and inject various other malware. Here is the list of those exploits:
This bulk of vulnerabilities is called “ProxyLogon”. It was used by the Chinese government-backed hacker groups that were aiming at corporate espionage – reading the emails, harvesting the credentials and even collecting the personal information about employees. In process of these attacks, hackers used the following web shells:
Is it possible to avoid the exploitation of these vulnerabilities?
Sure, all of these viruses are already added to the detection databases of Microsoft Defender. Last one got a very big update in Windows 11, so its detection capabilities rose significantly. It will be extremely attentive with exploitable apps, and Exchange is just one of them. Along with updating the Exchange Server with the last security patches, it will create a perfect shield at your network.
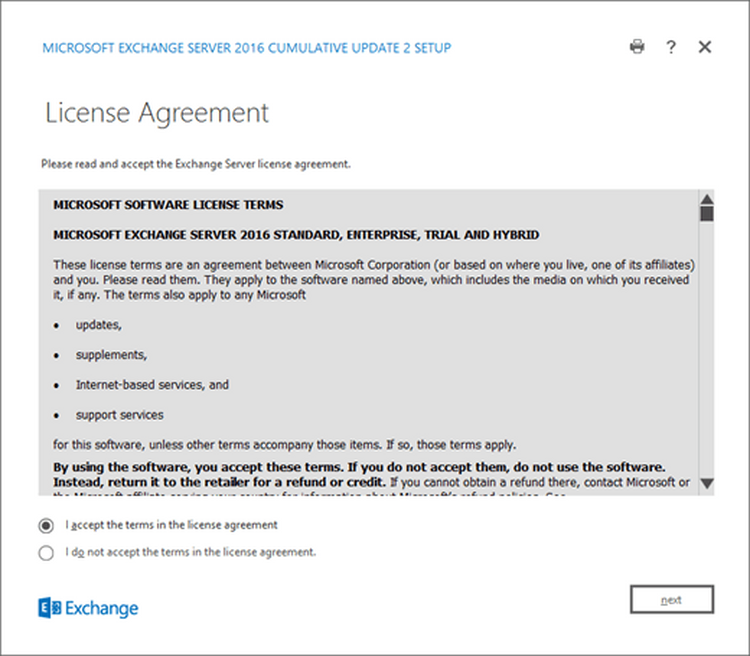
The window of Exchange Server update
For the companies who decided to use the separate anti-malware tools (not Microsoft Defender), Microsoft released a stand-alone tool, called MSERT. It is, exactly, the alter-ego of the Defender – but without the proactive protection and several security features that were applied with Windows 11 release. Nonetheless, no one can help you to deal with the Microsoft products’ problems better than Microsoft itself.
What is MSERT?
Microsoft Support Emergency Response Tool, or shortly MSERT, is a stand-alone anti-malware tool that is spread by Microsoft. It is pretty useful in the cases when you don’t use MS Defender, or it was disabled by the injected malware. Not responding Defender is very often the case when your PC or network is infected with professionally-made malware. Sometimes, malware can also eliminate the third-party antivirus tools – with the help of apps like CCleaner, for example.
MSERT does not have such problems – it just comes to your device, eliminates the malware, and goes. The problem is that it does not have any on-run scanning facilities, as well as system recovery functions – only on-demand scans and malware removal. Thus, it is not recommended to use it as a full-featured anti-malware tool.
How to use the MSERT tool?
Besides the fact that it has an interface and can be launched as a usual program, adjusting some of the parameters can be done exclusively through the console. For example, by default, MSERT will delete all detected threats. To avoid such a problem, you need to launch it through the console with the following command:
msert.exe /N
/N argument will enable the quarantine list in the MSERT program. That gives you a chance to save the elements that were detected as malicious, but which in fact are legit. You can download the MSERT on the official Microsoft website. There will be no problem using it even if you don’t have the experience of working with a console. The GUI of this program fits all the needs – regardless of a pretty minimalistic design.
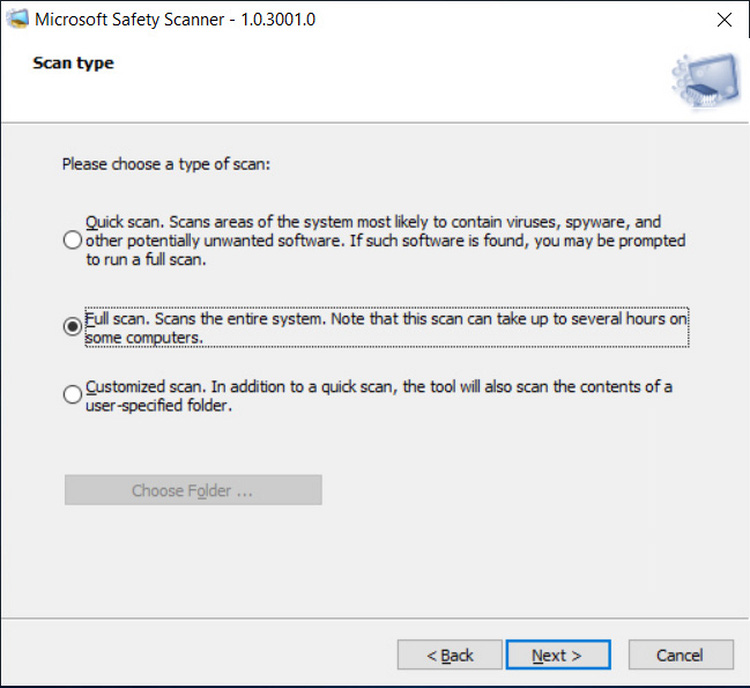
Just choose the scan type you need, and wait for some time. Microsoft warns that the scan may last for several hours, and they are right when there are a lot of files on your computer. Full scan is about checking each file, each registry key and each system configuration – in order to detect the malware activity.



Leave a Comment