Information security experts studied MonitorMinor, a stalker product for Android. Experts found that malware traces activity in Gmail, Instagram, Facebook and WhatsApp; they also concluded that the application is ahead of existing software of this class in its capabilities.
Let me remind you that the term stalkerware usually means commercial spyware, which is positioned as legal. With it, users can access personal data stored on smartphones and tablets of other users. For example, we talked about such software on the example of Spyware.Socelars or Spyware.Arkei, while with the use of advanced Pegasus program, Jeff Bezos’s smartphone was hacked.Such software, as a rule, is used for secret surveillance of other people, for example, by abusive husbands, and therefore carries serious risks for those on whose devices it is installed.
As a rule, the simplest function of the stalkerware is the ability to transmit the victim’s current geographic coordinates. There are many such “stalkers” due to the fact that special web resources are used to display coordinates and their writing is reduced to a couple of lines of code”, – report Kaspersky Lab experts.
Often, developers of such solutions turn to geofencing technology, when a notification about the victim’s movements is sent only if she leaves a certain sector or, on the contrary, gets into it. In some cases, the function of intercepting SMS and data about calls is added to the transmission of the geolocation (an application that is capable to record them is much less common).
However, these days, SMS is not used so often (mainly for one-time passwords), as their niche is almost completely captured by messengers, with the help of which today even conducted business negotiations. Moreover, they claim to be an alternative to “traditional” voice communications. Therefore, in order to be “in the market”, stalker software must be able to intercept data from instant messengers. The sample found by the researchers, which received the verdict Monitor.AndroidOS.MonitorMinor.c, is one of the representatives of the class of stalker software that can do this.
MonitorMinor receives high rights in the system using utilities such as SuperUser, which provide root access to the system. It is not so important how exactly they get to the device – they are delivered directly from the factory, installed by the device owner, or they are installed by the malware. The main thing is that with their appearance one of the key security systems of the system ceases to exist (in fact, all security systems cease to exist, but the researchers write specifically about Discretionary Access Control).
Using this privilege escalation, MonitorMinor gains full access to the data of the following applications:
- LINE: Free Calls & Messages
- Gmail
- Zalo — Video Call
- Kik
- Hangouts
- Viber
- Hike News & Content
- Skype
- Snapchat
- JusTalk
- BOTIM
At the same time, the MonitorMinor functions are not limited to intercepting data from social networking applications and instant messengers.
Using root privileges, the program extracts the file /data/system/gesture.key from the device, which contains the hash sum of the password or screen unlock pattern.
As a result, the MonitorMinor operator can unlock the device when it is nearby, or the next time it has physical access to the device. For the first time in the history of threat monitoring for mobile platforms, experts have discovered this feature.
Also, after gaining root access, the malware will remount the system partition from read-only to write mode, copy itself to it, delete it from the user partition, and remount the system partition to read-only mode. After this “castling”, it will no longer be possible to remove the “stalker” using regular tool of the OS“, – according to information security experts.
Of course, the privilege escalation option is not available on all devices, and it could assumed that without root, the malware would not be so effective. However, it is not true.
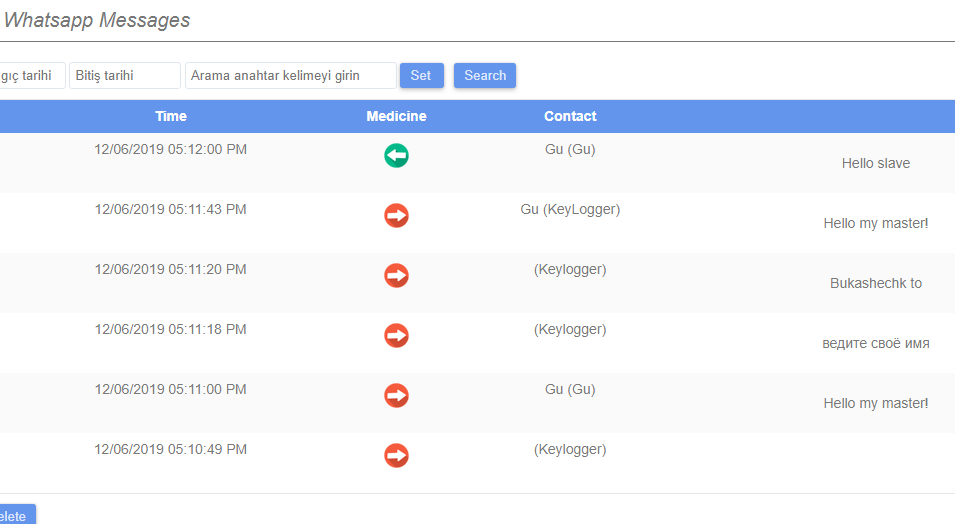
The malware intercepts events in the above applications using the Accessibility Services API. Simply put, MonitorMinor without root is able to work effectively on all devices where there are Accessibility Services (and most of these devices). Using the same API, the application also implements the keylogger function. That is, the range of using MonitorMinor is not limited to social networks and instant messengers: everything that the victim enters will be automatically sent to MonitorMinor servers. The application also monitors the clipboard and sends its owner its contents. In addition, it allows its owner:
- manage the device using SMS commands
- show real-time video from the device’s cameras
- record sound from the device’s microphone
- show browsing history in Chrome
- show statistics on the use of certain applications
- show contents of internal storage of the device
- show contact list content
- show syslog
According to company statistics, users from India face most often MonitorMinor: now, this country accounts for the largest share of installations (14.71%). In addition, a Gmail account with an Indian name is registered in the body of MonitorMinor, which allows us to make an assumption about the country of origin of the program. However, together with these analysts, they managed to find control panels in Turkish and English.
The second country in terms of popularity with MonitorMinor is Mexico (11.76%), and Germany, Saudi Arabia and the United Kingdom (5.88%) are located in the third, fourth and fifth, with a difference of thousandths of a percent.


Leave a Comment